¿Cuál es la diferencia entre una red WiFi para invitados y su red principal?
Esta guía de referencia técnica explica las diferencias arquitectónicas entre las redes WiFi para invitados y corporativas, centrándose en la segmentación de VLAN, los modelos de autenticación y las mejores prácticas de seguridad para entornos empresariales.
Escucha esta guía
Ver transcripción del podcast
- Resumen Ejecutivo
- Análisis Técnico Detallado: Arquitectura y Aislamiento
- Mapeo de SSID a VLAN
- Modelos de Autenticación y Cifrado
- Guía de Implementación: Construyendo Acceso Seguro para Invitados
- 1. Aprovisionamiento de Infraestructura
- 2. Aislamiento de Clientes
- 3. Modelado de Tráfico y QoS
- 4. Integración de Captive Portal
- Mejores Prácticas y Cumplimiento
- Solución de problemas y mitigación de riesgos
- ROI e Impacto Empresarial
- Informe de Expertos: Podcast

Resumen Ejecutivo
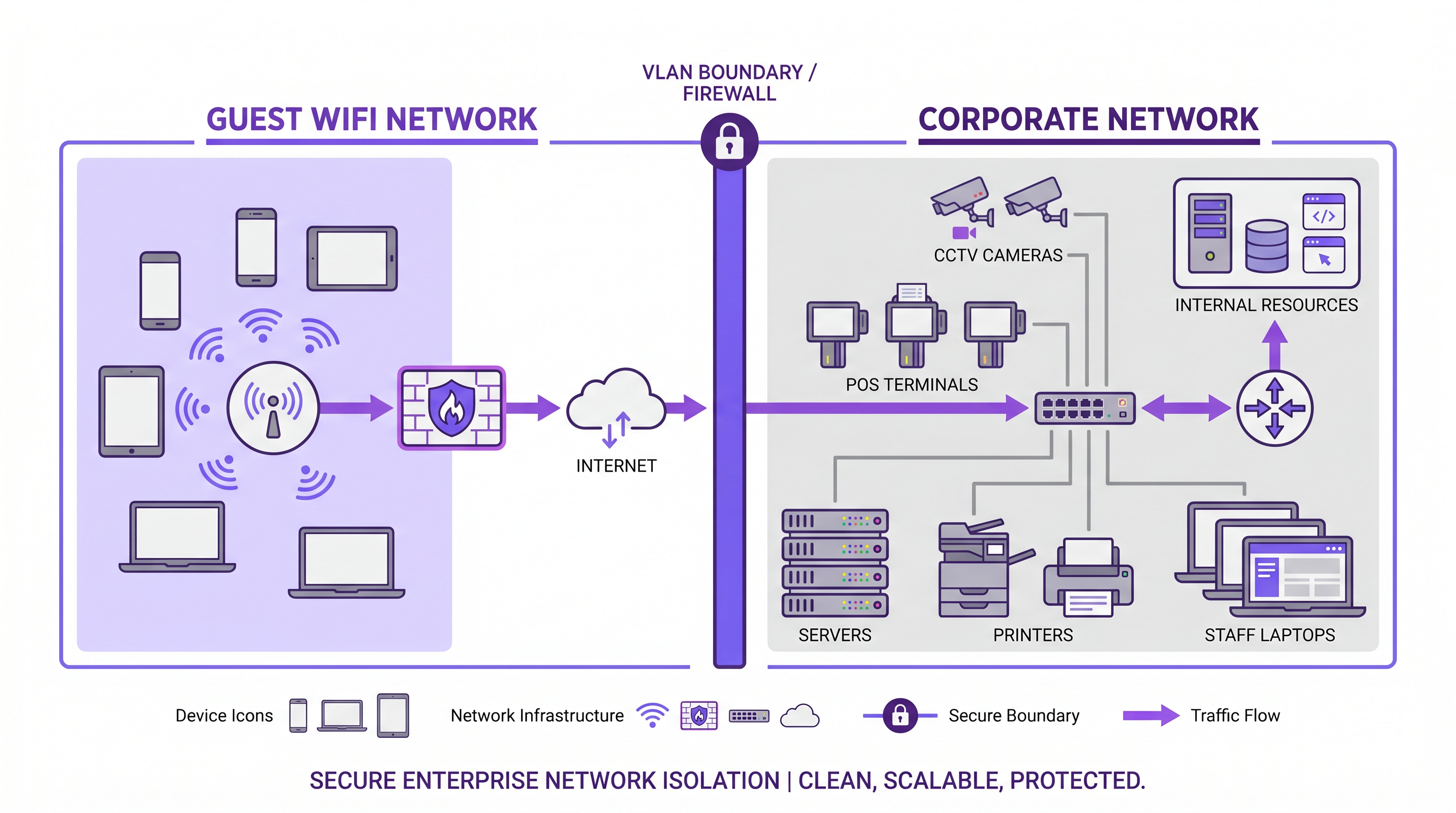
Al diseñar la arquitectura de red para entornos de cara al público, la distinción entre una red WiFi para invitados y una red corporativa principal es fundamentalmente una cuestión de seguridad, cumplimiento e integridad operativa. Una red WiFi para invitados proporciona acceso solo a internet para visitantes, clientes y dispositivos no gestionados, mientras que la red corporativa aloja sistemas críticos para el negocio, terminales de punto de venta y datos propietarios.
Para los gerentes de TI y arquitectos de red, simplemente transmitir un SSID diferente es insuficiente. La verdadera segmentación de red requiere aislamiento a nivel de VLAN, modelos de autenticación distintos y políticas de tráfico separadas. Esta guía explora los requisitos técnicos para establecer un acceso seguro para invitados, la implementación de etiquetado de VLAN y Captive Portals, y el impacto comercial de transformar un costo operativo en un activo de datos de primera parte utilizando plataformas como Guest WiFi y WiFi Analytics .
Análisis Técnico Detallado: Arquitectura y Aislamiento
La diferencia fundamental entre las redes para invitados y corporativas radica en la arquitectura subyacente de Capa 2 y Capa 3. Una implementación robusta de WiFi para invitados en entornos empresariales se basa en una estricta separación lógica para garantizar que el tráfico no autenticado nunca atraviese el mismo dominio de difusión que los datos corporativos.
Mapeo de SSID a VLAN
El mecanismo fundamental para la separación de redes es el mapeo de SSID a VLAN. Los puntos de acceso de grado empresarial están configurados para transmitir múltiples Identificadores de Conjunto de Servicios (SSID). Cada SSID se mapea a una Red de Área Local Virtual (VLAN) distinta.
- VLAN de Invitados: Configurada con una ruta exclusiva a la puerta de enlace de internet. El enrutamiento entre VLAN está explícitamente deshabilitado.
- VLAN Corporativa: Configurada con rutas a recursos internos (controladores de dominio, servidores de archivos, intranet).
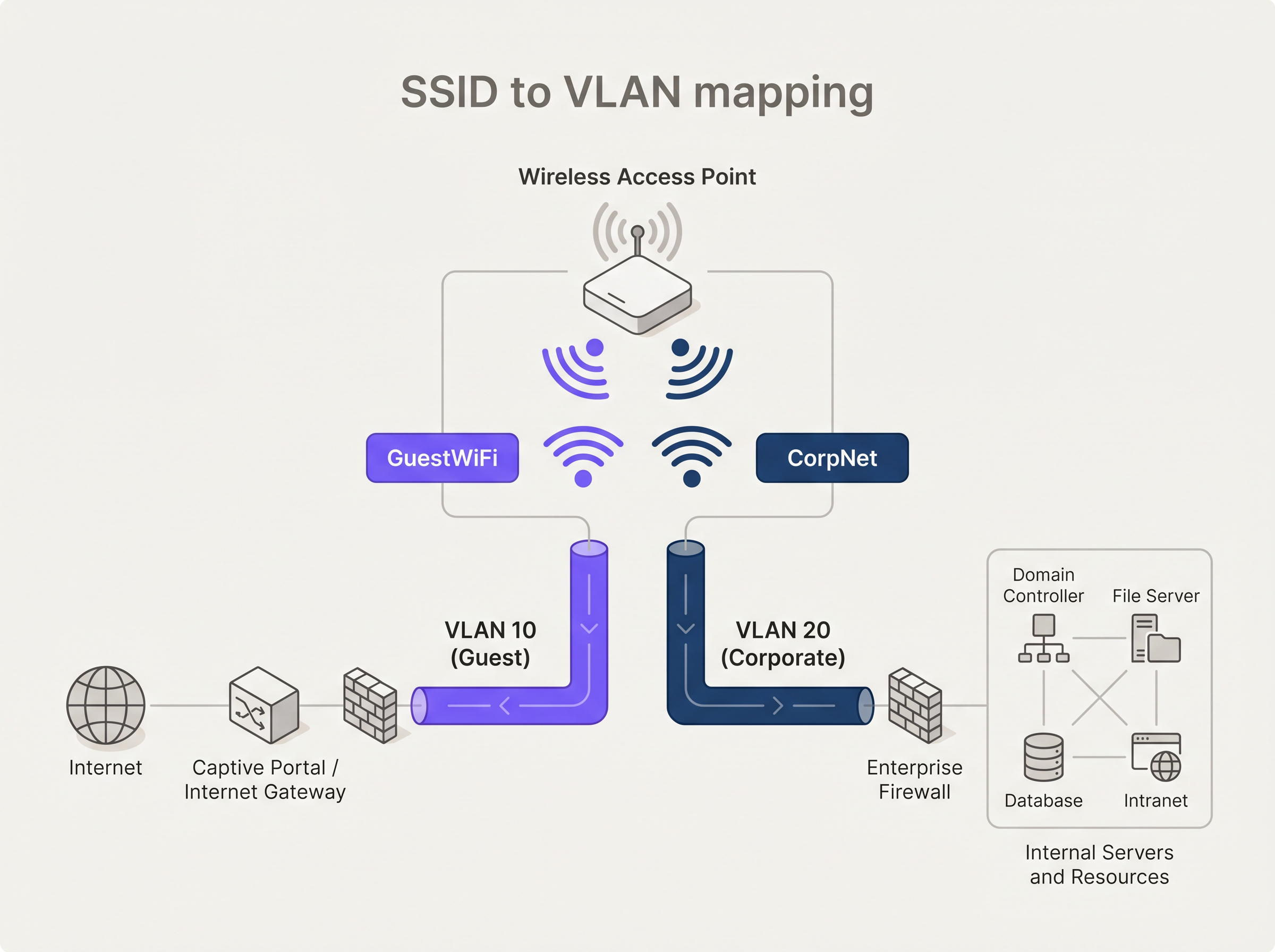
Para mantener esta separación en toda la infraestructura de conmutación, los puntos de acceso deben conectarse a puertos troncales 802.1Q en lugar de puertos de acceso. Esto asegura que las etiquetas de VLAN se conserven a medida que el tráfico se mueve desde el borde a las capas de distribución y núcleo.
Modelos de Autenticación y Cifrado
Los requisitos de autenticación difieren significativamente entre los dos entornos.
Autenticación Corporativa: El estándar empresarial es IEEE 802.1X, típicamente respaldado por un servidor RADIUS. La autenticación basada en certificados (EAP-TLS) se prefiere sobre los métodos basados en credenciales (PEAP-MSCHAPv2) para asegurar que solo los dispositivos gestionados puedan conectarse. Para proteger el propio tráfico de autenticación, las organizaciones deben implementar RadSec: Securing RADIUS Authentication Traffic with TLS .
Autenticación de Invitados: Los dispositivos de invitados no están gestionados. El enfoque estándar es un Captive Portal, una página web que intercepta la solicitud inicial HTTP/HTTPS. Las plataformas modernas aprovechan este punto de intercepción no solo para la aceptación de los términos de servicio, sino también para la autenticación basada en perfiles y la captura de datos compatible con GDPR.
En cuanto al cifrado, WPA3 es el estándar actual. Las redes de invitados deben utilizar WPA3-SAE (Simultaneous Authentication of Equals) para proporcionar secreto hacia adelante, protegiendo el tráfico pasado incluso si la clave precompartida se ve comprometida. Las redes corporativas deben emplear WPA3-Enterprise en modo de 192 bits.
Guía de Implementación: Construyendo Acceso Seguro para Invitados
Desplegar una red inalámbrica segura para invitados requiere una configuración cuidadosa en toda la pila de red.
1. Aprovisionamiento de Infraestructura
Asegúrese de que todos los controladores inalámbricos, puntos de acceso y switches soporten el etiquetado de VLAN 802.1Q. El hardware de consumo no es adecuado para entornos empresariales. Configure ámbitos DHCP dedicados para la VLAN de invitados (por ejemplo, 192.168.100.0/24) y asigne resolvedores DNS públicos (como 8.8.8.8 o 1.1.1.1) para evitar la enumeración de recursos internos basada en DNS.
2. Aislamiento de Clientes
Habilite el aislamiento de clientes inalámbricos (también conocido como aislamiento de AP) en el SSID de invitados. Esto evita que los dispositivos conectados al mismo punto de acceso se comuniquen entre sí, mitigando el riesgo de movimiento lateral o ataques peer-to-peer dentro de la red de invitados.
3. Modelado de Tráfico y QoS
Implemente políticas estrictas de Calidad de Servicio (QoS). Aplique limitación de velocidad a la VLAN de invitados para limitar el ancho de banda por cliente (por ejemplo, 10 Mbps de descarga / 2 Mbps de subida) y asegure que el tráfico corporativo, particularmente VoIP y videoconferencia, reciba cola de prioridad.
4. Integración de Captive Portal
Integre el SSID de invitados con una solución robusta de Captive Portal. Para establecimientos en Retail o Hospitality , el Captive Portal es el principal punto de contacto digital. La plataforma de Purple permite a los establecimientos autenticar usuarios a través de inicio de sesión social o formulario, transformando direcciones MAC anónimas en perfiles de cliente accionables.
Mejores Prácticas y Cumplimiento
Adherirse a los estándares de la industria es innegociable, particularmente en sectores regulados.
- Cumplimiento PCI DSS: Si su establecimiento procesa pagos con tarjeta, el Entorno de Datos del Titular de la Tarjeta (CDE) debe estar estrictamente aislado del tráfico de invitados. Cualquier segmento de red compartido viola los requisitos de PCI DSS.
- GDPR y Privacidad de Datos: Al capturar datos de usuario a través de Captive Portals, deben existir mecanismos de consentimiento explícito. La arquitectura de datos debe soportar el derecho al olvido y la residencia segura de los datos.
- Integración SD-WAN: Para cadenas de retail u hospitality distribuidas, enrutar el tráfico de invitados directamente a internet en el borde de la sucursal (salida local) mientras se transporta el tráfico corporativo a través de túneles seguros es altamente eficiente. Lea más sobre The Core SD WAN Benefits for Modern Businesses .
Solución de problemas y mitigación de riesgos
Los modos de fallo comunes en las implementaciones de WiFi para invitados a menudo provienen de la desviación de la configuración o de hardware inadecuado.
Problema: Invitados accediendo a direcciones IP internas. Causa: Configuración de VLAN incorrecta o enrutamiento inter-VLAN habilitado en el switch/firewall principal. Mitigación: Auditar las Listas de Control de Acceso (ACLs). Implementar una política de denegación por defecto para el tráfico originado en la VLAN de invitados destinado al espacio de IP privadas RFC 1918.
Problema: Degradación de la red corporativa durante las horas pico de visitantes. Causa: Insuficiente limitación de ancho de banda en la red de invitados. Mitigación: Aplicar límites estrictos de velocidad por cliente y límites generales de ancho de banda de la VLAN de invitados en el borde del firewall.
ROI e Impacto Empresarial
Históricamente, el WiFi para invitados se consideraba un costo irrecuperable, una necesidad operativa para centros de Transporte , instalaciones de Salud y entornos minoristas. Al implementar un Captive Portal sofisticado y una capa de análisis, este centro de costos se convierte en un activo generador de ingresos.
El ROI se mide a través de:
- Adquisición de Datos de Primera Parte: Construcción de una base de datos CRM de visitantes verificados.
- Automatización de Marketing: Activación de campañas automatizadas basadas en la frecuencia de visitas y el tiempo de permanencia.
- Monetización de Medios Minoristas: Utilización de la página de bienvenida del Captive Portal como espacio publicitario premium.
Informe de Expertos: Podcast
Escuche a nuestro consultor sénior desglosar las diferencias arquitectónicas y los errores comunes en las implementaciones de WiFi para invitados empresariales.
Definiciones clave
VLAN (Virtual Local Area Network)
A logical grouping of devices on the same physical network infrastructure, functioning as if they were on separate isolated LANs.
Used to separate guest traffic from corporate traffic across the same switches and access points.
SSID (Service Set Identifier)
The public name of a wireless network broadcast by an access point.
The primary identifier users see when connecting; must be mapped to specific VLANs for security.
Captive Portal
A web page that intercepts a user's initial internet request on a public network, requiring action (login, acceptance of terms) before granting access.
The primary authentication and data capture mechanism for enterprise guest WiFi.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The gold standard for securing the corporate main network, ensuring only authorized, managed devices can connect.
Client Isolation (AP Isolation)
A wireless security feature that prevents devices connected to the same AP from communicating directly with each other.
Critical for guest networks to prevent peer-to-peer attacks and lateral movement between untrusted devices.
QoS (Quality of Service)
Technologies that manage data traffic to reduce packet loss, latency, and jitter on the network by prioritizing specific types of data.
Used to ensure business-critical corporate traffic is not degraded by heavy bandwidth usage on the guest network.
WPA3-SAE
Simultaneous Authentication of Equals, the secure key establishment protocol used in WPA3-Personal.
Provides forward secrecy for guest networks, replacing the vulnerable pre-shared key (PSK) method of WPA2.
Inter-VLAN Routing
The process of forwarding network traffic from one VLAN to another using a router or Layer 3 switch.
Must be explicitly disabled or heavily restricted via ACLs between guest and corporate VLANs to maintain isolation.
Ejemplos resueltos
A 200-room hotel needs to deploy WiFi for both guests and administrative staff using the same physical access points. How should the network be architected to ensure PCI DSS compliance for the front desk POS terminals?
Deploy 802.1Q VLAN tagging across all switches and APs. Create VLAN 10 for Guests, VLAN 20 for Admin Staff, and VLAN 30 for POS terminals. The Guest SSID maps to VLAN 10 with client isolation enabled and routes directly to the internet via a captive portal. The Admin SSID maps to VLAN 20 with 802.1X authentication. The POS terminals are hardwired to access ports assigned to VLAN 30. The firewall must have strict ACLs explicitly denying any routing between VLAN 10/20 and VLAN 30.
A large retail chain is experiencing poor performance on their corporate inventory scanners because customers are streaming high-definition video on the free guest WiFi.
Implement QoS policies at the wireless controller and firewall levels. Apply a per-client bandwidth limit (e.g., 5 Mbps) on the Guest SSID. Configure the corporate SSID (used by scanners) with high-priority QoS tags (e.g., WMM Voice/Video categories) and guarantee a minimum bandwidth allocation for the corporate VLAN at the WAN edge.
Preguntas de práctica
Q1. You are deploying a new guest WiFi network for a hospital. The hospital requires guests to accept a Terms of Service policy before accessing the internet. Which authentication mechanism is most appropriate?
Sugerencia: Consider how unmanaged devices interact with public networks versus managed corporate devices.
Ver respuesta modelo
A Captive Portal is the correct mechanism. Unlike 802.1X which requires pre-configured certificates or credentials on managed devices, a captive portal intercepts the initial web request from any unmanaged device and redirects it to a splash page where the Terms of Service can be presented and accepted.
Q2. A network engineer has configured a new 'Guest' SSID with a WPA3 password, but guests are still receiving IP addresses from the internal corporate DHCP server (10.0.0.x). What is the architectural flaw?
Sugerencia: Look at the Layer 2 configuration between the access point and the switch.
Ver respuesta modelo
The SSID has not been mapped to a dedicated VLAN, or the access point is connected to an access port rather than a trunk port. Because VLAN tagging is missing or stripped, the guest traffic is falling into the native corporate VLAN broadcast domain, allowing it to reach the internal DHCP server.
Q3. To save costs, a retail manager suggests plugging a consumer-grade wireless router into the back-office switch to provide guest WiFi. Why is this a critical security risk?
Sugerencia: Consider the capabilities of consumer hardware regarding network segmentation.
Ver respuesta modelo
Consumer-grade routers typically do not support 802.1Q VLAN tagging. Plugging it directly into the back-office switch places guest traffic on the same Layer 2 network as the corporate devices (like POS systems). This eliminates network segmentation, exposing the corporate network to lateral movement and violating PCI DSS compliance.
Continúe leyendo esta serie
Gestión de ancho de banda para WiFi de personal: modelado, QoS y reducción de tráfico
Esta guía detalla métodos prácticos para gestionar el ancho de banda para el WiFi de personal en entornos corporativos. Cubre el modelado de tráfico, la implementación de QoS y cómo el despliegue de Purple Shield reduce la carga de la red sin requerir actualizaciones de infraestructura.
¿Qué es una Solicitud de Sondeo? Entendiendo Cómo los Dispositivos Descubren Redes
Esta guía de referencia técnica ofrece un análisis profundo de las solicitudes de sondeo IEEE 802.11, el escaneo activo versus pasivo, y el impacto de la aleatorización de MAC en el análisis de ubicaciones. Proporciona estrategias de implementación prácticas para que los arquitectos de red optimicen despliegues de alta densidad, mitiguen las tormentas de sondeo y aseguren una recopilación de datos precisa y compatible con GDPR utilizando capas de identidad autenticadas.
Cómo solucionar el WiFi lento sin actualizar tu plan de internet
Una guía de referencia técnica completa para gerentes de TI y arquitectos de red sobre cómo optimizar el rendimiento del WiFi empresarial sin aumentar el ancho de banda del ISP. Cubre la sintonización de RF, la gestión de la densidad de clientes, la implementación de QoS y cómo aprovechar el análisis de WiFi para diagnosticar y resolver cuellos de botella.