HIPAA-konformes Gast-WiFi für Gesundheitsdienstleister
Dieser technische Leitfaden bietet umsetzbare Compliance-Strategien für IT-Teams im Gesundheitswesen, die Gast-WiFi bereitstellen. Er behandelt Netzwerksegmentierung, Datenverarbeitung und BAA-Anforderungen, um ein nahtloses Besuchererlebnis zu gewährleisten, ohne die HIPAA-Standards zu gefährden.
🎧 Diesen Leitfaden anhören
Transkript anzeigen
- Zusammenfassung
- Technischer Einblick
- Das Drei-Zonen-Segmentierungsmodell
- Authentifizierungs- und Verschlüsselungsstandards
- Implementierungsleitfaden
- Captive Portal Konfiguration
- Business Associate Agreements (BAA)
- Best Practices
- Fehlerbehebung & Risikominderung
- Fehlkonfiguration von gemeinsam genutzten Access Points
- Illegale 'temporäre' Netzwerke
- Ausweitung der Datenaufbewahrung durch Anbieter
- ROI & Geschäftsauswirkungen
Zusammenfassung
IT-Leiter und Netzwerkarchitekten im Gesundheitswesen stehen vor einer anhaltenden Herausforderung: ein robustes Gast-WiFi für Patienten und Besucher bereitzustellen, ohne die Organisation HIPAA-Compliance-Risiken auszusetzen. Obwohl ein reines Gastnetzwerk nicht von Natur aus elektronisch geschützte Gesundheitsinformationen (ePHI) verarbeitet, führt die Konvergenz von Gast- und klinischer Infrastruktur oft zu unbeabsichtigten Schwachstellen. Dieser Leitfaden bietet einen praktischen, herstellerneutralen Rahmen für die Bereitstellung von HIPAA-konformem Gast-WiFi. Er behandelt das wesentliche Drei-Zonen-Segmentierungsmodell, Strategien zur Datenminimierung für Captive Portals und die genauen Bedingungen, unter denen ein Business Associate Agreement (BAA) mit Ihrem WiFi-Anbieter erforderlich ist. Indem Gast-WiFi als Infrastrukturprojekt mit einer Compliance-Komponente behandelt wird, können Organisationen das Patientenerlebnis in Krankenhäusern, Ambulanzen und verwandten Gesundheitseinrichtungen zuversichtlich verbessern.
Technischer Einblick
Die Grundlage für HIPAA-konformes Gast-WiFi liegt in einer rigorosen Netzwerkarchitektur. Die Sicherheitsregel schreibt den Schutz von ePHI vor unbefugtem Zugriff vor, was technisch eine strikte Isolation zwischen nicht vertrauenswürdigen Gastgeräten und kritischen klinischen Systemen bedeutet.
Das Drei-Zonen-Segmentierungsmodell
Um Compliance zu erreichen, müssen Gesundheitsnetzwerke eine Drei-Zonen-Segmentierungsstrategie implementieren. Diese Architektur verhindert laterale Bewegungen aus der Gastumgebung in Bereiche, in denen sich ePHI befindet.
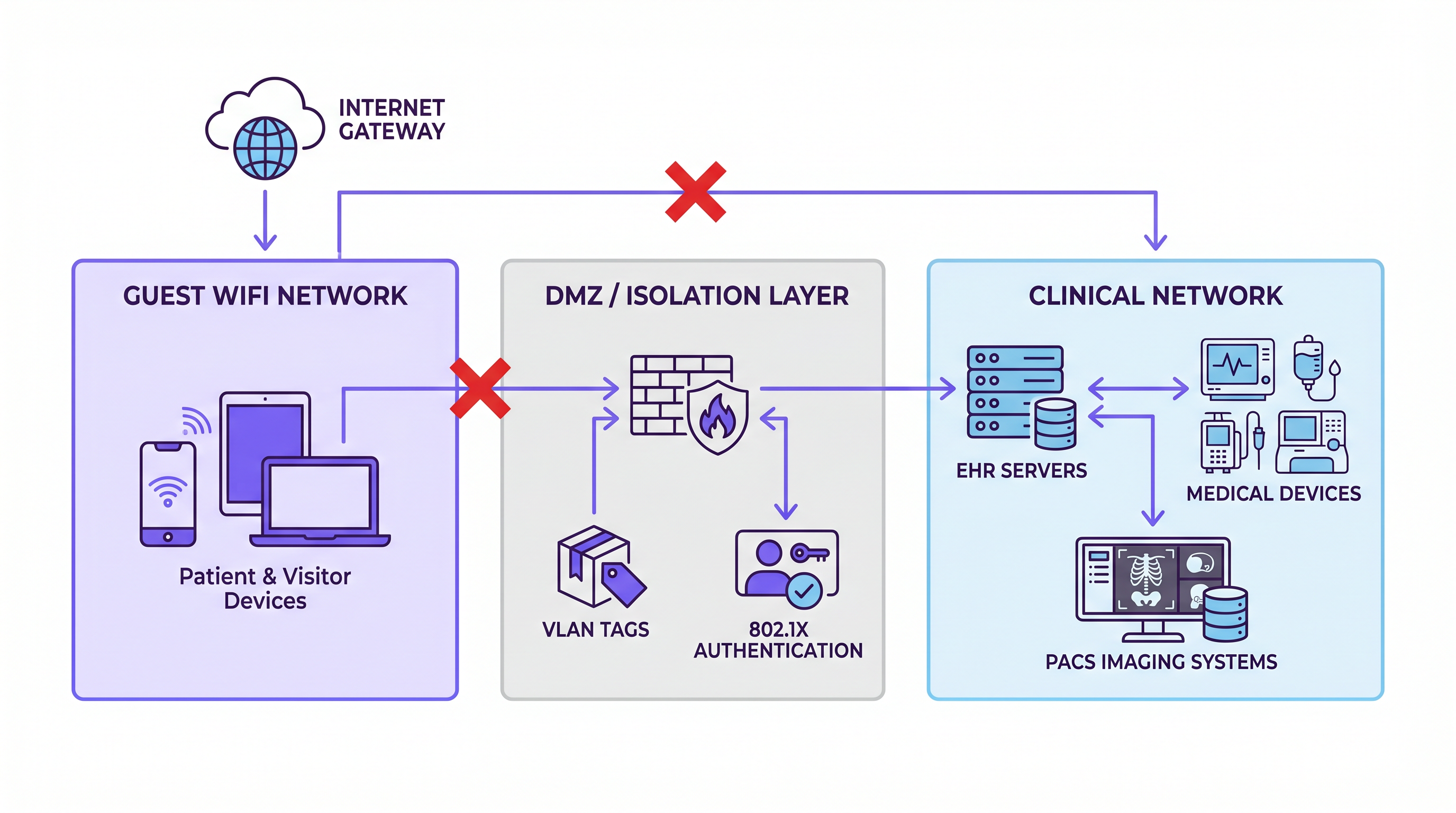
Zone 1: Gastnetzwerk Diese Zone dient Patienten- und Besuchergeräten. Sie bietet ausschließlich Internetzugang. Es darf kein Routing zu internen Systemen geben und keinen Zugriff auf klinische VLANs. Der Datenverkehr aus dieser Zone muss direkt über das Internet-Gateway ausgeleitet werden.
Zone 2: DMZ / Isolationsschicht Die Isolationsschicht beherbergt das Captive Portal, Authentifizierungssysteme und jegliche Datenerfassungsinfrastruktur. Wenn Sie eine WiFi Analytics -Plattform bereitstellen, um Verbindungsdaten oder Verweildauer zu erfassen, befindet sie sich hier. Diese Zone ist logisch sowohl vom Gast- als auch vom klinischen Netzwerk getrennt und fungiert als kontrollierter Vermittler.
Zone 3: Klinisches Netzwerk Diese Zone enthält EHR-Server, medizinische Geräte, PACS-Bildgebungssysteme und klinische Kommunikationsplattformen. Sie muss auf Netzwerkebene vollständig von Zone 1 und 2 getrennt sein (Air-Gapped). Firewall-Regeln müssen eine Default-Deny-Haltung durchsetzen, um sicherzustellen, dass jeglicher zonenübergreifender Datenverkehr über explizite, auditierte Pfade verläuft.
Authentifizierungs- und Verschlüsselungsstandards
Obwohl WPA3 Personal der bevorzugte Standard für Gastnetzwerke ist – der eine individualisierte Datenverschlüsselung selbst in offenen Netzwerken bietet, um Abhören zu verhindern – garantiert er nicht von Natur aus die HIPAA-Compliance. Compliance wird durch die Gesamtarchitektur erreicht. Für das klinische Netzwerk ist die IEEE 802.1X portbasierte Authentifizierung unerlässlich, um sicherzustellen, dass nur autorisierte Geräte eine Verbindung herstellen können, und um zu verhindern, dass nicht autorisierte Geräte die Lücke zwischen Gast- und klinischen Umgebungen überbrücken.
Implementierungsleitfaden
Die Bereitstellung einer konformen Gast-WiFi-Lösung erfordert eine sorgfältige Konfiguration und einen Ansatz zur Datenminimierung.
Captive Portal Konfiguration
Das Captive Portal ist eine häufige Quelle für unbeabsichtigte HIPAA-Exposition. Wenn das Portal von Benutzern die Eingabe identifizierbarer Informationen verlangt (wie Name, E-Mail-Adresse oder Geburtsdatum) und diese Benutzer Patienten sind, könnte der resultierende Datensatz mit einem Gesundheitsereignis verknüpft werden, wodurch ePHI entsteht.
Um dieses Risiko zu mindern, implementieren Sie eine Strategie zur minimalen Datenerfassung. Erfassen Sie nur die MAC-Adresse und den Verbindungszeitstempel. Wenn eine umfassendere Datenerfassung für Marketing- oder Betriebsanalysen erforderlich ist, stellen Sie sicher, dass die Daten wirklich anonymisiert sind und nicht mit einem bestimmten Patientenakt verknüpft werden können. Bei der Bewertung globaler Datenschutzrahmen berücksichtigen Sie, wie diese Praktiken mit umfassenderen Vorschriften übereinstimmen, wie in unserem Leitfaden zu CCPA vs GDPR: Global Privacy Compliance for Guest WiFi Data erörtert.
Business Associate Agreements (BAA)
Die Feststellung, ob Sie ein BAA mit Ihrem WiFi-Anbieter benötigen, ist ein entscheidender Compliance-Schritt. Ein Anbieter wird zu einem Business Associate, wenn er ePHI in Ihrem Namen erstellt, empfängt, pflegt oder übermittelt.
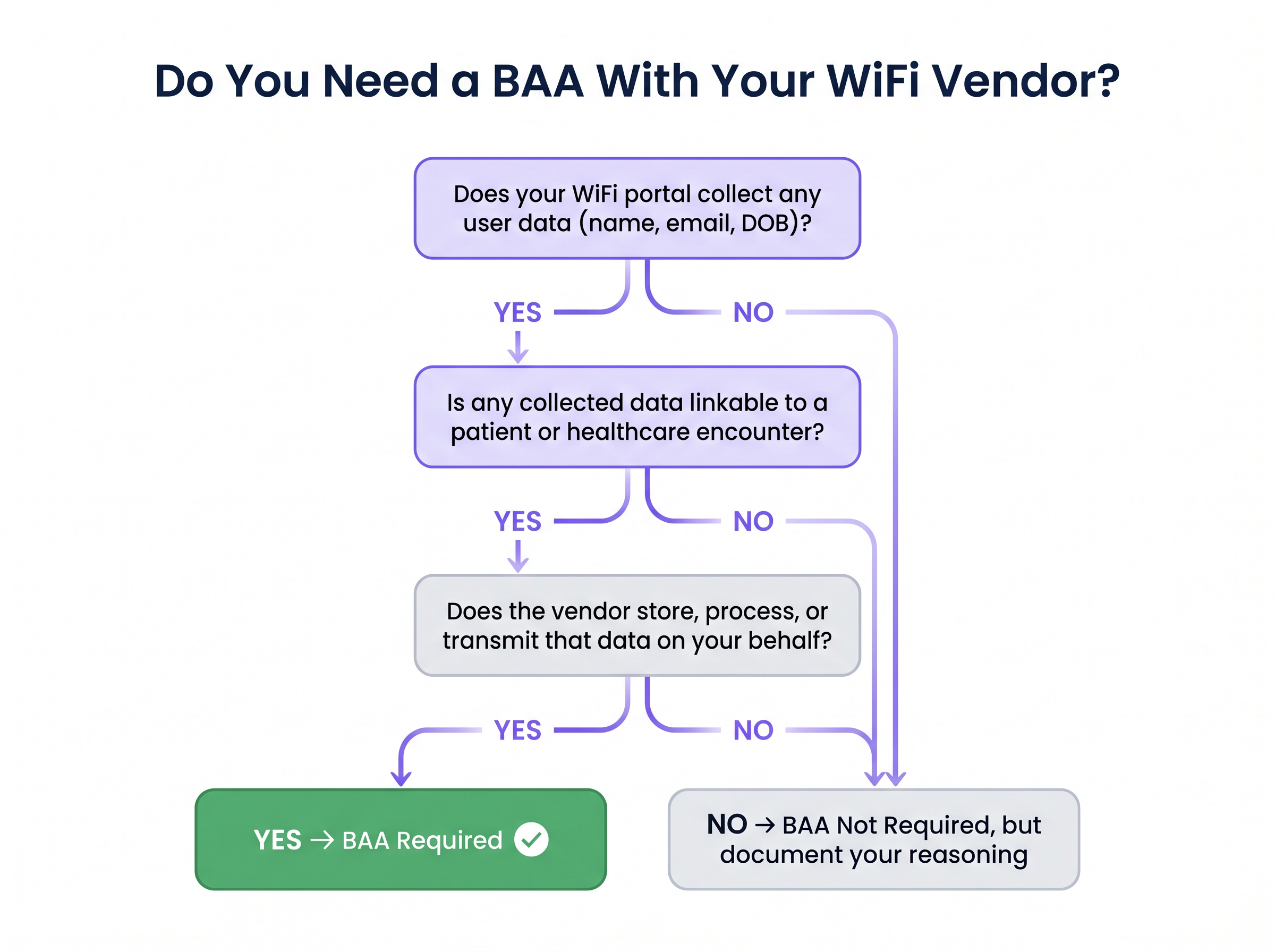
Wenn die Plattform Ihres Anbieters Verbindungslogs speichert, die identifizierbare Patienteninformationen auf ihrer Cloud-Infrastruktur enthalten, ist ein BAA obligatorisch. Umgekehrt, wenn die Plattform nur anonymisierte, nicht verknüpfbare Daten sammelt – wie aggregierte Besucherzahlen oder Sitzungsdauern ohne Identität – ist ein BAA möglicherweise nicht zwingend erforderlich. Sie müssen diese Entscheidung jedoch in Ihrem Risikoregister dokumentieren, um Auditoren ein bewusstes Compliance-Management zu demonstrieren.
Best Practices
Die Einhaltung branchenüblicher Best Practices gewährleistet fortlaufende Compliance und Netzwerkintegrität.
- Strikte VLAN-Trennung durchsetzen: Überprüfen Sie die VLAN-Trennung auf Hardwareebene, nicht nur auf Controllerebene.
- Gemeinsam genutzte Access Points müssen korrekt mit VLAN-Tagging und Firewall-Regeln konfiguriert werden, um VLAN-Hopping zu verhindern.
- Umfassende Protokollierung implementieren: Obwohl ein reines Gastnetzwerk möglicherweise nicht direkt unter die HIPAA-Protokollierungsanforderungen fällt, ist die AufrechterhaltungProtokolle sind unerlässlich, um die Isolation während eines Audits nachzuweisen. Erfassen Sie Verbindungszeitstempel, MAC-Adressen, DHCP-Zuweisungen und Firewall-Verweigerungsereignisse an der Grenze. Bewahren Sie diese Protokolle für mindestens sechs Jahre auf.
- Regelmäßige Compliance-Überprüfungen: Beziehen Sie die WiFi-Plattformkonfiguration in Ihre jährliche HIPAA-Risikobewertung ein. Überprüfen Sie die Versionshinweise des Anbieters auf Änderungen der Datenverarbeitungspraktiken, die neue Compliance-Anforderungen mit sich bringen könnten.
- Zentralisierte Netzwerkverwaltung: Für Multi-Site-Bereitstellungen nutzen Sie eine Cloud-verwaltete WiFi-Plattform mit standortspezifischer VLAN-Konfiguration, die an einem gemeinsamen Controller endet, um eine konsistente Richtliniendurchsetzung an allen Standorten zu gewährleisten. Dieser Ansatz weist architektonische Ähnlichkeiten mit modernen WAN-Bereitstellungen auf, wie in The Core SD WAN Benefits for Modern Businesses detailliert beschrieben.
Fehlerbehebung & Risikominderung
IT-Teams im Gesundheitswesen müssen wachsam sein gegenüber häufigen Fehlermodi, die die Segmentierung und Compliance gefährden.
Fehlkonfiguration von gemeinsam genutzten Access Points
In älteren Einrichtungen dienen Access Points oft mehreren SSIDs auf derselben Hardware. Eine fehlerhafte Konfiguration von VLAN-Tagging und Firewall-Regeln kann dazu führen, dass Gastverkehr das klinische VLAN erreicht. Abhilfe: Führen Sie umfassende Audits aller Access Points durch, um die VLAN-Trennung auf Hardware-Ebene zu überprüfen.
Illegale 'temporäre' Netzwerke
Mitarbeiter von Einrichtungen setzen manchmal Consumer-Router für das Wartezimmer-WiFi ein und verbinden diese direkt mit dem Hauptnetzwerk-Switch. Dies schafft eine sofortige, unüberwachte Compliance-Lücke. Abhilfe: Setzen Sie einen strengen Änderungsmanagementprozess durch, der eine IT-Überprüfung für jede neue Netzwerkgerätebereitstellung erfordert.
Ausweitung der Datenaufbewahrung durch Anbieter
Eine WiFi-Analyseplattform, die ursprünglich für minimale Datenerfassung konfiguriert wurde, könnte später Funktionen aktivieren, die umfassendere Benutzerprofile erfassen und so ihren Compliance-Status ändern. Abhilfe: Etablieren Sie einen regelmäßigen Überprüfungszyklus für Datenverarbeitungsvereinbarungen mit Anbietern und überwachen Sie Plattform-Updates genau.
ROI & Geschäftsauswirkungen
Ein ordnungsgemäß implementiertes, HIPAA-konformes Gast-WiFi-Netzwerk liefert einen erheblichen Geschäftswert über die grundlegende Konnektivität hinaus. Durch die Bereitstellung eines nahtlosen digitalen Erlebnisses können Gesundheitsdienstleister die Patientenzufriedenheitswerte (HCAHPS) verbessern und die Besuchernavigation optimieren.
Darüber hinaus können anonymisierte Analysedaten, die aus dem Gastnetzwerk gesammelt werden, das Facility Management informieren, die Personalbesetzung basierend auf der Besucherfrequenz optimieren und die gesamte betriebliche Effizienz des Veranstaltungsortes verbessern. Für ein tieferes Verständnis, wie diese Vorteile quantifiziert werden können, verweisen wir auf unser Framework Measuring ROI on Guest WiFi: A Framework for CMOs . Letztendlich stellt die Behandlung von Gast-WiFi als strategisches Infrastruktur-Asset und nicht als bloße Annehmlichkeit sowohl die Einhaltung gesetzlicher Vorschriften als auch einen messbaren Return on Investment sicher.
Schlüsselbegriffe & Definitionen
ePHI (Electronic Protected Health Information)
Any protected health information that is produced, saved, transferred, or received in an electronic form.
Understanding what constitutes ePHI is critical, as its presence dictates the applicability of the HIPAA Security Rule to network infrastructure.
Network Segmentation
The practice of dividing a computer network into smaller, distinct sub-networks to improve performance and security.
Essential for isolating guest WiFi traffic from clinical systems that process ePHI.
Business Associate Agreement (BAA)
A written contract between a HIPAA-covered entity and a Business Associate that establishes the permitted and required uses and disclosures of ePHI.
Required when a WiFi vendor's platform collects and stores identifiable data that could be linked to a patient.
Captive Portal
A web page that a user of a public access network is obliged to view and interact with before access is granted.
The primary point of data collection on a guest network, requiring careful configuration to minimise HIPAA exposure.
VLAN Tagging
The process of adding a tag to a network frame to identify the Virtual Local Area Network (VLAN) to which it belongs.
Used to logically separate guest, staff, and clinical traffic on shared network hardware.
WPA3 Personal
The latest Wi-Fi security protocol that provides individualised data encryption even on open networks.
Recommended for guest networks to protect user traffic from eavesdropping, though it does not alone ensure HIPAA compliance.
802.1X Authentication
An IEEE standard for port-based Network Access Control (PNAC) that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
Crucial for securing the clinical network by ensuring only authorised medical devices and staff can connect.
Default-Deny Posture
A firewall security principle where all traffic is blocked by default, and only explicitly permitted traffic is allowed to pass.
The mandatory configuration for firewalls separating the guest network from the clinical network.
Fallstudien
A 400-bed regional hospital needs to deploy guest WiFi across patient wards, waiting areas, and a café without exposing its clinical network to compliance risks.
The network team configures Cisco Catalyst switches with strict VLAN tagging to create three separate logical networks: guest, staff, and clinical. The guest VLAN is terminated at a dedicated internet breakout with no routing to the internal core. The captive portal is configured to collect only an email address for terms acceptance. The WiFi analytics platform is scoped strictly to aggregate footfall data, ensuring no individual profiles are created. The hospital executes a BAA with the WiFi vendor to cover the email address data. Firewall logs capturing cross-zone deny events are forwarded to the hospital's SIEM and retained for seven years.
A multi-site healthcare group with twelve outpatient clinics wants a unified guest WiFi experience with consistent branding and centralised analytics, but each clinic has different underlying network infrastructure.
The IT director deploys a cloud-managed WiFi platform with per-site VLAN configuration, all terminating to a shared cloud controller. The clinical networks at each site remain entirely on-premises and are never connected to the cloud management plane. Guest data collection on the captive portal is strictly limited to anonymised device identifiers and session metadata. Because no identifiable data is collected, no BAA is required. The compliance team formally documents this decision and the supporting architecture in the organisation's risk register.
Szenarioanalyse
Q1. A hospital's marketing team wants to implement a captive portal on the guest WiFi that requires users to log in using their social media accounts to gather demographic data for targeted campaigns. How should the IT director respond?
💡 Hinweis:Consider the implications of collecting identifiable data in a healthcare setting and the BAA requirements.
Empfohlenen Ansatz anzeigen
The IT director should advise against this approach unless strict compliance measures are met. Collecting identifiable demographic data via social login creates a dataset that could link individuals to a healthcare encounter, potentially generating ePHI. If the marketing team insists on this feature, the hospital must ensure the WiFi vendor signs a Business Associate Agreement (BAA) and that the data is stored securely in compliance with HIPAA regulations. A safer alternative is to use MAC address tracking for anonymised footfall analytics.
Q2. During a network audit, it is discovered that the guest WiFi and the clinical network share the same physical access points, separated only by VLANs configured on the central wireless controller. Is this configuration compliant?
💡 Hinweis:Think about the points of failure in logical separation and where enforcement must occur.
Empfohlenen Ansatz anzeigen
This configuration presents a significant risk. While VLAN separation at the controller is necessary, it is not sufficient. If the physical access points themselves are not properly configured with VLAN tagging and local firewall rules, a misconfiguration or vulnerability in the AP could allow guest traffic to 'hop' onto the clinical VLAN before it even reaches the controller. Compliance requires verifying isolation at the hardware level across all shared infrastructure.
Q3. A clinic decides to offer an open, unencrypted guest WiFi network to ensure maximum compatibility with older visitor devices. They implement a strict firewall blocking all access to the internal clinical network. Are they fully mitigating their security risks?
💡 Hinweis:Consider the security of the guest traffic itself, even if the clinical network is protected.
Empfohlenen Ansatz anzeigen
While the strict firewall protects the clinical network (addressing the primary HIPAA concern regarding ePHI), offering an unencrypted open network exposes guests to eavesdropping and man-in-the-middle attacks. Best practice dictates implementing WPA3 Personal, which provides individualised encryption even on open networks. If WPA3 is not feasible, the clinic should enforce HTTPS for any captive portal interactions to protect user credentials during the onboarding process.
Wichtigste Erkenntnisse
- ✓Guest WiFi does not inherently handle ePHI, but shared infrastructure creates significant HIPAA compliance risks.
- ✓Implement a strict three-zone network architecture: Guest, DMZ (Isolation), and Clinical.
- ✓Enforce a default-deny firewall posture between the guest network and any clinical systems.
- ✓Minimise data collection on captive portals to reduce the risk of creating linkable ePHI datasets.
- ✓Execute a Business Associate Agreement (BAA) if your WiFi vendor stores or processes identifiable patient data.
- ✓Maintain comprehensive logs of boundary traffic (firewall denies, MAC addresses) to prove network isolation during audits.
- ✓Regularly audit access points to ensure VLAN separation is enforced at the hardware level, preventing VLAN hopping.



