OCSP y revocación de certificados para la autenticación WiFi
Esta guía completa explora los mecanismos críticos de revocación de certificados en entornos WiFi empresariales, centrándose en la transición de CRL a OCSP. Proporciona estrategias de implementación accionables para equipos de TI que gestionan redes de gran escala y alta densidad donde la seguridad en tiempo real y la baja latencia son primordiales.
🎧 Escucha esta guía
Ver transcripción
- Resumen ejecutivo
- Inmersión técnica profunda
- La mecánica de la revocación en 802.1X
- La transición a OCSP
- Grapado OCSP en entornos WiFi
- Guía de implementación
- 1. Infraestructura de CA de alta disponibilidad
- 2. Configuración y almacenamiento en caché del servidor RADIUS
- 3. Mecanismos de failover y resiliencia
- Mejores prácticas
- Solución de problemas y mitigación de riesgos
- ROI e impacto empresarial

Resumen ejecutivo
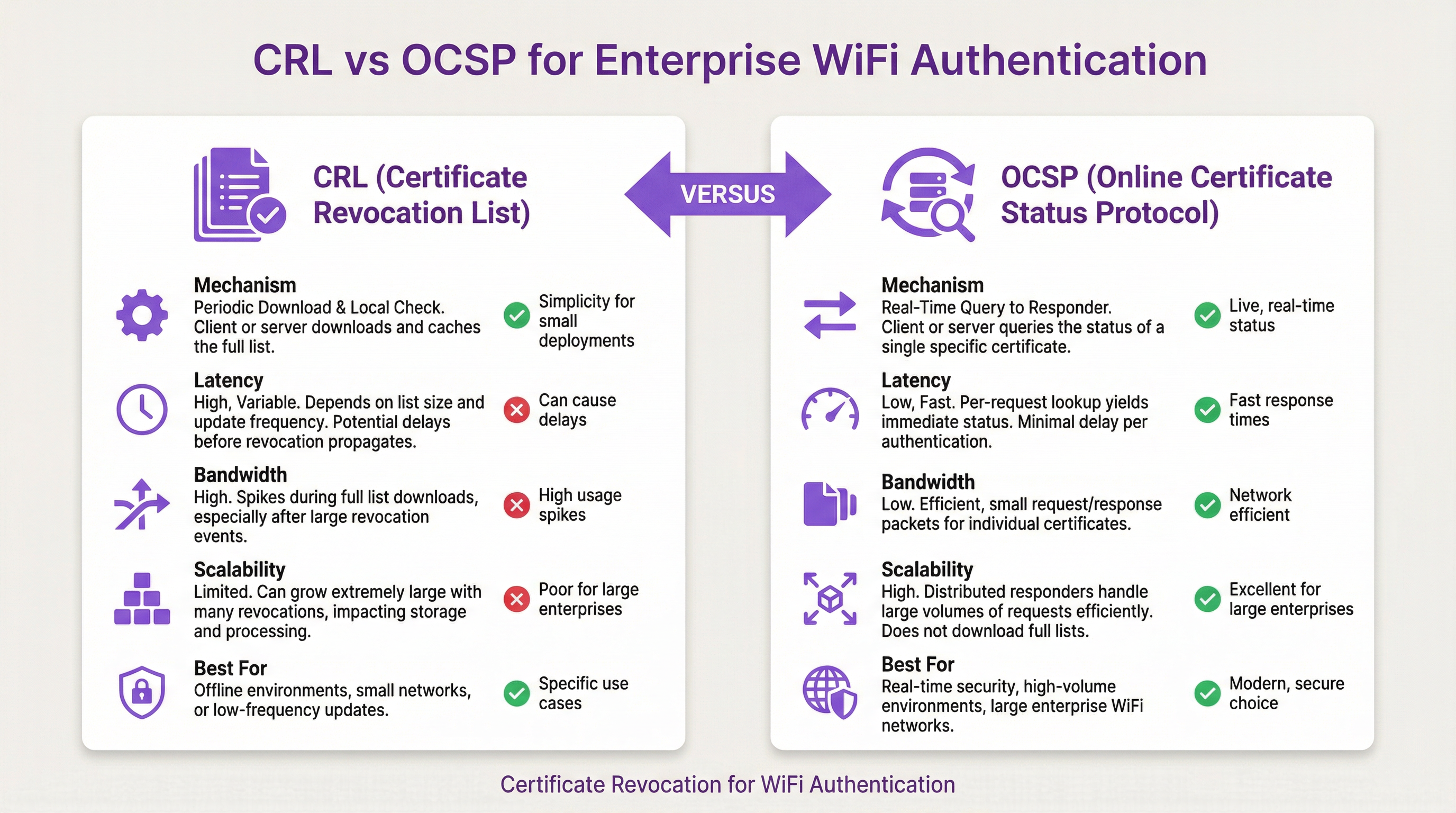
Para recintos empresariales que operan redes WiFi de alta densidad —desde extensas cadenas de retail hasta modernos centros de convenciones— la autenticación basada en certificados (EAP-TLS) es el estándar definitivo para asegurar el acceso a la red. Sin embargo, emitir un certificado es solo la mitad del ciclo de vida. El desafío operativo crítico reside en la revocación: garantizar que cuando un dispositivo se vea comprometido, se pierda o se retire del servicio, su acceso a la red se termine de inmediato. Esta guía explora la arquitectura técnica de la revocación de certificados, contrastando las Listas de Revocación de Certificados (CRL) heredadas con el Protocolo de Estado de Certificados en Línea (OCSP). Detallamos cómo los servidores RADIUS se integran con la Infraestructura de Clave Pública (PKI) para aplicar la revocación en tiempo real, las complejidades del grapado OCSP en un contexto 802.1X y los modelos de despliegue estratégico necesarios para equilibrar una seguridad estricta con una experiencia de usuario fluida. Al implementar una verificación OCSP robusta, los operadores de recintos pueden mitigar riesgos, asegurar el cumplimiento y mantener el alto rendimiento requerido para el Guest WiFi y el acceso empresarial.
Escuche nuestro informe ejecutivo de 10 minutos sobre este tema:
Inmersión técnica profunda
La mecánica de la revocación en 802.1X
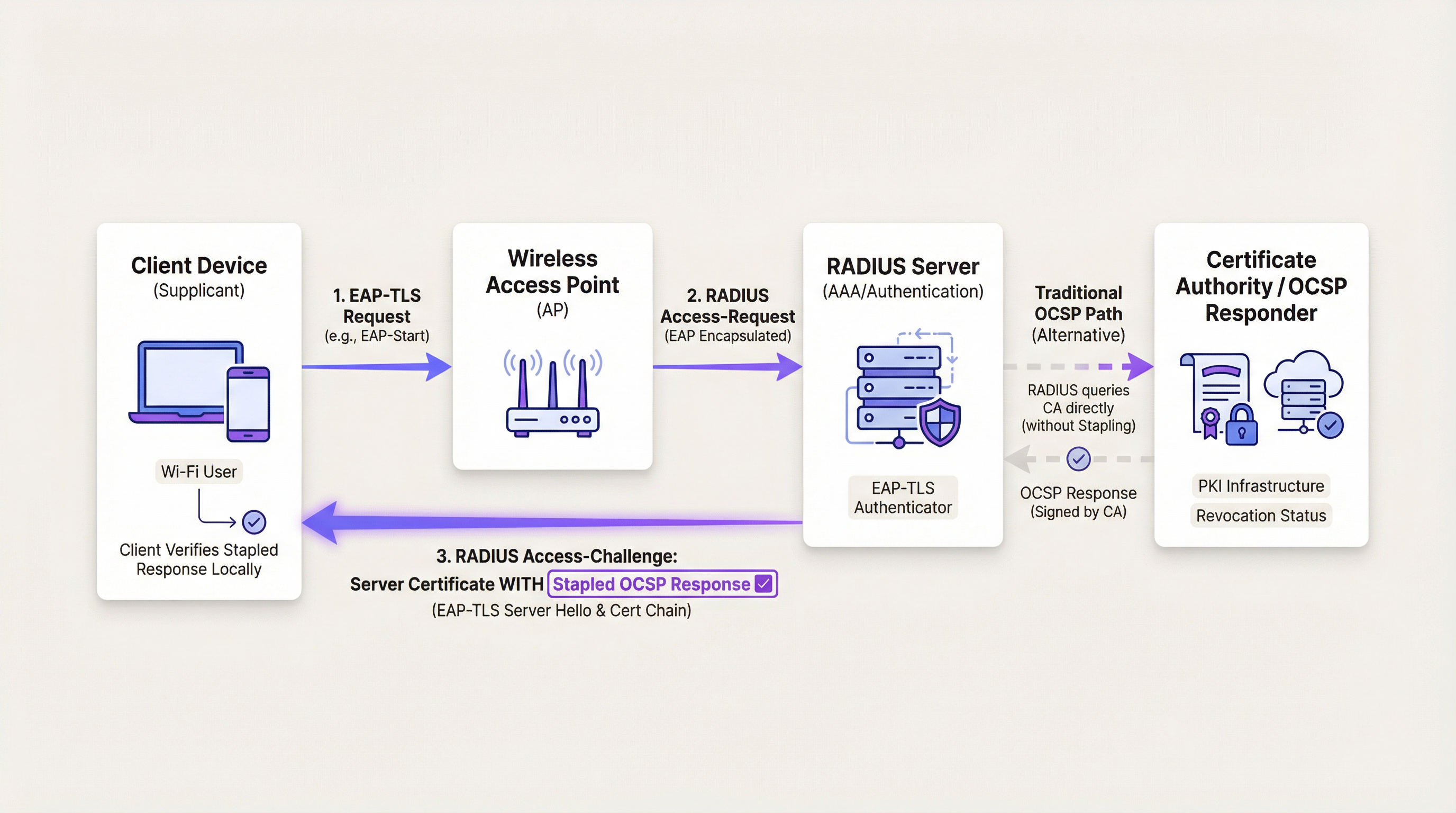
En un flujo de autenticación 802.1X, el punto de acceso inalámbrico (AP) actúa como un autenticador, pasando mensajes del Protocolo de Autenticación Extensible (EAP) entre el dispositivo cliente (suplicante) y el servidor RADIUS. Cuando un cliente presenta un certificado durante el saludo EAP-TLS, el servidor RADIUS debe validar su integridad criptográfica, verificar su cadena de confianza y confirmar su estado de revocación actual.
Históricamente, esto se lograba a través de una Lista de Revocación de Certificados (CRL). Una CRL es un archivo firmado digitalmente que contiene los números de serie de todos los certificados revocados emitidos por una Autoridad de Certificación (CA) específica. El servidor RADIUS descarga este archivo periódicamente y lo almacena localmente en caché. Aunque es sencillo de implementar, las CRL presentan desafíos de escalabilidad significativos. En grandes entornos empresariales, como los que se encuentran en el sector de Retail , las CRL pueden crecer hasta alcanzar megabytes de tamaño. Descargar y analizar estas listas consume ancho de banda y ciclos de procesamiento. Lo que es más crítico, las CRL introducen una ventana de vulnerabilidad: el tiempo entre que un certificado es revocado en la CA y el servidor RADIUS descarga la lista actualizada.
La transición a OCSP
Para abordar las limitaciones de las CRL, se desarrolló el Protocolo de Estado de Certificados en Línea (OCSP). OCSP reemplaza el modelo de descarga masiva con un mecanismo de consulta en tiempo real y específico. Cuando un cliente presenta un certificado, el servidor RADIUS extrae el URI del respondedor OCSP de la extensión de Acceso a la Información de la Autoridad (AIA) del certificado. Luego envía una solicitud HTTP ligera al respondedor, consultando el estado de ese número de serie de certificado específico. El respondedor devuelve una respuesta firmada indicando si el certificado es 'Bueno', 'Revocado' o 'Desconocido'.
Este enfoque elimina la ventana de vulnerabilidad asociada con las CRL, aplicando las revocaciones de inmediato. También reduce significativamente el consumo de ancho de banda, ya que el servidor RADIUS solo solicita datos para los certificados que intentan autenticarse activamente.
Grapado OCSP en entornos WiFi
El grapado OCSP es una técnica de optimización del rendimiento ampliamente utilizada en servidores web. En lugar de que el cliente consulte al respondedor OCSP, el servidor consulta periódicamente al respondedor sobre su propio estado de certificado. Luego 'grapa' la respuesta firmada al certificado que presenta al cliente durante el saludo TLS. Esto traslada la carga de la consulta del cliente al servidor y reduce el número de conexiones de red externas requeridas.
En el contexto de la autenticación WiFi, el grapado OCSP es muy relevante pero tiene matices. Durante EAP-TLS, el servidor RADIUS presenta su propio certificado de servidor al cliente para demostrar su identidad. El servidor RADIUS puede utilizar el grapado OCSP aquí, adjuntando la respuesta OCSP al Server Hello de EAP-TLS. Esto permite que el dispositivo cliente verifique el estado de revocación del servidor RADIUS sin requerir su propia conexión a internet, una característica crítica para dispositivos a los que aún no se les ha concedido acceso a la red.
Sin embargo, grapar el estado del certificado del cliente no es factible. El cliente no puede grapar su propio estado porque la red aún no confía en él. Por lo tanto, para la validación del certificado del cliente, el servidor RADIUS debe realizar una consulta OCSP tradicional a la CA.
Guía de implementación
Desplegar OCSP en un entorno empresarial de alta densidad requiere una planificación arquitectónica cuidadosa para garantizar tanto la seguridad como la disponibilidad. Los siguientes pasos describen una estrategia de despliegue robusta.
1. Infraestructura de CA de alta disponibilidad
El cambio a OCSP introduce una dependencia crítica de la infraestructura del respondedor de la CA. Si el servidor RADIUS no puede comunicarse con el respondedor OCSP, no puede verificar de manera definitiva el estado del certificado. Por lo tanto, el respondedor OCSP debe ser altamente disponible, estar distribuido geográficamente y ubicarse detrás de balanceadores de carga para manejar picos de autenticación, como los que se experimentan durante una gran conferencia o evento deportivo.
2. Configuración y almacenamiento en caché del servidor RADIUS
Para mitigar la latencia introducida por las consultas OCSP en tiempo real, los servidores RADIUS empresariales deben configurarse con mecanismos de almacenamiento en caché inteligentes. Cuando un servidor RADIUS recibe una respuesta 'Buena' del respondedor OCSP, debe almacenar esa respuesta en caché durante una duración configurable, generalmente entre 15 y 60 minutos. Las solicitudes de autenticación posteriores del mismo cliente dentro de esa ventana se validarán contra la caché, omitiendo la consulta externa. Esto equilibra la necesidad de seguridad en tiempo real con los requisitos de rendimiento de una red ocupada.
3. Mecanismos de failover y resiliencia
Los arquitectos de red deben definir el comportamiento del servidor RADIUS en caso de que el respondedor OCSP no esté disponible. Esto se conoce como 'falla abierta' frente a 'falla cerrada'. En una configuración de 'falla cerrada', el servidor RADIUS denegará el acceso si no puede verificar el estado del certificado. Esta es la postura más segura, pero conlleva el riesgo de interrupciones generalizadas si la infraestructura de la CA falla. En una configuración de 'falla abierta', el servidor RADIUS permitirá el acceso si el respondedor no está disponible, priorizando la disponibilidad sobre la seguridad estricta.
Un enfoque híbrido recomendado consiste en configurar el servidor RADIUS para que intente primero una consulta OCSP. Si el respondedor no está disponible, el servidor recurre a una CRL almacenada localmente en caché. Esto proporciona resiliencia contra interrupciones de la CA mientras se mantiene un nivel básico de verificación de revocación.
Mejores prácticas
- Minimizar la vida útil de los certificados: Si bien la revocación maneja la invalidación prematura, el control de seguridad más efectivo es una vida útil corta del certificado. Implemente el aprovisionamiento automatizado de certificados a través de MDM para emitir certificados válidos por días o semanas, en lugar de años. Esto reduce por completo la dependencia de los mecanismos de revocación. Para leer más sobre la seguridad de los dispositivos modernos, consulte nuestra guía sobre Autenticación 802.1X: Asegurando el acceso a la red en dispositivos modernos .
- Monitorear la latencia de OCSP: Monitoree continuamente la latencia de las consultas OCSP desde sus servidores RADIUS a la infraestructura de la CA. Una latencia alta afectará directamente la experiencia del usuario, provocando tiempos de espera de autenticación y caídas de conexión.
- Implementar controles de acceso estrictos a la CA: La seguridad de su red WiFi está intrínsecamente ligada a la seguridad de su CA. Asegúrese de que existan controles de acceso estrictos, autenticación multifactor y auditorías exhaustivas para todas las interfaces de gestión de la CA.
Solución de problemas y mitigación de riesgos
Al desplegar OCSP, los equipos de TI suelen encontrarse con varios modos de falla comunes:
- Tiempos de espera de autenticación: Si el respondedor OCSP tarda en responder, el saludo EAP-TLS puede agotar el tiempo de espera. Esto suele ser causado por la congestión de la red o una infraestructura de CA con recursos insuficientes. La mitigación implica optimizar el almacenamiento en caché de OCSP en el servidor RADIUS y escalar la infraestructura del respondedor.
- Desviación del reloj: Las respuestas OCSP están selladas en tiempo y firmadas. Si el reloj del servidor RADIUS no está sincronizado con la CA, el servidor puede rechazar una respuesta OCSP válida por considerarla expirada. Asegúrese de que todos los componentes de la infraestructura estén sincronizados a través de servidores NTP confiables.
- Bloqueo de firewall: Las consultas OCSP suelen utilizar HTTP (puerto 80) o HTTPS (puerto 443). Asegúrese de que los firewalls entre el servidor RADIUS y la infraestructura de la CA estén configurados para permitir este tráfico. Las implementaciones modernas utilizan cada vez más HTTPS para proteger la privacidad y evitar que observadores de red analicen las consultas de certificados.
ROI e impacto empresarial
La implementación de mecanismos robustos de revocación de certificados ofrece un valor empresarial medible más allá del simple cumplimiento de seguridad.
- Mitigación de riesgos: Al eliminar la ventana de vulnerabilidad asociada con las CRL, OCSP reduce significativamente el riesgo de que un dispositivo comprometido acceda a recursos corporativos sensibles. Esto protege la propiedad intelectual y mitiga el daño financiero y de reputación de una brecha de datos.
- Eficiencia operativa: La automatización de las verificaciones de revocación a través de OCSP reduce la carga administrativa asociada con la gestión de archivos CRL masivos. Los equipos de TI pueden centrarse en iniciativas estratégicas en lugar de solucionar fallas en la descarga de CRL.
- Habilitación del cumplimiento: Para los recintos que operan en industrias reguladas, como Sector Salud o finanzas, los controles de acceso estrictos y la revocación en tiempo real suelen ser requisitos de cumplimiento obligatorios (por ejemplo, HIPAA, PCI DSS). Un despliegue robusto de OCSP garantiza el cumplimiento continuo y simplifica los procesos de auditoría.
Términos clave y definiciones
OCSP (Online Certificate Status Protocol)
An internet protocol used for obtaining the revocation status of an X.509 digital certificate in real-time.
Used by RADIUS servers to instantly verify if a device's certificate has been revoked, closing the vulnerability window associated with legacy CRLs.
CRL (Certificate Revocation List)
A periodically updated, digitally signed list of certificate serial numbers that have been revoked by the issuing Certificate Authority.
The legacy method for revocation checking. It suffers from scalability issues and introduces a vulnerability window between updates.
OCSP Stapling
A mechanism where the certificate presenter (e.g., a RADIUS server) obtains a time-stamped OCSP response from the CA and appends it to the certificate during the TLS handshake.
Used to improve performance and privacy by offloading the OCSP query burden from the client device.
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
A highly secure 802.1X authentication method that requires mutual certificate-based authentication between the client and the RADIUS server.
The standard protocol used in enterprise WiFi environments that necessitates robust certificate revocation checking.
Vulnerability Window
The period of time between a certificate being revoked at the CA and the enforcing system (e.g., RADIUS server) becoming aware of the revocation.
A primary driver for adopting OCSP over CRLs, as OCSP effectively reduces this window to near zero.
Fail Open vs. Fail Closed
A configuration decision determining the system's behaviour when a dependency (like an OCSP responder) is unreachable. 'Fail open' allows access; 'fail closed' denies access.
A critical architectural decision for IT teams balancing network availability against strict security compliance.
AIA (Authority Information Access)
An extension within an X.509 certificate that indicates how to access information and services for the issuer of the certificate, including the OCSP responder URI.
The RADIUS server reads this extension to determine exactly where to send the OCSP query for a specific client certificate.
Supplicant
The software client on a device (e.g., a laptop or smartphone) that attempts to access the network and responds to authentication requests.
The entity presenting the client certificate that the RADIUS server must validate against the OCSP responder.
Casos de éxito
A 500-room luxury hotel in the [Hospitality](/industries/hospitality) sector is upgrading its back-of-house WiFi network to use EAP-TLS for staff devices. They currently use a centralized RADIUS server in their corporate data centre, connected via SD-WAN. They are concerned that real-time OCSP queries to their cloud-based CA will cause authentication timeouts during shift changes when hundreds of staff connect simultaneously.
The implementation must prioritize low-latency authentication without compromising security. The solution involves three steps: 1) Deploy a localized RADIUS proxy at the hotel property to handle the initial EAP termination. 2) Configure the RADIUS proxy to perform OCSP queries and cache the 'Good' responses for 60 minutes. 3) Implement a fallback mechanism where the RADIUS proxy relies on a locally downloaded, daily CRL if the SD-WAN link to the cloud CA fails.
A large public-sector organisation is deploying [Sensors](/products/sensors) across multiple municipal buildings. These IoT devices authenticate via 802.1X using certificates with a 5-year lifespan. The IT security team requires immediate network disconnection if a sensor is reported stolen.
Given the long certificate lifespan, robust revocation is critical. The organisation must configure their RADIUS servers to perform mandatory OCSP queries for every authentication request from the sensor VLAN. Caching should be disabled or set to a very short duration (e.g., 5 minutes). The RADIUS servers must be configured to 'fail closed'—if the OCSP responder is unreachable, the sensor is denied access.
Análisis de escenarios
Q1. Your organisation is migrating from a daily CRL download to real-time OCSP checking for your corporate WiFi. During the pilot phase, you notice a significant increase in authentication timeouts, particularly for users roaming between buildings. What is the most likely cause and the recommended mitigation?
💡 Sugerencia:Consider the latency introduced by external network queries during the EAP-TLS handshake.
Mostrar enfoque recomendado
The timeouts are likely caused by the latency of performing an external HTTP query to the OCSP responder for every authentication event, including fast reconnects during roaming. The recommended mitigation is to configure OCSP caching on the RADIUS server. By caching 'Good' responses for a period (e.g., 30 minutes), subsequent roam events will be validated locally against the cache, eliminating the external query latency and preventing timeouts.
Q2. A critical security audit requires that no compromised device can access the network for more than 5 minutes after its certificate is revoked in the MDM platform. Your RADIUS server is configured to use OCSP with a 60-minute cache. Does this configuration meet the audit requirement?
💡 Sugerencia:Analyze the relationship between the cache duration and the vulnerability window.
Mostrar enfoque recomendado
No, this configuration fails the audit requirement. The 60-minute cache creates a vulnerability window of up to one hour. If a device authenticates and its 'Good' status is cached, and the certificate is revoked 1 minute later, the RADIUS server will continue to permit access for the remaining 59 minutes based on the cached response. To meet the 5-minute requirement, the OCSP cache duration must be reduced to 5 minutes or less, though this will increase the query load on the CA infrastructure.
Q3. During a major ISP outage, your cloud-based OCSP responder becomes unreachable. Your RADIUS server is configured for OCSP checking with a 'fail closed' policy. What is the impact on the network, and how could the architecture be improved for resilience?
💡 Sugerencia:Consider the implications of 'fail closed' when a critical dependency is unavailable.
Mostrar enfoque recomendado
The impact is a total outage for all new WiFi authentications. Because the RADIUS server cannot reach the responder and is configured to 'fail closed', it will deny all access requests. To improve resilience, the architecture should implement a fallback mechanism. The RADIUS server should be configured to attempt OCSP first, and if unreachable, fall back to a locally cached CRL. This allows authentications to proceed using the last known good revocation state during the ISP outage.
Conclusiones clave
- ✓OCSP replaces bulky CRL downloads with real-time, targeted certificate status queries, eliminating the vulnerability window.
- ✓In 802.1X environments, the RADIUS server performs the OCSP query to validate the client's certificate before granting network access.
- ✓OCSP stapling allows the RADIUS server to prove its own validity to the client without requiring the client to query the CA.
- ✓Intelligent caching of 'Good' OCSP responses on the RADIUS server is critical to prevent authentication timeouts in high-density venues.
- ✓Implementing a CRL fallback mechanism ensures network resilience if the primary OCSP responder becomes unreachable.
- ✓A 'fail closed' configuration maximizes security but risks widespread outages, whereas 'fail open' prioritizes availability.
- ✓Robust certificate lifecycle management, including short certificate lifespans, reduces reliance on revocation mechanisms.



