WiFi administrado en la nube vs. WiFi basado en controladores: ¿Cuál debería elegir?
This guide provides a vendor-neutral technical comparison of cloud-managed WiFi and controller-based (on-premise) WiFi architectures, helping IT managers, network architects, and CTOs make an informed deployment decision. It covers the architectural trade-offs across scalability, data sovereignty, cost model, and offline resilience, with real-world case studies from hospitality, retail, and public-sector environments. It also explains how Purple's WiFi intelligence platform integrates with either architecture to deliver guest experience management, first-party data capture, and GDPR-compliant analytics.
🎧 Escucha esta guía
Ver transcripción
- Resumen ejecutivo
- Análisis técnico detallado
- ¿Qué es el WiFi administrado en la nube?
- ¿Qué es el WiFi basado en controladores?
- Ventajas y desventajas arquitectónicas: Una comparación estructurada
- Consideraciones de arquitectura de seguridad
- Cómo se integra Purple con ambas arquitecturas
- Guía de implementación
- Paso 1: Defina su perfil de requisitos
- Paso 2: Seleccione su modelo de arquitectura
- Paso 3: Evalúe a los proveedores de red
- Paso 4: Implemente Purple como su capa de inteligencia
- Paso 5: Valide el cumplimiento y la seguridad
- Mejores prácticas
- Resolución de problemas y mitigación de riesgos
- ROI e impacto comercial

Resumen ejecutivo
La decisión entre WiFi administrado en la nube y WiFi basado en controladores es una de las elecciones arquitectónicas más trascendentales que tomará un equipo de redes en esta década. Ambos modelos ofrecen conectividad inalámbrica de nivel empresarial, pero difieren fundamentalmente en dónde reside la inteligencia, cómo escalan, cuánto cuestan a lo largo del tiempo y cómo manejan las obligaciones de cumplimiento.
El WiFi administrado en la nube traslada la función del controlador a una plataforma en la nube alojada por el proveedor, lo que permite el aprovisionamiento zero-touch, actualizaciones automáticas de firmware y una gestión centralizada (single-pane-of-glass) en un número ilimitado de sitios. El WiFi basado en controladores mantiene esa inteligencia en las instalaciones (on-premise), proporcionando máxima soberanía de datos, resiliencia sin conexión y control granular, a costa de un mayor CapEx y una mayor carga operativa.
Para la mayoría de los operadores con múltiples sitios (cadenas hoteleras, propiedades comerciales, operadores de estadios y autoridades locales), el WiFi administrado en la nube representa hoy en día la opción operativamente superior. Para implementaciones grandes en un solo campus con requisitos estrictos de residencia de datos, los controladores locales siguen siendo atractivos. En cualquier caso, la plataforma de gestión de WiFi de Purple opera como una capa superpuesta independiente de la infraestructura, agregando la gestión de la experiencia del invitado, la captura de datos en cumplimiento con el GDPR y analíticas procesables sobre la arquitectura que elija.
Análisis técnico detallado
¿Qué es el WiFi administrado en la nube?
El WiFi administrado en la nube es una arquitectura de LAN inalámbrica en la que la función del controlador (autenticación, aplicación de políticas, gestión de radiofrecuencia, distribución de firmware y monitoreo) se aloja en una plataforma en la nube operada por el proveedor en lugar de hardware local dedicado. Los puntos de acceso en los sitios locales se conectan a la plataforma de gestión en la nube a través de túneles cifrados HTTPS o CAPWAP, recibiendo su configuración y enviando datos de telemetría hacia arriba. El plano de datos (el reenvío real del tráfico de usuarios) generalmente permanece local en el punto de acceso, lo que garantiza que una interrupción de la WAN no interrumpa las sesiones activas de los usuarios.
Las principales plataformas de WiFi administrado en la nube incluyen Cisco Meraki, Aruba Central (HPE), Juniper Mist, Extreme Networks CloudIQ y Ruckus One. Cada plataforma proporciona una consola de gestión basada en la web, una API RESTful para la integración con sistemas de terceros y diversos grados de optimización de RF impulsada por IA y detección de anomalías.
¿Qué es el WiFi basado en controladores?
El WiFi basado en controladores es la arquitectura inalámbrica empresarial tradicional en la que se implementa un controlador de LAN inalámbrica (WLC) físico o virtual en las instalaciones para gestionar todos los puntos de acceso dentro de un sitio o campus. El controlador maneja la autenticación IEEE 802.1X a través de RADIUS, aplica políticas de QoS y seguridad, gestiona el roaming rápido entre puntos de acceso (IEEE 802.11r) y proporciona monitoreo y resolución de problemas centralizados. En una configuración de túnel dividido o conmutación local, el tráfico del usuario se reenvía localmente en el punto de acceso; en una configuración de conmutación centralizada, todo el tráfico se tuneliza de vuelta al controlador.
Las principales plataformas basadas en controladores incluyen Cisco Catalyst Wireless (anteriormente AireOS), Aruba Mobility Controllers, Juniper Mist con controladores virtuales locales y Ruckus SmartZone. Estas plataformas son maduras, ricas en funciones y se implementan ampliamente en entornos empresariales, de atención médica y del sector público.
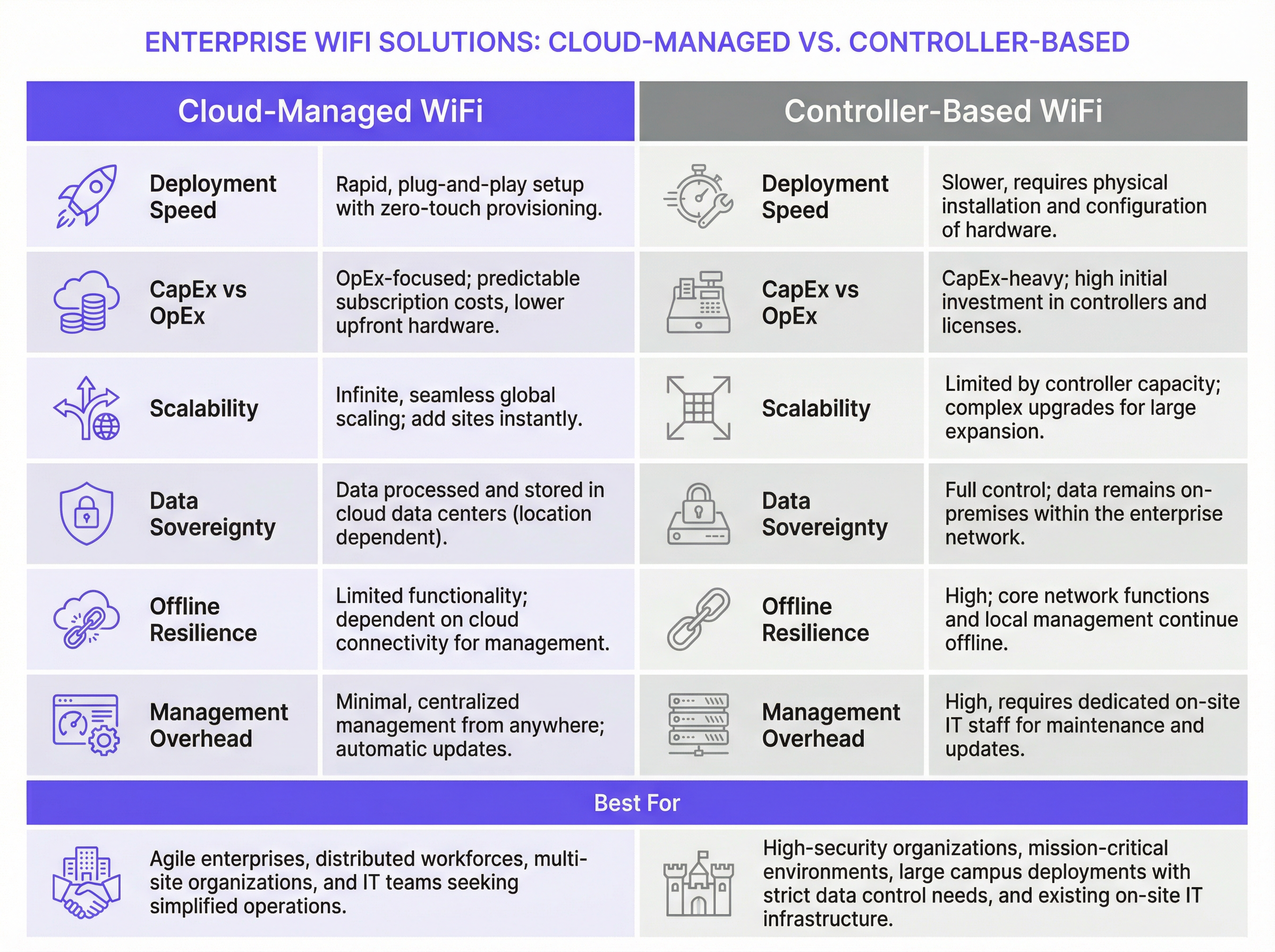
Ventajas y desventajas arquitectónicas: Una comparación estructurada
| Dimensión | WiFi administrado en la nube | WiFi basado en controladores |
|---|---|---|
| Velocidad de implementación | Rápida; aprovisionamiento zero-touch mediante configuración previa de AP | Más lenta; requiere instalación del controlador en el sitio y registro de AP |
| Modelo de costos | Dominado por OpEx; licencias de suscripción por AP | Dominado por CapEx; compra de hardware más contratos de soporte anuales |
| Escalabilidad | Prácticamente ilimitada; agregue sitios sin cambios de hardware | Limitada por la capacidad del controlador; requiere actualizaciones de hardware para escalar |
| Resiliencia sin conexión | El reenvío de tráfico local continúa; se pierde el acceso a la gestión | Funcionalidad completa de gestión y plano de datos mantenida localmente |
| Soberanía de datos | Datos de gestión procesados en la nube (depende de la región) | Todos los datos permanecen dentro del límite de la red empresarial |
| Gestión de firmware | Actualizaciones automáticas gestionadas por el proveedor | Manual o programada; requiere supervisión del equipo de TI |
| Funciones avanzadas | Mejorando rápidamente; optimización de RF impulsada por IA disponible | Maduras; QoS avanzado, servicios de ubicación y granularidad de políticas |
| Gestión multisitio | Panel de control único (single pane of glass) para todos los sitios de forma nativa | Requiere herramientas de NOC adicionales o gestión por sitio |
| Carga de TI | Baja; requiere experiencia mínima en el sitio | Alta; requiere ingenieros inalámbricos capacitados para el mantenimiento |
Consideraciones de arquitectura de seguridad
Ambas arquitecturas admiten estándares de seguridad de nivel empresarial. WPA3-Enterprise con autenticación IEEE 802.1X está disponible en todas las plataformas modernas administradas en la nube y basadas en controladores. La integración de RADIUS para la autenticación centralizada es estándar en ambos modelos. La segmentación de VLAN para aislar el tráfico de invitados, personal e IoT es compatible con todos los principales proveedores.
La distinción clave de seguridad radica en el plano de gestión. En una implementación basada en controladores, todo el tráfico de gestión permanece dentro del perímetro de su red, lo cual es una ventaja significativa para las organizaciones sujetas a PCI DSS (que requiere controles estrictos en los entornos de datos de los titulares de tarjetas) o requisitos de certificación ISO 27001. En una implementación administrada en la nube, el tráfico de gestión atraviesa el internet público (aunque cifrado) y su postura de seguridad depende en parte de los propios controles de seguridad y certificaciones del proveedor de la nube.
Para el WiFi de invitados específicamente, el cumplimiento del GDPR requiere que cualquier dato personal recopilado a través de un Captive Portal (incluidas direcciones de correo electrónico, tokens de inicio de sesión social o identificadores de dispositivos) se capture con consentimiento explícito e informado, se almacene de forma segura y esté sujeto a los derechos del titular de los datos, incluidos el acceso y la eliminación. Esta obligación se aplica independientemente de si su red subyacente está administrada en la nube o basada en controladores. El marco de gestión de consentimiento de Purple aborda este requisito directamente, proporcionando registros de consentimiento con marca de tiempo, políticas automatizadas de retención de datos y un portal de autoservicio para las solicitudes de los titulares de los datos.
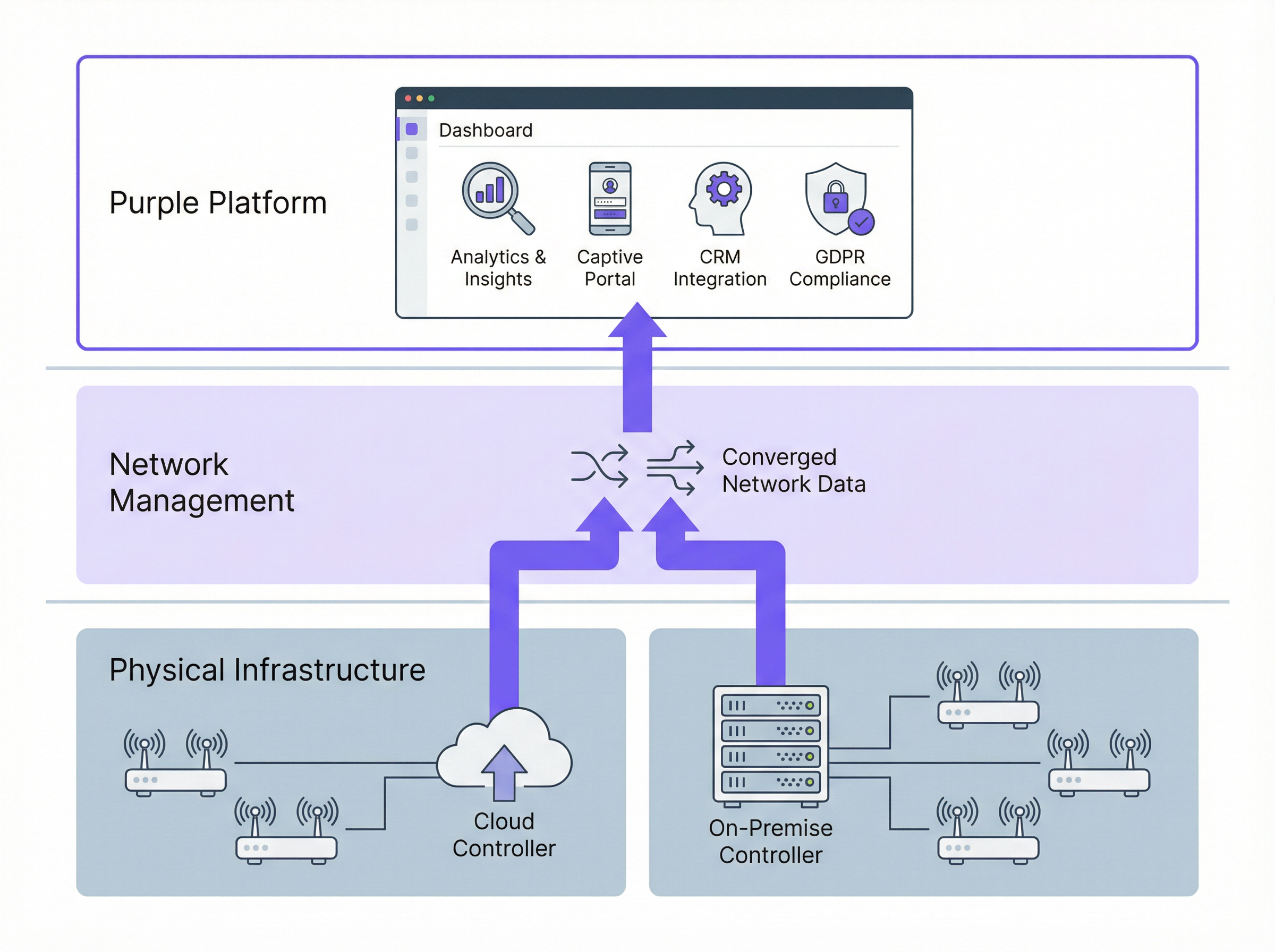
Cómo se integra Purple con ambas arquitecturas
Purple opera como una capa superpuesta de inteligencia WiFi: no reemplaza a su proveedor de red, sino que lo complementa con una capa de experiencia del invitado y analíticas. Purple se conecta a su infraestructura de red a través de APIs estándar e integración RADIUS, independientemente de si sus puntos de acceso están administrados por una plataforma en la nube o un controlador local.
Para el WiFi de invitados, Purple proporciona un Captive Portal personalizable que maneja la autenticación del usuario (inicio de sesión social, correo electrónico, verificación por SMS o la aplicación de Purple), la captura de consentimiento en cumplimiento con el GDPR y la transferencia fluida a la red. Para el WiFi del personal, las capacidades de red basadas en identidad de Purple permiten el aprovisionamiento y la revocación automáticos de acceso vinculados a su sistema de recursos humanos o gestión de identidad, lo que garantiza que el acceso a la red de un empleado que se marcha se cancele sin intervención manual.
La plataforma de analíticas de Purple luego procesa los datos de conexión para generar métricas de afluencia, análisis de tiempo de permanencia, proporciones de visitantes nuevos frente a recurrentes e información demográfica. Estas analíticas están disponibles a través del panel de control de Purple, mediante integración de API con sus herramientas de inteligencia empresarial o a través de conectores CRM directos a plataformas que incluyen Salesforce, HubSpot y Microsoft Dynamics.
Guía de implementación
Paso 1: Defina su perfil de requisitos
Antes de evaluar proveedores, documente sus requisitos en cinco dimensiones: cantidad y distribución de sitios (campus único frente a propiedad multisitio); obligaciones de cumplimiento (GDPR, PCI DSS, requisitos de residencia de datos); capacidad del equipo de TI (¿puede soportar hardware local en cada sitio?); objetivos comerciales (¿necesita captura de datos de invitados y analíticas?); y modelo de presupuesto (preferencia de CapEx frente a OpEx).
Paso 2: Seleccione su modelo de arquitectura
Aplique la siguiente lógica de decisión. Si opera más de cinco sitios distribuidos geográficamente, el WiFi administrado en la nube es casi con certeza la opción correcta para su capa de acceso: los ahorros operativos de la gestión centralizada y el aprovisionamiento zero-touch superarán los costos de suscripción en un plazo de doce a dieciocho meses. Si opera un solo campus grande con requisitos estrictos de soberanía de datos, evalúe los controladores locales, incluidas las opciones de controladores virtuales que reducen el CapEx de hardware. Si tiene una combinación de tipos de sitios, considere un modelo híbrido deliberado con criterios claramente definidos para cada tipo de implementación.
Paso 3: Evalúe a los proveedores de red
Emita una RFP estructurada que cubra: especificaciones de hardware de AP (soporte para Wi-Fi 6E, diseño de antena, requisitos de PoE); capacidades de la plataforma de gestión (integridad de la API, monitoreo, alertas); certificaciones de seguridad (SOC 2 Tipo II para plataformas en la nube, ISO 27001); compromisos de SLA (garantías de tiempo de actividad, tiempos de respuesta de soporte); y ecosistema de integración (RADIUS, VLAN, APIs de plataformas de terceros).
Paso 4: Implemente Purple como su capa de inteligencia
Una vez seleccionada su infraestructura de red, implemente Purple para agregar la gestión de la experiencia del invitado y analíticas. El proceso de implementación de Purple implica: configurar un SSID de invitados dedicado en su infraestructura de red; apuntar la página de inicio del SSID o la autenticación RADIUS a la plataforma en la nube de Purple; personalizar el Captive Portal con su identidad de marca y flujos de consentimiento; y conectar Purple a sus plataformas de CRM y automatización de marketing a través del mercado de integraciones.
Paso 5: Valide el cumplimiento y la seguridad
Antes del lanzamiento, realice una revisión de cumplimiento que cubra: validación del flujo de consentimiento del GDPR (asegúrese de que el consentimiento sea explícito, granular y esté registrado); verificación de la segmentación de la red (confirme que el tráfico de invitados no pueda llegar a los sistemas internos); evaluación del alcance de PCI DSS (si los datos de tarjetas de pago se procesan en cualquier parte de la red); y pruebas de penetración del entorno de WiFi de invitados.
Mejores prácticas
Segmente agresivamente. Implemente siempre SSID separados para invitados, personal y dispositivos IoT, cada uno asignado a una VLAN dedicada con políticas de firewall adecuadas. El tráfico de invitados debe estar aislado de los sistemas internos de forma predeterminada, con acceso exclusivo a internet a menos que un requisito comercial específico justifique lo contrario.
Aplique WPA3 donde el hardware lo soporte. Los puntos de acceso Wi-Fi 6 y Wi-Fi 6E admiten WPA3 universalmente. Para las redes de invitados, WPA3-Personal con Autenticación Simultánea de Iguales (SAE) proporciona una protección significativamente más fuerte contra ataques de diccionario fuera de línea que WPA2-PSK. Para las redes del personal, WPA3-Enterprise con 802.1X proporciona autenticación por usuario y secreto hacia adelante (forward secrecy).
Planifique para OpenRoaming. El estándar OpenRoaming de la Wi-Fi Alliance, basado en Passpoint (IEEE 802.11u), permite a los usuarios conectarse automáticamente a cualquier red habilitada para OpenRoaming utilizando credenciales de su proveedor de identidad de origen: su operador móvil, su empleador o una plataforma como la aplicación de Purple. La implementación de OpenRoaming elimina la fricción del Captive Portal para los usuarios recurrentes mientras mantiene un acceso autenticado y seguro. Purple es compatible con OpenRoaming de forma nativa.
Automatice la gestión de firmware. El firmware sin parches es uno de los vectores de ataque más comunes en las implementaciones de WiFi empresarial. Las plataformas administradas en la nube manejan esto automáticamente; para las implementaciones locales, establezca un ciclo de revisión de firmware trimestral y utilice la funcionalidad de actualización programada de su controlador para enviar actualizaciones durante las ventanas de mantenimiento.
Monitoree continuamente. Implemente capacidades WIDS (Sistema de Detección de Intrusiones Inalámbricas), disponibles en todas las principales plataformas empresariales, para detectar puntos de acceso no autorizados, ataques de desautenticación y ataques de gemelo malvado (evil twin). Integre las alertas de WIDS con su plataforma SIEM para un monitoreo de seguridad centralizado.
Resolución de problemas y mitigación de riesgos
Riesgo: Interrupción de la plataforma de gestión en la nube. Mitigación: Verifique que la plataforma elegida admita la supervivencia local de los AP (la capacidad de los puntos de acceso para continuar operando con su última configuración conocida si se pierde la conectividad a la nube). Todas las principales plataformas en la nube (Meraki, Aruba Central, Juniper Mist) admiten esta capacidad. Pruébelo explícitamente durante su fase de pruebas de aceptación.
Riesgo: Incumplimiento del GDPR en la captura de datos de invitados. Mitigación: Utilice una plataforma como Purple que proporcione un marco de gestión de consentimiento preconstruido y revisado legalmente. Evite crear Captive Portals personalizados sin revisión legal: el lenguaje específico, la granularidad y los requisitos de registro para el consentimiento del GDPR son precisos y con frecuencia se implementan incorrectamente.
Riesgo: Falla del hardware del controlador en implementaciones locales. Mitigación: Implemente controladores en pares de alta disponibilidad con conmutación por error (failover) automática. Para los controladores virtuales, asegúrese de que la infraestructura del hipervisor subyacente tenga la redundancia adecuada. Documente su objetivo de tiempo de recuperación (RTO) y pruebe los procedimientos de conmutación por error anualmente.
Riesgo: Ancho de banda WAN insuficiente para la gestión en la nube. Mitigación: El tráfico de gestión en la nube suele ser modesto (de uno a dos megabits por segundo por cada cien puntos de acceso), pero se dispara durante las actualizaciones de firmware. Programe las actualizaciones de firmware durante las horas de menor actividad y utilice políticas de QoS para priorizar el tráfico de gestión sobre los datos de los invitados si el ancho de banda WAN es limitado.
Riesgo: Dependencia del proveedor (vendor lock-in). Mitigación: Evalúe la apertura de la API de la plataforma elegida y su soporte para estándares neutrales al proveedor (RADIUS, 802.1X, etiquetado de VLAN). La arquitectura independiente de la infraestructura de Purple significa que puede cambiar su proveedor de red subyacente sin perder los datos de sus invitados, el historial de analíticas o las integraciones de CRM.
ROI e impacto comercial
El caso de negocio para el WiFi administrado en la nube con Purple como capa de inteligencia está bien establecido en múltiples verticales. McDonald's, un cliente de Purple, logró una reducción del 90 % en las visitas de ingenieros de TI al sitio al implementar WiFi de invitados administrado en la nube con gestión centralizada: un ahorro de costos operativos directos que financió la inversión de la plataforma durante el primer año. El Aeropuerto de Bruselas Sur Charleroi logró un ROI del 10,630 % gracias a las analíticas de WiFi de invitados de Purple, impulsado por una mejor experiencia del pasajero, un mayor tiempo de permanencia en las áreas comerciales y decisiones comerciales basadas en datos.
Para una propiedad hotelera típica de 40 establecimientos, el modelo financiero se ve aproximadamente de la siguiente manera. Implementación basada en controladores: £80,000 a £120,000 en CapEx de hardware de controlador, más £15,000 a £25,000 por año en contratos de soporte, más tiempo de ingeniería para mantenimiento. Implementación administrada en la nube: £0 en hardware de controlador, más £8,000 a £15,000 por año en suscripciones de plataforma, más una carga de ingeniería significativamente reducida. El modelo administrado en la nube generalmente alcanza el punto de equilibrio entre 18 y 24 meses y ofrece un costo total de propiedad más bajo en un horizonte de cinco años.
El valor comercial de la capa de analíticas de Purple agrega una dimensión adicional al cálculo del ROI. Los datos de origen (first-party data) de los invitados capturados a través del Captive Portal de Purple (direcciones de correo electrónico, frecuencia de visitas, datos demográficos) tienen un valor comercial directo para campañas de marketing, inscripción en programas de lealtad y comunicaciones personalizadas. Las organizaciones que integran Purple con su plataforma CRM generalmente reportan un aumento del 25 al 40 % en contactos calificados por marketing dentro de los primeros doce meses de implementación.
Escuche el podcast Purple Technical Briefing para obtener un recorrido en audio de 10 minutos de esta guía, que cubre las ventajas y desventajas de la arquitectura, recomendaciones de implementación y una sesión rápida de preguntas y respuestas.
Términos clave y definiciones
Cloud-Managed WiFi
A wireless LAN architecture in which the controller function — including authentication, policy enforcement, radio frequency management, and firmware distribution — is hosted in a vendor-operated cloud platform. Access points connect to the cloud platform for configuration and monitoring, while local traffic forwarding typically remains at the access point.
IT teams encounter this term when evaluating modern WiFi platforms from vendors such as Cisco Meraki, Aruba Central, and Juniper Mist. It is the dominant deployment model for new enterprise WiFi deployments as of 2024.
On-Premise WiFi Controller (WLC)
A physical or virtual appliance deployed within the enterprise network that centrally manages all access points, handling authentication, QoS, roaming, and security policy enforcement. All management traffic remains within the enterprise network perimeter.
IT teams encounter this in legacy enterprise environments and in organisations with strict data sovereignty or compliance requirements. Major platforms include Cisco Catalyst 9800, Aruba Mobility Controller, and Ruckus SmartZone.
Zero-Touch Provisioning (ZTP)
A deployment capability that allows network devices — access points, switches, or routers — to be shipped directly to a site and automatically configured upon first connection to the network, without requiring on-site engineer intervention. The device contacts a cloud management platform, downloads its pre-staged configuration, and becomes operational.
ZTP is a primary operational advantage of cloud-managed WiFi for multi-site deployments. It eliminates the need to pre-configure devices in a staging environment or dispatch engineers to remote sites for initial setup.
IEEE 802.1X
An IEEE standard for port-based network access control that provides an authentication framework for devices connecting to a LAN or WLAN. It requires a supplicant (the connecting device), an authenticator (the access point or switch), and an authentication server (typically a RADIUS server) to complete an authentication exchange before network access is granted.
IT teams implement 802.1X for staff WiFi networks to enforce per-user authentication, typically using EAP-TLS (certificate-based) or PEAP-MSCHAPv2 (username/password) as the inner authentication method. It is required for WPA3-Enterprise deployments.
WPA3-Enterprise
The current generation of WiFi security protocol for enterprise networks, defined by the Wi-Fi Alliance. WPA3-Enterprise uses IEEE 802.1X for authentication and supports 192-bit cryptographic strength (CNSA suite) for high-security environments. It provides forward secrecy, meaning that the compromise of a long-term key does not expose past session traffic.
IT teams should be deploying WPA3-Enterprise on all new staff WiFi SSIDs where hardware supports it. All Wi-Fi 6 and Wi-Fi 6E certified access points are required to support WPA3.
Captive Portal
A web page presented to users when they connect to a WiFi network, requiring them to complete an action — accepting terms of service, entering credentials, or providing personal information — before being granted internet access. Captive portals are implemented using DNS and HTTP redirection at the network level.
IT teams deploy captive portals for guest WiFi to enforce acceptable use policies, capture user data for marketing or analytics purposes, and comply with legal requirements for identifying users on public networks. Purple provides a fully customisable, GDPR-compliant captive portal as a core product feature.
GDPR (General Data Protection Regulation)
The European Union's primary data protection regulation, effective from May 2018, which governs the collection, processing, and storage of personal data relating to EU residents. Under GDPR, organisations must have a lawful basis for processing personal data, provide transparent privacy notices, and respect data subject rights including access, rectification, and erasure.
GDPR is directly relevant to guest WiFi deployments because the collection of email addresses, device identifiers, or behavioural data via a captive portal constitutes processing of personal data. Organisations must ensure their captive portal consent flows meet GDPR requirements for valid consent under Article 7.
OpenRoaming
A Wi-Fi Alliance standard built on Passpoint (IEEE 802.11u) that enables automatic, seamless WiFi authentication across networks operated by different providers, using credentials from a user's home identity provider (mobile carrier, employer, or platform account). Users connect without a captive portal, and the network authenticates them via a federated identity exchange.
IT teams deploying guest WiFi in venues with high repeat visitor rates — airports, hotel chains, retail estates — should evaluate OpenRoaming to reduce authentication friction for returning users. Purple supports OpenRoaming natively, enabling users who have previously authenticated via the Purple App to connect automatically at any Purple-enabled venue.
PCI DSS (Payment Card Industry Data Security Standard)
A set of security standards developed by the major card networks (Visa, Mastercard, Amex, Discover) that applies to any organisation that stores, processes, or transmits payment card data. PCI DSS includes specific requirements for network segmentation, access control, encryption, and monitoring that directly affect WiFi architecture design.
IT teams at hospitality, retail, and events venues must ensure that their WiFi architecture does not bring guest or staff networks into PCI DSS scope unnecessarily. The standard approach is to isolate payment card processing systems on a dedicated, firewalled network segment that is physically and logically separated from guest WiFi traffic.
WiFi Management Platform
A software platform that provides centralised visibility, configuration management, analytics, and policy enforcement for a wireless LAN deployment. This term encompasses both the network management layer (controller or cloud platform) and the application layer (guest experience, analytics, and compliance platforms such as Purple).
IT teams use this term when evaluating the full stack of software required to operate an enterprise WiFi deployment. It is important to distinguish between the network management layer (which controls how APs operate) and the intelligence layer (which extracts business value from the network).
Casos de éxito
A 45-property mid-market hotel chain is replacing end-of-life WiFi infrastructure across its estate. Properties range from 80 to 220 rooms. The IT team consists of three engineers based at head office, with no dedicated on-site IT staff at individual properties. The chain wants to capture guest email addresses for its loyalty programme and needs GDPR-compliant data handling. Budget is constrained, with a preference for OpEx over CapEx. Which WiFi architecture should they choose, and how should Purple be deployed?
This scenario is a strong fit for cloud-managed WiFi with Purple as the guest experience layer. The recommended deployment approach is as follows.
Infrastructure selection: Deploy a cloud-managed platform such as Cisco Meraki MR or Aruba Instant On across all 45 properties. Use zero-touch provisioning: pre-stage AP configurations in the cloud management portal, then ship APs directly to each property for installation by local staff or a third-party field services provider. No on-site controller hardware is required.
SSID architecture: Configure three SSIDs per property: (1) a guest SSID mapped to an internet-only VLAN, with Purple's captive portal as the splash page; (2) a staff SSID using WPA3-Enterprise with 802.1X authentication against the chain's Active Directory via a cloud RADIUS service such as Cisco ISE or JumpCloud; (3) an IoT SSID for in-room devices, isolated on a dedicated VLAN with restricted inter-device communication.
Purple deployment: Configure Purple's captive portal on the guest SSID. Implement a two-step consent flow: step one collects the guest's email address and loyalty programme opt-in; step two presents the WiFi terms of service and GDPR privacy notice with explicit consent checkboxes. Connect Purple to the chain's CRM (e.g., Salesforce) via Purple's native connector to sync guest profiles automatically.
Compliance validation: Enable Purple's data retention policies to automatically anonymise guest records after 24 months in line with the chain's data retention schedule. Configure Purple's consent audit log to satisfy GDPR Article 7(1) requirements for demonstrating valid consent.
Ongoing management: All 45 properties are managed from a single cloud dashboard. Firmware updates are pushed automatically during the 02:00–04:00 maintenance window. The three-person IT team receives automated alerts for AP offline events and can remotely diagnose and resolve most issues without travel.
A Premier League football stadium with a capacity of 62,000 seats is upgrading its WiFi infrastructure ahead of a major international tournament. The stadium hosts 25 home matches per year plus concerts and corporate events. Peak concurrent users are estimated at 18,000 during sold-out events. The stadium's IT team has five engineers on-site. Data sovereignty is a concern as the stadium processes payment card data in its hospitality suites. The stadium wants to offer free guest WiFi to all fans and capture connection data for sponsorship reporting. What architecture is recommended?
This scenario warrants a hybrid architecture with on-premise controllers for the primary network and Purple as the analytics and guest experience layer.
Infrastructure selection: Deploy a centralised on-premise wireless LAN controller cluster (e.g., Cisco Catalyst 9800 or Aruba Mobility Controller) in the stadium's data centre. Deploy Wi-Fi 6E access points (802.11ax, 6 GHz band) across the bowl, concourses, hospitality suites, and back-of-house areas — approximately 800 to 1,200 APs depending on the stadium's geometry. Use a high-density AP deployment design with directional antennas to serve seated fans without co-channel interference.
Network segmentation: Create separate VLANs for: fan guest WiFi (internet-only, Purple captive portal); hospitality suite WiFi (internet plus access to point-of-sale systems, PCI DSS scoped); staff and operations WiFi (access to stadium management systems); and broadcast and media WiFi (dedicated high-bandwidth SSID for press and broadcast teams).
PCI DSS compliance: The hospitality suite network must be isolated from the guest network and subject to PCI DSS controls including network segmentation, access logging, and quarterly vulnerability scanning. The on-premise controller architecture supports this by keeping all PCI-scoped traffic within the stadium's network perimeter.
Purple deployment: Deploy Purple's captive portal on the fan guest WiFi SSID. For a stadium environment, minimise friction: use a single-click social login or the Purple App for authentication. Configure Purple's analytics to capture per-event connection counts, peak concurrent users, and return visitor rates — the key metrics for sponsorship reporting. Integrate Purple with the stadium's sponsorship management platform via API to automate report generation.
Capacity planning: For 18,000 peak concurrent users, target a minimum of one AP per 30 to 40 concurrent users in high-density seating areas, with a throughput budget of 2 to 5 Mbps per user for typical fan usage patterns (social media, messaging, live score apps).
A national retail chain with 280 stores wants to deploy guest WiFi to capture customer data for its marketing team, while also improving store operations through WiFi-based footfall analytics. The chain's IT team manages infrastructure centrally. Stores range from small convenience formats (500 sq ft) to large superstore formats (50,000 sq ft). Some stores are in areas with limited or unreliable internet connectivity. How should the architecture be designed to handle the connectivity variability?
Architecture: Cloud-managed WiFi with local AP survivability enabled, plus Purple for guest experience and analytics.
Connectivity resilience: For stores in areas with unreliable internet connectivity, configure APs with local survivability mode — this ensures that guest WiFi continues to operate with the last-known configuration even if the cloud management connection is lost. For the most connectivity-constrained stores, consider deploying a 4G/LTE failover router as a secondary WAN link, with automatic failover triggered when the primary connection drops below a defined threshold.
Tiered AP deployment: For small convenience formats, deploy two to three APs per store. For large superstore formats, deploy 15 to 25 APs with a high-density design in checkout and food service areas. Use the cloud management platform's template-based configuration to push consistent SSID, VLAN, and security policies across all 280 stores from a single configuration template.
Purple analytics for operations: Beyond guest data capture, configure Purple's footfall analytics to measure customer dwell time in key departments, identify peak traffic periods, and compare performance across the estate. This data feeds directly into the retail operations team's workforce planning and merchandising decisions.
Data architecture: Connect Purple to the chain's CDP (Customer Data Platform) via API to merge WiFi-derived behavioural data with transactional data from the POS system, creating unified customer profiles that the marketing team can use for personalised campaigns.
Análisis de escenarios
Q1. A regional NHS trust operates 12 hospitals and 45 GP surgeries across a county. The trust's IT team of eight engineers manages all infrastructure centrally. The trust is subject to NHS Data Security and Protection Toolkit requirements and processes patient data on its clinical networks. It wants to offer free guest WiFi to patients and visitors in waiting areas, and is evaluating whether to deploy cloud-managed or controller-based WiFi. What architecture would you recommend, and what are the key compliance considerations?
💡 Sugerencia:Consider the NHS DSP Toolkit requirements around data residency and the separation between clinical and guest networks. Also consider the IT team's capacity to manage 57 sites.
Mostrar enfoque recomendado
The recommended architecture is cloud-managed WiFi for the guest network, with strict network segmentation to ensure the guest network is completely isolated from clinical systems. The 57-site scale and the small central IT team make cloud-managed WiFi the operationally superior choice — the alternative of deploying on-premise controllers at each site would require significantly more engineering resource than the team can sustain. The guest WiFi SSID should be on a dedicated VLAN with internet-only access, enforced by firewall rules that block all traffic to clinical network segments. This segmentation ensures that the guest network does not fall within the scope of NHS DSP Toolkit clinical data requirements. For data residency, select a cloud-managed platform that processes and stores data within the UK (or EEA at minimum), and verify this in the vendor's data processing agreement. Deploy Purple on the guest SSID for GDPR-compliant patient data capture, with consent flows that clearly distinguish between WiFi access (which requires minimal data) and optional marketing communications (which require explicit opt-in). The key compliance consideration is demonstrating to NHS Digital that clinical data cannot be accessed from the guest network — this requires documented network segmentation evidence, not just a policy statement.
Q2. A conference centre operator runs a single 15,000 sq metre venue that hosts 200 events per year, ranging from small boardroom meetings (20 delegates) to large exhibitions (5,000 attendees). The venue's IT team has two engineers. The operator wants to offer exhibitor-grade WiFi (dedicated bandwidth per stand) as a paid service, alongside free delegate WiFi. The venue currently has an ageing on-premise controller that is out of support. What architecture should replace it?
💡 Sugerencia:Consider the variable density requirements (20 to 5,000 users), the paid WiFi service model, and the small IT team. Also consider how Purple can support the commercial model.
Mostrar enfoque recomendado
Replace the ageing on-premise controller with a cloud-managed WiFi platform, deploying Wi-Fi 6E access points throughout the venue. The cloud-managed model suits the small IT team and eliminates the hardware maintenance burden of an on-premise controller. For the paid exhibitor WiFi service, configure dedicated SSIDs per exhibition stand using dynamic VLAN assignment, with bandwidth shaping policies enforced at the access point level — all major cloud-managed platforms support this capability. For the free delegate WiFi, deploy Purple's captive portal to capture delegate data (email, organisation, job title) with GDPR-compliant consent, creating a valuable database for the venue's marketing and event follow-up activities. Purple's analytics will also provide the venue operator with per-event attendance data, dwell time metrics, and return visitor rates — useful for commercial reporting to event organisers. The variable density requirement (20 to 5,000 users) is handled by the cloud management platform's dynamic RF management, which automatically adjusts transmit power and channel allocation based on active user density. Ensure the AP deployment design includes sufficient density for peak exhibition capacity, and validate throughput during a high-density test before the first major event.
Q3. A luxury hotel group is deploying a new WiFi estate across 8 five-star properties in Europe. Each property has 150 to 300 rooms, multiple F&B outlets, spa facilities, and conference rooms. The group's CTO wants to use WiFi data to personalise the guest experience — recognising returning guests, understanding their movement patterns within the property, and triggering personalised offers via the hotel app. The group's legal team has flagged GDPR concerns about tracking guest movements. How should the architecture be designed to achieve the commercial objective while remaining GDPR-compliant?
💡 Sugerencia:Consider the distinction between network-level data (which device is connected to which AP) and personal data (which guest is connected). GDPR compliance depends on the consent basis and the data minimisation principle.
Mostrar enfoque recomendado
Deploy cloud-managed WiFi across all 8 properties with Purple as the guest intelligence layer. The GDPR compliance framework requires careful design of the consent and data architecture. At the point of WiFi authentication via Purple's captive portal, present guests with a layered consent notice: the first layer covers basic WiFi access (minimal data, legitimate interest basis); the second layer, presented as an optional enhancement, covers personalised services including movement analytics and targeted offers (explicit consent basis, clearly described). Guests who consent to personalised services have their device's WiFi probe data associated with their guest profile, enabling movement pattern analysis. Guests who do not consent receive standard WiFi access without tracking. This approach satisfies GDPR's requirement for granular, informed consent and the data minimisation principle (only collecting movement data from guests who have explicitly consented). Purple's consent management framework records consent timestamps and scope for each guest, providing the audit trail required under GDPR Article 7. The hotel app integration allows consenting guests to receive personalised offers triggered by their location within the property — for example, a spa offer when they are near the spa entrance. The legal team should review the privacy notice language to ensure the description of movement analytics is sufficiently clear and specific to constitute valid informed consent.
Conclusiones clave
- ✓Cloud-managed WiFi is operationally superior for multi-site deployments (5+ sites) due to zero-touch provisioning, automatic firmware updates, and single-pane-of-glass management — typically delivering lower total cost of ownership than on-premise controllers within 18 to 24 months.
- ✓Controller-based WiFi remains the right choice for large single-campus deployments with strict data sovereignty requirements, PCI DSS scope concerns, or the need for advanced features such as granular QoS and real-time RF optimisation.
- ✓Purple operates as an infrastructure-agnostic WiFi intelligence overlay — it integrates with both cloud-managed and controller-based architectures, adding GDPR-compliant guest data capture, footfall analytics, and CRM integration without requiring changes to the underlying network infrastructure.
- ✓GDPR compliance for guest WiFi is non-negotiable and applies regardless of network architecture: consent must be explicit, granular, and recorded before any personal data is processed. Purple's consent management framework addresses this requirement out of the box.
- ✓Security best practice for any enterprise WiFi deployment requires WPA3-Enterprise on staff networks, strict VLAN segmentation between guest, staff, and IoT traffic, and a documented firmware management process — automated in cloud-managed deployments, scheduled quarterly in on-premise deployments.
- ✓The commercial ROI of guest WiFi analytics is well-evidenced: Purple customers including McDonald's (90% reduction in IT engineer site visits) and Brussels South Charleroi Airport (10,630% ROI) demonstrate that WiFi intelligence delivers measurable business value beyond connectivity.
- ✓Avoid the hybrid trap: if you must operate both cloud-managed and controller-based infrastructure, define explicit criteria for each deployment type and ensure your monitoring and security operations tools can span both environments — unmanaged architectural complexity erodes the cost savings you were trying to achieve.



