Como o Passpoint (Hotspot 2.0) Transforma a Experiência de Wi-Fi de Convidados
Um guia de referência técnica abrangente que detalha como os protocolos Passpoint (Hotspot 2.0) e 802.11u substituem os Captive Portals tradicionais por um roaming Wi-Fi seguro e contínuo, semelhante ao celular. Fornece aos líderes de TI visões gerais da arquitetura, estruturas de implementação e o caso de negócio para a adoção de autenticação baseada em credenciais para resolver desafios de randomização de MAC e melhorar a experiência do convidado.
🎧 Ouça este Guia
Ver Transcrição
- Resumo Executivo
- Aprofundamento Técnico
- O Problema da Seleção de Rede e o 802.11u
- Arquitetura de Autenticação e Segurança
- A Federação OpenRoaming
- Guia de Implementação
- Pré-requisitos de Infraestrutura
- A Estratégia de SSID Duplo
- Melhores Práticas
- Resolução de Problemas e Mitigação de Riscos
- ROI e Impacto no Negócio

Resumo Executivo
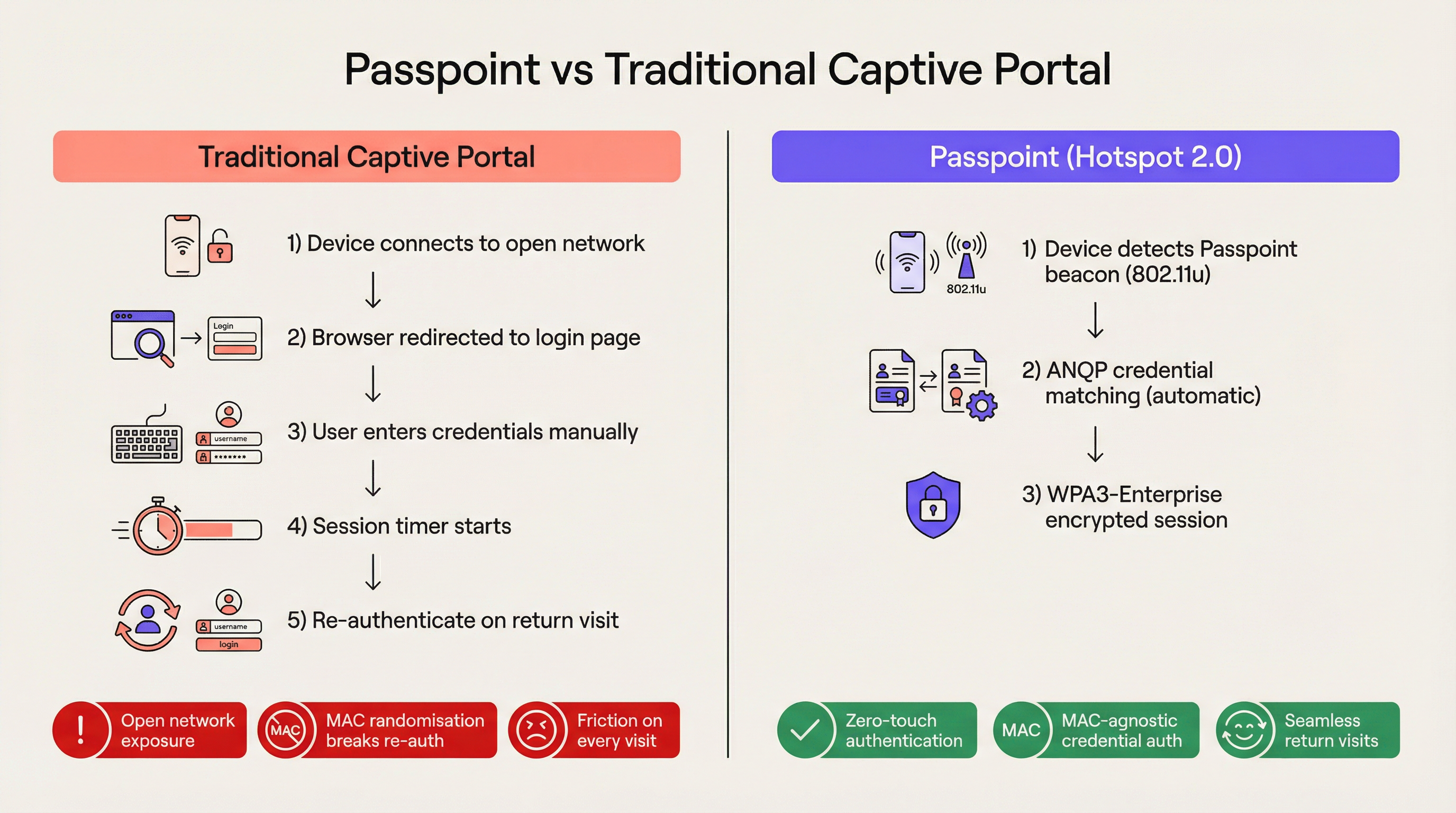
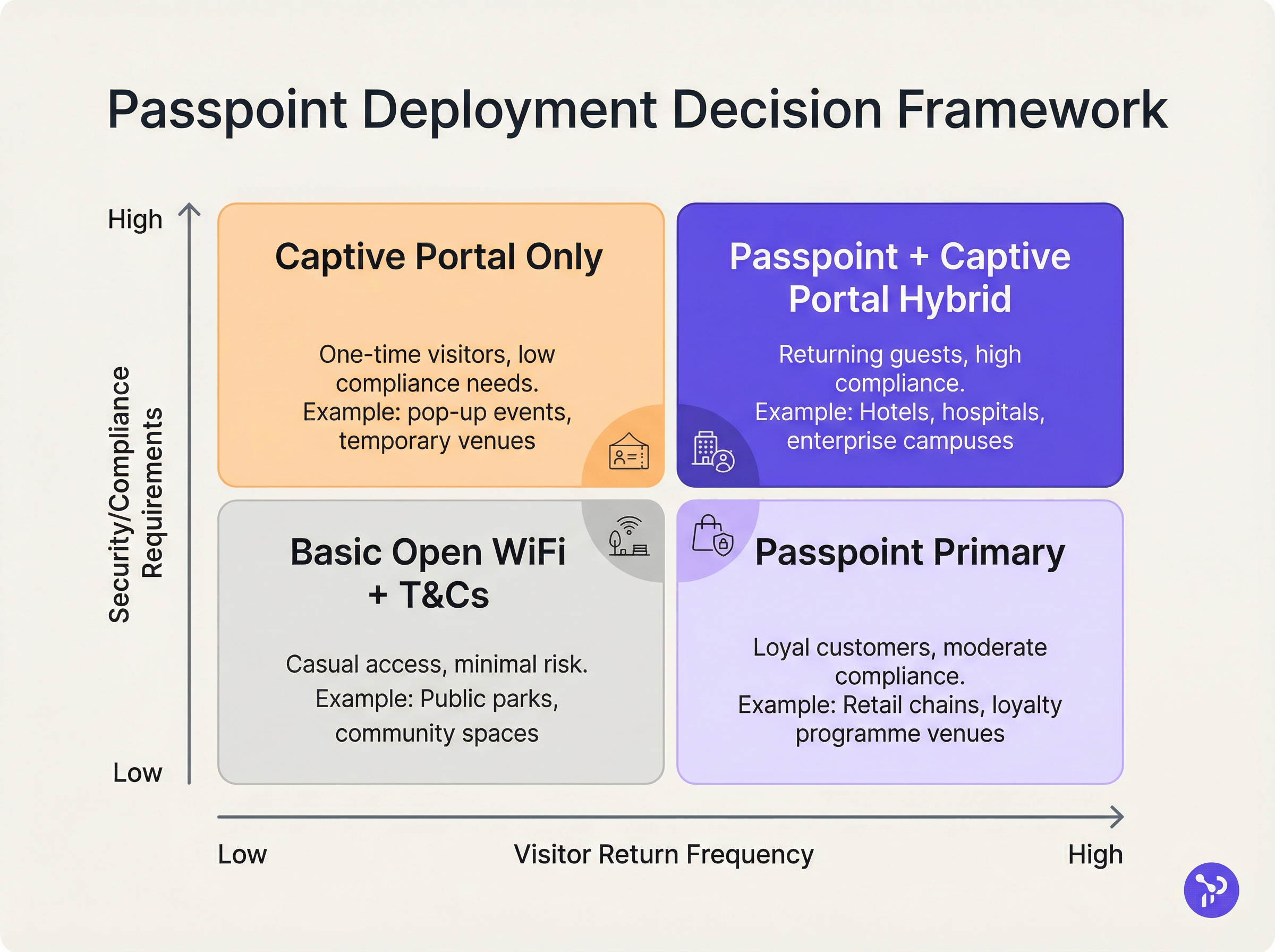
Para o espaço empresarial moderno, a fricção é uma desvantagem competitiva. Os Captive Portals tradicionais, embora outrora o padrão para o acesso à rede de convidados, representam agora um estrangulamento operacional significativo e uma fonte de frustração persistente para o utilizador. O Passpoint, também conhecido como Hotspot 2.0, transforma fundamentalmente este paradigma ao substituir a autenticação manual baseada na web por um roaming contínuo, semelhante ao celular. Ao tirar partido da norma IEEE 802.11u e da encriptação WPA3-Enterprise, o Passpoint permite que os dispositivos dos convidados descubram, autentiquem e se liguem a redes Wi-Fi empresariais de forma automática e segura.
Para os líderes de TI em Hospitality , Retail e grandes espaços públicos, a transição para o Passpoint já não é opcional. A randomização de endereços MAC predefinida implementada nos dispositivos iOS e Android modernos quebrou efetivamente a lógica de reautenticação dos Captive Portals legados, o que significa que os convidados que regressam aparecem como novos dispositivos em cada visita. O Passpoint resolve isto autenticando o perfil de credenciais do utilizador em vez do seu endereço de hardware. Este guia detalha a arquitetura técnica do Passpoint, o impacto comercial da implementação e uma estrutura de implementação neutra em termos de fornecedor, concebida para melhorar a experiência de Guest WiFi enquanto reduz a carga de trabalho do suporte técnico.
Aprofundamento Técnico
O Problema da Seleção de Rede e o 802.11u
Nas implementações de Wi-Fi legadas, os dispositivos dependem de um mecanismo fundamentalmente frágil para a seleção de rede: a procura de Service Set Identifiers (SSID) conhecidos. Esta abordagem exige que o utilizador se tenha ligado anteriormente à rede ou que selecione manualmente a rede de uma lista. Não fornece visibilidade pré-associação sobre a postura de segurança da rede, requisitos de autenticação ou disponibilidade de internet a montante. O Passpoint aborda esta limitação através da emenda IEEE 802.11u, que introduz o Interworking com Redes Externas.
Em vez de procurar passivamente por SSID, um dispositivo com Passpoint ativado consulta ativamente a infraestrutura de rede antes de tentar a associação. Quando um ponto de acesso transmite o seu beacon, inclui um Elemento de Interworking — um sinalizador que indica o suporte para 802.11u. O dispositivo cliente deteta este sinalizador e inicia um pedido de Generic Advertisement Service (GAS). Encapsulada neste pedido está uma consulta de Access Network Query Protocol (ANQP). O dispositivo pergunta à infraestrutura: "Que Roaming Consortium Organisational Identifiers (OIs) suporta?" Se a resposta do ponto de acesso corresponder a um perfil de credenciais armazenado no dispositivo, a autenticação automática prossegue.
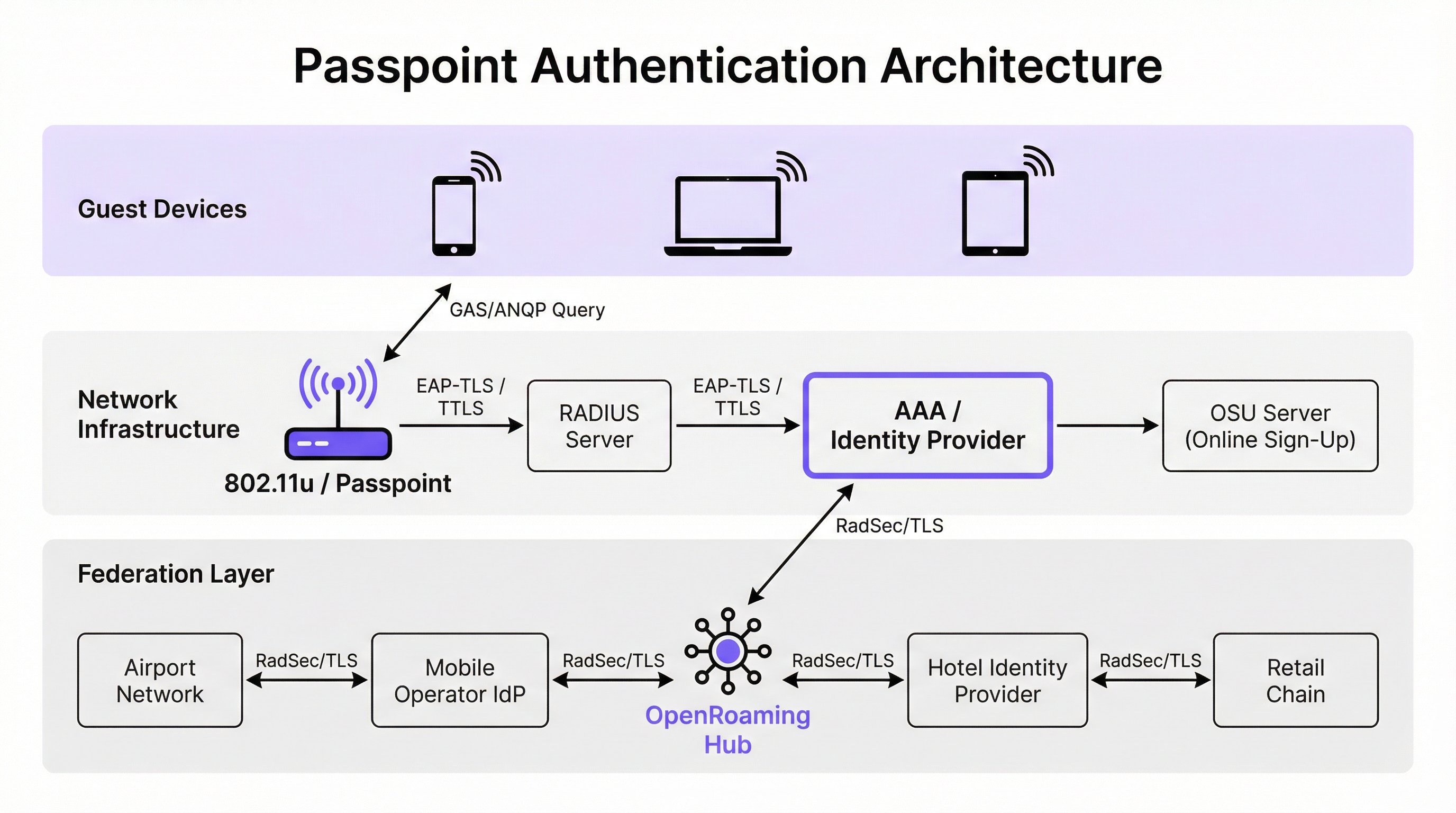
Arquitetura de Autenticação e Segurança
O Passpoint exige segurança de nível empresarial, eliminando completamente a fase de "rede aberta" inerente às implementações de Captive Portal. A autenticação é gerida através do controlo de acesso à rede baseado em porta IEEE 802.1X, juntamente com um método Extensible Authentication Protocol (EAP). Os métodos mais prevalentes em implementações empresariais são o EAP-TLS (baseado em certificados de cliente e servidor), EAP-TTLS (credenciais tuneladas) e EAP-SIM/AKA (para cenários de offload celular).
Esta arquitetura fornece autenticação mútua. O dispositivo prova criptograficamente a sua identidade à rede e, crucialmente, a rede prova a sua identidade ao dispositivo. Esta verificação mútua é a principal defesa contra pontos de acesso evil twin e tentativas de interceção man-in-the-middle. Além disso, o Passpoint exige encriptação WPA2-Enterprise ou WPA3-Enterprise. O WPA3-Enterprise introduz o modo de segurança de 192 bits e exige forward secrecy, garantindo que, mesmo que as chaves de sessão sejam comprometidas no futuro, o tráfego histórico permaneça encriptado.
A Federação OpenRoaming
Embora o Passpoint defina o mecanismo técnico para descoberta e autenticação, o OpenRoaming fornece a estrutura de confiança. Desenvolvido pela Wireless Broadband Alliance (WBA), o OpenRoaming é uma federação global que permite que os Fornecedores de Identidade (como operadores de rede móvel, Google ou Apple) e Fornecedores de Acesso (como hotéis, estádios e cadeias de retalho) confiem nas credenciais uns dos outros sem exigir acordos bilaterais entre todas as entidades.
O OpenRoaming opera num modelo de Public Key Infrastructure (PKI) hub-and-spoke. Os pedidos de autenticação são transmitidos através da federação utilizando túneis RadSec (RADIUS sobre TLS). Ao transmitir o OI OpenRoaming livre de liquidação (5A-03-BA), um espaço empresarial pode fornecer instantaneamente acesso Wi-Fi contínuo e seguro a milhões de utilizadores globalmente que já possuem um perfil de identidade compatível nos seus dispositivos.
Guia de Implementação
A implementação do Passpoint requer uma base de infraestrutura mais sofisticada do que uma rede aberta tradicional, mas os componentes são padrão em ambientes empresariais modernos.
Pré-requisitos de Infraestrutura
- Pontos de Acesso Certificados para Passpoint: A infraestrutura sem fios deve suportar as especificações 802.11u e Hotspot 2.0. A grande maioria dos pontos de acesso empresariais fabricados nos últimos cinco anos por fornecedores como a Cisco, Aruba e Ruckus cumprem este requisito.
- Infraestrutura RADIUS/AAA: Um servidor RADIUS robusto capaz de lidar com a autenticação EAP e encaminhar pedidos para os repositórios de identidade apropriados. Se participar no OpenRoaming, o servidor RADIUSrver deve suportar RadSec para proxying seguro.
- Servidor de Registo Online (OSU): Para ambientes que emitem as suas próprias credenciais (em vez de dependerem apenas de identidades federadas), um servidor OSU fornece o mecanismo para o aprovisionamento seguro de perfis Passpoint para dispositivos de convidados.
A Estratégia de SSID Duplo
O modelo de implementação mais eficaz para locais em transição para o Passpoint é a estratégia de SSID duplo. Esta abordagem mantém um SSID de Captive Portal tradicional para o onboarding inicial, enquanto disponibiliza um SSID Passpoint para ligações subsequentes sem interrupções.
Quando um convidado se liga ao SSID do Captive Portal pela primeira vez, conclui o fluxo de autenticação padrão (ex: aceitar termos e condições, fornecer um endereço de e-mail). Após a autenticação bem-sucedida, o portal apresenta uma opção para descarregar um perfil Passpoint. Uma vez instalado, o dispositivo preferirá automaticamente o SSID Passpoint seguro em todas as visitas futuras. Este modelo de onboarding progressivo garante a acessibilidade para dispositivos legados, enquanto migra a maioria dos utilizadores para a rede Passpoint segura e sem fricção.
Melhores Práticas
Ao desenhar uma arquitetura Passpoint, os líderes de TI devem aderir a várias melhores práticas críticas para garantir a estabilidade operacional e a segurança.
Em primeiro lugar, a gestão do ciclo de vida dos certificados é fundamental. Se utilizar EAP-TLS, a expiração dos certificados de cliente ou servidor resultará em falhas de autenticação silenciosas que são difíceis de diagnosticar pelos helpdesks de primeira linha. Implemente protocolos de renovação automática de certificados e monitorização proativa. Como destacado no nosso guia sobre Avaliação de Postura do Dispositivo para Controlo de Acesso à Rede , uma visibilidade robusta dos endpoints é essencial ao gerir o acesso baseado em certificados.
Em segundo lugar, garanta a compatibilidade com dispositivos legados. Embora o iOS 7+, Android 6+ e Windows 10+ suportem nativamente o Passpoint, certos dispositivos IoT, hardware legado e dispositivos estritamente geridos por empresas podem não ter suporte. A estratégia de SSID duplo mitiga este risco ao fornecer um método de acesso alternativo.
Em terceiro lugar, ao configurar elementos ANQP, certifique-se de que a Informação do Local é precisa e descritiva. Estes metadados são frequentemente exibidos pelo sistema operativo do dispositivo do cliente para fornecer contexto sobre a rede à qual o utilizador se está a ligar.
Resolução de Problemas e Mitigação de Riscos
A complexidade do Passpoint introduz domínios de falha específicos que diferem das implementações de Captive Portal.
Modo de Falha 1: Timeout ou Inacessibilidade do RADIUS Se o servidor RADIUS local não conseguir contactar o Fornecedor de Identidade a montante (especialmente em cenários de OpenRoaming federado), o handshake EAP expirará por timeout. Mitigação: Implemente infraestrutura RADIUS redundante e garanta uma monitorização robusta dos túneis RadSec. Reveja a nossa documentação técnica sobre RadSec: Sécurisation du trafic d'authentification RADIUS avec TLS para orientações de configuração.
Modo de Falha 2: Falhas no Aprovisionamento de Perfis Os utilizadores podem encontrar erros ao tentar descarregar o perfil Passpoint do servidor OSU, muitas vezes devido a limitações do navegador do Captive Portal em dispositivos móveis. Mitigação: Desenhe o fluxo do Captive Portal para sair do mini-navegador do assistente de rede cativa (CNA) para o navegador nativo do sistema do dispositivo antes de iniciar o download do perfil.
Modo de Falha 3: Impacto da Randomização de MAC na Análise de Dados Embora o Passpoint resolva a quebra de autenticação causada pela randomização de MAC, as plataformas de análise legadas que dependem apenas de endereços MAC continuarão a reportar contagens de visitantes imprecisas. Mitigação: Integre os registos de autenticação RADIUS com a sua plataforma de WiFi Analytics . Ao rastrear identificadores de credenciais únicos (como a Identidade de Utilizador Cobrável ou NAI anonimizado) em vez de endereços MAC, os locais podem restaurar métricas precisas de fluxo de visitantes e fidelização.
ROI e Impacto no Negócio
O caso de negócio para a implementação do Passpoint baseia-se em três pilares mensuráveis: eficiência operacional, redução de risco e experiência do utilizador.
Do ponto de vista operacional, a eliminação da fricção do Captive Portal correlaciona-se diretamente com uma redução nos tickets de suporte de TI relacionados com a conectividade Wi-Fi. Em grandes ambientes de Saúde ou Transportes , isto representa uma poupança de custos significativa.
Relativamente à mitigação de riscos, a mudança de redes abertas para a encriptação WPA3-Enterprise reduz substancialmente a exposição a riscos do local. Para ambientes de retalho sujeitos a PCI DSS, a redução na superfície de tratamento de dados (ao eliminar a recolha de credenciais via web) simplifica as auditorias de conformidade.
Finalmente, a melhoria na experiência do utilizador é profunda. Na hotelaria, os estudos mostram consistentemente que um Wi-Fi fiável e sem interrupções é um dos principais impulsionadores da satisfação dos hóspedes e da repetição de reservas. Ao implementar o Passpoint, os locais oferecem uma experiência de conectividade que espelha a fiabilidade das redes móveis, transformando o Wi-Fi de um utilitário frustrante numa comodidade premium e transparente.
Termos-Chave e Definições
IEEE 802.11u
The wireless networking standard amendment that enables Interworking with External Networks, allowing devices to query APs before associating.
When configuring wireless controllers, engineers must enable 802.11u to allow devices to discover Passpoint capabilities.
ANQP (Access Network Query Protocol)
A query and response protocol used by devices to discover network services, roaming agreements, and venue information before connecting.
IT teams configure ANQP profiles on the wireless controller to broadcast their supported Roaming Consortium OIs and NAI Realms.
Roaming Consortium OI
An Organisational Identifier broadcast by the access point that indicates which identity providers or federations the network supports.
If an enterprise joins OpenRoaming, they must ensure their APs broadcast the specific OpenRoaming OI (5A-03-BA).
OSU (Online Sign-Up)
A standardized process and server infrastructure for securely provisioning Passpoint credentials and certificates to a user's device.
When building a self-service onboarding flow for a loyalty programme, developers will integrate with an OSU server to push the profile to the device.
RadSec
A protocol that encapsulates RADIUS authentication traffic within a TLS tunnel to ensure secure transmission over untrusted networks.
Required when proxying authentication requests from a local venue to a cloud-based OpenRoaming hub.
NAI Realm
Network Access Identifier Realm; indicates the domain of the user and the specific EAP authentication methods supported by the network.
Configured alongside ANQP to tell client devices whether the network requires EAP-TLS, EAP-TTLS, or EAP-SIM.
EAP-TLS
Extensible Authentication Protocol - Transport Layer Security; a highly secure authentication method requiring both client and server certificates.
Often used in enterprise employee Wi-Fi deployments where IT can push certificates to managed devices via MDM.
MAC Address Randomisation
A privacy feature in modern mobile operating systems that generates a fake, temporary hardware address for each Wi-Fi network connection.
The primary catalyst driving venues away from captive portals, as it breaks the ability to recognize returning visitors based on their hardware.
Estudos de Caso
A 400-room enterprise hotel chain is experiencing a high volume of helpdesk tickets from returning guests who complain they must manually reconnect to the Wi-Fi in the lobby, restaurant, and their rooms, despite having connected previously. The hotel currently uses a traditional open SSID with a captive portal. How should the network architect resolve this?
The architect should implement a Dual-SSID strategy. First, deploy a secure Passpoint SSID broadcasting the hotel's specific Roaming Consortium OI. Second, modify the existing captive portal on the open SSID to serve as an onboarding funnel. When a guest logs in via the portal, they are prompted to download a Passpoint configuration profile to their device. Once installed, the device will automatically and securely authenticate via 802.1X/EAP to the Passpoint SSID as they move between the lobby, restaurant, and room, eliminating manual re-authentication.
A national retail chain wants to offer secure, seamless Wi-Fi across its 500 locations to drive loyalty app engagement. However, managing custom certificates or individual credentials for millions of potential customers is deemed operationally unfeasible. What is the recommended deployment architecture?
The retailer should deploy Passpoint and federate with OpenRoaming. By configuring their access points to broadcast the settlement-free OpenRoaming OI (5A-03-BA) and establishing RadSec tunnels from their RADIUS infrastructure to an OpenRoaming hub, the retailer allows any customer with a compatible identity provider profile (such as a modern Samsung device or a mobile carrier profile) to connect automatically. The retailer can then integrate this with their loyalty app to trigger push notifications upon successful network association.
Análise de Cenários
Q1. A hospital IT director wants to deploy Passpoint to ensure doctors' mobile devices connect securely to the clinical network, while patients connect to a separate guest network. The doctors use unmanaged personal devices (BYOD). Which EAP method and provisioning strategy should the architect recommend?
💡 Dica:Consider the balance between security and the operational overhead of managing certificates on unmanaged personal devices.
Mostrar Abordagem Recomendada
The architect should recommend EAP-TTLS with an Online Sign-Up (OSU) server provisioning flow. EAP-TLS requires client certificates, which are operationally difficult to deploy and manage on unmanaged BYOD devices. EAP-TTLS allows the doctors to authenticate securely using their existing Active Directory/LDAP credentials (username and password) tunneled inside a secure TLS session. The OSU server can provide a self-service portal where doctors log in once to download the profile, enabling automatic connection thereafter.
Q2. During a Passpoint deployment pilot, Android devices are successfully authenticating and connecting, but iOS devices are failing during the EAP handshake. The RADIUS logs show 'Unknown CA' errors. What is the most likely cause and solution?
💡 Dica:Apple's iOS has strict requirements regarding the trust chain for RADIUS server certificates.
Mostrar Abordagem Recomendada
The most likely cause is that the RADIUS server is using a self-signed certificate or a certificate issued by a private internal Certificate Authority (CA) that the iOS devices do not inherently trust. Android devices sometimes allow users to bypass or ignore certificate validation (though this is poor security practice), whereas iOS strictly enforces it for Passpoint profiles. The solution is to replace the RADIUS server certificate with one issued by a publicly trusted commercial CA (e.g., DigiCert, Let's Encrypt), or ensure the private CA root certificate is explicitly bundled within the Passpoint configuration profile pushed to the iOS devices.
Q3. A stadium venue has implemented OpenRoaming. A user with a valid Google OpenRoaming profile walks into the venue, but their device does not attempt to connect automatically. What specific configuration on the stadium's wireless LAN controller should the network engineer verify first?
💡 Dica:How does the device know that the access point supports the OpenRoaming federation before it attempts to connect?
Mostrar Abordagem Recomendada
The engineer should verify the ANQP configuration, specifically checking that the Access Points are broadcasting the correct Roaming Consortium Organisational Identifier (OI) for OpenRoaming, which is 5A-03-BA. If this OI is not included in the AP's beacon or GAS response, the device will not recognize the network as an OpenRoaming participant and will not attempt to authenticate.
Principais Conclusões
- ✓Passpoint (Hotspot 2.0) replaces manual captive portal logins with automatic, cellular-like Wi-Fi roaming.
- ✓It uses IEEE 802.11u for pre-association network discovery and WPA3-Enterprise for encrypted, mutually authenticated connections.
- ✓Passpoint solves the MAC address randomisation issue by authenticating the user's credential profile rather than their hardware address.
- ✓OpenRoaming is the global federation framework that allows Passpoint devices to connect across different venues seamlessly.
- ✓A dual-SSID strategy (Captive Portal for onboarding, Passpoint for returning users) is the recommended deployment model for enterprise venues.



