WiFi para Invitados compatible con HIPAA para Proveedores de Atención Médica
Esta guía de referencia técnica proporciona estrategias de cumplimiento aplicables para equipos de TI de atención médica que implementan WiFi para invitados. Cubre la segmentación de red, el manejo de datos y los requisitos de BAA para garantizar una experiencia de visitante fluida sin comprometer los estándares HIPAA.
🎧 Escucha esta guía
Ver transcripción
- Resumen Ejecutivo
- Análisis Técnico Detallado
- El Modelo de Segmentación de Tres Zonas
- Estándares de Autenticación y Cifrado
- Guía de Implementación
- Configuración del Captive Portal
- Acuerdos de Asociado Comercial (BAA)
- Mejores Prácticas
- Solución de Problemas y Mitigación de Riesgos
- Mala Configuración de Puntos de Acceso Compartidos
- Redes 'Temporales' Maliciosas
- Aumento Gradual de la Retención de Datos del Proveedor
- ROI e Impacto Empresarial
Resumen Ejecutivo
Los directores de TI de atención médica y los arquitectos de red se enfrentan a un desafío persistente: ofrecer un WiFi para Invitados robusto para pacientes y visitantes sin exponer a la organización a los riesgos de cumplimiento de HIPAA. Si bien una red de invitados pura no procesa inherentemente información de salud protegida electrónicamente (ePHI), la convergencia de la infraestructura de invitados y clínica a menudo crea vulnerabilidades no deseadas. Esta guía proporciona un marco práctico y neutral para el proveedor para implementar WiFi para invitados compatible con HIPAA. Cubre el modelo esencial de segmentación de tres zonas, estrategias de minimización de datos para Captive Portals, y las condiciones precisas bajo las cuales se requiere un Acuerdo de Asociado Comercial (BAA) con su proveedor de WiFi. Al tratar el WiFi para invitados como un proyecto de infraestructura con un componente de cumplimiento, las organizaciones pueden mejorar con confianza la experiencia del paciente en hospitales, clínicas ambulatorias e instalaciones de Atención Médica relacionadas.
Análisis Técnico Detallado
La base del WiFi para invitados compatible con HIPAA reside en una arquitectura de red rigurosa. La Regla de Seguridad exige la protección de la ePHI contra el acceso no autorizado, lo que se traduce técnicamente en un aislamiento estricto entre los dispositivos de invitados no confiables y los sistemas clínicos críticos.
El Modelo de Segmentación de Tres Zonas
Para lograr el cumplimiento, las redes de atención médica deben implementar una estrategia de segmentación de tres zonas. Esta arquitectura previene el movimiento lateral desde el entorno de invitados hacia áreas donde reside la ePHI.
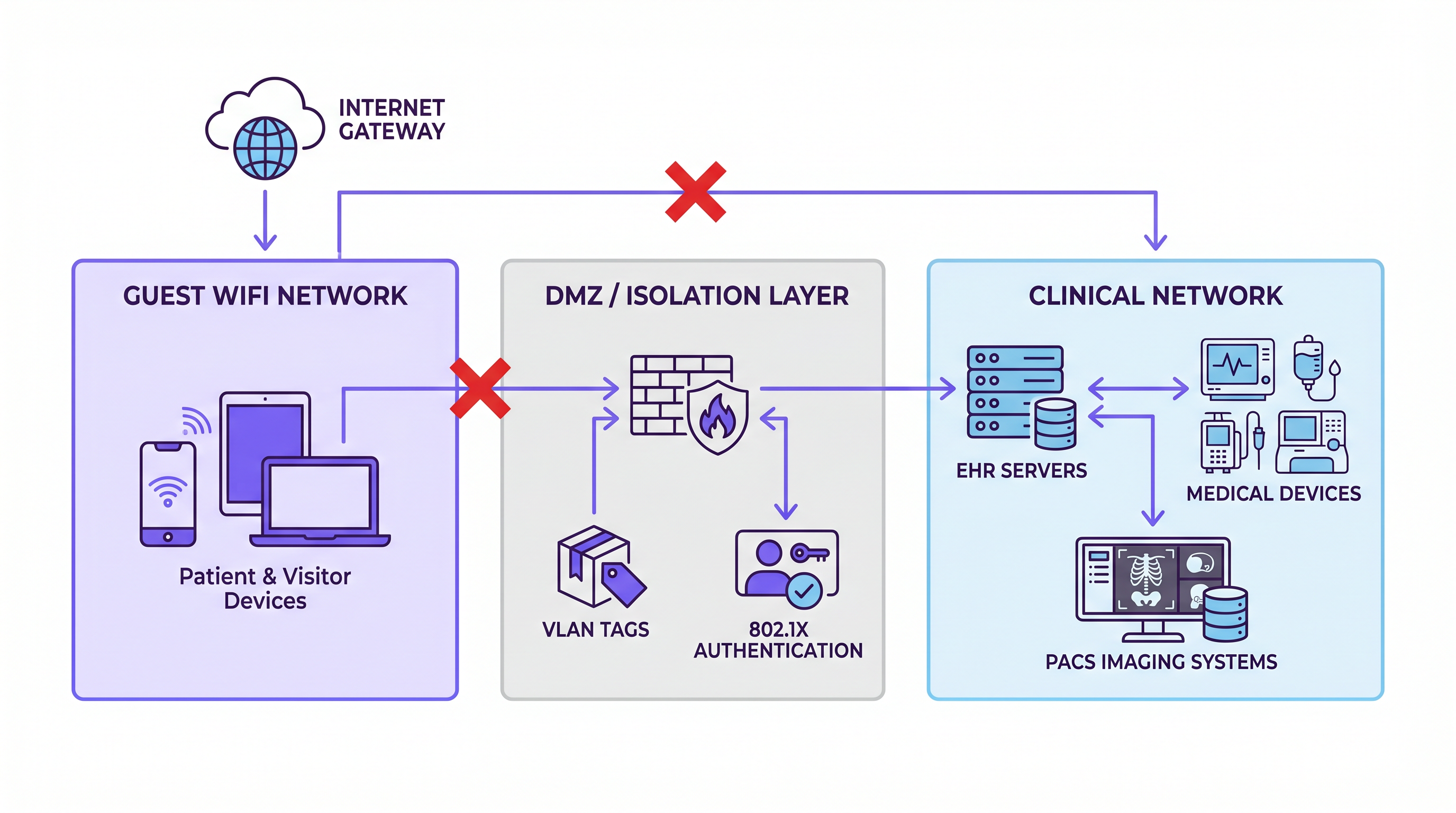
Zona 1: Red de Invitados Esta zona atiende a dispositivos de pacientes y visitantes. Proporciona acceso a internet exclusivamente. No debe haber enrutamiento a sistemas internos ni acceso a VLAN clínicas. El tráfico de esta zona debe salir directamente a través de la puerta de enlace de internet.
Zona 2: DMZ / Capa de Aislamiento La capa de aislamiento aloja el Captive Portal, los sistemas de autenticación y cualquier infraestructura de recopilación de datos. Si implementa una plataforma de Análisis de WiFi para capturar datos de conexión o tiempo de permanencia, reside aquí. Esta zona está lógicamente separada tanto de la red de invitados como de la clínica, actuando como un intermediario controlado.
Zona 3: Red Clínica Esta zona contiene servidores EHR, dispositivos médicos, sistemas de imágenes PACS y plataformas de comunicación clínica. Debe estar completamente aislada de las Zonas 1 y 2 a nivel de red. Las reglas del firewall deben aplicar una postura de denegación por defecto, asegurando que cualquier tráfico entre zonas viaje a través de rutas explícitas y auditadas.
Estándares de Autenticación y Cifrado
Si bien WPA3 Personal es el estándar preferido para las redes de invitados —proporcionando cifrado de datos individualizado incluso en redes abiertas para proteger contra la escucha— no garantiza inherentemente el cumplimiento de HIPAA. El cumplimiento se logra a través de la arquitectura general. Para la red clínica, la autenticación basada en puerto IEEE 802.1X es esencial para garantizar que solo los dispositivos autorizados puedan conectarse, evitando que dispositivos no autorizados cierren la brecha entre los entornos de invitados y clínicos.
Guía de Implementación
La implementación de una solución de WiFi para invitados compatible requiere una configuración cuidadosa y un enfoque de minimización de datos.
Configuración del Captive Portal
El Captive Portal es una fuente común de exposición inadvertida a HIPAA. Si el portal requiere que los usuarios envíen información identificable (como nombre, dirección de correo electrónico o fecha de nacimiento) y esos usuarios son pacientes, el conjunto de datos resultante podría vincularse a un encuentro de atención médica, creando así ePHI.
Para mitigar este riesgo, implemente una estrategia de recopilación de datos mínima. Capture solo la dirección MAC y la marca de tiempo de conexión. Si es necesaria una recopilación de datos más rica para marketing o análisis operativos, asegúrese de que los datos estén genuinamente anonimizados y no puedan vincularse a un registro de paciente específico. Al evaluar los marcos de privacidad globales, considere cómo estas prácticas se alinean con regulaciones más amplias, como se discute en nuestra guía sobre CCPA vs GDPR: Cumplimiento Global de Privacidad para Datos de WiFi de Invitados .
Acuerdos de Asociado Comercial (BAA)
Determinar si necesita un BAA con su proveedor de WiFi es un paso crítico para el cumplimiento. Un proveedor se convierte en un Asociado Comercial si crea, recibe, mantiene o transmite ePHI en su nombre.
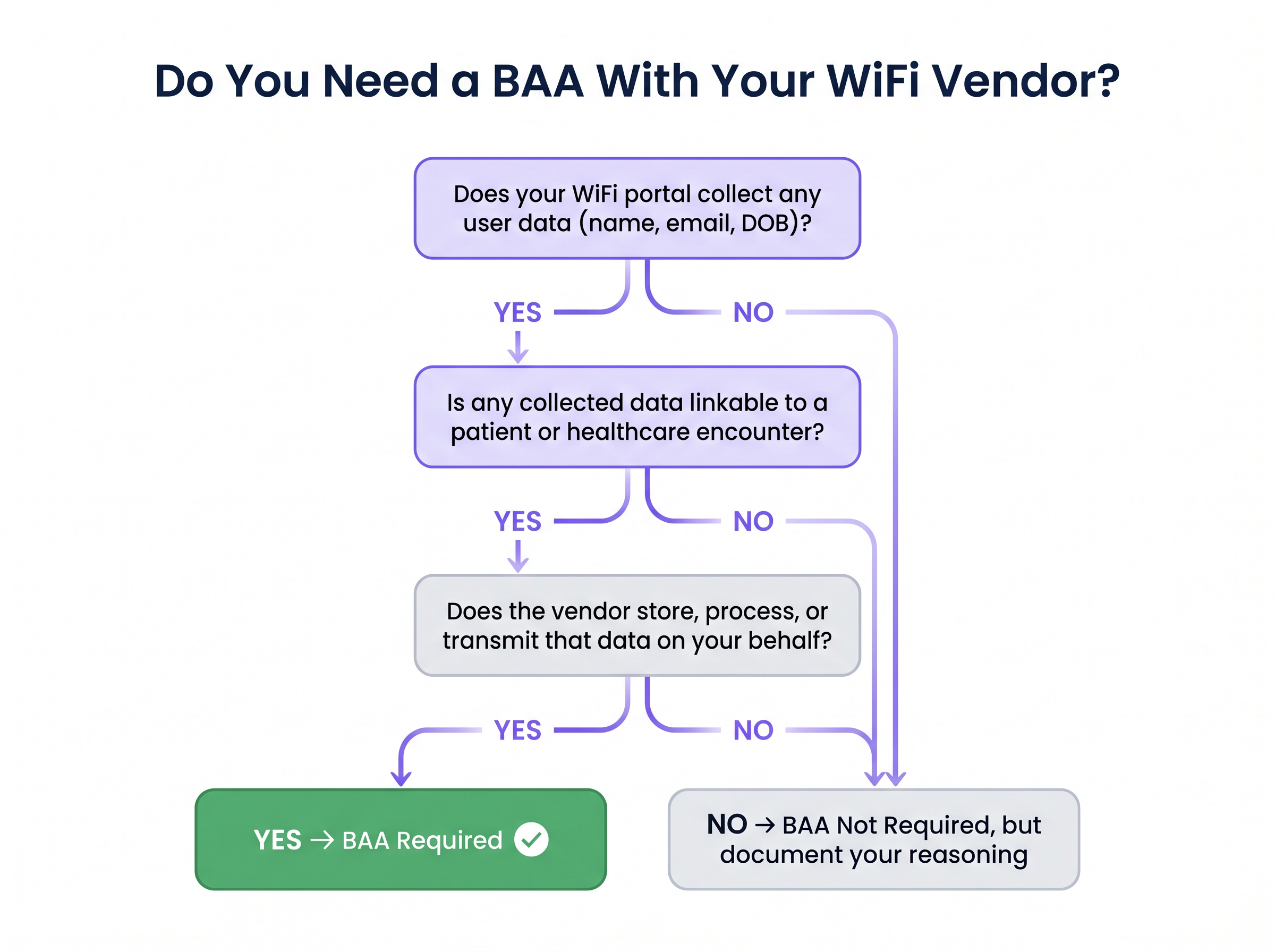
Si la plataforma de su proveedor almacena registros de conexión que contienen información identificable del paciente en su infraestructura en la nube, un BAA es obligatorio. Por el contrario, si la plataforma recopila solo datos anonimizados y no vinculables —como recuentos agregados de afluencia o duraciones de sesión sin identidad— un BAA podría no ser estrictamente necesario. Sin embargo, debe documentar esta decisión en su registro de riesgos para demostrar una gestión de cumplimiento deliberada a los auditores.
Mejores Prácticas
Adherirse a las mejores prácticas estándar de la industria garantiza el cumplimiento continuo y la integridad de la red.
- Aplicar Separación Estricta de VLAN: Verifique la separación de VLAN a nivel de hardware, no solo en el controlador. Los puntos de acceso compartidos deben configurarse correctamente con etiquetado de VLAN y reglas de firewall para evitar el salto de VLAN.
- Implementar Registro Exhaustivo: Si bien una red de invitados pura puede no caer directamente bajo los requisitos de registro de HIPAA, mantenerLos registros son esenciales para probar el aislamiento durante una auditoría. Capture las marcas de tiempo de conexión, las direcciones MAC, las asignaciones DHCP y los eventos de denegación del firewall en el límite. Conserve estos registros por un mínimo de seis años.
- Revisiones Regulares de Cumplimiento: Incluya la configuración de la plataforma WiFi en su evaluación anual de riesgos HIPAA. Revise las notas de la versión del proveedor para detectar cualquier cambio en las prácticas de manejo de datos que pueda introducir nuevos requisitos de cumplimiento.
- Centralice la Gestión de Red: Para implementaciones multisitio, utilice una plataforma WiFi gestionada en la nube con configuración VLAN por sitio que termine en un controlador compartido, asegurando una aplicación de políticas consistente en todas las ubicaciones. Este enfoque comparte similitudes arquitectónicas con las implementaciones WAN modernas, como se detalla en Los beneficios clave de SD WAN para empresas modernas .
Solución de Problemas y Mitigación de Riesgos
Los equipos de TI de atención médica deben estar atentos a los modos de falla comunes que comprometen la segmentación y el cumplimiento.
Mala Configuración de Puntos de Acceso Compartidos
En instalaciones antiguas, los puntos de acceso a menudo sirven múltiples SSIDs en el mismo hardware. La falta de configuración adecuada del etiquetado VLAN y las reglas del firewall puede permitir que el tráfico de invitados llegue a la VLAN clínica. Mitigación: Realice auditorías exhaustivas de todos los puntos de acceso para verificar la separación VLAN a nivel de hardware.
Redes 'Temporales' Maliciosas
El personal de las instalaciones a veces implementa routers de grado de consumidor para el WiFi de la sala de espera, conectándolos directamente al switch de red principal. Esto crea una brecha de cumplimiento inmediata y sin monitoreo. Mitigación: Aplique un proceso estricto de gestión de cambios que requiera la revisión de TI para cualquier nueva implementación de dispositivo de red.
Aumento Gradual de la Retención de Datos del Proveedor
Una plataforma de análisis WiFi configurada inicialmente para una recopilación mínima de datos podría habilitar posteriormente funciones que capturen perfiles de usuario más ricos, alterando su estado de cumplimiento. Mitigación: Establezca una cadencia de revisión regular para los acuerdos de procesamiento de datos del proveedor y monitoree de cerca las actualizaciones de la plataforma.
ROI e Impacto Empresarial
Una red WiFi para invitados correctamente implementada y compatible con HIPAA ofrece un valor empresarial significativo más allá de la conectividad básica. Al proporcionar una experiencia digital fluida, los proveedores de atención médica pueden mejorar las puntuaciones de satisfacción del paciente (HCAHPS) y optimizar la navegación de los visitantes.
Además, los análisis anonimizados recopilados de la red de invitados pueden informar la gestión de las instalaciones, optimizar los niveles de personal según el flujo de visitantes y mejorar la eficiencia operativa general del lugar. Para una comprensión más profunda de cómo cuantificar estos beneficios, consulte nuestro marco sobre Medición del ROI del WiFi para Invitados: Un Marco para CMOs . En última instancia, tratar el WiFi para invitados como un activo de infraestructura estratégico en lugar de una mera comodidad garantiza tanto el cumplimiento normativo como un retorno de la inversión medible.
Términos clave y definiciones
ePHI (Electronic Protected Health Information)
Any protected health information that is produced, saved, transferred, or received in an electronic form.
Understanding what constitutes ePHI is critical, as its presence dictates the applicability of the HIPAA Security Rule to network infrastructure.
Network Segmentation
The practice of dividing a computer network into smaller, distinct sub-networks to improve performance and security.
Essential for isolating guest WiFi traffic from clinical systems that process ePHI.
Business Associate Agreement (BAA)
A written contract between a HIPAA-covered entity and a Business Associate that establishes the permitted and required uses and disclosures of ePHI.
Required when a WiFi vendor's platform collects and stores identifiable data that could be linked to a patient.
Captive Portal
A web page that a user of a public access network is obliged to view and interact with before access is granted.
The primary point of data collection on a guest network, requiring careful configuration to minimise HIPAA exposure.
VLAN Tagging
The process of adding a tag to a network frame to identify the Virtual Local Area Network (VLAN) to which it belongs.
Used to logically separate guest, staff, and clinical traffic on shared network hardware.
WPA3 Personal
The latest Wi-Fi security protocol that provides individualised data encryption even on open networks.
Recommended for guest networks to protect user traffic from eavesdropping, though it does not alone ensure HIPAA compliance.
802.1X Authentication
An IEEE standard for port-based Network Access Control (PNAC) that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
Crucial for securing the clinical network by ensuring only authorised medical devices and staff can connect.
Default-Deny Posture
A firewall security principle where all traffic is blocked by default, and only explicitly permitted traffic is allowed to pass.
The mandatory configuration for firewalls separating the guest network from the clinical network.
Casos de éxito
A 400-bed regional hospital needs to deploy guest WiFi across patient wards, waiting areas, and a café without exposing its clinical network to compliance risks.
The network team configures Cisco Catalyst switches with strict VLAN tagging to create three separate logical networks: guest, staff, and clinical. The guest VLAN is terminated at a dedicated internet breakout with no routing to the internal core. The captive portal is configured to collect only an email address for terms acceptance. The WiFi analytics platform is scoped strictly to aggregate footfall data, ensuring no individual profiles are created. The hospital executes a BAA with the WiFi vendor to cover the email address data. Firewall logs capturing cross-zone deny events are forwarded to the hospital's SIEM and retained for seven years.
A multi-site healthcare group with twelve outpatient clinics wants a unified guest WiFi experience with consistent branding and centralised analytics, but each clinic has different underlying network infrastructure.
The IT director deploys a cloud-managed WiFi platform with per-site VLAN configuration, all terminating to a shared cloud controller. The clinical networks at each site remain entirely on-premises and are never connected to the cloud management plane. Guest data collection on the captive portal is strictly limited to anonymised device identifiers and session metadata. Because no identifiable data is collected, no BAA is required. The compliance team formally documents this decision and the supporting architecture in the organisation's risk register.
Análisis de escenarios
Q1. A hospital's marketing team wants to implement a captive portal on the guest WiFi that requires users to log in using their social media accounts to gather demographic data for targeted campaigns. How should the IT director respond?
💡 Sugerencia:Consider the implications of collecting identifiable data in a healthcare setting and the BAA requirements.
Mostrar enfoque recomendado
The IT director should advise against this approach unless strict compliance measures are met. Collecting identifiable demographic data via social login creates a dataset that could link individuals to a healthcare encounter, potentially generating ePHI. If the marketing team insists on this feature, the hospital must ensure the WiFi vendor signs a Business Associate Agreement (BAA) and that the data is stored securely in compliance with HIPAA regulations. A safer alternative is to use MAC address tracking for anonymised footfall analytics.
Q2. During a network audit, it is discovered that the guest WiFi and the clinical network share the same physical access points, separated only by VLANs configured on the central wireless controller. Is this configuration compliant?
💡 Sugerencia:Think about the points of failure in logical separation and where enforcement must occur.
Mostrar enfoque recomendado
This configuration presents a significant risk. While VLAN separation at the controller is necessary, it is not sufficient. If the physical access points themselves are not properly configured with VLAN tagging and local firewall rules, a misconfiguration or vulnerability in the AP could allow guest traffic to 'hop' onto the clinical VLAN before it even reaches the controller. Compliance requires verifying isolation at the hardware level across all shared infrastructure.
Q3. A clinic decides to offer an open, unencrypted guest WiFi network to ensure maximum compatibility with older visitor devices. They implement a strict firewall blocking all access to the internal clinical network. Are they fully mitigating their security risks?
💡 Sugerencia:Consider the security of the guest traffic itself, even if the clinical network is protected.
Mostrar enfoque recomendado
While the strict firewall protects the clinical network (addressing the primary HIPAA concern regarding ePHI), offering an unencrypted open network exposes guests to eavesdropping and man-in-the-middle attacks. Best practice dictates implementing WPA3 Personal, which provides individualised encryption even on open networks. If WPA3 is not feasible, the clinic should enforce HTTPS for any captive portal interactions to protect user credentials during the onboarding process.
Conclusiones clave
- ✓Guest WiFi does not inherently handle ePHI, but shared infrastructure creates significant HIPAA compliance risks.
- ✓Implement a strict three-zone network architecture: Guest, DMZ (Isolation), and Clinical.
- ✓Enforce a default-deny firewall posture between the guest network and any clinical systems.
- ✓Minimise data collection on captive portals to reduce the risk of creating linkable ePHI datasets.
- ✓Execute a Business Associate Agreement (BAA) if your WiFi vendor stores or processes identifiable patient data.
- ✓Maintain comprehensive logs of boundary traffic (firewall denies, MAC addresses) to prove network isolation during audits.
- ✓Regularly audit access points to ensure VLAN separation is enforced at the hardware level, preventing VLAN hopping.



