Cloud-Managed WiFi vs. Controller-basiertes WiFi: Wofür sollten Sie sich entscheiden?
This guide provides a vendor-neutral technical comparison of cloud-managed WiFi and controller-based (on-premise) WiFi architectures, helping IT managers, network architects, and CTOs make an informed deployment decision. It covers the architectural trade-offs across scalability, data sovereignty, cost model, and offline resilience, with real-world case studies from hospitality, retail, and public-sector environments. It also explains how Purple's WiFi intelligence platform integrates with either architecture to deliver guest experience management, first-party data capture, and GDPR-compliant analytics.
🎧 Diesen Leitfaden anhören
Transkript anzeigen
- Executive Summary
- Technischer Deep-Dive
- Was ist Cloud-Managed WiFi?
- Was ist Controller-basiertes WiFi?
- Architektonische Abwägungen: Ein strukturierter Vergleich
- Überlegungen zur Sicherheitsarchitektur
- Wie sich Purple in beide Architekturen integriert
- Implementierungsleitfaden
- Schritt 1: Definieren Sie Ihr Anforderungsprofil
- Schritt 2: Wählen Sie Ihr Architekturmodell
- Schritt 3: Evaluieren Sie Netzwerkanbieter
- Schritt 4: Stellen Sie Purple als Ihren Intelligence Layer bereit
- Schritt 5: Validieren Sie Compliance und Sicherheit
- Best Practices
- Troubleshooting und Risikominderung
- ROI und geschäftliche Auswirkungen

Executive Summary
Die Entscheidung zwischen Cloud-Managed WiFi und Controller-basiertem WiFi ist eine der folgenreichsten Architekturentscheidungen, die ein Netzwerkteam in diesem Jahrzehnt treffen wird. Beide Modelle bieten drahtlose Konnektivität auf Enterprise-Niveau, unterscheiden sich jedoch grundlegend darin, wo die Intelligenz angesiedelt ist, wie sie skalieren, welche Kosten im Laufe der Zeit anfallen und wie sie Compliance-Verpflichtungen handhaben.
Cloud-Managed WiFi verlagert die Controller-Funktion in eine vom Anbieter gehostete Cloud-Plattform und ermöglicht so Zero-Touch-Provisioning, automatische Firmware-Updates und ein Single-Pane-of-Glass-Management über unbegrenzt viele Standorte hinweg. Controller-basiertes WiFi behält diese Intelligenz On-Premise und bietet maximale Datenhoheit, Offline-Resilienz und granulare Kontrolle – auf Kosten höherer CapEx und eines größeren operativen Aufwands.
Für die meisten Betreiber mit mehreren Standorten – Hotelketten, Einzelhandelsunternehmen, Stadionbetreiber und Kommunalbehörden – stellt Cloud-Managed WiFi mittlerweile die operativ überlegene Wahl dar. Für große Single-Campus-Bereitstellungen mit strengen Anforderungen an die Datenresidenz bleiben On-Premise-Controller weiterhin attraktiv. In beiden Fällen fungiert die WiFi-Management-Plattform von Purple als infrastrukturunabhängiges Overlay, das Guest Experience Management, GDPR-konforme Datenerfassung und umsetzbare Analysen ergänzt – unabhängig davon, für welche Architektur Sie sich entscheiden.
Technischer Deep-Dive
Was ist Cloud-Managed WiFi?
Cloud-Managed WiFi ist eine WLAN-Architektur, bei der die Controller-Funktion – Authentifizierung, Richtliniendurchsetzung, Hochfrequenzmanagement (RF-Management), Firmware-Verteilung und Monitoring – in einer vom Anbieter betriebenen Cloud-Plattform statt auf dedizierter On-Premise-Hardware gehostet wird. Access Points an lokalen Standorten verbinden sich über verschlüsselte HTTPS- oder CAPWAP-Tunnel mit der Cloud-Management-Plattform, empfangen ihre Konfiguration und senden Telemetriedaten Upstream. Die Data Plane – die eigentliche Weiterleitung des Benutzerverkehrs – bleibt in der Regel lokal am Access Point, wodurch sichergestellt wird, dass ein WAN-Ausfall aktive Benutzersitzungen nicht unterbricht.
Zu den führenden Cloud-Managed WiFi-Plattformen gehören Cisco Meraki, Aruba Central (HPE), Juniper Mist, Extreme Networks CloudIQ und Ruckus One. Jede Plattform bietet eine webbasierte Management-Konsole, eine RESTful API zur Integration mit Drittsystemen sowie unterschiedliche Grade an KI-gesteuerter RF-Optimierung und Anomalieerkennung.
Was ist Controller-basiertes WiFi?
Controller-basiertes WiFi ist die traditionelle Enterprise-WLAN-Architektur, bei der ein physischer oder virtueller Wireless LAN Controller (WLC) On-Premise bereitgestellt wird, um alle Access Points innerhalb eines Standorts oder Campus zu verwalten. Der Controller übernimmt die IEEE 802.1X-Authentifizierung via RADIUS, setzt QoS- und Sicherheitsrichtlinien durch, verwaltet das Fast Roaming zwischen Access Points (IEEE 802.11r) und bietet zentralisiertes Monitoring und Troubleshooting. In einer Split-Tunnel- oder Local-Switching-Konfiguration wird der Benutzerverkehr lokal am Access Point weitergeleitet; in einer Centralised-Switching-Konfiguration wird der gesamte Datenverkehr zurück zum Controller getunnelt.
Zu den wichtigsten Controller-basierten Plattformen zählen Cisco Catalyst Wireless (ehemals AireOS), Aruba Mobility Controllers, Juniper Mist mit virtuellen On-Premise-Controllern und Ruckus SmartZone. Diese Plattformen sind ausgereift, funktionsreich und in Unternehmens-, Gesundheits- und öffentlichen Sektoren weit verbreitet.
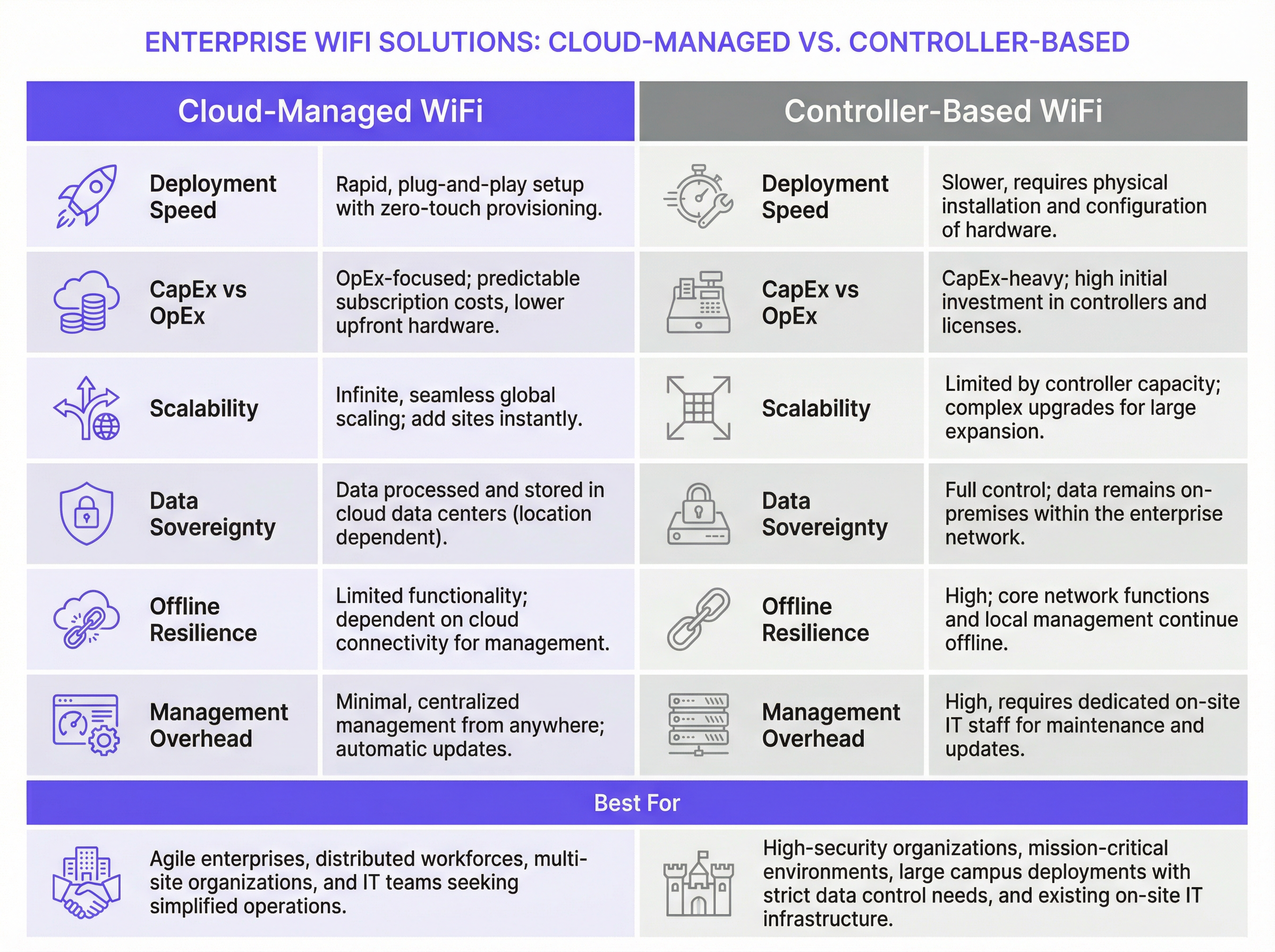
Architektonische Abwägungen: Ein strukturierter Vergleich
| Dimension | Cloud-Managed WiFi | Controller-basiertes WiFi |
|---|---|---|
| Bereitstellungsgeschwindigkeit | Schnell; Zero-Touch-Provisioning durch vorab konfigurierte APs | Langsamer; erfordert Controller-Installation vor Ort und AP-Registrierung |
| Kostenmodell | OpEx-dominant; Abonnement-Lizenzierung pro AP | CapEx-dominant; Hardwarekauf plus jährliche Supportverträge |
| Skalierbarkeit | Praktisch unbegrenzt; Hinzufügen von Standorten ohne Hardwareänderungen | Begrenzt durch Controller-Kapazität; erfordert Hardware-Upgrades zur Skalierung |
| Offline-Resilienz | Lokale Datenweiterleitung läuft weiter; Management-Zugriff geht verloren | Volle Management- und Data-Plane-Funktionalität bleibt lokal erhalten |
| Datenhoheit | Management-Daten werden in der Cloud verarbeitet (regionsabhängig) | Alle Daten verbleiben innerhalb der Unternehmensnetzwerkgrenze |
| Firmware-Management | Automatische, vom Anbieter verwaltete Updates | Manuell oder geplant; erfordert Überwachung durch das IT-Team |
| Erweiterte Funktionen | Verbessern sich schnell; KI-gesteuerte RF-Optimierung verfügbar | Ausgereift; erweitertes QoS, Ortungsdienste und Richtliniengranularität |
| Multi-Site-Management | Nativ als Single-Pane-of-Glass über alle Standorte hinweg | Erfordert zusätzliche NOC-Tools oder standortspezifisches Management |
| IT-Aufwand | Gering; minimales Fachwissen vor Ort erforderlich | Hoch; erfordert qualifizierte Wireless-Ingenieure für die Wartung |
Überlegungen zur Sicherheitsarchitektur
Beide Architekturen unterstützen Sicherheitsstandards auf Enterprise-Niveau. WPA3-Enterprise mit IEEE 802.1X-Authentifizierung ist auf allen modernen Cloud-Managed- und Controller-basierten Plattformen verfügbar. Die RADIUS-Integration für eine zentralisierte Authentifizierung ist in beiden Modellen Standard. Die VLAN-Segmentierung zur Isolierung von Gast-, Mitarbeiter- und IoT-Datenverkehr wird von allen großen Anbietern unterstützt.
Der wesentliche Sicherheitsunterschied liegt in der Management Plane. Bei einer Controller-basierten Bereitstellung verbleibt der gesamte Management-Datenverkehr innerhalb Ihres Netzwerkperimeters, was ein erheblicher Vorteil für Unternehmen ist, die den Anforderungen von PCI DSS (was strenge Kontrollen für Karteninhaber-Datenumgebungen erfordert) oder der ISO 27001-Zertifizierung unterliegen. Bei einer Cloud-Managed-Bereitstellung durchläuft der Management-Datenverkehr das öffentliche Internet – wenn auch verschlüsselt – und Ihre Sicherheitslage hängt teilweise von den eigenen Sicherheitskontrollen und Zertifizierungen des Cloud-Anbieters ab.
Speziell für Gast-WiFi erfordert die GDPR-Compliance, dass alle personenbezogenen Daten, die über ein Captive Portal erfasst werden – einschließlich E-Mail-Adressen, Social-Login-Token oder Gerätekennungen –, mit ausdrücklicher, informierter Zustimmung erfasst, sicher gespeichert und den Rechten der betroffenen Personen (einschließlich Auskunft und Löschung) unterworfen werden. Diese Verpflichtung gilt unabhängig davon, ob Ihr zugrunde liegendes Netzwerk Cloud-Managed oder Controller-basiert ist. Das Consent-Management-Framework von Purple adressiert diese Anforderung direkt und bietet mit Zeitstempeln versehene Einwilligungsnachweise, automatisierte Richtlinien zur Datenaufbewahrung und ein Self-Service-Portal für Anfragen von betroffenen Personen.
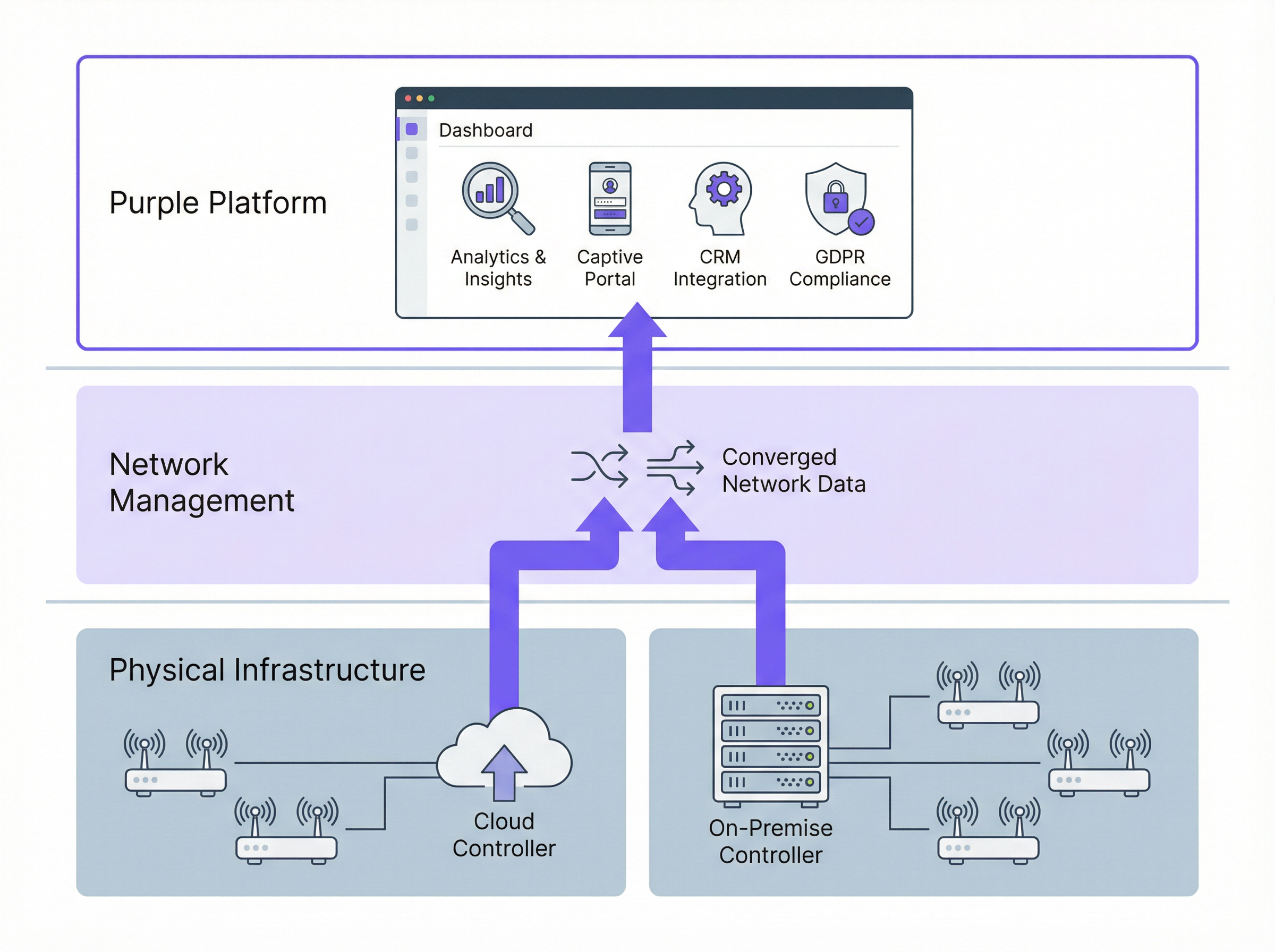
Wie sich Purple in beide Architekturen integriert
Purple fungiert als WiFi-Intelligence-Overlay – es ersetzt nicht Ihren Netzwerkanbieter, sondern erweitert ihn um eine Guest-Experience- und Analytics-Ebene. Purple verbindet sich über Standard-APIs und RADIUS-Integration mit Ihrer Netzwerkinfrastruktur, unabhängig davon, ob Ihre Access Points von einer Cloud-Plattform oder einem On-Premise-Controller verwaltet werden.
Für Gast-WiFi bietet Purple ein anpassbares Captive Portal, das die Benutzerauthentifizierung (Social Login, E-Mail, SMS-Verifizierung oder die Purple App), die GDPR-konforme Erfassung von Einwilligungen und die nahtlose Übergabe an das Netzwerk übernimmt. Für Mitarbeiter-WiFi ermöglichen die identitätsbasierten Netzwerkfunktionen von Purple eine automatische Bereitstellung und den Entzug von Zugriffsrechten in Verbindung mit Ihrem HR- oder Identity-Management-System – so wird sichergestellt, dass der Netzwerkzugriff eines ausscheidenden Mitarbeiters ohne manuelles Eingreifen beendet wird.
Die Analytics-Plattform von Purple verarbeitet anschließend die Verbindungsdaten, um Footfall-Metriken, Verweildaueranalysen, das Verhältnis von neuen zu wiederkehrenden Besuchern sowie demografische Erkenntnisse zu generieren. Diese Analysen sind über das Dashboard von Purple, per API-Integration mit Ihren Business-Intelligence-Tools oder über direkte CRM-Konnektoren zu Plattformen wie Salesforce, HubSpot und Microsoft Dynamics verfügbar.
Implementierungsleitfaden
Schritt 1: Definieren Sie Ihr Anforderungsprofil
Bevor Sie Anbieter evaluieren, dokumentieren Sie Ihre Anforderungen in fünf Dimensionen: Anzahl und Verteilung der Standorte (Single-Campus vs. Multi-Site-Bestand); Compliance-Verpflichtungen (GDPR, PCI DSS, Anforderungen an die Datenresidenz); Kapazität des IT-Teams (Können Sie On-Premise-Hardware an jedem Standort betreuen?); Kommerzielle Ziele (Benötigen Sie die Erfassung von Gastdaten und Analysen?); und Budgetmodell (Präferenz für CapEx vs. OpEx).
Schritt 2: Wählen Sie Ihr Architekturmodell
Wenden Sie folgende Entscheidungslogik an: Wenn Sie mehr als fünf geografisch verteilte Standorte betreiben, ist Cloud-Managed WiFi mit an Sicherheit grenzender Wahrscheinlichkeit die richtige Wahl für Ihren Access Layer – die operativen Einsparungen durch zentralisiertes Management und Zero-Touch-Provisioning werden die Abonnementkosten innerhalb von zwölf bis achtzehn Monaten übersteigen. Wenn Sie einen einzelnen großen Campus mit strengen Anforderungen an die Datenhoheit betreiben, evaluieren Sie On-Premise-Controller, einschließlich virtueller Controller-Optionen, die die Hardware-CapEx reduzieren. Wenn Sie über eine Mischung von Standorttypen verfügen, ziehen Sie ein bewusstes Hybridmodell mit klar definierten Kriterien für jeden Bereitstellungstyp in Betracht.
Schritt 3: Evaluieren Sie Netzwerkanbieter
Erstellen Sie einen strukturierten RFP (Request for Proposal), der Folgendes abdeckt: AP-Hardware-Spezifikationen (Wi-Fi 6E-Unterstützung, Antennendesign, PoE-Anforderungen); Funktionen der Management-Plattform (API-Vollständigkeit, Monitoring, Alerting); Sicherheitszertifizierungen (SOC 2 Typ II für Cloud-Plattformen, ISO 27001); SLA-Verpflichtungen (Uptime-Garantien, Support-Reaktionszeiten); und das Integrations-Ökosystem (RADIUS, VLAN, APIs von Drittanbieter-Plattformen).
Schritt 4: Stellen Sie Purple als Ihren Intelligence Layer bereit
Sobald Ihre Netzwerkinfrastruktur ausgewählt ist, stellen Sie Purple bereit, um Guest Experience Management und Analytics hinzuzufügen. Der Bereitstellungsprozess von Purple umfasst: Konfiguration einer dedizierten Gast-SSID in Ihrer Netzwerkinfrastruktur; Weiterleitung der Splash-Page oder RADIUS-Authentifizierung der SSID an die Cloud-Plattform von Purple; Anpassung des Captive Portal an Ihre Markenidentität und Consent-Flows; sowie die Anbindung von Purple an Ihre CRM- und Marketing-Automation-Plattformen über den Integrations-Marktplatz.
Schritt 5: Validieren Sie Compliance und Sicherheit
Führen Sie vor dem Go-Live eine Compliance-Prüfung durch, die Folgendes abdeckt: Validierung des GDPR-Consent-Flows (stellen Sie sicher, dass die Einwilligung ausdrücklich, granular und protokolliert ist); Überprüfung der Netzwerksegmentierung (bestätigen Sie, dass der Gast-Datenverkehr keine internen Systeme erreichen kann); Bewertung des PCI DSS-Geltungsbereichs (falls Zahlungskartendaten irgendwo im Netzwerk verarbeitet werden); und Penetrationstests der Gast-WiFi-Umgebung.
Best Practices
Aggressiv segmentieren. Stellen Sie immer separate SSIDs für Gäste, Mitarbeiter und IoT-Geräte bereit, die jeweils einem dedizierten VLAN mit entsprechenden Firewall-Richtlinien zugeordnet sind. Der Gast-Datenverkehr sollte standardmäßig von internen Systemen isoliert sein und nur Internetzugang bieten, es sei denn, eine spezifische geschäftliche Anforderung rechtfertigt etwas anderes.
WPA3 erzwingen, wo die Hardware dies unterstützt. Wi-Fi 6- und Wi-Fi 6E-Access-Points unterstützen WPA3 durchgängig. Für Gastnetzwerke bietet WPA3-Personal mit Simultaneous Authentication of Equals (SAE) einen deutlich stärkeren Schutz vor Offline-Wörterbuchangriffen als WPA2-PSK. Für Mitarbeiternetzwerke bietet WPA3-Enterprise mit 802.1X eine benutzerbezogene Authentifizierung und Forward Secrecy.
Planen Sie für OpenRoaming. Der OpenRoaming-Standard der Wi-Fi Alliance, der auf Passpoint (IEEE 802.11u) basiert, ermöglicht es Benutzern, sich automatisch mit jedem OpenRoaming-fähigen Netzwerk zu verbinden, indem sie die Anmeldeinformationen ihres Home-Identity-Providers verwenden – ihres Mobilfunkanbieters, ihres Arbeitgebers oder einer Plattform wie der Purple App. Die Bereitstellung von OpenRoaming eliminiert die Reibungsverluste durch das Captive Portal für wiederkehrende Benutzer und sorgt gleichzeitig für einen authentifizierten, sicheren Zugang. Purple unterstützt OpenRoaming nativ.
Automatisieren Sie das Firmware-Management. Ungepatchte Firmware ist einer der häufigsten Angriffsvektoren in Enterprise-WiFi-Bereitstellungen. Cloud-Managed-Plattformen erledigen dies automatisch; richten Sie für On-Premise-Bereitstellungen einen vierteljährlichen Firmware-Überprüfungszyklus ein und nutzen Sie die geplante Update-Funktion Ihres Controllers, um Updates während der Wartungsfenster zu pushen.
Kontinuierliches Monitoring. Stellen Sie WIDS-Funktionen (Wireless Intrusion Detection System) bereit, die auf allen großen Enterprise-Plattformen verfügbar sind, um Rogue Access Points, Deauthentifizierungsangriffe und Evil-Twin-Angriffe zu erkennen. Integrieren Sie WIDS-Warnungen in Ihre SIEM-Plattform für ein zentralisiertes Sicherheits-Monitoring.
Troubleshooting und Risikominderung
Risiko: Ausfall der Cloud-Management-Plattform. Maßnahme: Stellen Sie sicher, dass die von Ihnen gewählte Plattform lokale AP-Survivability unterstützt – die Fähigkeit von Access Points, mit ihrer zuletzt bekannten Konfiguration weiterzuarbeiten, wenn die Cloud-Konnektivität unterbrochen wird. Alle großen Cloud-Plattformen (Meraki, Aruba Central, Juniper Mist) unterstützen diese Funktion. Testen Sie dies explizit während Ihrer Abnahmetestphase.
Risiko: GDPR-Non-Compliance bei der Erfassung von Gastdaten. Maßnahme: Verwenden Sie eine Plattform wie Purple, die ein vorgefertigtes, rechtlich geprüftes Consent-Management-Framework bietet. Vermeiden Sie die Entwicklung benutzerdefinierter Captive Portals ohne rechtliche Prüfung – die spezifischen Anforderungen an Sprache, Granularität und Protokollierung für die GDPR-Einwilligung sind präzise und werden häufig falsch implementiert.
Risiko: Ausfall der Controller-Hardware bei On-Premise-Bereitstellungen. Maßnahme: Stellen Sie Controller in Hochverfügbarkeitspaaren mit automatischem Failover bereit. Stellen Sie bei virtuellen Controllern sicher, dass die zugrunde liegende Hypervisor-Infrastruktur über eine angemessene Redundanz verfügt. Dokumentieren Sie Ihr Recovery Time Objective (RTO) und testen Sie die Failover-Verfahren jährlich.
Risiko: Unzureichende WAN-Bandbreite für das Cloud-Management. Maßnahme: Der Cloud-Management-Datenverkehr ist in der Regel moderat – ein bis zwei Megabit pro Sekunde pro hundert Access Points –, weist jedoch bei Firmware-Updates Spitzen auf. Planen Sie Firmware-Updates außerhalb der Spitzenzeiten und verwenden Sie QoS-Richtlinien, um den Management-Datenverkehr gegenüber Gastdaten zu priorisieren, falls die WAN-Bandbreite begrenzt ist.
Risiko: Vendor Lock-in. Maßnahme: Evaluieren Sie die Offenheit der API Ihrer gewählten Plattform und deren Unterstützung für herstellerneutrale Standards (RADIUS, 802.1X, VLAN-Tagging). Die infrastrukturunabhängige Architektur von Purple bedeutet, dass Sie Ihren zugrunde liegenden Netzwerkanbieter wechseln können, ohne Ihre Gastdaten, den Analytics-Verlauf oder CRM-Integrationen zu verlieren.
ROI und geschäftliche Auswirkungen
Der Business Case für Cloud-Managed WiFi mit Purple als Intelligence Layer hat sich in zahlreichen Branchen etabliert. McDonald's, ein Kunde von Purple, erzielte durch die Bereitstellung von Cloud-Managed Gast-WiFi mit zentralisiertem Management eine Reduzierung der Vor-Ort-Einsätze von IT-Technikern um 90 % – eine direkte Einsparung von Betriebskosten, die die Investition in die Plattform bereits im ersten Jahr amortisierte. Der Flughafen Brüssel-Charleroi (Brussels South Charleroi Airport) erzielte einen ROI von 10.630 % durch die Gast-WiFi-Analysen von Purple, angetrieben durch eine verbesserte Passenger Experience, eine längere Verweildauer in den Einzelhandelsbereichen und datengesteuerte kommerzielle Entscheidungen.
Für einen typischen Hotelbestand mit 40 Häusern sieht das Finanzmodell in etwa wie folgt aus. Controller-basierte Bereitstellung: 80.000 £ bis 120.000 £ an CapEx für Controller-Hardware, plus 15.000 £ bis 25.000 £ pro Jahr für Supportverträge, zuzüglich der Technikerzeit für die Wartung. Cloud-Managed-Bereitstellung: 0 £ für Controller-Hardware, plus 8.000 £ bis 15.000 £ pro Jahr für Plattform-Abonnements, zuzüglich eines deutlich reduzierten Technikeraufwands. Das Cloud-Managed-Modell erreicht in der Regel innerhalb von 18 bis 24 Monaten den Break-even und bietet über einen Zeitraum von fünf Jahren niedrigere Gesamtbetriebskosten (Total Cost of Ownership).
Der kommerzielle Wert des Analytics Layers von Purple fügt der ROI-Berechnung eine weitere Dimension hinzu. First-Party-Gastdaten, die über das Captive Portal von Purple erfasst werden – E-Mail-Adressen, Besuchshäufigkeit, demografische Daten –, haben einen direkten kommerziellen Wert für Marketingkampagnen, die Anmeldung zu Treueprogrammen und personalisierte Kommunikation. Unternehmen, die Purple in ihre CRM-Plattform integrieren, verzeichnen in der Regel innerhalb der ersten zwölf Monate nach der Bereitstellung einen Anstieg der Marketing-Qualified Contacts um 25 bis 40 %.
Hören Sie sich den Purple Technical Briefing Podcast an, um einen 10-minütigen Audio-Walkthrough dieses Leitfadens zu erhalten, der architektonische Abwägungen, Implementierungsempfehlungen und ein kurzes Q&A abdeckt.
Schlüsselbegriffe & Definitionen
Cloud-Managed WiFi
A wireless LAN architecture in which the controller function — including authentication, policy enforcement, radio frequency management, and firmware distribution — is hosted in a vendor-operated cloud platform. Access points connect to the cloud platform for configuration and monitoring, while local traffic forwarding typically remains at the access point.
IT teams encounter this term when evaluating modern WiFi platforms from vendors such as Cisco Meraki, Aruba Central, and Juniper Mist. It is the dominant deployment model for new enterprise WiFi deployments as of 2024.
On-Premise WiFi Controller (WLC)
A physical or virtual appliance deployed within the enterprise network that centrally manages all access points, handling authentication, QoS, roaming, and security policy enforcement. All management traffic remains within the enterprise network perimeter.
IT teams encounter this in legacy enterprise environments and in organisations with strict data sovereignty or compliance requirements. Major platforms include Cisco Catalyst 9800, Aruba Mobility Controller, and Ruckus SmartZone.
Zero-Touch Provisioning (ZTP)
A deployment capability that allows network devices — access points, switches, or routers — to be shipped directly to a site and automatically configured upon first connection to the network, without requiring on-site engineer intervention. The device contacts a cloud management platform, downloads its pre-staged configuration, and becomes operational.
ZTP is a primary operational advantage of cloud-managed WiFi for multi-site deployments. It eliminates the need to pre-configure devices in a staging environment or dispatch engineers to remote sites for initial setup.
IEEE 802.1X
An IEEE standard for port-based network access control that provides an authentication framework for devices connecting to a LAN or WLAN. It requires a supplicant (the connecting device), an authenticator (the access point or switch), and an authentication server (typically a RADIUS server) to complete an authentication exchange before network access is granted.
IT teams implement 802.1X for staff WiFi networks to enforce per-user authentication, typically using EAP-TLS (certificate-based) or PEAP-MSCHAPv2 (username/password) as the inner authentication method. It is required for WPA3-Enterprise deployments.
WPA3-Enterprise
The current generation of WiFi security protocol for enterprise networks, defined by the Wi-Fi Alliance. WPA3-Enterprise uses IEEE 802.1X for authentication and supports 192-bit cryptographic strength (CNSA suite) for high-security environments. It provides forward secrecy, meaning that the compromise of a long-term key does not expose past session traffic.
IT teams should be deploying WPA3-Enterprise on all new staff WiFi SSIDs where hardware supports it. All Wi-Fi 6 and Wi-Fi 6E certified access points are required to support WPA3.
Captive Portal
A web page presented to users when they connect to a WiFi network, requiring them to complete an action — accepting terms of service, entering credentials, or providing personal information — before being granted internet access. Captive portals are implemented using DNS and HTTP redirection at the network level.
IT teams deploy captive portals for guest WiFi to enforce acceptable use policies, capture user data for marketing or analytics purposes, and comply with legal requirements for identifying users on public networks. Purple provides a fully customisable, GDPR-compliant captive portal as a core product feature.
GDPR (General Data Protection Regulation)
The European Union's primary data protection regulation, effective from May 2018, which governs the collection, processing, and storage of personal data relating to EU residents. Under GDPR, organisations must have a lawful basis for processing personal data, provide transparent privacy notices, and respect data subject rights including access, rectification, and erasure.
GDPR is directly relevant to guest WiFi deployments because the collection of email addresses, device identifiers, or behavioural data via a captive portal constitutes processing of personal data. Organisations must ensure their captive portal consent flows meet GDPR requirements for valid consent under Article 7.
OpenRoaming
A Wi-Fi Alliance standard built on Passpoint (IEEE 802.11u) that enables automatic, seamless WiFi authentication across networks operated by different providers, using credentials from a user's home identity provider (mobile carrier, employer, or platform account). Users connect without a captive portal, and the network authenticates them via a federated identity exchange.
IT teams deploying guest WiFi in venues with high repeat visitor rates — airports, hotel chains, retail estates — should evaluate OpenRoaming to reduce authentication friction for returning users. Purple supports OpenRoaming natively, enabling users who have previously authenticated via the Purple App to connect automatically at any Purple-enabled venue.
PCI DSS (Payment Card Industry Data Security Standard)
A set of security standards developed by the major card networks (Visa, Mastercard, Amex, Discover) that applies to any organisation that stores, processes, or transmits payment card data. PCI DSS includes specific requirements for network segmentation, access control, encryption, and monitoring that directly affect WiFi architecture design.
IT teams at hospitality, retail, and events venues must ensure that their WiFi architecture does not bring guest or staff networks into PCI DSS scope unnecessarily. The standard approach is to isolate payment card processing systems on a dedicated, firewalled network segment that is physically and logically separated from guest WiFi traffic.
WiFi Management Platform
A software platform that provides centralised visibility, configuration management, analytics, and policy enforcement for a wireless LAN deployment. This term encompasses both the network management layer (controller or cloud platform) and the application layer (guest experience, analytics, and compliance platforms such as Purple).
IT teams use this term when evaluating the full stack of software required to operate an enterprise WiFi deployment. It is important to distinguish between the network management layer (which controls how APs operate) and the intelligence layer (which extracts business value from the network).
Fallstudien
A 45-property mid-market hotel chain is replacing end-of-life WiFi infrastructure across its estate. Properties range from 80 to 220 rooms. The IT team consists of three engineers based at head office, with no dedicated on-site IT staff at individual properties. The chain wants to capture guest email addresses for its loyalty programme and needs GDPR-compliant data handling. Budget is constrained, with a preference for OpEx over CapEx. Which WiFi architecture should they choose, and how should Purple be deployed?
This scenario is a strong fit for cloud-managed WiFi with Purple as the guest experience layer. The recommended deployment approach is as follows.
Infrastructure selection: Deploy a cloud-managed platform such as Cisco Meraki MR or Aruba Instant On across all 45 properties. Use zero-touch provisioning: pre-stage AP configurations in the cloud management portal, then ship APs directly to each property for installation by local staff or a third-party field services provider. No on-site controller hardware is required.
SSID architecture: Configure three SSIDs per property: (1) a guest SSID mapped to an internet-only VLAN, with Purple's captive portal as the splash page; (2) a staff SSID using WPA3-Enterprise with 802.1X authentication against the chain's Active Directory via a cloud RADIUS service such as Cisco ISE or JumpCloud; (3) an IoT SSID for in-room devices, isolated on a dedicated VLAN with restricted inter-device communication.
Purple deployment: Configure Purple's captive portal on the guest SSID. Implement a two-step consent flow: step one collects the guest's email address and loyalty programme opt-in; step two presents the WiFi terms of service and GDPR privacy notice with explicit consent checkboxes. Connect Purple to the chain's CRM (e.g., Salesforce) via Purple's native connector to sync guest profiles automatically.
Compliance validation: Enable Purple's data retention policies to automatically anonymise guest records after 24 months in line with the chain's data retention schedule. Configure Purple's consent audit log to satisfy GDPR Article 7(1) requirements for demonstrating valid consent.
Ongoing management: All 45 properties are managed from a single cloud dashboard. Firmware updates are pushed automatically during the 02:00–04:00 maintenance window. The three-person IT team receives automated alerts for AP offline events and can remotely diagnose and resolve most issues without travel.
A Premier League football stadium with a capacity of 62,000 seats is upgrading its WiFi infrastructure ahead of a major international tournament. The stadium hosts 25 home matches per year plus concerts and corporate events. Peak concurrent users are estimated at 18,000 during sold-out events. The stadium's IT team has five engineers on-site. Data sovereignty is a concern as the stadium processes payment card data in its hospitality suites. The stadium wants to offer free guest WiFi to all fans and capture connection data for sponsorship reporting. What architecture is recommended?
This scenario warrants a hybrid architecture with on-premise controllers for the primary network and Purple as the analytics and guest experience layer.
Infrastructure selection: Deploy a centralised on-premise wireless LAN controller cluster (e.g., Cisco Catalyst 9800 or Aruba Mobility Controller) in the stadium's data centre. Deploy Wi-Fi 6E access points (802.11ax, 6 GHz band) across the bowl, concourses, hospitality suites, and back-of-house areas — approximately 800 to 1,200 APs depending on the stadium's geometry. Use a high-density AP deployment design with directional antennas to serve seated fans without co-channel interference.
Network segmentation: Create separate VLANs for: fan guest WiFi (internet-only, Purple captive portal); hospitality suite WiFi (internet plus access to point-of-sale systems, PCI DSS scoped); staff and operations WiFi (access to stadium management systems); and broadcast and media WiFi (dedicated high-bandwidth SSID for press and broadcast teams).
PCI DSS compliance: The hospitality suite network must be isolated from the guest network and subject to PCI DSS controls including network segmentation, access logging, and quarterly vulnerability scanning. The on-premise controller architecture supports this by keeping all PCI-scoped traffic within the stadium's network perimeter.
Purple deployment: Deploy Purple's captive portal on the fan guest WiFi SSID. For a stadium environment, minimise friction: use a single-click social login or the Purple App for authentication. Configure Purple's analytics to capture per-event connection counts, peak concurrent users, and return visitor rates — the key metrics for sponsorship reporting. Integrate Purple with the stadium's sponsorship management platform via API to automate report generation.
Capacity planning: For 18,000 peak concurrent users, target a minimum of one AP per 30 to 40 concurrent users in high-density seating areas, with a throughput budget of 2 to 5 Mbps per user for typical fan usage patterns (social media, messaging, live score apps).
A national retail chain with 280 stores wants to deploy guest WiFi to capture customer data for its marketing team, while also improving store operations through WiFi-based footfall analytics. The chain's IT team manages infrastructure centrally. Stores range from small convenience formats (500 sq ft) to large superstore formats (50,000 sq ft). Some stores are in areas with limited or unreliable internet connectivity. How should the architecture be designed to handle the connectivity variability?
Architecture: Cloud-managed WiFi with local AP survivability enabled, plus Purple for guest experience and analytics.
Connectivity resilience: For stores in areas with unreliable internet connectivity, configure APs with local survivability mode — this ensures that guest WiFi continues to operate with the last-known configuration even if the cloud management connection is lost. For the most connectivity-constrained stores, consider deploying a 4G/LTE failover router as a secondary WAN link, with automatic failover triggered when the primary connection drops below a defined threshold.
Tiered AP deployment: For small convenience formats, deploy two to three APs per store. For large superstore formats, deploy 15 to 25 APs with a high-density design in checkout and food service areas. Use the cloud management platform's template-based configuration to push consistent SSID, VLAN, and security policies across all 280 stores from a single configuration template.
Purple analytics for operations: Beyond guest data capture, configure Purple's footfall analytics to measure customer dwell time in key departments, identify peak traffic periods, and compare performance across the estate. This data feeds directly into the retail operations team's workforce planning and merchandising decisions.
Data architecture: Connect Purple to the chain's CDP (Customer Data Platform) via API to merge WiFi-derived behavioural data with transactional data from the POS system, creating unified customer profiles that the marketing team can use for personalised campaigns.
Szenarioanalyse
Q1. A regional NHS trust operates 12 hospitals and 45 GP surgeries across a county. The trust's IT team of eight engineers manages all infrastructure centrally. The trust is subject to NHS Data Security and Protection Toolkit requirements and processes patient data on its clinical networks. It wants to offer free guest WiFi to patients and visitors in waiting areas, and is evaluating whether to deploy cloud-managed or controller-based WiFi. What architecture would you recommend, and what are the key compliance considerations?
💡 Hinweis:Consider the NHS DSP Toolkit requirements around data residency and the separation between clinical and guest networks. Also consider the IT team's capacity to manage 57 sites.
Empfohlenen Ansatz anzeigen
The recommended architecture is cloud-managed WiFi for the guest network, with strict network segmentation to ensure the guest network is completely isolated from clinical systems. The 57-site scale and the small central IT team make cloud-managed WiFi the operationally superior choice — the alternative of deploying on-premise controllers at each site would require significantly more engineering resource than the team can sustain. The guest WiFi SSID should be on a dedicated VLAN with internet-only access, enforced by firewall rules that block all traffic to clinical network segments. This segmentation ensures that the guest network does not fall within the scope of NHS DSP Toolkit clinical data requirements. For data residency, select a cloud-managed platform that processes and stores data within the UK (or EEA at minimum), and verify this in the vendor's data processing agreement. Deploy Purple on the guest SSID for GDPR-compliant patient data capture, with consent flows that clearly distinguish between WiFi access (which requires minimal data) and optional marketing communications (which require explicit opt-in). The key compliance consideration is demonstrating to NHS Digital that clinical data cannot be accessed from the guest network — this requires documented network segmentation evidence, not just a policy statement.
Q2. A conference centre operator runs a single 15,000 sq metre venue that hosts 200 events per year, ranging from small boardroom meetings (20 delegates) to large exhibitions (5,000 attendees). The venue's IT team has two engineers. The operator wants to offer exhibitor-grade WiFi (dedicated bandwidth per stand) as a paid service, alongside free delegate WiFi. The venue currently has an ageing on-premise controller that is out of support. What architecture should replace it?
💡 Hinweis:Consider the variable density requirements (20 to 5,000 users), the paid WiFi service model, and the small IT team. Also consider how Purple can support the commercial model.
Empfohlenen Ansatz anzeigen
Replace the ageing on-premise controller with a cloud-managed WiFi platform, deploying Wi-Fi 6E access points throughout the venue. The cloud-managed model suits the small IT team and eliminates the hardware maintenance burden of an on-premise controller. For the paid exhibitor WiFi service, configure dedicated SSIDs per exhibition stand using dynamic VLAN assignment, with bandwidth shaping policies enforced at the access point level — all major cloud-managed platforms support this capability. For the free delegate WiFi, deploy Purple's captive portal to capture delegate data (email, organisation, job title) with GDPR-compliant consent, creating a valuable database for the venue's marketing and event follow-up activities. Purple's analytics will also provide the venue operator with per-event attendance data, dwell time metrics, and return visitor rates — useful for commercial reporting to event organisers. The variable density requirement (20 to 5,000 users) is handled by the cloud management platform's dynamic RF management, which automatically adjusts transmit power and channel allocation based on active user density. Ensure the AP deployment design includes sufficient density for peak exhibition capacity, and validate throughput during a high-density test before the first major event.
Q3. A luxury hotel group is deploying a new WiFi estate across 8 five-star properties in Europe. Each property has 150 to 300 rooms, multiple F&B outlets, spa facilities, and conference rooms. The group's CTO wants to use WiFi data to personalise the guest experience — recognising returning guests, understanding their movement patterns within the property, and triggering personalised offers via the hotel app. The group's legal team has flagged GDPR concerns about tracking guest movements. How should the architecture be designed to achieve the commercial objective while remaining GDPR-compliant?
💡 Hinweis:Consider the distinction between network-level data (which device is connected to which AP) and personal data (which guest is connected). GDPR compliance depends on the consent basis and the data minimisation principle.
Empfohlenen Ansatz anzeigen
Deploy cloud-managed WiFi across all 8 properties with Purple as the guest intelligence layer. The GDPR compliance framework requires careful design of the consent and data architecture. At the point of WiFi authentication via Purple's captive portal, present guests with a layered consent notice: the first layer covers basic WiFi access (minimal data, legitimate interest basis); the second layer, presented as an optional enhancement, covers personalised services including movement analytics and targeted offers (explicit consent basis, clearly described). Guests who consent to personalised services have their device's WiFi probe data associated with their guest profile, enabling movement pattern analysis. Guests who do not consent receive standard WiFi access without tracking. This approach satisfies GDPR's requirement for granular, informed consent and the data minimisation principle (only collecting movement data from guests who have explicitly consented). Purple's consent management framework records consent timestamps and scope for each guest, providing the audit trail required under GDPR Article 7. The hotel app integration allows consenting guests to receive personalised offers triggered by their location within the property — for example, a spa offer when they are near the spa entrance. The legal team should review the privacy notice language to ensure the description of movement analytics is sufficiently clear and specific to constitute valid informed consent.
Wichtigste Erkenntnisse
- ✓Cloud-managed WiFi is operationally superior for multi-site deployments (5+ sites) due to zero-touch provisioning, automatic firmware updates, and single-pane-of-glass management — typically delivering lower total cost of ownership than on-premise controllers within 18 to 24 months.
- ✓Controller-based WiFi remains the right choice for large single-campus deployments with strict data sovereignty requirements, PCI DSS scope concerns, or the need for advanced features such as granular QoS and real-time RF optimisation.
- ✓Purple operates as an infrastructure-agnostic WiFi intelligence overlay — it integrates with both cloud-managed and controller-based architectures, adding GDPR-compliant guest data capture, footfall analytics, and CRM integration without requiring changes to the underlying network infrastructure.
- ✓GDPR compliance for guest WiFi is non-negotiable and applies regardless of network architecture: consent must be explicit, granular, and recorded before any personal data is processed. Purple's consent management framework addresses this requirement out of the box.
- ✓Security best practice for any enterprise WiFi deployment requires WPA3-Enterprise on staff networks, strict VLAN segmentation between guest, staff, and IoT traffic, and a documented firmware management process — automated in cloud-managed deployments, scheduled quarterly in on-premise deployments.
- ✓The commercial ROI of guest WiFi analytics is well-evidenced: Purple customers including McDonald's (90% reduction in IT engineer site visits) and Brussels South Charleroi Airport (10,630% ROI) demonstrate that WiFi intelligence delivers measurable business value beyond connectivity.
- ✓Avoid the hybrid trap: if you must operate both cloud-managed and controller-based infrastructure, define explicit criteria for each deployment type and ensure your monitoring and security operations tools can span both environments — unmanaged architectural complexity erodes the cost savings you were trying to achieve.



