HIPAA-Compliant Guest WiFi for Healthcare Providers
This technical reference guide provides actionable compliance strategies for healthcare IT teams deploying guest WiFi. It covers network segmentation, data handling, and BAA requirements to ensure a seamless visitor experience without compromising HIPAA standards.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- The Three-Zone Segmentation Model
- Authentication and Encryption Standards
- Implementation Guide
- Captive Portal Configuration
- Business Associate Agreements (BAA)
- Best Practices
- Troubleshooting & Risk Mitigation
- Shared Access Point Misconfiguration
- Rogue 'Temporary' Networks
- Vendor Data Retention Creep
- ROI & Business Impact
Executive Summary
Healthcare IT directors and network architects face a persistent challenge: delivering robust Guest WiFi for patients and visitors without exposing the organisation to HIPAA compliance risks. While a pure guest network does not inherently process electronic protected health information (ePHI), the convergence of guest and clinical infrastructure often creates unintended vulnerabilities. This guide provides a practical, vendor-neutral framework for deploying HIPAA-compliant guest WiFi. It covers the essential three-zone segmentation model, data minimisation strategies for captive portals, and the precise conditions under which a Business Associate Agreement (BAA) is required with your WiFi vendor. By treating guest WiFi as an infrastructure project with a compliance component, organisations can confidently enhance patient experience across hospitals, outpatient clinics, and related Healthcare facilities.
Technical Deep-Dive
The foundation of HIPAA-compliant guest WiFi lies in rigorous network architecture. The Security Rule mandates the protection of ePHI against unauthorised access, which translates technically to strict isolation between untrusted guest devices and critical clinical systems.
The Three-Zone Segmentation Model
To achieve compliance, healthcare networks must implement a three-zone segmentation strategy. This architecture prevents lateral movement from the guest environment into areas where ePHI resides.
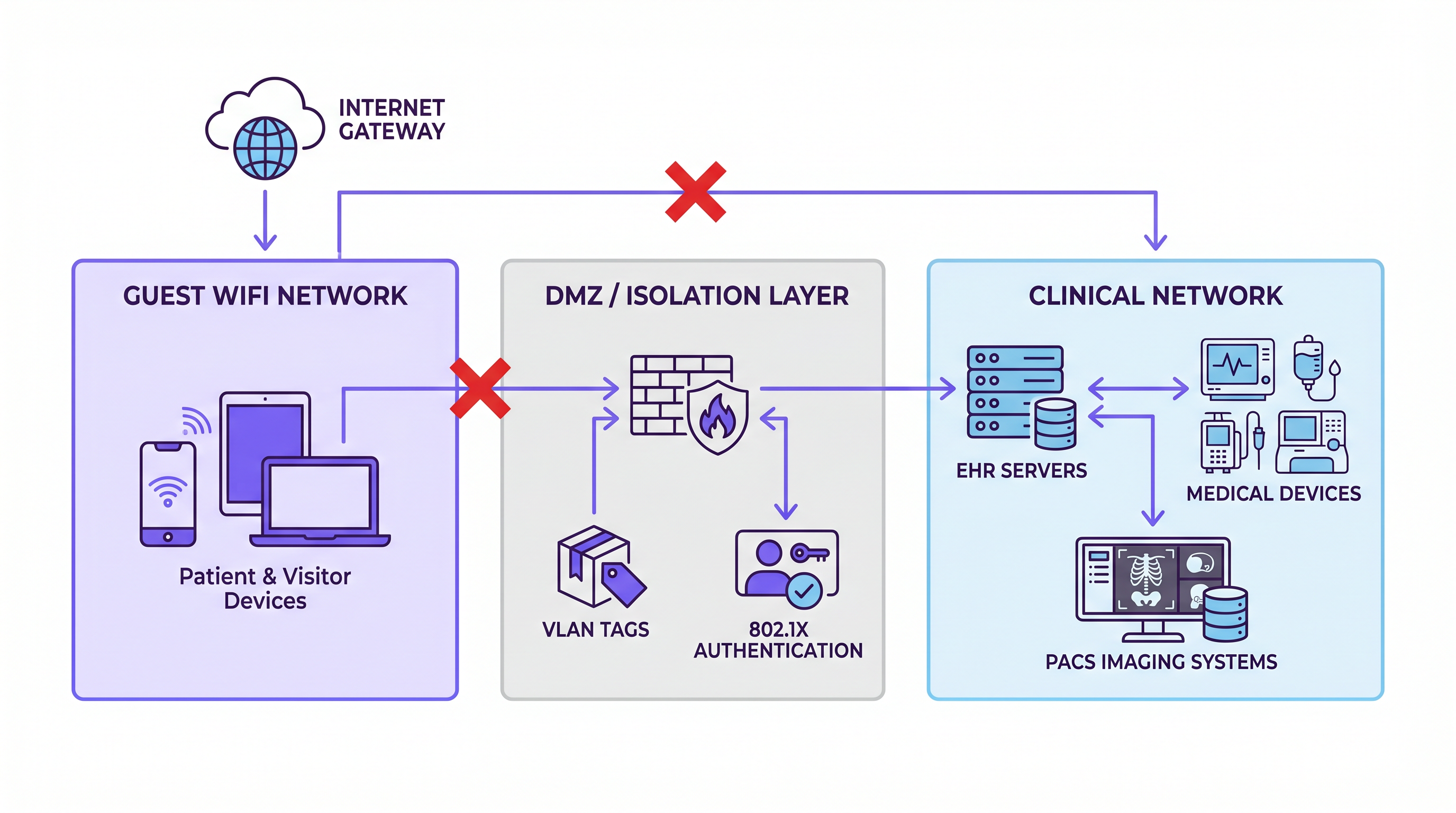
Zone 1: Guest Network This zone serves patient and visitor devices. It provides internet access exclusively. There must be no routing to internal systems and no access to clinical VLANs. Traffic from this zone must egress directly through the internet gateway.
Zone 2: DMZ / Isolation Layer The isolation layer hosts the captive portal, authentication systems, and any data collection infrastructure. If you deploy a WiFi Analytics platform to capture connection data or dwell time, it resides here. This zone is logically separated from both the guest and clinical networks, acting as a controlled intermediary.
Zone 3: Clinical Network This zone contains EHR servers, medical devices, PACS imaging systems, and clinical communication platforms. It must be completely air-gapped from Zones 1 and 2 at the network level. Firewall rules must enforce a default-deny posture, ensuring that any cross-zone traffic travels through explicit, audited pathways.
Authentication and Encryption Standards
While WPA3 Personal is the preferred standard for guest networks—providing individualised data encryption even on open networks to protect against eavesdropping—it does not inherently guarantee HIPAA compliance. Compliance is achieved through the overall architecture. For the clinical network, IEEE 802.1X port-based authentication is essential to ensure only authorised devices can connect, preventing rogue devices from bridging the gap between guest and clinical environments.
Implementation Guide
Deploying a compliant guest WiFi solution requires careful configuration and a data minimisation approach.
Captive Portal Configuration
The captive portal is a common source of inadvertent HIPAA exposure. If the portal requires users to submit identifiable information (such as name, email address, or date of birth) and those users are patients, the resulting dataset could be linked to a healthcare encounter, thereby creating ePHI.
To mitigate this risk, implement a minimal data collection strategy. Capture only the MAC address and connection timestamp. If richer data collection is necessary for marketing or operational analytics, ensure the data is genuinely anonymised and cannot be linked to a specific patient record. When evaluating global privacy frameworks, consider how these practices align with broader regulations, as discussed in our guide on CCPA vs GDPR: Global Privacy Compliance for Guest WiFi Data .
Business Associate Agreements (BAA)
Determining whether you need a BAA with your WiFi vendor is a critical compliance step. A vendor becomes a Business Associate if they create, receive, maintain, or transmit ePHI on your behalf.
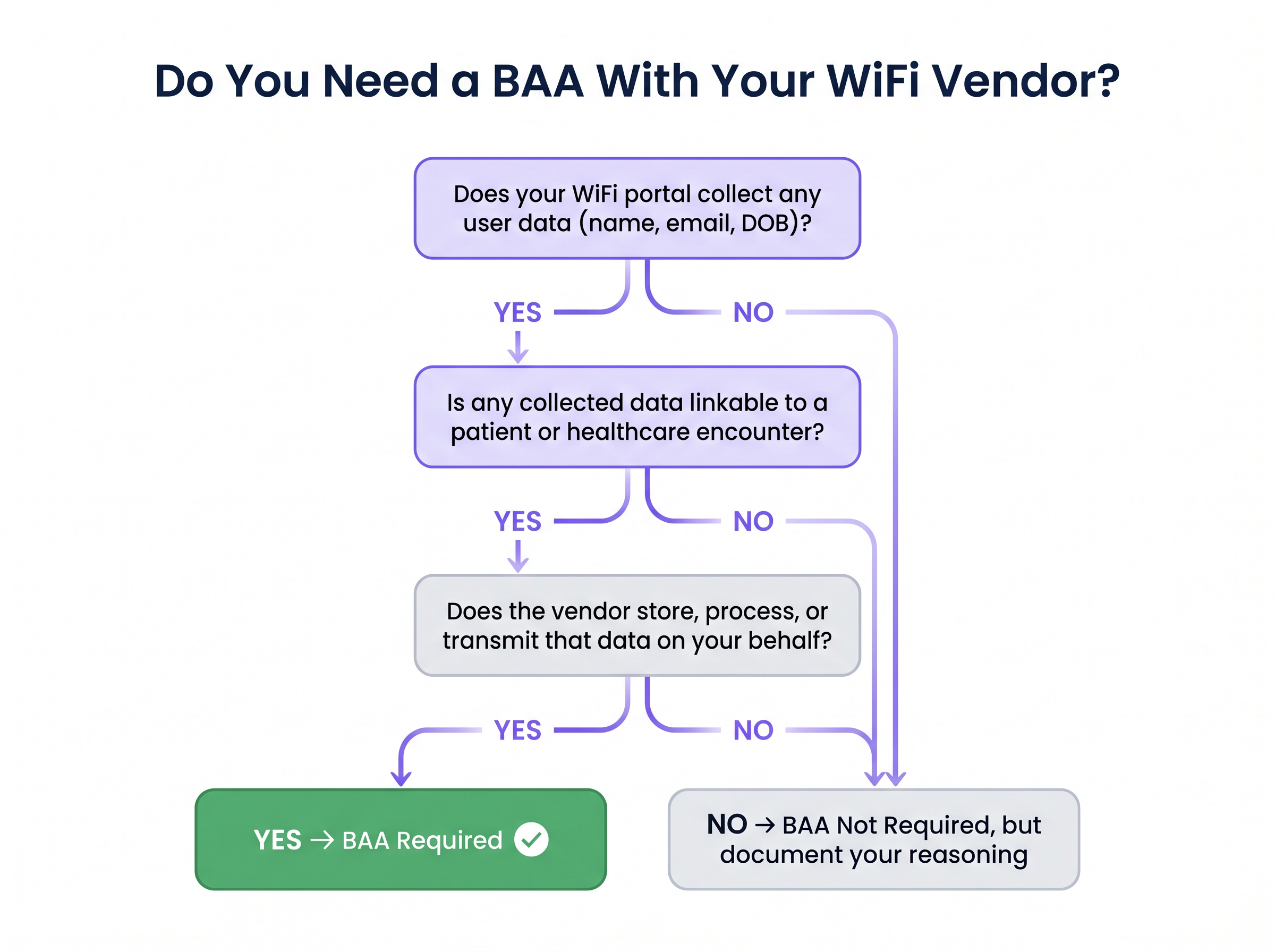
If your vendor's platform stores connection logs containing identifiable patient information on their cloud infrastructure, a BAA is mandatory. Conversely, if the platform collects only anonymised, non-linkable data—such as aggregate footfall counts or session durations without identity—a BAA may not be strictly required. However, you must document this decision in your risk register to demonstrate deliberate compliance management to auditors.
Best Practices
Adhering to industry-standard best practices ensures ongoing compliance and network integrity.
- Enforce Strict VLAN Separation: Verify VLAN separation at the hardware level, not just at the controller. Shared access points must be correctly configured with VLAN tagging and firewall rules to prevent VLAN hopping.
- Implement Comprehensive Logging: While a pure guest network may not directly fall under HIPAA logging requirements, maintaining logs is essential for proving isolation during an audit. Capture connection timestamps, MAC addresses, DHCP assignments, and firewall deny events at the boundary. Retain these logs for a minimum of six years.
- Regular Compliance Reviews: Include the WiFi platform configuration in your annual HIPAA risk assessment. Review vendor release notes for any changes to data handling practices that might introduce new compliance requirements.
- Centralise Network Management: For multi-site deployments, utilise a cloud-managed WiFi platform with per-site VLAN configuration terminating at a shared controller, ensuring consistent policy enforcement across all locations. This approach shares architectural similarities with modern WAN deployments, as detailed in The Core SD WAN Benefits for Modern Businesses .
Troubleshooting & Risk Mitigation
Healthcare IT teams must be vigilant against common failure modes that compromise segmentation and compliance.
Shared Access Point Misconfiguration
In older facilities, access points often serve multiple SSIDs on the same hardware. Failure to properly configure VLAN tagging and firewall rules can allow guest traffic to reach the clinical VLAN. Mitigation: Conduct comprehensive audits of all access points to verify hardware-level VLAN separation.
Rogue 'Temporary' Networks
Facilities personnel sometimes deploy consumer-grade routers for waiting room WiFi, connecting them directly to the main network switch. This creates an immediate, unmonitored compliance gap. Mitigation: Enforce a strict change management process requiring IT review for any new network device deployment.
Vendor Data Retention Creep
A WiFi analytics platform initially configured for minimal data collection might later enable features that capture richer user profiles, altering its compliance status. Mitigation: Establish a regular review cadence for vendor data processing agreements and monitor platform updates closely.
ROI & Business Impact
A properly implemented, HIPAA-compliant guest WiFi network delivers significant business value beyond basic connectivity. By providing a seamless digital experience, healthcare providers can improve patient satisfaction scores (HCAHPS) and streamline visitor navigation.
Furthermore, anonymised analytics gathered from the guest network can inform facility management, optimise staffing levels based on footfall, and improve the overall operational efficiency of the venue. For a deeper understanding of how to quantify these benefits, refer to our framework on Measuring ROI on Guest WiFi: A Framework for CMOs . Ultimately, treating guest WiFi as a strategic infrastructure asset rather than a mere amenity ensures both regulatory compliance and a measurable return on investment.
Key Terms & Definitions
ePHI (Electronic Protected Health Information)
Any protected health information that is produced, saved, transferred, or received in an electronic form.
Understanding what constitutes ePHI is critical, as its presence dictates the applicability of the HIPAA Security Rule to network infrastructure.
Network Segmentation
The practice of dividing a computer network into smaller, distinct sub-networks to improve performance and security.
Essential for isolating guest WiFi traffic from clinical systems that process ePHI.
Business Associate Agreement (BAA)
A written contract between a HIPAA-covered entity and a Business Associate that establishes the permitted and required uses and disclosures of ePHI.
Required when a WiFi vendor's platform collects and stores identifiable data that could be linked to a patient.
Captive Portal
A web page that a user of a public access network is obliged to view and interact with before access is granted.
The primary point of data collection on a guest network, requiring careful configuration to minimise HIPAA exposure.
VLAN Tagging
The process of adding a tag to a network frame to identify the Virtual Local Area Network (VLAN) to which it belongs.
Used to logically separate guest, staff, and clinical traffic on shared network hardware.
WPA3 Personal
The latest Wi-Fi security protocol that provides individualised data encryption even on open networks.
Recommended for guest networks to protect user traffic from eavesdropping, though it does not alone ensure HIPAA compliance.
802.1X Authentication
An IEEE standard for port-based Network Access Control (PNAC) that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
Crucial for securing the clinical network by ensuring only authorised medical devices and staff can connect.
Default-Deny Posture
A firewall security principle where all traffic is blocked by default, and only explicitly permitted traffic is allowed to pass.
The mandatory configuration for firewalls separating the guest network from the clinical network.
Case Studies
A 400-bed regional hospital needs to deploy guest WiFi across patient wards, waiting areas, and a café without exposing its clinical network to compliance risks.
The network team configures Cisco Catalyst switches with strict VLAN tagging to create three separate logical networks: guest, staff, and clinical. The guest VLAN is terminated at a dedicated internet breakout with no routing to the internal core. The captive portal is configured to collect only an email address for terms acceptance. The WiFi analytics platform is scoped strictly to aggregate footfall data, ensuring no individual profiles are created. The hospital executes a BAA with the WiFi vendor to cover the email address data. Firewall logs capturing cross-zone deny events are forwarded to the hospital's SIEM and retained for seven years.
A multi-site healthcare group with twelve outpatient clinics wants a unified guest WiFi experience with consistent branding and centralised analytics, but each clinic has different underlying network infrastructure.
The IT director deploys a cloud-managed WiFi platform with per-site VLAN configuration, all terminating to a shared cloud controller. The clinical networks at each site remain entirely on-premises and are never connected to the cloud management plane. Guest data collection on the captive portal is strictly limited to anonymised device identifiers and session metadata. Because no identifiable data is collected, no BAA is required. The compliance team formally documents this decision and the supporting architecture in the organisation's risk register.
Scenario Analysis
Q1. A hospital's marketing team wants to implement a captive portal on the guest WiFi that requires users to log in using their social media accounts to gather demographic data for targeted campaigns. How should the IT director respond?
💡 Hint:Consider the implications of collecting identifiable data in a healthcare setting and the BAA requirements.
Show Recommended Approach
The IT director should advise against this approach unless strict compliance measures are met. Collecting identifiable demographic data via social login creates a dataset that could link individuals to a healthcare encounter, potentially generating ePHI. If the marketing team insists on this feature, the hospital must ensure the WiFi vendor signs a Business Associate Agreement (BAA) and that the data is stored securely in compliance with HIPAA regulations. A safer alternative is to use MAC address tracking for anonymised footfall analytics.
Q2. During a network audit, it is discovered that the guest WiFi and the clinical network share the same physical access points, separated only by VLANs configured on the central wireless controller. Is this configuration compliant?
💡 Hint:Think about the points of failure in logical separation and where enforcement must occur.
Show Recommended Approach
This configuration presents a significant risk. While VLAN separation at the controller is necessary, it is not sufficient. If the physical access points themselves are not properly configured with VLAN tagging and local firewall rules, a misconfiguration or vulnerability in the AP could allow guest traffic to 'hop' onto the clinical VLAN before it even reaches the controller. Compliance requires verifying isolation at the hardware level across all shared infrastructure.
Q3. A clinic decides to offer an open, unencrypted guest WiFi network to ensure maximum compatibility with older visitor devices. They implement a strict firewall blocking all access to the internal clinical network. Are they fully mitigating their security risks?
💡 Hint:Consider the security of the guest traffic itself, even if the clinical network is protected.
Show Recommended Approach
While the strict firewall protects the clinical network (addressing the primary HIPAA concern regarding ePHI), offering an unencrypted open network exposes guests to eavesdropping and man-in-the-middle attacks. Best practice dictates implementing WPA3 Personal, which provides individualised encryption even on open networks. If WPA3 is not feasible, the clinic should enforce HTTPS for any captive portal interactions to protect user credentials during the onboarding process.
Key Takeaways
- ✓Guest WiFi does not inherently handle ePHI, but shared infrastructure creates significant HIPAA compliance risks.
- ✓Implement a strict three-zone network architecture: Guest, DMZ (Isolation), and Clinical.
- ✓Enforce a default-deny firewall posture between the guest network and any clinical systems.
- ✓Minimise data collection on captive portals to reduce the risk of creating linkable ePHI datasets.
- ✓Execute a Business Associate Agreement (BAA) if your WiFi vendor stores or processes identifiable patient data.
- ✓Maintain comprehensive logs of boundary traffic (firewall denies, MAC addresses) to prove network isolation during audits.
- ✓Regularly audit access points to ensure VLAN separation is enforced at the hardware level, preventing VLAN hopping.



