PEAP-MSCHAPv2: Porque Ainda é Comum, Porque é Arriscado e Como Evoluir
Um guia de referência técnica abrangente que detalha as vulnerabilidades de segurança críticas do PEAP-MSCHAPv2, incluindo ataques "evil twin" e captura de credenciais. Fornece um roteiro prático e neutro em relação a fornecedores para equipas de TI migrarem redes WiFi empresariais para a autenticação segura EAP-TLS baseada em certificados.
🎧 Ouça este Guia
Ver Transcrição
- Resumo Executivo
- Análise Técnica Profunda: A Anatomia da Vulnerabilidade
- A Falha Criptográfica
- O Vetor de Ataque "Evil Twin"
- Guia de Implementação: Migrar para EAP-TLS
- Fase 1: Auditoria e Inventário
- Fase 2: Implementação de PKI e Configuração de RADIUS
- Fase 3: Distribuição de Certificados via MDM
- Fase 4: Gestão de Dispositivos Legados
- Boas Práticas e Conformidade
- ROI e Impacto no Negócio
- Referências
Resumo Executivo
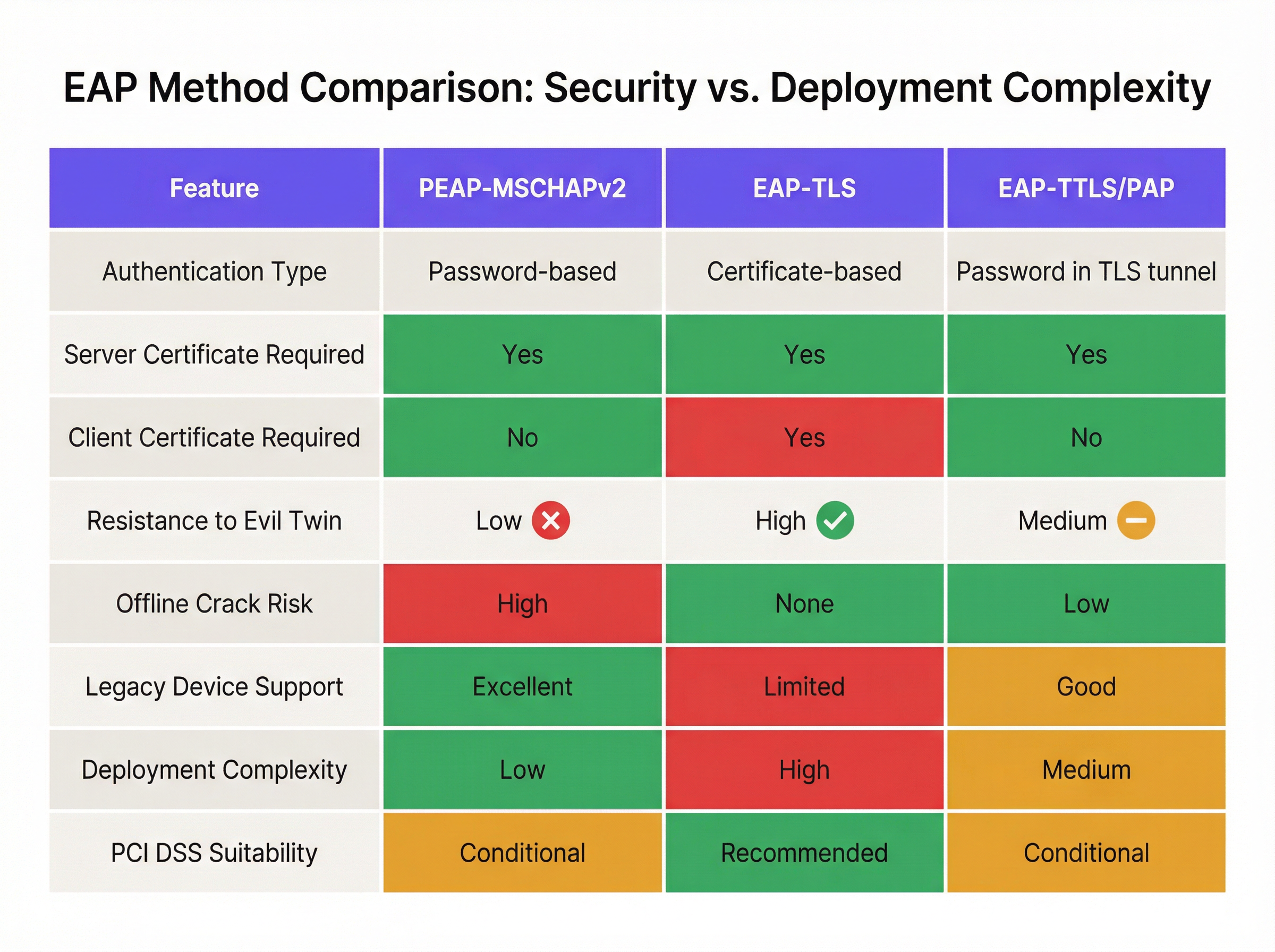
Apesar das vulnerabilidades criptográficas bem documentadas, o PEAP-MSCHAPv2 continua a ser o método EAP mais amplamente implementado para autenticação WiFi empresarial nos setores da hotelaria, retalho e público. A sua prevalência contínua é impulsionada pela facilidade de implementação — especificamente a sua integração nativa com o Active Directory — e não pela eficácia da segurança. No entanto, o perfil de risco mudou drasticamente. Ferramentas de exploração automatizadas tornaram o ataque "evil twin" acessível, permitindo que agentes maliciosos capturem e quebrem hashes de desafio-resposta MSCHAPv2 com um esforço trivial, levando diretamente ao comprometimento de credenciais do Active Directory.
Para diretores de TI e arquitetos de rede, o mandato é claro: o PEAP-MSCHAPv2 já não é adequado para qualquer ambiente sujeito a quadros de conformidade como o PCI DSS ou GDPR. Este guia fornece uma análise crítica dos vetores de ataque específicos que visam o PEAP-MSCHAPv2 e descreve um caminho de migração pragmático e faseado para o EAP-TLS. Ao tirar partido de soluções modernas de Gestão de Dispositivos Móveis (MDM) e de Infraestrutura de Chaves Públicas (PKI) na nuvem, as organizações podem transitar para uma autenticação robusta baseada em certificados sem interromper as operações comerciais ou alienar dispositivos legados.
Análise Técnica Profunda: A Anatomia da Vulnerabilidade
Para compreender por que razão o PEAP-MSCHAPv2 deve ser descontinuado, é necessário examinar a sua arquitetura criptográfica subjacente. O MSCHAPv2 (Microsoft Challenge Handshake Authentication Protocol versão 2) foi concebido no final da década de 1990 e baseia-se no algoritmo de hashing MD4 e no Data Encryption Standard (DES) [1]. Ambos são considerados obsoletos pelos padrões criptográficos modernos.
A Falha Criptográfica
A fraqueza fundamental reside na forma como o MSCHAPv2 gere o hash NT da palavra-passe do utilizador. O protocolo divide uma chave de 21 bytes derivada do hash NT em três chaves DES de 7 bytes. Crucialmente, a terceira chave utiliza apenas dois bytes significativos do hash, preenchendo o resto com bytes nulos. Esta falha estrutural reduz a complexidade criptográfica exponencialmente.
Em 2012, o investigador de segurança Moxie Marlinspike demonstrou que o handshake MSCHAPv2 podia ser quebrado de forma determinística, reduzindo o problema à quebra de uma única chave DES [2]. Utilizando serviços de quebra baseados na nuvem ou plataformas de GPU modernas que executam ferramentas como o hashcat, um atacante pode recuperar a palavra-passe do Active Directory em texto simples a partir de um handshake capturado em poucas horas, independentemente da complexidade da palavra-passe.
O Vetor de Ataque "Evil Twin"
A fraqueza criptográfica é explorada no terreno através do ataque "evil twin". Num cenário típico num escritório corporativo ou local de Hotelaria :
- Implementação de AP Falso: O atacante implementa um ponto de acesso falso (rogue AP) que transmite o SSID corporativo alvo (ex: "Staff-WiFi").
- Dominância de Sinal: O AP falso opera com uma potência de transmissão mais elevada, forçando os dispositivos clientes próximos a associarem-se a ele em vez de à infraestrutura legítima.
- Autenticação RADIUS Falsa: Quando o cliente inicia o túnel PEAP, o AP falso encaminha o pedido para um servidor RADIUS controlado pelo atacante (como o hostapd-wpe).
- Falha na Validação de Certificado: O servidor RADIUS falso apresenta um certificado digital autoassinado ou não verificado. Se o dispositivo cliente estiver mal configurado para ignorar a validação rigorosa do certificado do servidor — ou se o utilizador simplesmente clicar em "Aceitar" num aviso de confiança — o túnel é estabelecido.
- Captura de Credenciais: O cliente transmite o desafio-resposta MSCHAPv2 através do túnel comprometido. O atacante captura o hash e termina a ligação.
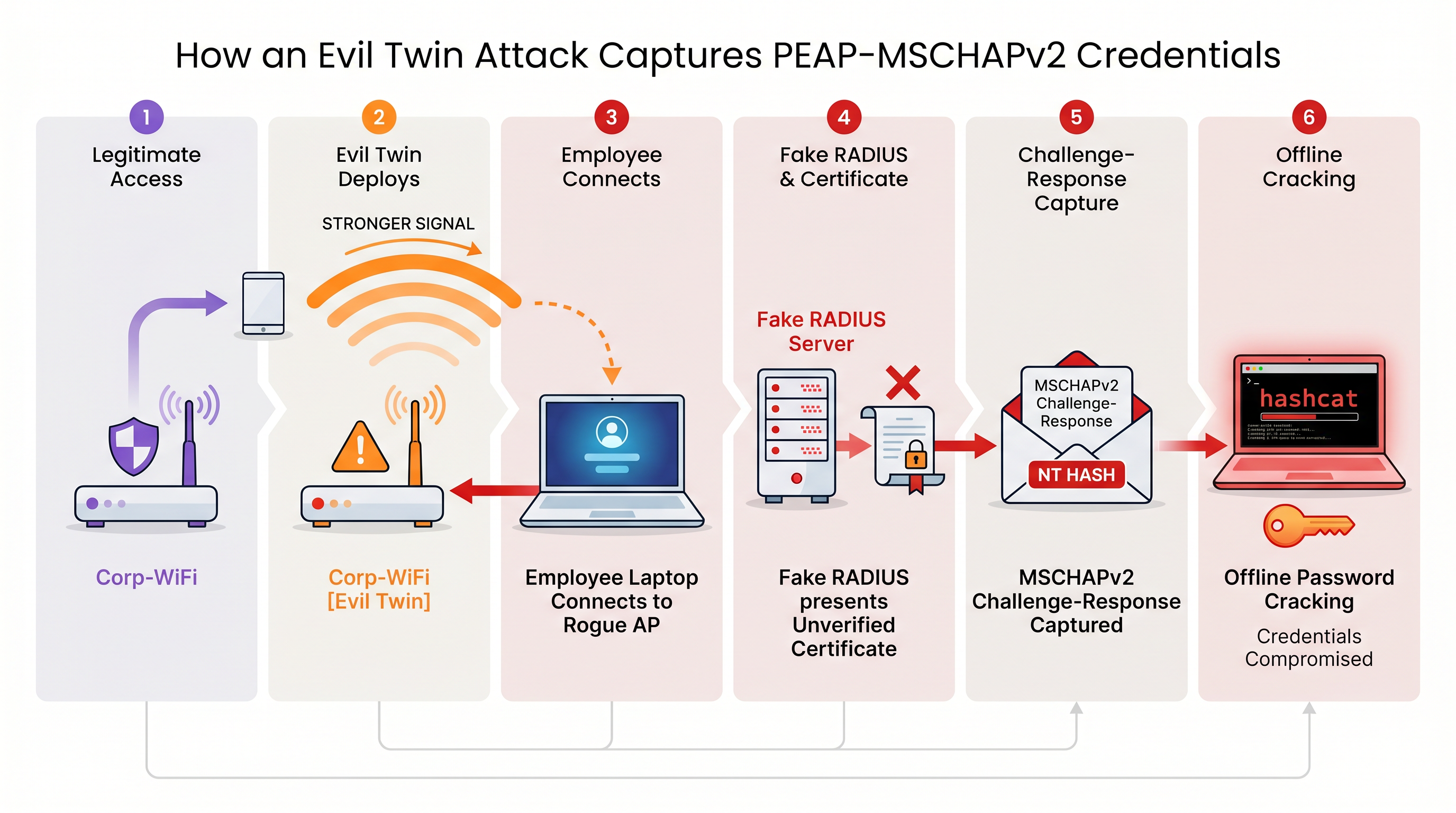
Sem uma validação rigorosa do certificado do servidor aplicada ao nível do endpoint, todos os dispositivos que utilizam PEAP-MSCHAPv2 estão vulneráveis a esta técnica de captura de credenciais. Isto é particularmente preocupante para ambientes de Retalho , onde as redes de apoio (back-of-house) partilham frequentemente proximidade física com espaços públicos.
Guia de Implementação: Migrar para EAP-TLS
A mitigação definitiva para as vulnerabilidades do MSCHAPv2 é a migração para o EAP-TLS (Extensible Authentication Protocol-Transport Layer Security). O EAP-TLS exige autenticação mútua: tanto o servidor RADIUS como o dispositivo cliente devem apresentar certificados digitais válidos. Como não são transmitidas ou transformadas em hash quaisquer palavras-passe durante o handshake, o EAP-TLS é inteiramente imune a ataques de dicionário offline e altamente resistente a falsificações "evil twin".
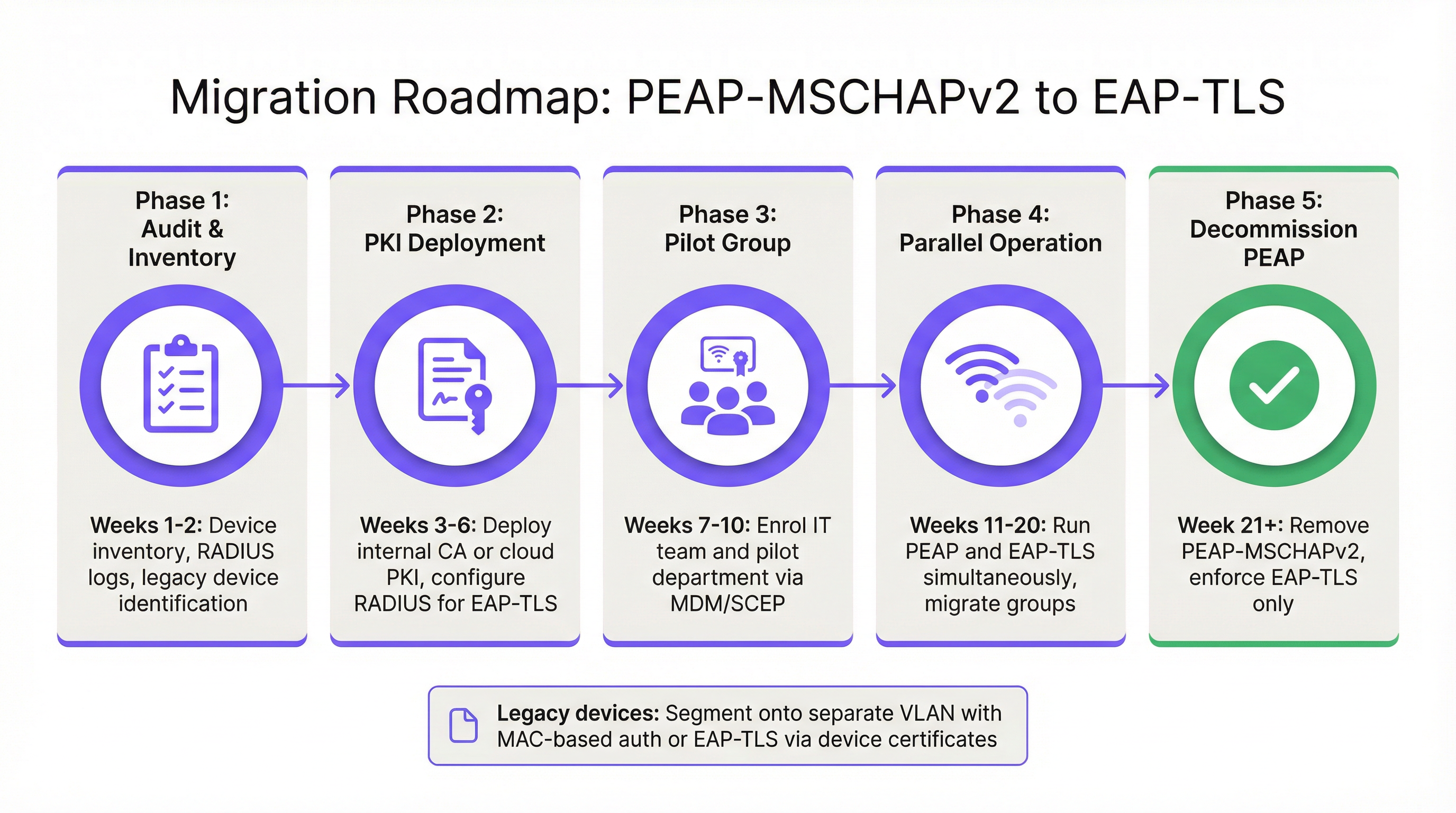
Historicamente, a barreira à adoção do EAP-TLS era a complexidade de implementar uma Infraestrutura de Chaves Públicas (PKI) local. Hoje, a PKI na nuvem e as integrações modernas de MDM simplificaram o processo.
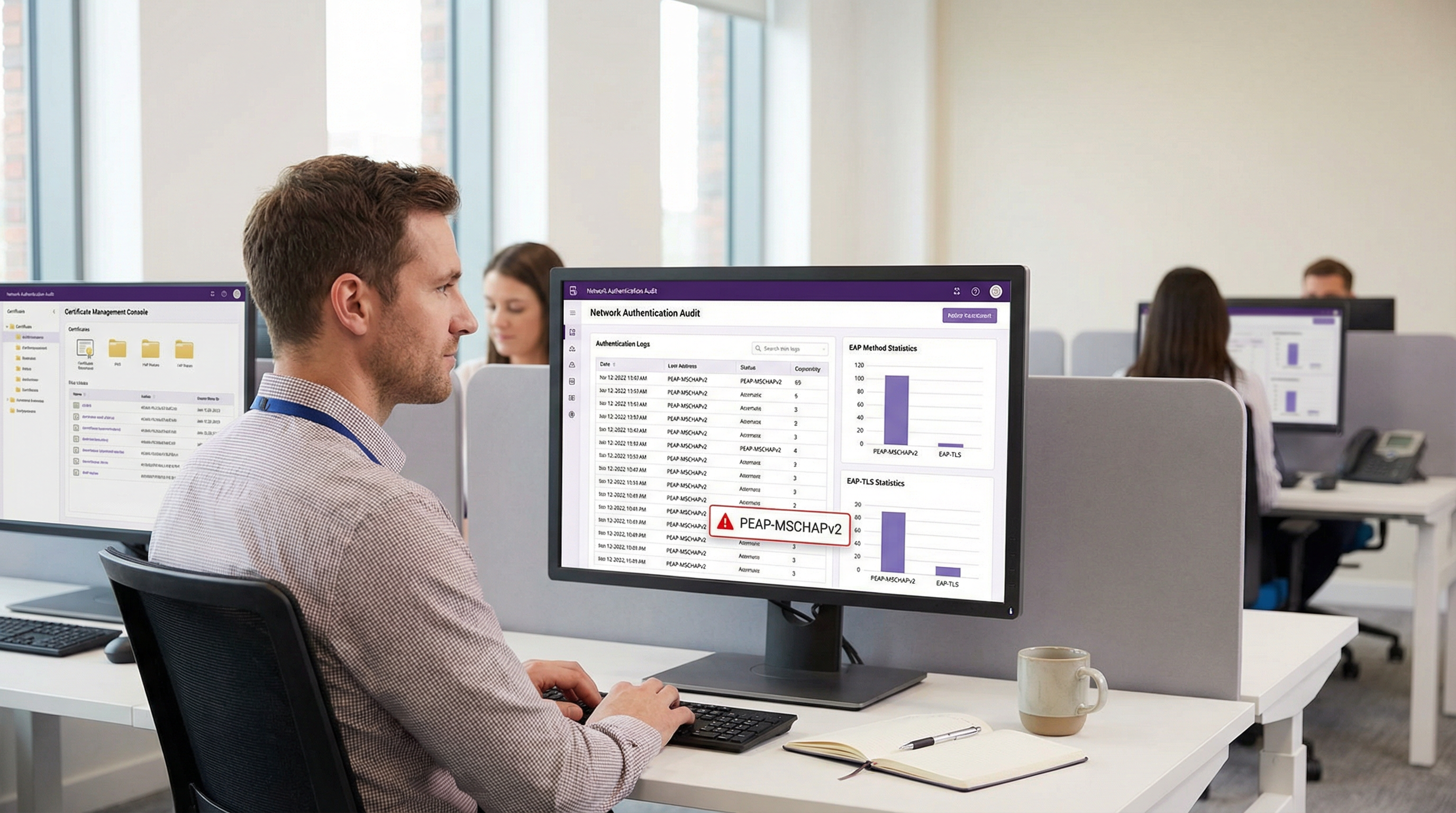
Fase 1: Auditoria e Inventário
Antes de alterar as políticas de autenticação, realize uma auditoria abrangente aos seus registos RADIUS atuais (ex: Cisco ISE, Aruba ClearPass ou Windows NPS). Identifique todos os dispositivos que se autenticam atualmente via PEAP. Categorize estes dispositivos em dois grupos:
- Dispositivos Geridos: Portáteis, tablets e smartphones corporativos inscritos numa plataforma de MDM (ex: Intune, Jamf).
- Dispositivos Não Geridos/Legados: Sensores IoT, terminais de ponto de venda antigos, leitores de códigos de barras ou dispositivos BYOD que não suportam a inscrição de certificados.
Fase 2: Implementação de PKI e Configuração de RADIUS
Implemente uma solução de PKI para emitir certificados de cliente e servidor. As plataformas de PKI nativas da nuvem podem integrar-se diretamente com o Entra ID ou Google Workspace, eliminando a necessidade de uma infraestrutura pesada de Microsoft AD CS local. Configure o seu servidor RADIUS para aceitar autenticação EAP-TLS. Crucialmente, configure a política de rede para suportar simultaneamente PEAP e EAP-TLS no mesmo SSID durante o período de transição.
Fase 3: Distribuição de Certificados via MDM
Aproveite a sua plataforma de MDM para distribuir silenciosamente certificados de cliente para dispositivos geridos utilizando protocolos como o SCEP (Simple Certificate Enrollment Protocol). Simultaneamente, envie uma atualização de perfil WiFi via MDM que instrua os dispositivos a priorizar o EAP-TLS para o SSID corporativo. Isto garante uma transição sem intervenção (zero-touch) para os utilizadores finais.
Fase 4: Gestão de Dispositivos Legados
Os dispositivos legados que não suportam EAP-TLS nunca devem ditar a postura de segurança da rede corporativa principal. Em vez disso, segmente estes dispositivos numa VLAN dedicada. Implemente o MAC-based Authentication Bypass (MAB) combinado com Listas de Controlo de Acesso (ACLs) rigorosas para garantir que estes dispositivos apenas comunicam com os servidores internos específicos necessários para a sua função.
Boas Práticas e Conformidade
Manter um ambiente sem fios empresarial seguro requer a adesão contínua aos padrões da indústria.
- Impor Validação de Certificado do Servidor: Se tiver de manter temporariamente o PEAP-MSCHAPv2, utilize o MDM para impor o pinning rigoroso do certificado do servidor em todos os endpoints. Impeça os utilizadores de confiar manualmente em certificados desconhecidos.
- Descontinuar WPA2-Personal: Garanta que todo o acesso corporativo depende de 802.1X (WPA2/WPA3-Enterprise). As Chaves Pré-Partilhadas (PSK) devem ser estritamente limitadas a redes IoT isoladas.
- Alinhar com o PCI DSS: Para locais que processam pagamentos, o Requisito 4 do PCI DSS exige criptografia forte para a transmissão de dados de titulares de cartões em redes sem fios. O PCI Security Standards Council recomenda explicitamente o EAP-TLS para uma autenticação robusta [3].
- Monitorizar Análises: Utilize plataformas como o WiFi Analytics da Purple para monitorizar a saúde da rede, identificar padrões de ligação anómalos e garantir que dispositivos legados não tentam aceder a sub-redes restritas.
ROI e Impacto no Negócio
O retorno sobre o investimento (ROI) da migração para o EAP-TLS é medido principalmente na mitigação de riscos. Um ataque "evil twin" bem-sucedido contra o PEAP-MSCHAPv2 produz credenciais válidas do Active Directory, proporcionando aos atacantes acesso inicial à rede corporativa. O impacto financeiro de uma violação de dados resultante, implementação de ransomware ou multa regulatória (como ao abrigo do GDPR) supera largamente o custo operacional de implementar uma PKI na nuvem e atualizar perfis de MDM.
Além disso, a autenticação baseada em certificados reduz significativamente o volume de pedidos de suporte relacionados com expiração e bloqueio de palavras-passe. Ao mudar para o EAP-TLS, as equipas de TI eliminam a fricção do acesso WiFi baseado em palavras-passe, proporcionando uma experiência de conectividade segura e contínua que suporta arquiteturas de rede modernas de confiança zero (zero-trust).
Referências
[1] Microsoft Security Response Center. "Weaknesses in MS-CHAPv2 authentication." Agosto 2012. [2] Marlinspike, Moxie. "Defeating PPTP VPNs and WPA2 Enterprise with MS-CHAPv2." DEF CON 20, 2012. [3] PCI Security Standards Council. "Information Supplement: PCI DSS Wireless Guidelines."
Termos-Chave e Definições
PEAP (Protected Extensible Authentication Protocol)
An EAP method that encapsulates the authentication process within a secure TLS tunnel to protect the inner authentication credentials from being intercepted over the air.
Widely used because it only requires a server-side certificate, making it easier to deploy than mutually authenticated methods.
MSCHAPv2
The inner authentication protocol commonly used inside a PEAP tunnel, which relies on a challenge-response mechanism using the NT hash of the user's password.
The primary source of vulnerability in PEAP deployments due to its reliance on outdated MD4 hashing and DES encryption.
EAP-TLS
An EAP method requiring mutual authentication, where both the RADIUS server and the client device present digital certificates to prove their identity.
The industry gold standard for enterprise WiFi security, immune to offline dictionary and evil twin attacks.
Evil Twin Attack
A wireless attack where a rogue access point mimics a legitimate corporate SSID to trick client devices into connecting, allowing the attacker to intercept traffic or capture authentication credentials.
The primary vector used by attackers to capture MSCHAPv2 handshakes from vulnerable PEAP deployments.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The core server infrastructure (like Cisco ISE or NPS) that processes 802.1X authentication requests from access points.
PKI (Public Key Infrastructure)
A set of roles, policies, hardware, software, and procedures needed to create, manage, distribute, use, store, and revoke digital certificates.
The foundational infrastructure required to deploy EAP-TLS, increasingly delivered via cloud-native SaaS platforms.
MDM (Mobile Device Management)
Software that allows IT administrators to control, secure, and enforce policies on smartphones, tablets, and endpoints.
Essential for EAP-TLS migrations, as it is used to silently push client certificates and strict WiFi profiles to corporate devices.
MAB (MAC Authentication Bypass)
A port-based access control method that authenticates devices based on their MAC address rather than requiring a username/password or certificate.
Used as a fallback mechanism to authenticate legacy 'headless' devices (like printers) that cannot support 802.1X protocols.
Estudos de Caso
A 400-room hotel chain is currently using PEAP-MSCHAPv2 for its back-of-house staff network. The IT director wants to migrate to EAP-TLS but is concerned about 50 legacy handheld inventory scanners that run an outdated OS and do not support certificate enrollment. How should the network architect handle this migration without breaking inventory operations?
The network architect should implement a segmented approach. First, deploy a cloud PKI and configure the central RADIUS server to accept both EAP-TLS and PEAP-MSCHAPv2. Use the hotel's MDM platform to push client certificates and an updated EAP-TLS WiFi profile to all modern staff laptops and tablets. For the 50 legacy scanners, create a dedicated, hidden SSID mapped to an isolated VLAN. Configure MAC-based Authentication Bypass (MAB) for these specific scanner MAC addresses on the RADIUS server. Apply strict network ACLs to this VLAN so the scanners can only reach the inventory database server and nothing else. Once all modern devices are using EAP-TLS, disable PEAP-MSCHAPv2 on the primary staff network.
A retail organisation has rolled out Windows 11 22H2 to its corporate fleet. The IT helpdesk is suddenly receiving tickets that users cannot connect to the corporate WPA2-Enterprise WiFi network, which uses PEAP-MSCHAPv2. What is the likely cause, and what is the immediate remediation?
The likely cause is the introduction of Windows Defender Credential Guard, which is enabled by default in Windows 11 22H2 and newer. Credential Guard isolates and protects NTLM password hashes and Kerberos Ticket Granting Tickets. Because PEAP-MSCHAPv2 requires access to the NT hash to generate the challenge-response, Credential Guard intentionally breaks this authentication method to prevent credential theft. The immediate remediation is to accelerate the migration to EAP-TLS, which uses certificate-based authentication and is fully compatible with Credential Guard. A temporary, less secure workaround would be disabling Credential Guard via Group Policy, but this is strongly discouraged as it weakens the overall OS security posture.
Análise de Cenários
Q1. You are auditing a newly acquired subsidiary's wireless network. They use PEAP-MSCHAPv2. The IT manager claims they are secure from evil twin attacks because they have hidden the SSID and disabled SSID broadcasting. Is their network secure from credential capture?
💡 Dica:Consider how client devices behave when configured to connect to hidden networks, and whether hiding an SSID prevents a rogue AP from spoofing it.
Mostrar Abordagem Recomendada
No, the network is not secure. Hiding the SSID (disabling beacon frames) provides zero cryptographic security. In fact, devices configured to connect to hidden networks actively broadcast probe requests containing the SSID name, effectively announcing the hidden network to any attacker listening. An attacker can easily capture the SSID name, spin up an evil twin AP broadcasting that exact SSID, and execute the standard MSCHAPv2 credential capture attack. The only defense is strict server certificate validation or migrating to EAP-TLS.
Q2. During an EAP-TLS migration pilot, you push client certificates to 20 Windows laptops via Intune. However, authentication fails for all 20 devices. The RADIUS server logs show 'Client Certificate Not Trusted'. The client certificates were issued by your new Cloud PKI. What critical configuration step was missed?
💡 Dica:For mutual authentication to work, both sides must trust the entity that issued the other side's certificate.
Mostrar Abordagem Recomendada
The RADIUS server has not been configured to trust the Root CA of the new Cloud PKI. While the laptops have the correct client certificates, when they present them to the RADIUS server, the server rejects them because it does not have the Cloud PKI's Root/Intermediate certificates in its local trust store. You must import the public Root CA certificate of the Cloud PKI into the RADIUS server's trusted certificate authorities store.
Q3. Your organisation mandates EAP-TLS for the corporate WiFi. A senior executive insists on connecting their personal, unmanaged iPad to the corporate network to access internal financial dashboards. How do you accommodate this request while maintaining the EAP-TLS security posture?
💡 Dica:Consider the prerequisites for EAP-TLS and the definition of a 'managed' device.
Mostrar Abordagem Recomendada
You cannot securely accommodate this request on the primary corporate network without compromising the EAP-TLS architecture. EAP-TLS requires a client certificate. Because the iPad is unmanaged (BYOD), the IT department cannot securely push a certificate via MDM. Allowing the executive to manually install a certificate introduces significant risk and administrative overhead. The correct approach is to deny access to the corporate SSID. Instead, the executive should connect to the Guest WiFi and use a secure corporate VPN (which supports modern MFA/SAML authentication) to access internal resources, or the device must be enrolled in the corporate MDM to receive a certificate.
Principais Conclusões
- ✓PEAP-MSCHAPv2 relies on obsolete cryptography (MD4 and DES) that can be trivially cracked offline.
- ✓The protocol is highly vulnerable to 'Evil Twin' attacks if endpoint devices do not strictly validate the RADIUS server certificate.
- ✓Modern Windows updates (Credential Guard) are actively breaking MSCHAPv2 authentication to prevent hash theft.
- ✓EAP-TLS is the definitive replacement, offering mutual authentication via digital certificates and immunity to offline cracking.
- ✓Cloud PKI and modern MDM platforms have drastically reduced the complexity and cost of deploying EAP-TLS.
- ✓Legacy devices incompatible with EAP-TLS must be segmented onto dedicated, restricted VLANs rather than degrading primary network security.



