WiFi géré dans le cloud vs WiFi basé sur contrôleur : Lequel choisir ?
This guide provides a vendor-neutral technical comparison of cloud-managed WiFi and controller-based (on-premise) WiFi architectures, helping IT managers, network architects, and CTOs make an informed deployment decision. It covers the architectural trade-offs across scalability, data sovereignty, cost model, and offline resilience, with real-world case studies from hospitality, retail, and public-sector environments. It also explains how Purple's WiFi intelligence platform integrates with either architecture to deliver guest experience management, first-party data capture, and GDPR-compliant analytics.
🎧 Écouter ce guide
Voir la transcription
- Synthèse
- Analyse technique approfondie
- Qu'est-ce que le WiFi géré dans le cloud ?
- Qu'est-ce que le WiFi basé sur contrôleur ?
- Compromis architecturaux : Une comparaison structurée
- Considérations sur l'architecture de sécurité
- Comment Purple s'intègre aux deux architectures
- Guide de mise en œuvre
- Étape 1 : Définir votre profil d'exigences
- Étape 2 : Sélectionner votre modèle d'architecture
- Étape 3 : Évaluer les fournisseurs réseau
- Étape 4 : Déployer Purple comme couche d'intelligence
- Étape 5 : Valider la conformité et la sécurité
- Bonnes pratiques
- Dépannage et atténuation des risques
- ROI et impact commercial

Synthèse
Le choix entre un WiFi géré dans le cloud et un WiFi basé sur contrôleur est l'une des décisions architecturales les plus lourdes de conséquences qu'une équipe réseau aura à prendre au cours de cette décennie. Les deux modèles offrent une connectivité sans fil de niveau entreprise, mais ils diffèrent fondamentalement sur l'emplacement de l'intelligence, leur évolutivité, leur coût sur le long terme et leur gestion des obligations de conformité.
Le WiFi géré dans le cloud déplace la fonction de contrôleur vers une plateforme cloud hébergée par le fournisseur, permettant un provisionnement sans intervention (zero-touch), des mises à jour automatiques des firmwares et une gestion centralisée (single-pane-of-glass) sur un nombre illimité de sites. Le WiFi basé sur contrôleur conserve cette intelligence sur site (on-premise), offrant une souveraineté maximale des données, une résilience hors ligne et un contrôle granulaire — au prix de dépenses d'investissement (CapEx) plus élevées et d'une charge opérationnelle accrue.
Pour la plupart des opérateurs multi-sites — chaînes hôtelières, réseaux de distribution, exploitants de stades et collectivités locales — le WiFi géré dans le cloud représente désormais le choix le plus performant sur le plan opérationnel. Pour les déploiements sur de grands campus uniques avec des exigences strictes en matière de résidence des données, les contrôleurs sur site restent pertinents. Dans les deux cas, la plateforme de gestion WiFi de Purple fonctionne comme une surcouche agnostique vis-à-vis de l'infrastructure, ajoutant la gestion de l'expérience client, la capture de données conforme au GDPR et des analyses exploitables, quelle que soit l'architecture choisie.
Analyse technique approfondie
Qu'est-ce que le WiFi géré dans le cloud ?
Le WiFi géré dans le cloud est une architecture LAN sans fil dans laquelle la fonction de contrôleur — authentification, application des politiques, gestion des fréquences radio, distribution des firmwares et surveillance — est hébergée sur une plateforme cloud exploitée par le fournisseur plutôt que sur du matériel dédié sur site. Les points d'accès des sites locaux se connectent à la plateforme de gestion cloud via des tunnels HTTPS ou CAPWAP chiffrés, recevant leur configuration et envoyant des données de télémétrie en amont. Le plan de données — le transfert réel du trafic utilisateur — reste généralement local au niveau du point d'accès, garantissant qu'une panne du WAN n'interrompt pas les sessions utilisateurs actives.
Les principales plateformes de WiFi géré dans le cloud incluent Cisco Meraki, Aruba Central (HPE), Juniper Mist, Extreme Networks CloudIQ et Ruckus One. Chaque plateforme fournit une console de gestion web, une API RESTful pour l'intégration avec des systèmes tiers, ainsi que différents niveaux d'optimisation RF et de détection d'anomalies basés sur l'IA.
Qu'est-ce que le WiFi basé sur contrôleur ?
Le WiFi basé sur contrôleur est l'architecture sans fil d'entreprise traditionnelle dans laquelle un contrôleur LAN sans fil (WLC) physique ou virtuel est déployé sur site pour gérer tous les points d'accès d'un site ou d'un campus. Le contrôleur gère l'authentification IEEE 802.1X via RADIUS, applique les politiques de QoS et de sécurité, gère l'itinérance rapide (fast roaming) entre les points d'accès (IEEE 802.11r) et fournit une surveillance et un dépannage centralisés. Dans une configuration de tunnel fractionné (split-tunnel) ou de commutation locale, le trafic utilisateur est transféré localement au niveau du point d'accès ; dans une configuration de commutation centralisée, tout le trafic est tunnelisé vers le contrôleur.
Les principales plateformes basées sur contrôleur incluent Cisco Catalyst Wireless (anciennement AireOS), Aruba Mobility Controllers, Juniper Mist avec des contrôleurs virtuels sur site, et Ruckus SmartZone. Ces plateformes sont matures, riches en fonctionnalités et largement déployées dans les environnements d'entreprise, de santé et du secteur public.
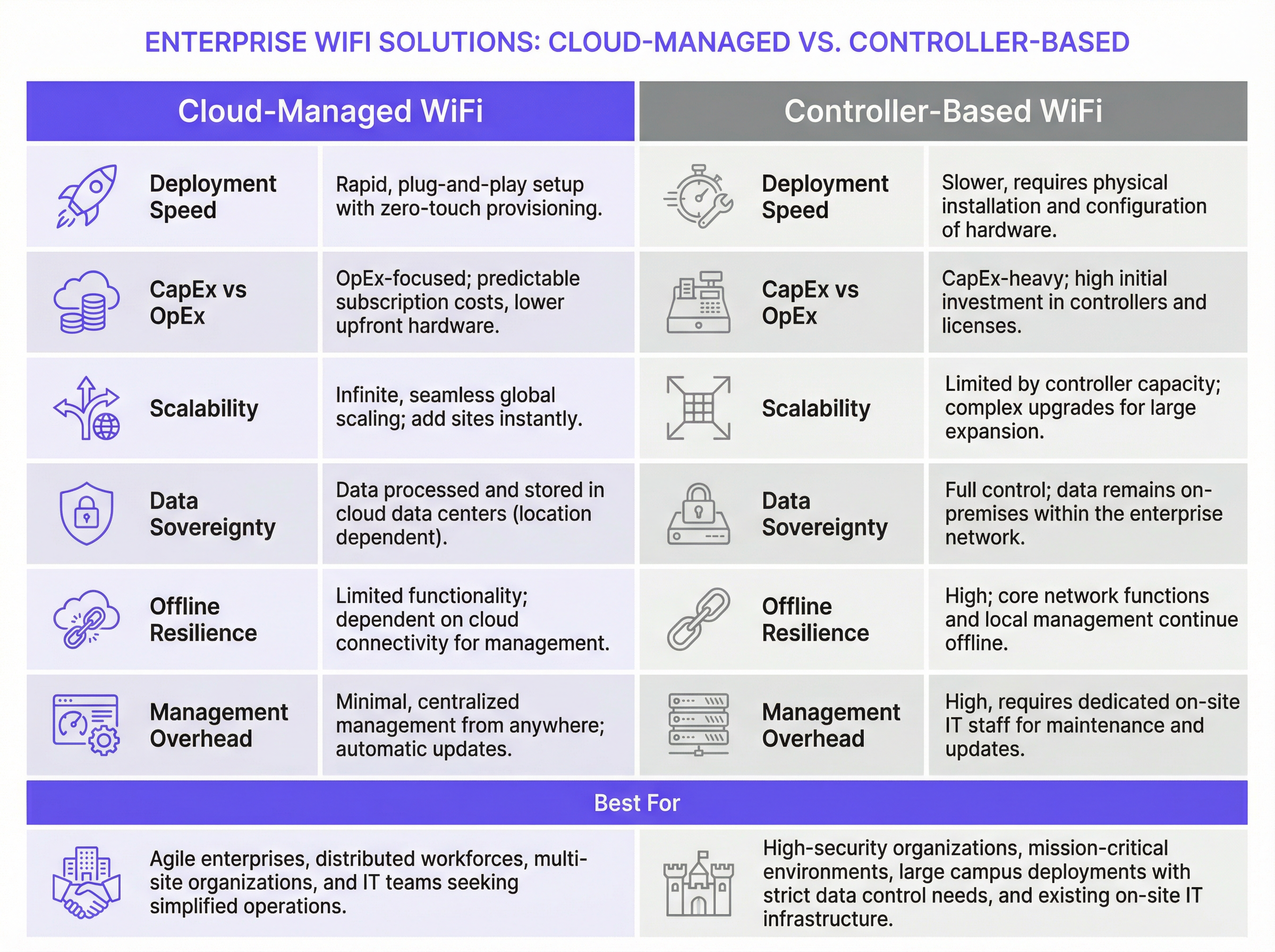
Compromis architecturaux : Une comparaison structurée
| Dimension | WiFi géré dans le cloud | WiFi basé sur contrôleur |
|---|---|---|
| Vitesse de déploiement | Rapide ; provisionnement zero-touch via une configuration pré-établie des points d'accès | Plus lente ; nécessite l'installation d'un contrôleur sur site et l'enregistrement des points d'accès |
| Modèle de coûts | Dominante OpEx ; licences par abonnement par point d'accès | Dominante CapEx ; achat de matériel et contrats de support annuels |
| Évolutivité | Pratiquement illimitée ; ajout de sites sans modification matérielle | Limitée par la capacité du contrôleur ; nécessite des mises à niveau matérielles pour évoluer |
| Résilience hors ligne | Le transfert du trafic local continue ; perte de l'accès à la gestion | Fonctionnalités complètes de gestion et du plan de données maintenues localement |
| Souveraineté des données | Données de gestion traitées dans le cloud (selon la région) | Toutes les données restent dans le périmètre du réseau d'entreprise |
| Gestion des firmwares | Mises à jour automatiques gérées par le fournisseur | Manuelle ou planifiée ; nécessite la supervision de l'équipe informatique |
| Fonctionnalités avancées | Amélioration rapide ; optimisation RF basée sur l'IA disponible | Matures ; QoS avancée, services de localisation et granularité des politiques |
| Gestion multi-sites | Interface centralisée (single pane of glass) native pour tous les sites | Nécessite des outils NOC supplémentaires ou une gestion par site |
| Charge informatique | Faible ; expertise sur site minimale requise | Élevée ; nécessite des ingénieurs réseau sans fil qualifiés pour la maintenance |
Considérations sur l'architecture de sécurité
Les deux architectures prennent en charge les normes de sécurité de niveau entreprise. Le WPA3-Enterprise avec authentification IEEE 802.1X est disponible sur toutes les plateformes modernes gérées dans le cloud et basées sur contrôleur. L'intégration RADIUS pour l'authentification centralisée est standard dans les deux modèles. La segmentation VLAN pour isoler le trafic des invités, du personnel et de l'IoT est prise en charge par tous les principaux fournisseurs.
La principale distinction en matière de sécurité réside dans le plan de gestion. Dans un déploiement basé sur contrôleur, tout le trafic de gestion reste dans le périmètre de votre réseau, ce qui constitue un avantage significatif pour les organisations soumises à la norme PCI DSS (qui exige des contrôles stricts sur les environnements de données des titulaires de cartes) ou aux exigences de certification ISO 27001. Dans un déploiement géré dans le cloud, le trafic de gestion transite par l'Internet public — bien qu'il soit chiffré — et votre posture de sécurité dépend en partie des propres contrôles de sécurité et certifications du fournisseur cloud.
Pour le WiFi invité en particulier, la conformité au GDPR exige que toute donnée personnelle collectée via un Captive Portal — y compris les adresses e-mail, les jetons de connexion sociale ou les identifiants d'appareils — soit capturée avec un consentement explicite et éclairé, stockée de manière sécurisée et soumise aux droits des personnes concernées, y compris l'accès et l'effacement. Cette obligation s'applique que votre réseau sous-jacent soit géré dans le cloud ou basé sur contrôleur. Le cadre de gestion du consentement de Purple répond directement à cette exigence, en fournissant des registres de consentement horodatés, des politiques automatisées de conservation des données et un portail en libre-service pour les demandes des personnes concernées.
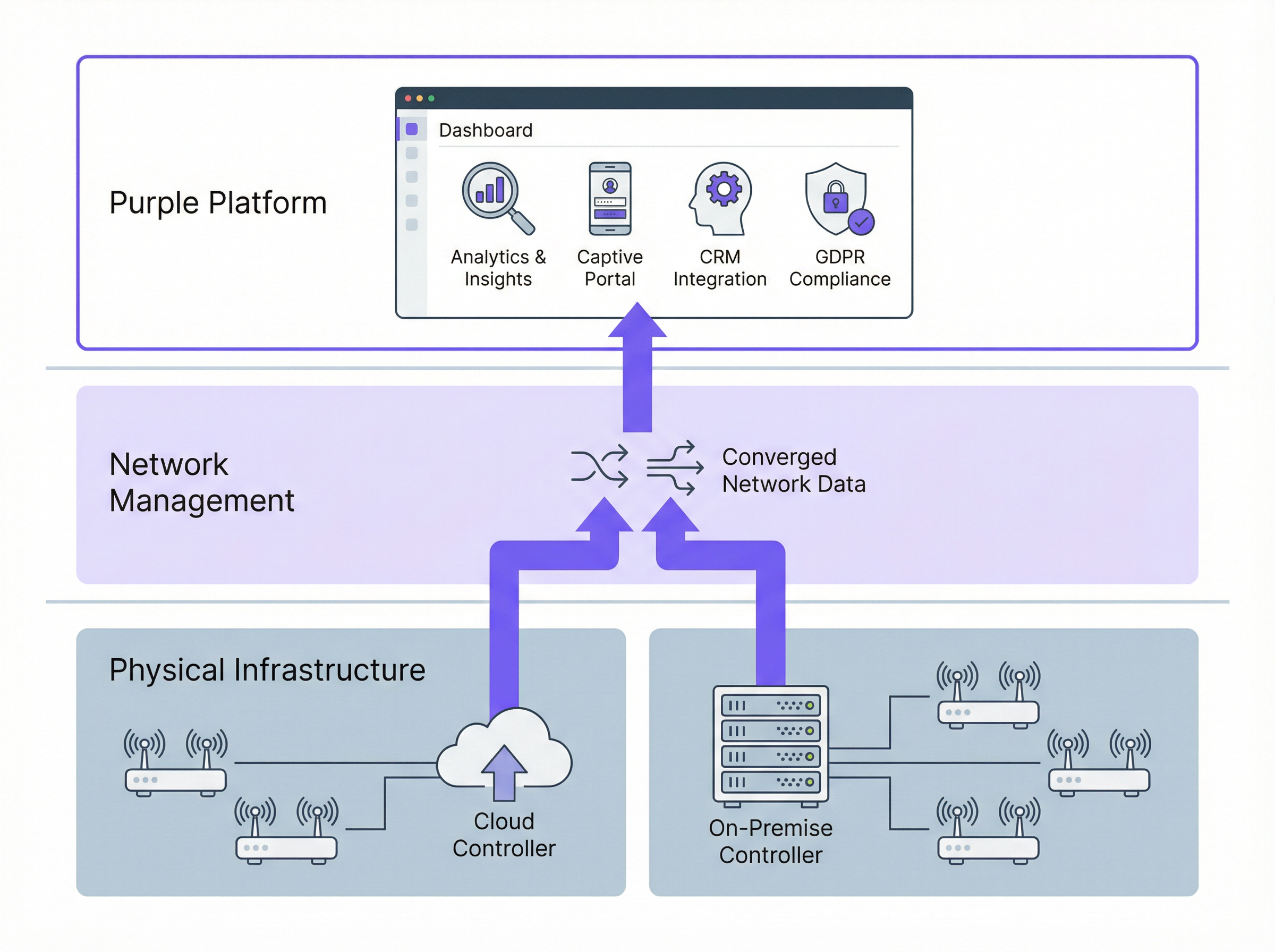
Comment Purple s'intègre aux deux architectures
Purple fonctionne comme une surcouche d'intelligence WiFi — il ne remplace pas votre fournisseur réseau, mais l'enrichit d'une couche d'expérience client et d'analyse. Purple se connecte à votre infrastructure réseau via des API standards et une intégration RADIUS, que vos points d'accès soient gérés par une plateforme cloud ou un contrôleur sur site.
Pour le WiFi invité, Purple fournit un Captive Portal personnalisable qui gère l'authentification des utilisateurs (connexion sociale, e-mail, vérification par SMS ou l'application Purple), la capture du consentement conforme au GDPR et un transfert transparent vers le réseau. Pour le WiFi du personnel, les capacités de mise en réseau basées sur l'identité de Purple permettent le provisionnement et la révocation automatiques des accès liés à votre système RH ou de gestion des identités — garantissant que l'accès au réseau d'un employé sur le départ est résilié sans intervention manuelle.
La plateforme d'analyse de Purple traite ensuite les données de connexion pour générer des indicateurs de fréquentation, des analyses de temps de présence, des ratios de nouveaux visiteurs par rapport aux visiteurs récurrents et des informations démographiques. Ces analyses sont disponibles via le tableau de bord de Purple, via une intégration API avec vos outils de Business Intelligence, ou via des connecteurs CRM directs vers des plateformes telles que Salesforce, HubSpot et Microsoft Dynamics.
Guide de mise en œuvre
Étape 1 : Définir votre profil d'exigences
Avant d'évaluer les fournisseurs, documentez vos exigences selon cinq dimensions : nombre et répartition des sites (campus unique vs parc multi-sites) ; obligations de conformité (GDPR, PCI DSS, exigences de résidence des données) ; capacité de l'équipe informatique (pouvez-vous prendre en charge du matériel sur site pour chaque emplacement ?) ; objectifs commerciaux (avez-vous besoin de capturer des données invités et d'obtenir des analyses ?) ; et modèle budgétaire (préférence pour le CapEx ou l'OpEx).
Étape 2 : Sélectionner votre modèle d'architecture
Appliquez la logique de décision suivante. Si vous exploitez plus de cinq sites géographiquement répartis, le WiFi géré dans le cloud est presque certainement le bon choix pour votre couche d'accès — les économies opérationnelles découlant de la gestion centralisée et du provisionnement zero-touch compenseront les coûts d'abonnement dans un délai de douze à dix-huit mois. Si vous exploitez un grand campus unique avec des exigences strictes en matière de souveraineté des données, évaluez les contrôleurs sur site, y compris les options de contrôleurs virtuels qui réduisent le CapEx matériel. Si vous avez un mélange de types de sites, envisagez un modèle hybride délibéré avec des critères clairement définis pour chaque type de déploiement.
Étape 3 : Évaluer les fournisseurs réseau
Émettez un appel d'offres (RFP) structuré couvrant : les spécifications matérielles des points d'accès (prise en charge du Wi-Fi 6E, conception des antennes, exigences PoE) ; les capacités de la plateforme de gestion (exhaustivité de l'API, surveillance, alertes) ; les certifications de sécurité (SOC 2 Type II pour les plateformes cloud, ISO 27001) ; les engagements SLA (garanties de disponibilité, temps de réponse du support) ; et l'écosystème d'intégration (RADIUS, VLAN, API de plateformes tierces).
Étape 4 : Déployer Purple comme couche d'intelligence
Une fois votre infrastructure réseau sélectionnée, déployez Purple pour ajouter la gestion de l'expérience client et les analyses. Le processus de déploiement de Purple implique : la configuration d'un SSID invité dédié sur votre infrastructure réseau ; la redirection de la page d'accueil du SSID ou de l'authentification RADIUS vers la plateforme cloud de Purple ; la personnalisation du Captive Portal avec votre identité de marque et vos flux de consentement ; et la connexion de Purple à vos plateformes CRM et d'automatisation du marketing via la marketplace d'intégrations.
Étape 5 : Valider la conformité et la sécurité
Avant la mise en production, effectuez un examen de conformité couvrant : la validation du flux de consentement GDPR (assurez-vous que le consentement est explicite, granulaire et enregistré) ; la vérification de la segmentation du réseau (confirmez que le trafic invité ne peut pas atteindre les systèmes internes) ; l'évaluation de la portée PCI DSS (si des données de cartes de paiement sont traitées n'importe où sur le réseau) ; et des tests d'intrusion de l'environnement WiFi invité.
Bonnes pratiques
Segmentez de manière agressive. Déployez toujours des SSID distincts pour les invités, le personnel et les appareils IoT, chacun mappé à un VLAN dédié avec des politiques de pare-feu appropriées. Le trafic invité doit être isolé des systèmes internes par défaut, avec un accès Internet uniquement, à moins qu'une exigence métier spécifique ne justifie le contraire.
Appliquez le WPA3 là où le matériel le prend en charge. Les points d'accès Wi-Fi 6 et Wi-Fi 6E prennent universellement en charge le WPA3. Pour les réseaux invités, le WPA3-Personal avec authentification simultanée des égaux (SAE) offre une protection nettement plus forte contre les attaques par dictionnaire hors ligne que le WPA2-PSK. Pour les réseaux du personnel, le WPA3-Enterprise avec 802.1X fournit une authentification par utilisateur et une confidentialité persistante (forward secrecy).
Prévoyez l'OpenRoaming. La norme OpenRoaming de la Wi-Fi Alliance, basée sur Passpoint (IEEE 802.11u), permet aux utilisateurs de se connecter automatiquement à n'importe quel réseau compatible OpenRoaming en utilisant les identifiants de leur fournisseur d'identité d'origine — leur opérateur mobile, leur employeur ou une plateforme comme l'application Purple. Le déploiement d'OpenRoaming élimine les frictions liées au Captive Portal pour les utilisateurs récurrents tout en maintenant un accès authentifié et sécurisé. Purple prend en charge OpenRoaming de manière native.
Automatisez la gestion des firmwares. Les firmwares non corrigés constituent l'un des vecteurs d'attaque les plus courants dans les déploiements WiFi d'entreprise. Les plateformes gérées dans le cloud s'en chargent automatiquement ; pour les déploiements sur site, établissez un cycle d'examen trimestriel des firmwares et utilisez la fonctionnalité de mise à jour planifiée de votre contrôleur pour déployer les mises à jour pendant les fenêtres de maintenance.
Surveillez en continu. Déployez les capacités WIDS (Wireless Intrusion Detection System), disponibles sur toutes les principales plateformes d'entreprise, pour détecter les points d'accès malveillants, les attaques par désauthentification et les attaques de type « evil twin ». Intégrez les alertes WIDS à votre plateforme SIEM pour une surveillance de sécurité centralisée.
Dépannage et atténuation des risques
Risque : Panne de la plateforme de gestion cloud. Atténuation : Vérifiez que la plateforme choisie prend en charge la survie locale des points d'accès (AP survivability) — la capacité des points d'accès à continuer de fonctionner avec leur dernière configuration connue en cas de perte de connectivité cloud. Toutes les grandes plateformes cloud (Meraki, Aruba Central, Juniper Mist) prennent en charge cette capacité. Testez-la explicitement lors de votre phase de tests d'acceptation.
Risque : Non-conformité au GDPR dans la capture des données invités. Atténuation : Utilisez une plateforme comme Purple qui fournit un cadre de gestion du consentement pré-intégré et validé juridiquement. Évitez de créer des Captive Portals personnalisés sans examen juridique — le langage spécifique, la granularité et les exigences d'enregistrement pour le consentement GDPR sont précis et fréquemment mal mis en œuvre.
Risque : Défaillance matérielle du contrôleur dans les déploiements sur site. Atténuation : Déployez les contrôleurs en paires à haute disponibilité avec basculement automatique. Pour les contrôleurs virtuels, assurez-vous que l'infrastructure de l'hyperviseur sous-jacent dispose d'une redondance appropriée. Documentez votre objectif de temps de récupération (RTO) et testez les procédures de basculement chaque année.
Risque : Bande passante WAN insuffisante pour la gestion cloud. Atténuation : Le trafic de gestion cloud est généralement modeste — un à deux mégabits par seconde pour cent points d'accès — mais connaît des pics lors des mises à jour de firmwares. Planifiez les mises à jour de firmwares pendant les heures creuses et utilisez des politiques de QoS pour prioriser le trafic de gestion par rapport aux données invités si la bande passante WAN est limitée.
Risque : Dépendance vis-à-vis du fournisseur (Vendor lock-in). Atténuation : Évaluez l'ouverture de l'API de la plateforme choisie et sa prise en charge des normes neutres (RADIUS, 802.1X, marquage VLAN). L'architecture agnostique de Purple signifie que vous pouvez changer de fournisseur réseau sous-jacent sans perdre vos données invités, votre historique d'analyses ou vos intégrations CRM.
ROI et impact commercial
L'analyse de rentabilisation du WiFi géré dans le cloud avec Purple comme couche d'intelligence est bien établie dans de multiples secteurs verticaux. McDonald's, un client de Purple, a obtenu une réduction de 90 % des visites d'ingénieurs informatiques sur site en déployant un WiFi invité géré dans le cloud avec une gestion centralisée — une économie de coûts opérationnels directe qui a financé l'investissement de la plateforme dès la première année. L'aéroport de Charleroi Bruxelles-Sud a atteint un ROI de 10 630 % grâce aux analyses du WiFi invité de Purple, portées par une expérience passager améliorée, un temps de présence accru dans les zones commerciales et des décisions commerciales basées sur les données.
Pour un parc hôtelier typique de 40 établissements, le modèle financier se présente approximativement comme suit. Déploiement basé sur contrôleur : 80 000 £ à 120 000 £ en CapEx matériel pour les contrôleurs, plus 15 000 £ à 25 000 £ par an en contrats de support, plus le temps d'ingénierie pour la maintenance. Déploiement géré dans le cloud : 0 £ de matériel pour les contrôleurs, plus 8 000 £ à 15 000 £ par an en abonnements à la plateforme, plus des frais d'ingénierie considérablement réduits. Le modèle géré dans le cloud atteint généralement le seuil de rentabilité dans les 18 à 24 mois et offre un coût total de possession inférieur sur un horizon de cinq ans.
La valeur commerciale de la couche d'analyse de Purple ajoute une dimension supplémentaire au calcul du ROI. Les données invités de première main (first-party data) capturées via le Captive Portal de Purple — adresses e-mail, fréquence des visites, données démographiques — ont une valeur commerciale directe pour les campagnes marketing, l'inscription aux programmes de fidélité et les communications personnalisées. Les organisations qui intègrent Purple à leur plateforme CRM signalent généralement une augmentation de 25 à 40 % des contacts qualifiés pour le marketing au cours des douze premiers mois de déploiement.
Écoutez le podcast Purple Technical Briefing pour une présentation audio de 10 minutes de ce guide, couvrant les compromis architecturaux, les recommandations de mise en œuvre et une session de questions-réponses rapide.
Termes clés et définitions
Cloud-Managed WiFi
A wireless LAN architecture in which the controller function — including authentication, policy enforcement, radio frequency management, and firmware distribution — is hosted in a vendor-operated cloud platform. Access points connect to the cloud platform for configuration and monitoring, while local traffic forwarding typically remains at the access point.
IT teams encounter this term when evaluating modern WiFi platforms from vendors such as Cisco Meraki, Aruba Central, and Juniper Mist. It is the dominant deployment model for new enterprise WiFi deployments as of 2024.
On-Premise WiFi Controller (WLC)
A physical or virtual appliance deployed within the enterprise network that centrally manages all access points, handling authentication, QoS, roaming, and security policy enforcement. All management traffic remains within the enterprise network perimeter.
IT teams encounter this in legacy enterprise environments and in organisations with strict data sovereignty or compliance requirements. Major platforms include Cisco Catalyst 9800, Aruba Mobility Controller, and Ruckus SmartZone.
Zero-Touch Provisioning (ZTP)
A deployment capability that allows network devices — access points, switches, or routers — to be shipped directly to a site and automatically configured upon first connection to the network, without requiring on-site engineer intervention. The device contacts a cloud management platform, downloads its pre-staged configuration, and becomes operational.
ZTP is a primary operational advantage of cloud-managed WiFi for multi-site deployments. It eliminates the need to pre-configure devices in a staging environment or dispatch engineers to remote sites for initial setup.
IEEE 802.1X
An IEEE standard for port-based network access control that provides an authentication framework for devices connecting to a LAN or WLAN. It requires a supplicant (the connecting device), an authenticator (the access point or switch), and an authentication server (typically a RADIUS server) to complete an authentication exchange before network access is granted.
IT teams implement 802.1X for staff WiFi networks to enforce per-user authentication, typically using EAP-TLS (certificate-based) or PEAP-MSCHAPv2 (username/password) as the inner authentication method. It is required for WPA3-Enterprise deployments.
WPA3-Enterprise
The current generation of WiFi security protocol for enterprise networks, defined by the Wi-Fi Alliance. WPA3-Enterprise uses IEEE 802.1X for authentication and supports 192-bit cryptographic strength (CNSA suite) for high-security environments. It provides forward secrecy, meaning that the compromise of a long-term key does not expose past session traffic.
IT teams should be deploying WPA3-Enterprise on all new staff WiFi SSIDs where hardware supports it. All Wi-Fi 6 and Wi-Fi 6E certified access points are required to support WPA3.
Captive Portal
A web page presented to users when they connect to a WiFi network, requiring them to complete an action — accepting terms of service, entering credentials, or providing personal information — before being granted internet access. Captive portals are implemented using DNS and HTTP redirection at the network level.
IT teams deploy captive portals for guest WiFi to enforce acceptable use policies, capture user data for marketing or analytics purposes, and comply with legal requirements for identifying users on public networks. Purple provides a fully customisable, GDPR-compliant captive portal as a core product feature.
GDPR (General Data Protection Regulation)
The European Union's primary data protection regulation, effective from May 2018, which governs the collection, processing, and storage of personal data relating to EU residents. Under GDPR, organisations must have a lawful basis for processing personal data, provide transparent privacy notices, and respect data subject rights including access, rectification, and erasure.
GDPR is directly relevant to guest WiFi deployments because the collection of email addresses, device identifiers, or behavioural data via a captive portal constitutes processing of personal data. Organisations must ensure their captive portal consent flows meet GDPR requirements for valid consent under Article 7.
OpenRoaming
A Wi-Fi Alliance standard built on Passpoint (IEEE 802.11u) that enables automatic, seamless WiFi authentication across networks operated by different providers, using credentials from a user's home identity provider (mobile carrier, employer, or platform account). Users connect without a captive portal, and the network authenticates them via a federated identity exchange.
IT teams deploying guest WiFi in venues with high repeat visitor rates — airports, hotel chains, retail estates — should evaluate OpenRoaming to reduce authentication friction for returning users. Purple supports OpenRoaming natively, enabling users who have previously authenticated via the Purple App to connect automatically at any Purple-enabled venue.
PCI DSS (Payment Card Industry Data Security Standard)
A set of security standards developed by the major card networks (Visa, Mastercard, Amex, Discover) that applies to any organisation that stores, processes, or transmits payment card data. PCI DSS includes specific requirements for network segmentation, access control, encryption, and monitoring that directly affect WiFi architecture design.
IT teams at hospitality, retail, and events venues must ensure that their WiFi architecture does not bring guest or staff networks into PCI DSS scope unnecessarily. The standard approach is to isolate payment card processing systems on a dedicated, firewalled network segment that is physically and logically separated from guest WiFi traffic.
WiFi Management Platform
A software platform that provides centralised visibility, configuration management, analytics, and policy enforcement for a wireless LAN deployment. This term encompasses both the network management layer (controller or cloud platform) and the application layer (guest experience, analytics, and compliance platforms such as Purple).
IT teams use this term when evaluating the full stack of software required to operate an enterprise WiFi deployment. It is important to distinguish between the network management layer (which controls how APs operate) and the intelligence layer (which extracts business value from the network).
Études de cas
A 45-property mid-market hotel chain is replacing end-of-life WiFi infrastructure across its estate. Properties range from 80 to 220 rooms. The IT team consists of three engineers based at head office, with no dedicated on-site IT staff at individual properties. The chain wants to capture guest email addresses for its loyalty programme and needs GDPR-compliant data handling. Budget is constrained, with a preference for OpEx over CapEx. Which WiFi architecture should they choose, and how should Purple be deployed?
This scenario is a strong fit for cloud-managed WiFi with Purple as the guest experience layer. The recommended deployment approach is as follows.
Infrastructure selection: Deploy a cloud-managed platform such as Cisco Meraki MR or Aruba Instant On across all 45 properties. Use zero-touch provisioning: pre-stage AP configurations in the cloud management portal, then ship APs directly to each property for installation by local staff or a third-party field services provider. No on-site controller hardware is required.
SSID architecture: Configure three SSIDs per property: (1) a guest SSID mapped to an internet-only VLAN, with Purple's captive portal as the splash page; (2) a staff SSID using WPA3-Enterprise with 802.1X authentication against the chain's Active Directory via a cloud RADIUS service such as Cisco ISE or JumpCloud; (3) an IoT SSID for in-room devices, isolated on a dedicated VLAN with restricted inter-device communication.
Purple deployment: Configure Purple's captive portal on the guest SSID. Implement a two-step consent flow: step one collects the guest's email address and loyalty programme opt-in; step two presents the WiFi terms of service and GDPR privacy notice with explicit consent checkboxes. Connect Purple to the chain's CRM (e.g., Salesforce) via Purple's native connector to sync guest profiles automatically.
Compliance validation: Enable Purple's data retention policies to automatically anonymise guest records after 24 months in line with the chain's data retention schedule. Configure Purple's consent audit log to satisfy GDPR Article 7(1) requirements for demonstrating valid consent.
Ongoing management: All 45 properties are managed from a single cloud dashboard. Firmware updates are pushed automatically during the 02:00–04:00 maintenance window. The three-person IT team receives automated alerts for AP offline events and can remotely diagnose and resolve most issues without travel.
A Premier League football stadium with a capacity of 62,000 seats is upgrading its WiFi infrastructure ahead of a major international tournament. The stadium hosts 25 home matches per year plus concerts and corporate events. Peak concurrent users are estimated at 18,000 during sold-out events. The stadium's IT team has five engineers on-site. Data sovereignty is a concern as the stadium processes payment card data in its hospitality suites. The stadium wants to offer free guest WiFi to all fans and capture connection data for sponsorship reporting. What architecture is recommended?
This scenario warrants a hybrid architecture with on-premise controllers for the primary network and Purple as the analytics and guest experience layer.
Infrastructure selection: Deploy a centralised on-premise wireless LAN controller cluster (e.g., Cisco Catalyst 9800 or Aruba Mobility Controller) in the stadium's data centre. Deploy Wi-Fi 6E access points (802.11ax, 6 GHz band) across the bowl, concourses, hospitality suites, and back-of-house areas — approximately 800 to 1,200 APs depending on the stadium's geometry. Use a high-density AP deployment design with directional antennas to serve seated fans without co-channel interference.
Network segmentation: Create separate VLANs for: fan guest WiFi (internet-only, Purple captive portal); hospitality suite WiFi (internet plus access to point-of-sale systems, PCI DSS scoped); staff and operations WiFi (access to stadium management systems); and broadcast and media WiFi (dedicated high-bandwidth SSID for press and broadcast teams).
PCI DSS compliance: The hospitality suite network must be isolated from the guest network and subject to PCI DSS controls including network segmentation, access logging, and quarterly vulnerability scanning. The on-premise controller architecture supports this by keeping all PCI-scoped traffic within the stadium's network perimeter.
Purple deployment: Deploy Purple's captive portal on the fan guest WiFi SSID. For a stadium environment, minimise friction: use a single-click social login or the Purple App for authentication. Configure Purple's analytics to capture per-event connection counts, peak concurrent users, and return visitor rates — the key metrics for sponsorship reporting. Integrate Purple with the stadium's sponsorship management platform via API to automate report generation.
Capacity planning: For 18,000 peak concurrent users, target a minimum of one AP per 30 to 40 concurrent users in high-density seating areas, with a throughput budget of 2 to 5 Mbps per user for typical fan usage patterns (social media, messaging, live score apps).
A national retail chain with 280 stores wants to deploy guest WiFi to capture customer data for its marketing team, while also improving store operations through WiFi-based footfall analytics. The chain's IT team manages infrastructure centrally. Stores range from small convenience formats (500 sq ft) to large superstore formats (50,000 sq ft). Some stores are in areas with limited or unreliable internet connectivity. How should the architecture be designed to handle the connectivity variability?
Architecture: Cloud-managed WiFi with local AP survivability enabled, plus Purple for guest experience and analytics.
Connectivity resilience: For stores in areas with unreliable internet connectivity, configure APs with local survivability mode — this ensures that guest WiFi continues to operate with the last-known configuration even if the cloud management connection is lost. For the most connectivity-constrained stores, consider deploying a 4G/LTE failover router as a secondary WAN link, with automatic failover triggered when the primary connection drops below a defined threshold.
Tiered AP deployment: For small convenience formats, deploy two to three APs per store. For large superstore formats, deploy 15 to 25 APs with a high-density design in checkout and food service areas. Use the cloud management platform's template-based configuration to push consistent SSID, VLAN, and security policies across all 280 stores from a single configuration template.
Purple analytics for operations: Beyond guest data capture, configure Purple's footfall analytics to measure customer dwell time in key departments, identify peak traffic periods, and compare performance across the estate. This data feeds directly into the retail operations team's workforce planning and merchandising decisions.
Data architecture: Connect Purple to the chain's CDP (Customer Data Platform) via API to merge WiFi-derived behavioural data with transactional data from the POS system, creating unified customer profiles that the marketing team can use for personalised campaigns.
Analyse de scénario
Q1. A regional NHS trust operates 12 hospitals and 45 GP surgeries across a county. The trust's IT team of eight engineers manages all infrastructure centrally. The trust is subject to NHS Data Security and Protection Toolkit requirements and processes patient data on its clinical networks. It wants to offer free guest WiFi to patients and visitors in waiting areas, and is evaluating whether to deploy cloud-managed or controller-based WiFi. What architecture would you recommend, and what are the key compliance considerations?
💡 Astuce :Consider the NHS DSP Toolkit requirements around data residency and the separation between clinical and guest networks. Also consider the IT team's capacity to manage 57 sites.
Afficher l'approche recommandée
The recommended architecture is cloud-managed WiFi for the guest network, with strict network segmentation to ensure the guest network is completely isolated from clinical systems. The 57-site scale and the small central IT team make cloud-managed WiFi the operationally superior choice — the alternative of deploying on-premise controllers at each site would require significantly more engineering resource than the team can sustain. The guest WiFi SSID should be on a dedicated VLAN with internet-only access, enforced by firewall rules that block all traffic to clinical network segments. This segmentation ensures that the guest network does not fall within the scope of NHS DSP Toolkit clinical data requirements. For data residency, select a cloud-managed platform that processes and stores data within the UK (or EEA at minimum), and verify this in the vendor's data processing agreement. Deploy Purple on the guest SSID for GDPR-compliant patient data capture, with consent flows that clearly distinguish between WiFi access (which requires minimal data) and optional marketing communications (which require explicit opt-in). The key compliance consideration is demonstrating to NHS Digital that clinical data cannot be accessed from the guest network — this requires documented network segmentation evidence, not just a policy statement.
Q2. A conference centre operator runs a single 15,000 sq metre venue that hosts 200 events per year, ranging from small boardroom meetings (20 delegates) to large exhibitions (5,000 attendees). The venue's IT team has two engineers. The operator wants to offer exhibitor-grade WiFi (dedicated bandwidth per stand) as a paid service, alongside free delegate WiFi. The venue currently has an ageing on-premise controller that is out of support. What architecture should replace it?
💡 Astuce :Consider the variable density requirements (20 to 5,000 users), the paid WiFi service model, and the small IT team. Also consider how Purple can support the commercial model.
Afficher l'approche recommandée
Replace the ageing on-premise controller with a cloud-managed WiFi platform, deploying Wi-Fi 6E access points throughout the venue. The cloud-managed model suits the small IT team and eliminates the hardware maintenance burden of an on-premise controller. For the paid exhibitor WiFi service, configure dedicated SSIDs per exhibition stand using dynamic VLAN assignment, with bandwidth shaping policies enforced at the access point level — all major cloud-managed platforms support this capability. For the free delegate WiFi, deploy Purple's captive portal to capture delegate data (email, organisation, job title) with GDPR-compliant consent, creating a valuable database for the venue's marketing and event follow-up activities. Purple's analytics will also provide the venue operator with per-event attendance data, dwell time metrics, and return visitor rates — useful for commercial reporting to event organisers. The variable density requirement (20 to 5,000 users) is handled by the cloud management platform's dynamic RF management, which automatically adjusts transmit power and channel allocation based on active user density. Ensure the AP deployment design includes sufficient density for peak exhibition capacity, and validate throughput during a high-density test before the first major event.
Q3. A luxury hotel group is deploying a new WiFi estate across 8 five-star properties in Europe. Each property has 150 to 300 rooms, multiple F&B outlets, spa facilities, and conference rooms. The group's CTO wants to use WiFi data to personalise the guest experience — recognising returning guests, understanding their movement patterns within the property, and triggering personalised offers via the hotel app. The group's legal team has flagged GDPR concerns about tracking guest movements. How should the architecture be designed to achieve the commercial objective while remaining GDPR-compliant?
💡 Astuce :Consider the distinction between network-level data (which device is connected to which AP) and personal data (which guest is connected). GDPR compliance depends on the consent basis and the data minimisation principle.
Afficher l'approche recommandée
Deploy cloud-managed WiFi across all 8 properties with Purple as the guest intelligence layer. The GDPR compliance framework requires careful design of the consent and data architecture. At the point of WiFi authentication via Purple's captive portal, present guests with a layered consent notice: the first layer covers basic WiFi access (minimal data, legitimate interest basis); the second layer, presented as an optional enhancement, covers personalised services including movement analytics and targeted offers (explicit consent basis, clearly described). Guests who consent to personalised services have their device's WiFi probe data associated with their guest profile, enabling movement pattern analysis. Guests who do not consent receive standard WiFi access without tracking. This approach satisfies GDPR's requirement for granular, informed consent and the data minimisation principle (only collecting movement data from guests who have explicitly consented). Purple's consent management framework records consent timestamps and scope for each guest, providing the audit trail required under GDPR Article 7. The hotel app integration allows consenting guests to receive personalised offers triggered by their location within the property — for example, a spa offer when they are near the spa entrance. The legal team should review the privacy notice language to ensure the description of movement analytics is sufficiently clear and specific to constitute valid informed consent.
Points clés à retenir
- ✓Cloud-managed WiFi is operationally superior for multi-site deployments (5+ sites) due to zero-touch provisioning, automatic firmware updates, and single-pane-of-glass management — typically delivering lower total cost of ownership than on-premise controllers within 18 to 24 months.
- ✓Controller-based WiFi remains the right choice for large single-campus deployments with strict data sovereignty requirements, PCI DSS scope concerns, or the need for advanced features such as granular QoS and real-time RF optimisation.
- ✓Purple operates as an infrastructure-agnostic WiFi intelligence overlay — it integrates with both cloud-managed and controller-based architectures, adding GDPR-compliant guest data capture, footfall analytics, and CRM integration without requiring changes to the underlying network infrastructure.
- ✓GDPR compliance for guest WiFi is non-negotiable and applies regardless of network architecture: consent must be explicit, granular, and recorded before any personal data is processed. Purple's consent management framework addresses this requirement out of the box.
- ✓Security best practice for any enterprise WiFi deployment requires WPA3-Enterprise on staff networks, strict VLAN segmentation between guest, staff, and IoT traffic, and a documented firmware management process — automated in cloud-managed deployments, scheduled quarterly in on-premise deployments.
- ✓The commercial ROI of guest WiFi analytics is well-evidenced: Purple customers including McDonald's (90% reduction in IT engineer site visits) and Brussels South Charleroi Airport (10,630% ROI) demonstrate that WiFi intelligence delivers measurable business value beyond connectivity.
- ✓Avoid the hybrid trap: if you must operate both cloud-managed and controller-based infrastructure, define explicit criteria for each deployment type and ensure your monitoring and security operations tools can span both environments — unmanaged architectural complexity erodes the cost savings you were trying to achieve.



