WiFi gestito in cloud vs WiFi basato su controller: quale scegliere?
This guide provides a vendor-neutral technical comparison of cloud-managed WiFi and controller-based (on-premise) WiFi architectures, helping IT managers, network architects, and CTOs make an informed deployment decision. It covers the architectural trade-offs across scalability, data sovereignty, cost model, and offline resilience, with real-world case studies from hospitality, retail, and public-sector environments. It also explains how Purple's WiFi intelligence platform integrates with either architecture to deliver guest experience management, first-party data capture, and GDPR-compliant analytics.
🎧 Ascolta questa guida
Visualizza trascrizione
- Sintesi esecutiva
- Approfondimento tecnico
- Cos'è il WiFi gestito in cloud?
- Cos'è il WiFi basato su controller?
- Compromessi architetturali: un confronto strutturato
- Considerazioni sull'architettura di sicurezza
- Come Purple si integra con entrambe le architetture
- Guida all'implementazione
- Fase 1: Definire il profilo dei requisiti
- Fase 2: Selezionare il modello di architettura
- Fase 3: Valutare i vendor di rete
- Fase 4: Implementare Purple come livello di intelligence
- Fase 5: Convalidare conformità e sicurezza
- Best practice
- Risoluzione dei problemi e mitigazione dei rischi
- ROI e impatto aziendale

Sintesi esecutiva
La decisione tra WiFi gestito in cloud e WiFi basato su controller è una delle scelte architetturali più importanti che un team di rete prenderà in questo decennio. Entrambi i modelli offrono connettività wireless di livello enterprise, ma differiscono fondamentalmente per quanto riguarda la posizione dell'intelligenza, la scalabilità, i costi nel tempo e la gestione degli obblighi di conformità.
Il WiFi gestito in cloud sposta la funzione del controller su una piattaforma cloud ospitata dal vendor, consentendo il provisioning zero-touch, aggiornamenti automatici del firmware e una gestione centralizzata (single-pane-of-glass) su un numero illimitato di sedi. Il WiFi basato su controller mantiene tale intelligenza on-premise, offrendo la massima sovranità dei dati, resilienza offline e controllo granulare, al costo di un CapEx più elevato e di maggiori oneri operativi.
Per la maggior parte degli operatori multi-sede (catene alberghiere, reti di vendita al dettaglio, gestori di stadi ed enti locali), il WiFi gestito in cloud rappresenta oggi la scelta operativamente superiore. Per le grandi implementazioni in un singolo campus con rigidi requisiti di residenza dei dati, i controller on-premise rimangono una soluzione valida. In entrambi i casi, la piattaforma di gestione WiFi di Purple opera come un overlay indipendente dall'infrastruttura, aggiungendo la gestione dell'esperienza degli ospiti, l'acquisizione dei dati conforme al GDPR e analitiche azionabili, indipendentemente dall'architettura scelta.
Approfondimento tecnico
Cos'è il WiFi gestito in cloud?
Il WiFi gestito in cloud è un'architettura LAN wireless in cui la funzione del controller (autenticazione, applicazione delle policy, gestione delle radiofrequenze, distribuzione del firmware e monitoraggio) è ospitata in una piattaforma cloud gestita dal vendor anziché su hardware on-premise dedicato. Gli access point nelle sedi locali si connettono alla piattaforma di gestione cloud tramite tunnel HTTPS o CAPWAP crittografati, ricevendo la configurazione e inviando i dati di telemetria a monte. Il data plane (l'inoltro effettivo del traffico utente) rimane in genere locale sull'access point, garantendo che un'interruzione della WAN non interrompa le sessioni utente attive.
Le principali piattaforme WiFi gestite in cloud includono Cisco Meraki, Aruba Central (HPE), Juniper Mist, Extreme Networks CloudIQ e Ruckus One. Ogni piattaforma fornisce una console di gestione basata sul web, un'API RESTful per l'integrazione con sistemi di terze parti e vari gradi di ottimizzazione RF e rilevamento delle anomalie basati sull'intelligenza artificiale.
Cos'è il WiFi basato su controller?
Il WiFi basato su controller è la tradizionale architettura wireless enterprise in cui un wireless LAN controller (WLC) fisico o virtuale viene distribuito on-premise per gestire tutti gli access point all'interno di una sede o di un campus. Il controller gestisce l'autenticazione IEEE 802.1X tramite RADIUS, applica le policy di QoS e sicurezza, gestisce il fast roaming tra gli access point (IEEE 802.11r) e fornisce monitoraggio e risoluzione dei problemi centralizzati. In una configurazione split-tunnel o local-switching, il traffico utente viene inoltrato localmente sull'access point; in una configurazione centralised-switching, tutto il traffico viene reindirizzato al controller tramite tunnel.
Le principali piattaforme basate su controller includono Cisco Catalyst Wireless (in precedenza AireOS), Aruba Mobility Controllers, Juniper Mist con controller virtuali on-premise e Ruckus SmartZone. Queste piattaforme sono mature, ricche di funzionalità e ampiamente distribuite in ambienti aziendali, sanitari e del settore pubblico.
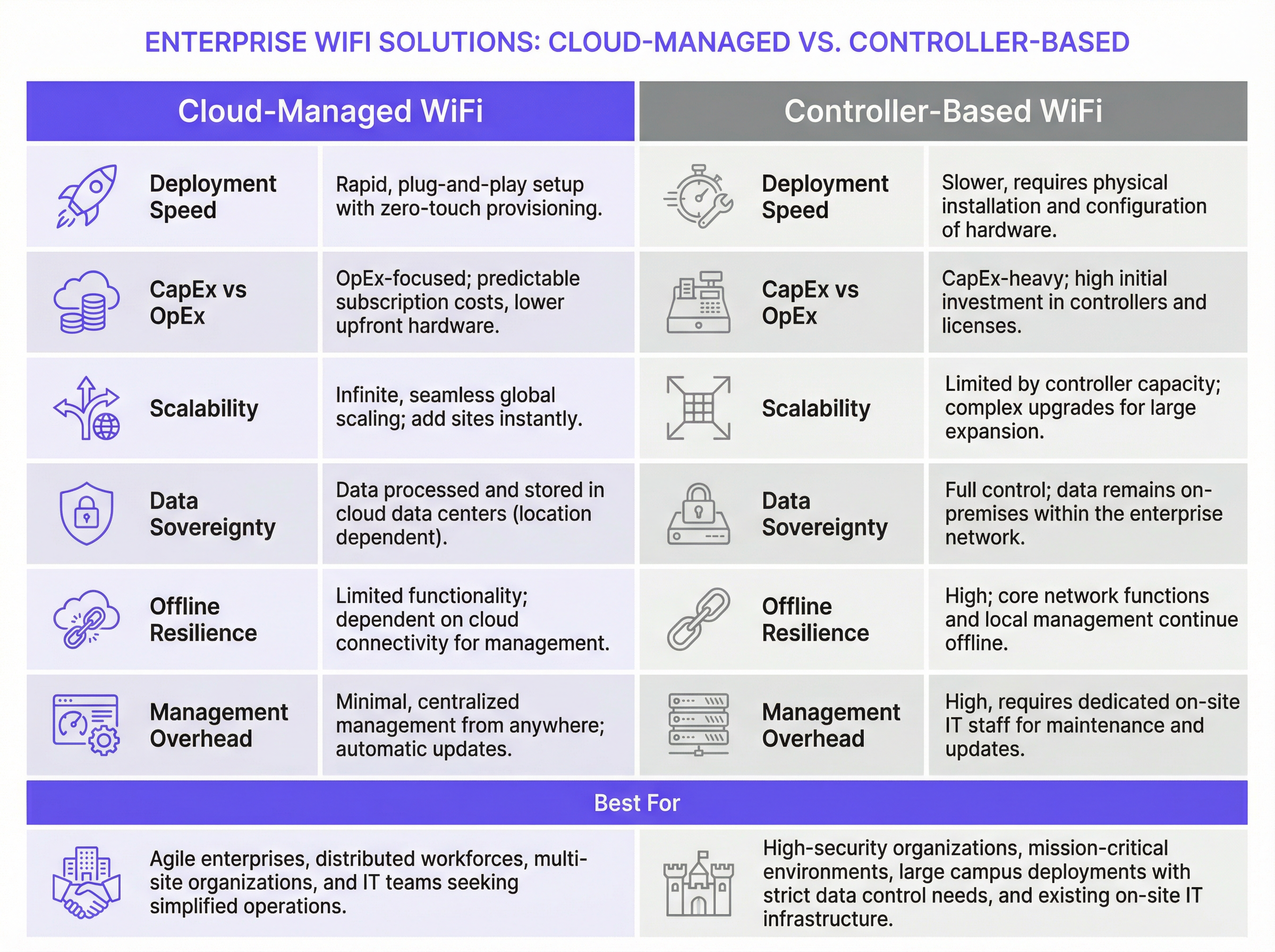
Compromessi architetturali: un confronto strutturato
| Dimensione | WiFi gestito in cloud | WiFi basato su controller |
|---|---|---|
| Velocità di implementazione | Rapida; provisioning zero-touch tramite configurazione pre-staged degli AP | Più lenta; richiede l'installazione del controller in loco e la registrazione degli AP |
| Modello di costo | Prevalentemente OpEx; licenze in abbonamento per AP | Prevalentemente CapEx; acquisto di hardware più contratti di supporto annuali |
| Scalabilità | Praticamente illimitata; aggiunta di sedi senza modifiche hardware | Limitata dalla capacità del controller; richiede aggiornamenti hardware per scalare |
| Resilienza offline | L'inoltro del traffico locale continua; accesso alla gestione perso | Piena funzionalità di gestione e data plane mantenuta localmente |
| Sovranità dei dati | Dati di gestione elaborati in cloud (dipendente dalla regione) | Tutti i dati rimangono all'interno del perimetro della rete aziendale |
| Gestione del firmware | Aggiornamenti automatici gestiti dal vendor | Manuale o programmata; richiede la supervisione del team IT |
| Funzionalità avanzate | In rapido miglioramento; ottimizzazione RF basata su IA disponibile | Mature; QoS avanzata, servizi di localizzazione e granularità delle policy |
| Gestione multi-sede | Single pane of glass nativo su tutte le sedi | Richiede strumenti NOC aggiuntivi o gestione per singola sede |
| Oneri IT | Bassi; competenze in loco minime richieste | Alti; richiede ingegneri wireless qualificati per la manutenzione |
Considerazioni sull'architettura di sicurezza
Entrambe le architetture supportano standard di sicurezza di livello enterprise. WPA3-Enterprise con autenticazione IEEE 802.1X è disponibile su tutte le moderne piattaforme gestite in cloud e basate su controller. L'integrazione RADIUS per l'autenticazione centralizzata è standard in entrambi i modelli. La segmentazione VLAN per isolare il traffico di ospiti, personale e IoT è supportata da tutti i principali vendor.
La principale distinzione in termini di sicurezza risiede nel management plane. In un'implementazione basata su controller, tutto il traffico di gestione rimane all'interno del perimetro di rete, il che rappresenta un vantaggio significativo per le organizzazioni soggette ai requisiti di certificazione PCI DSS (che richiede controlli rigorosi sugli ambienti dei dati dei titolari di carta) o ISO 27001. In un'implementazione gestita in cloud, il traffico di gestione attraversa l'internet pubblico (seppur crittografato) e la postura di sicurezza dipende in parte dai controlli e dalle certificazioni di sicurezza del vendor cloud.
Nello specifico per il WiFi degli ospiti, la conformità al GDPR richiede che qualsiasi dato personale raccolto tramite un Captive Portal (inclusi indirizzi e-mail, token di social login o identificatori di dispositivo) venga acquisito con un consenso esplicito e informato, archiviato in modo sicuro e soggetto ai diritti dell'interessato, inclusi l'accesso e la cancellazione. Questo obbligo si applica indipendentemente dal fatto che la rete sottostante sia gestita in cloud o basata su controller. Il framework di gestione del consenso di Purple soddisfa direttamente questo requisito, fornendo registri di consenso con marca temporale, policy automatizzate di conservazione dei dati e un portale self-service per le richieste degli interessati.
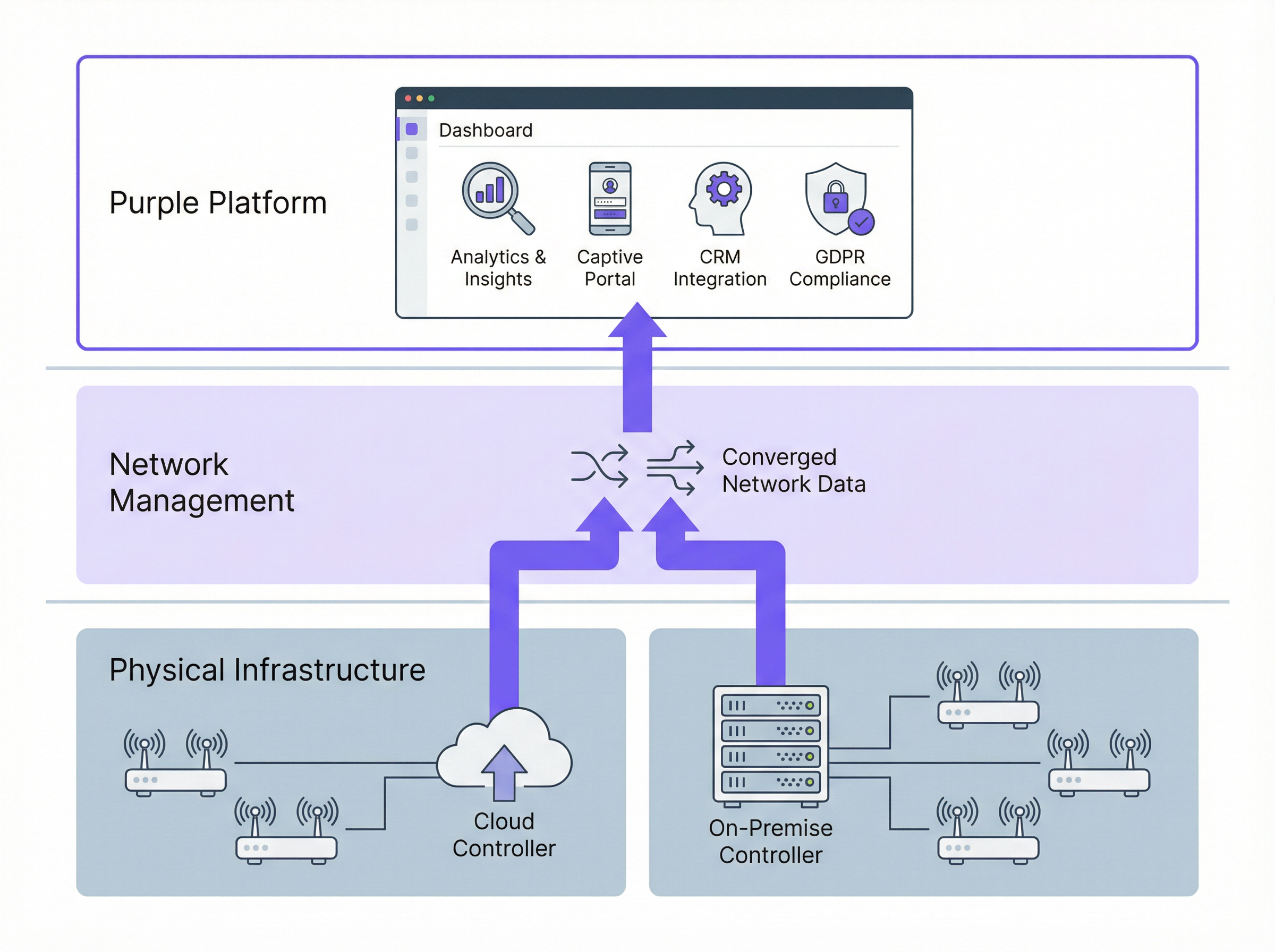
Come Purple si integra con entrambe le architetture
Purple opera come un overlay di intelligence WiFi: non sostituisce il vendor di rete, ma lo arricchisce con un livello di esperienza degli ospiti e analitiche. Purple si connette all'infrastruttura di rete tramite API standard e integrazione RADIUS, indipendentemente dal fatto che gli access point siano gestiti da una piattaforma cloud o da un controller on-premise.
Per il WiFi degli ospiti, Purple fornisce un Captive Portal personalizzabile che gestisce l'autenticazione dell'utente (social login, e-mail, verifica via SMS o la Purple App), l'acquisizione del consenso conforme al GDPR e il passaggio fluido alla rete. Per il WiFi del personale, le funzionalità di rete basate sull'identità di Purple consentono il provisioning e la revoca automatici degli accessi collegati al sistema HR o di gestione delle identità, garantendo che l'accesso alla rete di un dipendente in uscita venga terminato senza intervento manuale.
La piattaforma di analitica di Purple elabora quindi i dati di connessione per generare metriche di affluenza, analisi del tempo di permanenza, rapporti tra visitatori nuovi e di ritorno e insight demografici. Queste analitiche sono disponibili tramite la dashboard di Purple, tramite integrazione API con i tuoi strumenti di business intelligence o tramite connettori CRM diretti a piattaforme come Salesforce, HubSpot e Microsoft Dynamics.
Guida all'implementazione
Fase 1: Definire il profilo dei requisiti
Prima di valutare i vendor, documenta i tuoi requisiti in cinque dimensioni: numero e distribuzione delle sedi (singolo campus rispetto a una rete multi-sede); obblighi di conformità (GDPR, PCI DSS, requisiti di residenza dei dati); capacità del team IT (puoi supportare hardware on-premise in ogni sede?); obiettivi commerciali (hai bisogno di acquisizione dati degli ospiti e analitiche?); e modello di budget (preferenza CapEx rispetto a OpEx).
Fase 2: Selezionare il modello di architettura
Applica la seguente logica decisionale. Se gestisci più di cinque sedi distribuite geograficamente, il WiFi gestito in cloud è quasi certamente la scelta giusta per il tuo livello di accesso: i risparmi operativi derivanti dalla gestione centralizzata e dal provisioning zero-touch supereranno i costi di abbonamento entro dodici-diciotto mesi. Se gestisci un singolo grande campus con rigidi requisiti di sovranità dei dati, valuta i controller on-premise, incluse le opzioni di controller virtuali che riducono il CapEx hardware. Se hai un mix di tipologie di sedi, prendi in considerazione un modello ibrido ponderato con criteri chiaramente definiti per ogni tipo di implementazione.
Fase 3: Valutare i vendor di rete
Emetti una RFP strutturata che copra: specifiche hardware degli AP (supporto Wi-Fi 6E, design dell'antenna, requisiti PoE); capacità della piattaforma di gestione (completezza delle API, monitoraggio, avvisi); certificazioni di sicurezza (SOC 2 Type II per piattaforme cloud, ISO 27001); impegni SLA (garanzie di uptime, tempi di risposta del supporto); ed ecosistema di integrazione (RADIUS, VLAN, API di piattaforme di terze parti).
Fase 4: Implementare Purple come livello di intelligence
Una volta selezionata l'infrastruttura di rete, implementa Purple per aggiungere la gestione dell'esperienza degli ospiti e le analitiche. Il processo di implementazione di Purple prevede: la configurazione di un SSID dedicato agli ospiti sull'infrastruttura di rete; l'indirizzamento della splash page dell'SSID o dell'autenticazione RADIUS alla piattaforma cloud di Purple; la personalizzazione del Captive Portal con l'identità del tuo brand e i flussi di consenso; e la connessione di Purple alle tue piattaforme CRM e di marketing automation tramite il marketplace delle integrazioni.
Fase 5: Convalidare conformità e sicurezza
Prima del go-live, conduci una revisione della conformità che copra: convalida del flusso di consenso GDPR (assicurati che il consenso sia esplicito, granulare e registrato); verifica della segmentazione della rete (conferma che il traffico degli ospiti non possa raggiungere i sistemi interni); valutazione dell'ambito PCI DSS (se i dati delle carte di pagamento vengono elaborati in qualsiasi punto della rete); e penetration testing dell'ambiente WiFi degli ospiti.
Best practice
Segmentare in modo aggressivo. Implementa sempre SSID separati per ospiti, personale e dispositivi IoT, ciascuno mappato su una VLAN dedicata con policy firewall appropriate. Il traffico degli ospiti dovrebbe essere isolato dai sistemi interni per impostazione predefinita, con accesso solo a Internet, a meno che uno specifico requisito aziendale non giustifichi il contrario.
Applicare WPA3 dove l'hardware lo supporta. Gli access point Wi-Fi 6 e Wi-Fi 6E supportano universalmente WPA3. Per le reti degli ospiti, WPA3-Personal con Simultaneous Authentication of Equals (SAE) fornisce una protezione significativamente più forte contro gli attacchi a dizionario offline rispetto a WPA2-PSK. Per le reti del personale, WPA3-Enterprise con 802.1X fornisce autenticazione per utente e forward secrecy.
Pianificare l'OpenRoaming. Lo standard OpenRoaming della Wi-Fi Alliance, basato su Passpoint (IEEE 802.11u), consente agli utenti di connettersi automaticamente a qualsiasi rete abilitata per OpenRoaming utilizzando le credenziali del proprio provider di identità di origine: il proprio operatore di telefonia mobile, il proprio datore di lavoro o una piattaforma come la Purple App. L'implementazione di OpenRoaming elimina l'attrito del Captive Portal per gli utenti di ritorno, mantenendo un accesso autenticato e sicuro. Purple supporta OpenRoaming in modo nativo.
Automatizzare la gestione del firmware. Il firmware senza patch è uno dei vettori di attacco più comuni nelle implementazioni WiFi aziendali. Le piattaforme gestite in cloud gestiscono questo aspetto automaticamente; per le implementazioni on-premise, stabilisci un ciclo di revisione trimestrale del firmware e utilizza la funzionalità di aggiornamento programmato del controller per distribuire gli aggiornamenti durante le finestre di manutenzione.
Monitorare continuamente. Implementa funzionalità WIDS (Wireless Intrusion Detection System), disponibili su tutte le principali piattaforme enterprise, per rilevare access point non autorizzati, attacchi di deautenticazione e attacchi evil twin. Integra gli avvisi WIDS con la tua piattaforma SIEM per un monitoraggio della sicurezza centralizzato.
Risoluzione dei problemi e mitigazione dei rischi
Rischio: interruzione della piattaforma di gestione cloud. Mitigazione: verifica che la piattaforma scelta supporti la sopravvivenza locale degli AP, ovvero la capacità degli access point di continuare a funzionare con l'ultima configurazione nota in caso di perdita della connettività cloud. Tutte le principali piattaforme cloud (Meraki, Aruba Central, Juniper Mist) supportano questa funzionalità. Testala esplicitamente durante la fase di test di accettazione.
Rischio: non conformità al GDPR nell'acquisizione dei dati degli ospiti. Mitigazione: utilizza una piattaforma come Purple che fornisce un framework di gestione del consenso predefinito e revisionato legalmente. Evita di creare Captive Portal personalizzati senza una revisione legale: il linguaggio specifico, la granularità e i requisiti di registrazione per il consenso GDPR sono precisi e spesso implementati in modo errato.
Rischio: guasto hardware del controller nelle implementazioni on-premise. Mitigazione: implementa i controller in coppie ad alta disponibilità con failover automatico. Per i controller virtuali, assicurati che l'infrastruttura hypervisor sottostante disponga di una ridondanza appropriata. Documenta il tuo obiettivo di tempo di ripristino (RTO) e testa le procedure di failover annualmente.
Rischio: larghezza di banda WAN insufficiente per la gestione cloud. Mitigazione: il traffico di gestione cloud è in genere modesto (da uno a due megabit al secondo per cento access point), ma presenta picchi durante gli aggiornamenti del firmware. Programma gli aggiornamenti del firmware durante le ore non di punta e utilizza le policy QoS per dare priorità al traffico di gestione rispetto ai dati degli ospiti se la larghezza di banda WAN è limitata.
Rischio: vendor lock-in. Mitigazione: valuta l'apertura delle API della piattaforma scelta e il suo supporto per standard neutrali rispetto al vendor (RADIUS, 802.1X, tagging VLAN). L'architettura indipendente dall'infrastruttura di Purple ti consente di cambiare il vendor di rete sottostante senza perdere i dati degli ospiti, la cronologia delle analitiche o le integrazioni CRM.
ROI e impatto aziendale
Il business case per il WiFi gestito in cloud con Purple come livello di intelligence è ben consolidato in molteplici settori verticali. McDonald's, un cliente Purple, ha ottenuto una riduzione del 90% delle visite degli ingegneri IT in loco implementando il WiFi per gli ospiti gestito in cloud con gestione centralizzata: un risparmio diretto sui costi operativi che ha finanziato l'investimento nella piattaforma entro il primo anno. L'aeroporto di Bruxelles-Sud Charleroi ha ottenuto un ROI del 10.630% dalle analitiche del WiFi per gli ospiti di Purple, grazie al miglioramento dell'esperienza dei passeggeri, all'aumento del tempo di permanenza nelle aree commerciali e a decisioni commerciali basate sui dati.
Per una tipica catena alberghiera di 40 proprietà, il modello finanziario è approssimativamente il seguente. Implementazione basata su controller: da £ 80.000 a £ 120.000 in CapEx per l'hardware del controller, più da £ 15.000 a £ 25.000 all'anno in contratti di supporto, oltre al tempo di ingegneria per la manutenzione. Implementazione gestita in cloud: £ 0 per l'hardware del controller, più da £ 8.000 a £ 15.000 all'anno in abbonamenti alla piattaforma, oltre a oneri ingegneristici significativamente ridotti. Il modello gestito in cloud raggiunge in genere il punto di pareggio entro 18-24 mesi e offre un costo totale di proprietà inferiore su un orizzonte di cinque anni.
Il valore commerciale del livello di analitica di Purple aggiunge un'ulteriore dimensione al calcolo del ROI. I dati di prima parte degli ospiti acquisiti tramite il Captive Portal di Purple (indirizzi e-mail, frequenza delle visite, dati demografici) hanno un valore commerciale diretto per campagne di marketing, iscrizione a programmi fedeltà e comunicazioni personalizzate. Le organizzazioni che integrano Purple con la propria piattaforma CRM registrano in genere un aumento dal 25 al 40% dei contatti qualificati per il marketing entro i primi dodici mesi dall'implementazione.
Ascolta il podcast Purple Technical Briefing per una panoramica audio di 10 minuti di questa guida, che copre i compromessi architetturali, le raccomandazioni per l'implementazione e una rapida sessione di domande e risposte.
Termini chiave e definizioni
Cloud-Managed WiFi
A wireless LAN architecture in which the controller function — including authentication, policy enforcement, radio frequency management, and firmware distribution — is hosted in a vendor-operated cloud platform. Access points connect to the cloud platform for configuration and monitoring, while local traffic forwarding typically remains at the access point.
IT teams encounter this term when evaluating modern WiFi platforms from vendors such as Cisco Meraki, Aruba Central, and Juniper Mist. It is the dominant deployment model for new enterprise WiFi deployments as of 2024.
On-Premise WiFi Controller (WLC)
A physical or virtual appliance deployed within the enterprise network that centrally manages all access points, handling authentication, QoS, roaming, and security policy enforcement. All management traffic remains within the enterprise network perimeter.
IT teams encounter this in legacy enterprise environments and in organisations with strict data sovereignty or compliance requirements. Major platforms include Cisco Catalyst 9800, Aruba Mobility Controller, and Ruckus SmartZone.
Zero-Touch Provisioning (ZTP)
A deployment capability that allows network devices — access points, switches, or routers — to be shipped directly to a site and automatically configured upon first connection to the network, without requiring on-site engineer intervention. The device contacts a cloud management platform, downloads its pre-staged configuration, and becomes operational.
ZTP is a primary operational advantage of cloud-managed WiFi for multi-site deployments. It eliminates the need to pre-configure devices in a staging environment or dispatch engineers to remote sites for initial setup.
IEEE 802.1X
An IEEE standard for port-based network access control that provides an authentication framework for devices connecting to a LAN or WLAN. It requires a supplicant (the connecting device), an authenticator (the access point or switch), and an authentication server (typically a RADIUS server) to complete an authentication exchange before network access is granted.
IT teams implement 802.1X for staff WiFi networks to enforce per-user authentication, typically using EAP-TLS (certificate-based) or PEAP-MSCHAPv2 (username/password) as the inner authentication method. It is required for WPA3-Enterprise deployments.
WPA3-Enterprise
The current generation of WiFi security protocol for enterprise networks, defined by the Wi-Fi Alliance. WPA3-Enterprise uses IEEE 802.1X for authentication and supports 192-bit cryptographic strength (CNSA suite) for high-security environments. It provides forward secrecy, meaning that the compromise of a long-term key does not expose past session traffic.
IT teams should be deploying WPA3-Enterprise on all new staff WiFi SSIDs where hardware supports it. All Wi-Fi 6 and Wi-Fi 6E certified access points are required to support WPA3.
Captive Portal
A web page presented to users when they connect to a WiFi network, requiring them to complete an action — accepting terms of service, entering credentials, or providing personal information — before being granted internet access. Captive portals are implemented using DNS and HTTP redirection at the network level.
IT teams deploy captive portals for guest WiFi to enforce acceptable use policies, capture user data for marketing or analytics purposes, and comply with legal requirements for identifying users on public networks. Purple provides a fully customisable, GDPR-compliant captive portal as a core product feature.
GDPR (General Data Protection Regulation)
The European Union's primary data protection regulation, effective from May 2018, which governs the collection, processing, and storage of personal data relating to EU residents. Under GDPR, organisations must have a lawful basis for processing personal data, provide transparent privacy notices, and respect data subject rights including access, rectification, and erasure.
GDPR is directly relevant to guest WiFi deployments because the collection of email addresses, device identifiers, or behavioural data via a captive portal constitutes processing of personal data. Organisations must ensure their captive portal consent flows meet GDPR requirements for valid consent under Article 7.
OpenRoaming
A Wi-Fi Alliance standard built on Passpoint (IEEE 802.11u) that enables automatic, seamless WiFi authentication across networks operated by different providers, using credentials from a user's home identity provider (mobile carrier, employer, or platform account). Users connect without a captive portal, and the network authenticates them via a federated identity exchange.
IT teams deploying guest WiFi in venues with high repeat visitor rates — airports, hotel chains, retail estates — should evaluate OpenRoaming to reduce authentication friction for returning users. Purple supports OpenRoaming natively, enabling users who have previously authenticated via the Purple App to connect automatically at any Purple-enabled venue.
PCI DSS (Payment Card Industry Data Security Standard)
A set of security standards developed by the major card networks (Visa, Mastercard, Amex, Discover) that applies to any organisation that stores, processes, or transmits payment card data. PCI DSS includes specific requirements for network segmentation, access control, encryption, and monitoring that directly affect WiFi architecture design.
IT teams at hospitality, retail, and events venues must ensure that their WiFi architecture does not bring guest or staff networks into PCI DSS scope unnecessarily. The standard approach is to isolate payment card processing systems on a dedicated, firewalled network segment that is physically and logically separated from guest WiFi traffic.
WiFi Management Platform
A software platform that provides centralised visibility, configuration management, analytics, and policy enforcement for a wireless LAN deployment. This term encompasses both the network management layer (controller or cloud platform) and the application layer (guest experience, analytics, and compliance platforms such as Purple).
IT teams use this term when evaluating the full stack of software required to operate an enterprise WiFi deployment. It is important to distinguish between the network management layer (which controls how APs operate) and the intelligence layer (which extracts business value from the network).
Casi di studio
A 45-property mid-market hotel chain is replacing end-of-life WiFi infrastructure across its estate. Properties range from 80 to 220 rooms. The IT team consists of three engineers based at head office, with no dedicated on-site IT staff at individual properties. The chain wants to capture guest email addresses for its loyalty programme and needs GDPR-compliant data handling. Budget is constrained, with a preference for OpEx over CapEx. Which WiFi architecture should they choose, and how should Purple be deployed?
This scenario is a strong fit for cloud-managed WiFi with Purple as the guest experience layer. The recommended deployment approach is as follows.
Infrastructure selection: Deploy a cloud-managed platform such as Cisco Meraki MR or Aruba Instant On across all 45 properties. Use zero-touch provisioning: pre-stage AP configurations in the cloud management portal, then ship APs directly to each property for installation by local staff or a third-party field services provider. No on-site controller hardware is required.
SSID architecture: Configure three SSIDs per property: (1) a guest SSID mapped to an internet-only VLAN, with Purple's captive portal as the splash page; (2) a staff SSID using WPA3-Enterprise with 802.1X authentication against the chain's Active Directory via a cloud RADIUS service such as Cisco ISE or JumpCloud; (3) an IoT SSID for in-room devices, isolated on a dedicated VLAN with restricted inter-device communication.
Purple deployment: Configure Purple's captive portal on the guest SSID. Implement a two-step consent flow: step one collects the guest's email address and loyalty programme opt-in; step two presents the WiFi terms of service and GDPR privacy notice with explicit consent checkboxes. Connect Purple to the chain's CRM (e.g., Salesforce) via Purple's native connector to sync guest profiles automatically.
Compliance validation: Enable Purple's data retention policies to automatically anonymise guest records after 24 months in line with the chain's data retention schedule. Configure Purple's consent audit log to satisfy GDPR Article 7(1) requirements for demonstrating valid consent.
Ongoing management: All 45 properties are managed from a single cloud dashboard. Firmware updates are pushed automatically during the 02:00–04:00 maintenance window. The three-person IT team receives automated alerts for AP offline events and can remotely diagnose and resolve most issues without travel.
A Premier League football stadium with a capacity of 62,000 seats is upgrading its WiFi infrastructure ahead of a major international tournament. The stadium hosts 25 home matches per year plus concerts and corporate events. Peak concurrent users are estimated at 18,000 during sold-out events. The stadium's IT team has five engineers on-site. Data sovereignty is a concern as the stadium processes payment card data in its hospitality suites. The stadium wants to offer free guest WiFi to all fans and capture connection data for sponsorship reporting. What architecture is recommended?
This scenario warrants a hybrid architecture with on-premise controllers for the primary network and Purple as the analytics and guest experience layer.
Infrastructure selection: Deploy a centralised on-premise wireless LAN controller cluster (e.g., Cisco Catalyst 9800 or Aruba Mobility Controller) in the stadium's data centre. Deploy Wi-Fi 6E access points (802.11ax, 6 GHz band) across the bowl, concourses, hospitality suites, and back-of-house areas — approximately 800 to 1,200 APs depending on the stadium's geometry. Use a high-density AP deployment design with directional antennas to serve seated fans without co-channel interference.
Network segmentation: Create separate VLANs for: fan guest WiFi (internet-only, Purple captive portal); hospitality suite WiFi (internet plus access to point-of-sale systems, PCI DSS scoped); staff and operations WiFi (access to stadium management systems); and broadcast and media WiFi (dedicated high-bandwidth SSID for press and broadcast teams).
PCI DSS compliance: The hospitality suite network must be isolated from the guest network and subject to PCI DSS controls including network segmentation, access logging, and quarterly vulnerability scanning. The on-premise controller architecture supports this by keeping all PCI-scoped traffic within the stadium's network perimeter.
Purple deployment: Deploy Purple's captive portal on the fan guest WiFi SSID. For a stadium environment, minimise friction: use a single-click social login or the Purple App for authentication. Configure Purple's analytics to capture per-event connection counts, peak concurrent users, and return visitor rates — the key metrics for sponsorship reporting. Integrate Purple with the stadium's sponsorship management platform via API to automate report generation.
Capacity planning: For 18,000 peak concurrent users, target a minimum of one AP per 30 to 40 concurrent users in high-density seating areas, with a throughput budget of 2 to 5 Mbps per user for typical fan usage patterns (social media, messaging, live score apps).
A national retail chain with 280 stores wants to deploy guest WiFi to capture customer data for its marketing team, while also improving store operations through WiFi-based footfall analytics. The chain's IT team manages infrastructure centrally. Stores range from small convenience formats (500 sq ft) to large superstore formats (50,000 sq ft). Some stores are in areas with limited or unreliable internet connectivity. How should the architecture be designed to handle the connectivity variability?
Architecture: Cloud-managed WiFi with local AP survivability enabled, plus Purple for guest experience and analytics.
Connectivity resilience: For stores in areas with unreliable internet connectivity, configure APs with local survivability mode — this ensures that guest WiFi continues to operate with the last-known configuration even if the cloud management connection is lost. For the most connectivity-constrained stores, consider deploying a 4G/LTE failover router as a secondary WAN link, with automatic failover triggered when the primary connection drops below a defined threshold.
Tiered AP deployment: For small convenience formats, deploy two to three APs per store. For large superstore formats, deploy 15 to 25 APs with a high-density design in checkout and food service areas. Use the cloud management platform's template-based configuration to push consistent SSID, VLAN, and security policies across all 280 stores from a single configuration template.
Purple analytics for operations: Beyond guest data capture, configure Purple's footfall analytics to measure customer dwell time in key departments, identify peak traffic periods, and compare performance across the estate. This data feeds directly into the retail operations team's workforce planning and merchandising decisions.
Data architecture: Connect Purple to the chain's CDP (Customer Data Platform) via API to merge WiFi-derived behavioural data with transactional data from the POS system, creating unified customer profiles that the marketing team can use for personalised campaigns.
Analisi degli scenari
Q1. A regional NHS trust operates 12 hospitals and 45 GP surgeries across a county. The trust's IT team of eight engineers manages all infrastructure centrally. The trust is subject to NHS Data Security and Protection Toolkit requirements and processes patient data on its clinical networks. It wants to offer free guest WiFi to patients and visitors in waiting areas, and is evaluating whether to deploy cloud-managed or controller-based WiFi. What architecture would you recommend, and what are the key compliance considerations?
💡 Suggerimento:Consider the NHS DSP Toolkit requirements around data residency and the separation between clinical and guest networks. Also consider the IT team's capacity to manage 57 sites.
Mostra l'approccio consigliato
The recommended architecture is cloud-managed WiFi for the guest network, with strict network segmentation to ensure the guest network is completely isolated from clinical systems. The 57-site scale and the small central IT team make cloud-managed WiFi the operationally superior choice — the alternative of deploying on-premise controllers at each site would require significantly more engineering resource than the team can sustain. The guest WiFi SSID should be on a dedicated VLAN with internet-only access, enforced by firewall rules that block all traffic to clinical network segments. This segmentation ensures that the guest network does not fall within the scope of NHS DSP Toolkit clinical data requirements. For data residency, select a cloud-managed platform that processes and stores data within the UK (or EEA at minimum), and verify this in the vendor's data processing agreement. Deploy Purple on the guest SSID for GDPR-compliant patient data capture, with consent flows that clearly distinguish between WiFi access (which requires minimal data) and optional marketing communications (which require explicit opt-in). The key compliance consideration is demonstrating to NHS Digital that clinical data cannot be accessed from the guest network — this requires documented network segmentation evidence, not just a policy statement.
Q2. A conference centre operator runs a single 15,000 sq metre venue that hosts 200 events per year, ranging from small boardroom meetings (20 delegates) to large exhibitions (5,000 attendees). The venue's IT team has two engineers. The operator wants to offer exhibitor-grade WiFi (dedicated bandwidth per stand) as a paid service, alongside free delegate WiFi. The venue currently has an ageing on-premise controller that is out of support. What architecture should replace it?
💡 Suggerimento:Consider the variable density requirements (20 to 5,000 users), the paid WiFi service model, and the small IT team. Also consider how Purple can support the commercial model.
Mostra l'approccio consigliato
Replace the ageing on-premise controller with a cloud-managed WiFi platform, deploying Wi-Fi 6E access points throughout the venue. The cloud-managed model suits the small IT team and eliminates the hardware maintenance burden of an on-premise controller. For the paid exhibitor WiFi service, configure dedicated SSIDs per exhibition stand using dynamic VLAN assignment, with bandwidth shaping policies enforced at the access point level — all major cloud-managed platforms support this capability. For the free delegate WiFi, deploy Purple's captive portal to capture delegate data (email, organisation, job title) with GDPR-compliant consent, creating a valuable database for the venue's marketing and event follow-up activities. Purple's analytics will also provide the venue operator with per-event attendance data, dwell time metrics, and return visitor rates — useful for commercial reporting to event organisers. The variable density requirement (20 to 5,000 users) is handled by the cloud management platform's dynamic RF management, which automatically adjusts transmit power and channel allocation based on active user density. Ensure the AP deployment design includes sufficient density for peak exhibition capacity, and validate throughput during a high-density test before the first major event.
Q3. A luxury hotel group is deploying a new WiFi estate across 8 five-star properties in Europe. Each property has 150 to 300 rooms, multiple F&B outlets, spa facilities, and conference rooms. The group's CTO wants to use WiFi data to personalise the guest experience — recognising returning guests, understanding their movement patterns within the property, and triggering personalised offers via the hotel app. The group's legal team has flagged GDPR concerns about tracking guest movements. How should the architecture be designed to achieve the commercial objective while remaining GDPR-compliant?
💡 Suggerimento:Consider the distinction between network-level data (which device is connected to which AP) and personal data (which guest is connected). GDPR compliance depends on the consent basis and the data minimisation principle.
Mostra l'approccio consigliato
Deploy cloud-managed WiFi across all 8 properties with Purple as the guest intelligence layer. The GDPR compliance framework requires careful design of the consent and data architecture. At the point of WiFi authentication via Purple's captive portal, present guests with a layered consent notice: the first layer covers basic WiFi access (minimal data, legitimate interest basis); the second layer, presented as an optional enhancement, covers personalised services including movement analytics and targeted offers (explicit consent basis, clearly described). Guests who consent to personalised services have their device's WiFi probe data associated with their guest profile, enabling movement pattern analysis. Guests who do not consent receive standard WiFi access without tracking. This approach satisfies GDPR's requirement for granular, informed consent and the data minimisation principle (only collecting movement data from guests who have explicitly consented). Purple's consent management framework records consent timestamps and scope for each guest, providing the audit trail required under GDPR Article 7. The hotel app integration allows consenting guests to receive personalised offers triggered by their location within the property — for example, a spa offer when they are near the spa entrance. The legal team should review the privacy notice language to ensure the description of movement analytics is sufficiently clear and specific to constitute valid informed consent.
Punti chiave
- ✓Cloud-managed WiFi is operationally superior for multi-site deployments (5+ sites) due to zero-touch provisioning, automatic firmware updates, and single-pane-of-glass management — typically delivering lower total cost of ownership than on-premise controllers within 18 to 24 months.
- ✓Controller-based WiFi remains the right choice for large single-campus deployments with strict data sovereignty requirements, PCI DSS scope concerns, or the need for advanced features such as granular QoS and real-time RF optimisation.
- ✓Purple operates as an infrastructure-agnostic WiFi intelligence overlay — it integrates with both cloud-managed and controller-based architectures, adding GDPR-compliant guest data capture, footfall analytics, and CRM integration without requiring changes to the underlying network infrastructure.
- ✓GDPR compliance for guest WiFi is non-negotiable and applies regardless of network architecture: consent must be explicit, granular, and recorded before any personal data is processed. Purple's consent management framework addresses this requirement out of the box.
- ✓Security best practice for any enterprise WiFi deployment requires WPA3-Enterprise on staff networks, strict VLAN segmentation between guest, staff, and IoT traffic, and a documented firmware management process — automated in cloud-managed deployments, scheduled quarterly in on-premise deployments.
- ✓The commercial ROI of guest WiFi analytics is well-evidenced: Purple customers including McDonald's (90% reduction in IT engineer site visits) and Brussels South Charleroi Airport (10,630% ROI) demonstrate that WiFi intelligence delivers measurable business value beyond connectivity.
- ✓Avoid the hybrid trap: if you must operate both cloud-managed and controller-based infrastructure, define explicit criteria for each deployment type and ensure your monitoring and security operations tools can span both environments — unmanaged architectural complexity erodes the cost savings you were trying to achieve.



