Qual é a Diferença Entre uma Rede WiFi de Convidados e a Sua Rede Principal?
Este guia de referência técnica explica as diferenças arquitetónicas entre redes WiFi de convidados e corporativas, focando na segmentação de VLAN, modelos de autenticação e melhores práticas de segurança para ambientes empresariais.
Ouça este guia
Ver transcrição do podcast
- Resumo Executivo
- Análise Técnica Aprofundada: Arquitetura e Isolamento
- Mapeamento de SSID para VLAN
- Modelos de Autenticação e Criptografia
- Guia de Implementação: Construir Acesso Seguro para Convidados
- 1. Provisionamento da Infraestrutura
- 2. Isolamento de Clientes
- 3. Modelagem de Tráfego e QoS
- 4. Integração de Captive Portal
- Melhores Práticas e Conformidade
- Resolução de Problemas e Mitigação de Riscos
- ROI e Impacto no Negócio
- Briefing de Especialistas: Podcast

Resumo Executivo
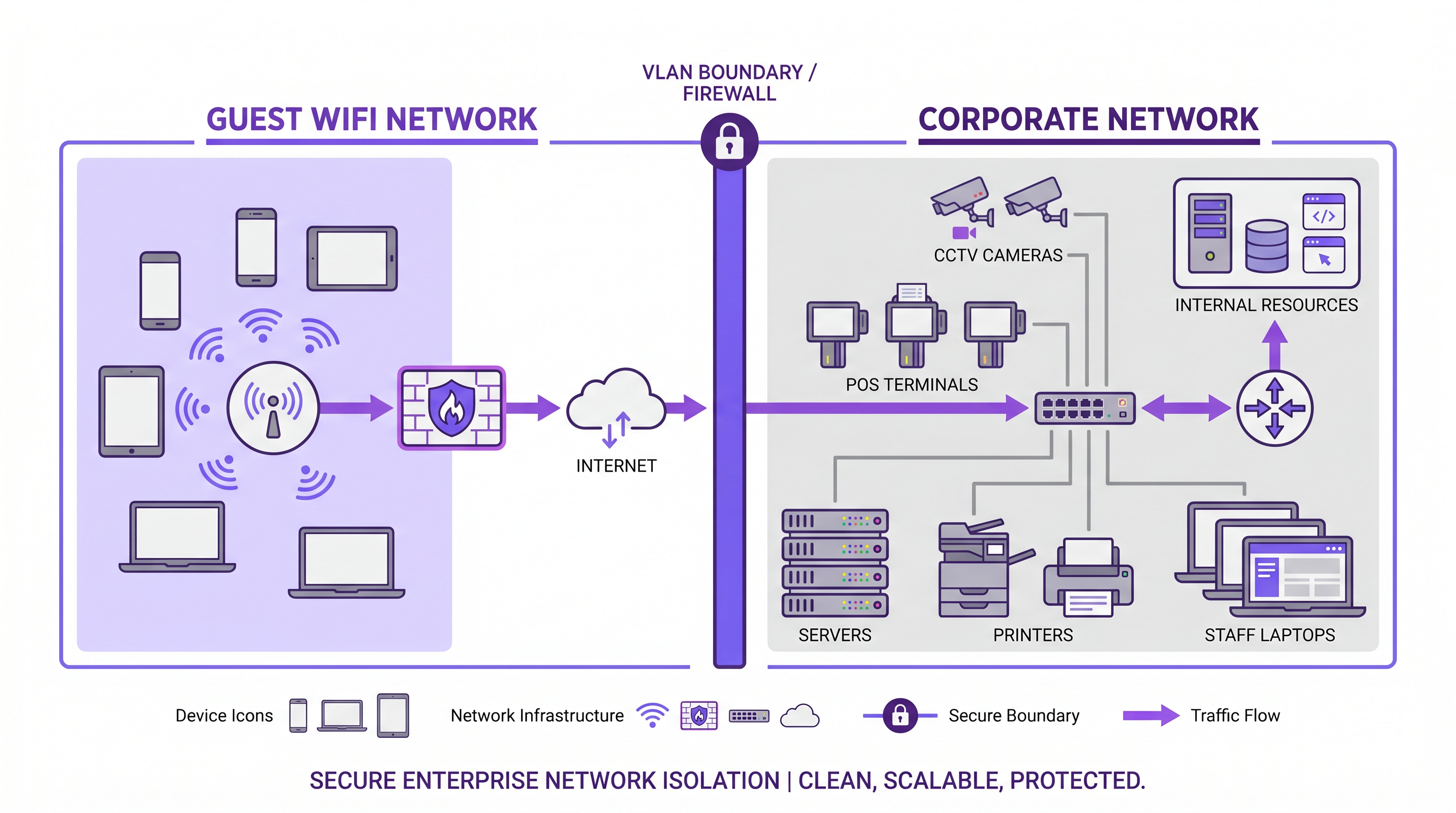
Ao projetar a arquitetura de rede para ambientes de acesso público, a distinção entre uma rede WiFi de convidados e uma rede corporativa principal é fundamentalmente uma questão de segurança, conformidade e integridade operacional. Uma rede WiFi de convidados fornece acesso apenas à internet para visitantes, clientes e dispositivos não geridos, enquanto a rede corporativa aloja sistemas críticos para o negócio, terminais de ponto de venda e dados proprietários.
Para gestores de TI e arquitetos de rede, simplesmente difundir um SSID diferente é insuficiente. A verdadeira segmentação de rede requer isolamento ao nível da VLAN, modelos de autenticação distintos e políticas de tráfego separadas. Este guia explora os requisitos técnicos para estabelecer acesso seguro para convidados, a implementação de VLAN tagging e Captive Portals, e o impacto comercial de transformar um custo operacional num ativo de dados primários usando plataformas como Guest WiFi e WiFi Analytics .
Análise Técnica Aprofundada: Arquitetura e Isolamento
A diferença central entre redes de convidados e corporativas reside na arquitetura subjacente da Camada 2 e Camada 3. Uma implementação robusta de WiFi de convidados empresarial depende de uma separação lógica rigorosa para garantir que o tráfego não autenticado nunca atravessa o mesmo domínio de difusão que os dados corporativos.
Mapeamento de SSID para VLAN
O mecanismo fundamental para a separação de rede é o mapeamento de SSID para VLAN. Os pontos de acesso de nível empresarial são configurados para difundir múltiplos Service Set Identifiers (SSIDs). Cada SSID é mapeado para uma Virtual Local Area Network (VLAN) distinta.
- VLAN de Convidados: Configurada com uma rota exclusivamente para o gateway da internet. O encaminhamento Inter-VLAN é explicitamente desativado.
- VLAN Corporativa: Configurada com rotas para recursos internos (controladores de domínio, servidores de ficheiros, intranet).
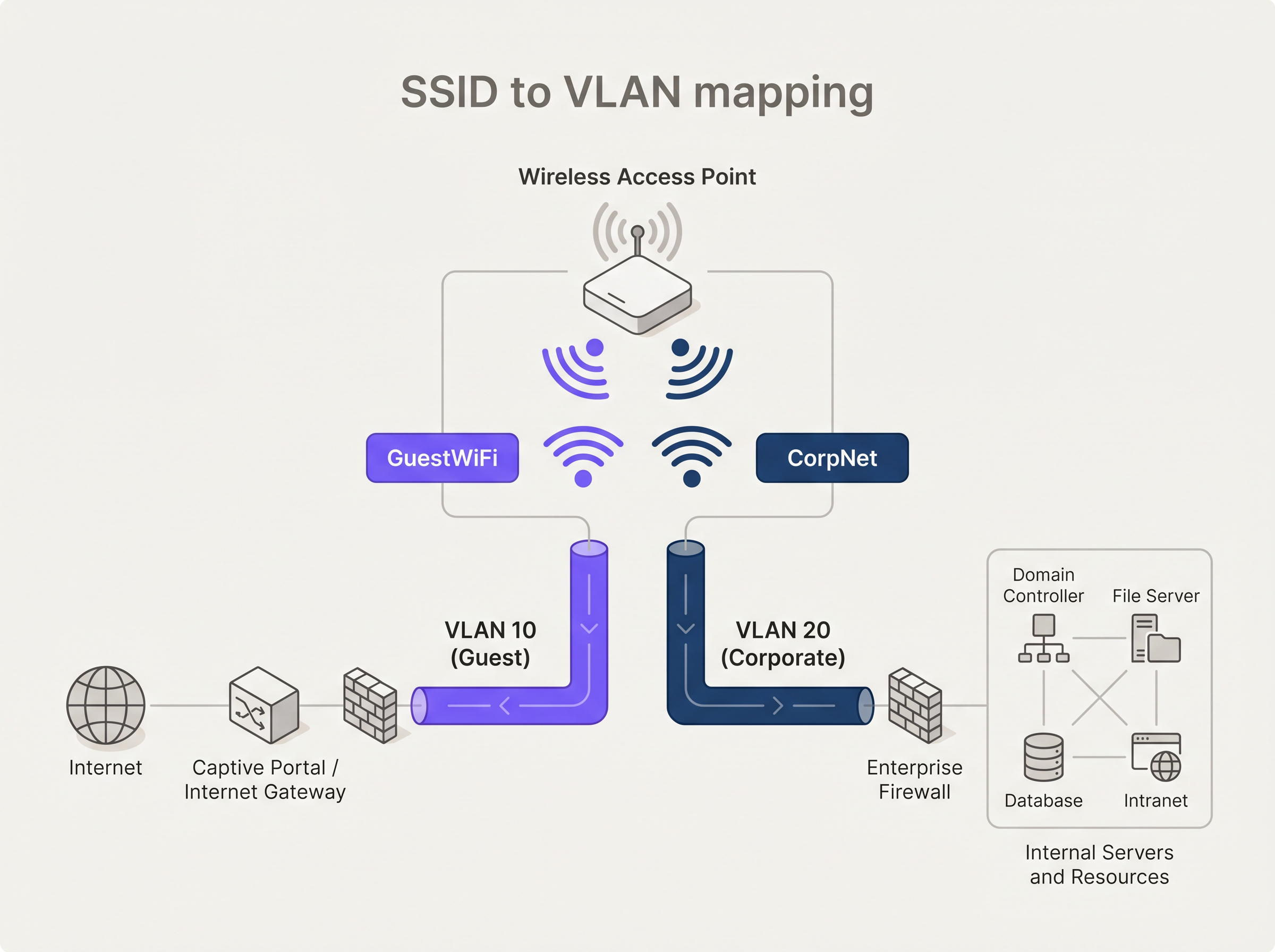
Para manter esta separação em toda a infraestrutura de switching, os pontos de acesso devem ser conectados a portas trunk 802.1Q em vez de portas de acesso. Isto garante que as tags de VLAN são preservadas à medida que o tráfego se move da borda para as camadas de distribuição e core.
Modelos de Autenticação e Criptografia
Os requisitos de autenticação diferem significativamente entre os dois ambientes.
Autenticação Corporativa: O padrão empresarial é IEEE 802.1X, tipicamente suportado por um servidor RADIUS. A autenticação baseada em certificado (EAP-TLS) é preferida em relação aos métodos baseados em credenciais (PEAP-MSCHAPv2) para garantir que apenas dispositivos geridos se possam conectar. Para proteger o próprio tráfego de autenticação, as organizações devem implementar RadSec: Securing RADIUS Authentication Traffic with TLS .
Autenticação de Convidados: Os dispositivos de convidados não são geridos. A abordagem padrão é um Captive Portal — uma página web que interceta o pedido HTTP/HTTPS inicial. As plataformas modernas aproveitam este ponto de interceção não apenas para a aceitação dos termos de serviço, mas para autenticação baseada em perfil e captura de dados em conformidade com o GDPR.
Relativamente à criptografia, WPA3 é o padrão atual. As redes de convidados devem utilizar WPA3-SAE (Simultaneous Authentication of Equals) para fornecer sigilo de encaminhamento, protegendo o tráfego passado mesmo que a chave pré-partilhada seja comprometida. As redes corporativas devem empregar WPA3-Enterprise no modo de 192 bits.
Guia de Implementação: Construir Acesso Seguro para Convidados
Implementar uma rede wireless segura para convidados requer uma configuração cuidadosa em toda a pilha de rede.
1. Provisionamento da Infraestrutura
Garanta que todos os controladores wireless, pontos de acesso e switches suportam 802.1Q VLAN tagging. Hardware de nível de consumidor é inadequado para ambientes empresariais. Configure âmbitos DHCP dedicados para a VLAN de convidados (por exemplo, 192.168.100.0/24) e atribua resolvedores DNS públicos (como 8.8.8.8 ou 1.1.1.1) para evitar a enumeração de recursos internos baseada em DNS.
2. Isolamento de Clientes
Ative o isolamento de clientes wireless (também conhecido como isolamento de AP) no SSID de convidados. Isto impede que dispositivos conectados ao mesmo ponto de acesso comuniquem entre si, mitigando o risco de movimento lateral ou ataques peer-to-peer dentro da rede de convidados.
3. Modelagem de Tráfego e QoS
Implemente políticas rigorosas de Quality of Service (QoS). Aplique limitação de taxa à VLAN de convidados para limitar a largura de banda por cliente (por exemplo, 10 Mbps de download / 2 Mbps de upload) e garanta que o tráfego corporativo, particularmente VoIP e videoconferência, recebe prioridade na fila.
4. Integração de Captive Portal
Integre o SSID de convidados com uma solução robusta de Captive Portal. Para locais em Retail ou Hospitality , o Captive Portal é o principal ponto de contacto digital. A plataforma da Purple permite que os locais autentiquem utilizadores via login social ou preenchimento de formulário, transformando endereços MAC anónimos em perfis de cliente acionáveis.
Melhores Práticas e Conformidade
Aderir aos padrões da indústria é inegociável, particularmente em setores regulados.
- Conformidade PCI DSS: Se o seu local processa pagamentos com cartão, o Cardholder Data Environment (CDE) deve ser estritamente isolado do tráfego de convidados. Qualquer segmento de rede partilhado viola os requisitos PCI DSS.
- GDPR e Privacidade de Dados: Ao capturar dados de utilizadores via Captive Portals, mecanismos de consentimento explícito devem estar em vigor. A arquitetura de dados deve suportar o direito ao esquecimento e a residência segura dos dados.
- Integração SD-WAN: Para cadeias de retalho ou hotelaria distribuídas, encaminhar o tráfego de convidados diretamente para a internet na borda da filial (local breakout) enquanto o tráfego corporativo é transportado de volta via túneis seguros é altamente eficiente. Leia mais sobre The Core SD WAN Benefits for Modern Businesses .
Resolução de Problemas e Mitigação de Riscos
Os modos de falha comuns em implementações de WiFi para convidados resultam frequentemente de desvios de configuração ou hardware inadequado.
Problema: Convidados a aceder a endereços IP internos. Causa: Configuração inadequada da VLAN ou encaminhamento inter-VLAN ativado no switch/firewall principal. Mitigação: Auditar as Listas de Controlo de Acesso (ACLs). Implementar uma política de negação por predefinição para o tráfego originado da VLAN de convidados destinado ao espaço IP privado RFC 1918.
Problema: Degradação da rede corporativa durante as horas de pico de visitantes. Causa: Limitação de largura de banda insuficiente na rede de convidados. Mitigação: Impor limites de taxa rigorosos por cliente e limites gerais de largura de banda da VLAN de convidados na extremidade da firewall.
ROI e Impacto no Negócio
Historicamente, o WiFi para convidados era visto como um custo irrecuperável — uma necessidade operacional para centros de Transporte , instalações de Saúde e ambientes de retalho. Ao implementar um Captive Portal sofisticado e uma camada de análise, este centro de custos torna-se um ativo gerador de receita.
O ROI é medido através de:
- Aquisição de Dados Próprios: Construção de uma base de dados CRM de visitantes verificados.
- Automação de Marketing: Acionamento de campanhas automatizadas com base na frequência de visitas e tempo de permanência.
- Monetização de Mídia de Retalho: Utilização da página de splash do Captive Portal como espaço publicitário premium.
Briefing de Especialistas: Podcast
Ouça o nosso consultor sénior a detalhar as diferenças arquitetónicas e as armadilhas comuns nas implementações de WiFi para convidados empresariais.
Definições Principais
VLAN (Virtual Local Area Network)
A logical grouping of devices on the same physical network infrastructure, functioning as if they were on separate isolated LANs.
Used to separate guest traffic from corporate traffic across the same switches and access points.
SSID (Service Set Identifier)
The public name of a wireless network broadcast by an access point.
The primary identifier users see when connecting; must be mapped to specific VLANs for security.
Captive Portal
A web page that intercepts a user's initial internet request on a public network, requiring action (login, acceptance of terms) before granting access.
The primary authentication and data capture mechanism for enterprise guest WiFi.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The gold standard for securing the corporate main network, ensuring only authorized, managed devices can connect.
Client Isolation (AP Isolation)
A wireless security feature that prevents devices connected to the same AP from communicating directly with each other.
Critical for guest networks to prevent peer-to-peer attacks and lateral movement between untrusted devices.
QoS (Quality of Service)
Technologies that manage data traffic to reduce packet loss, latency, and jitter on the network by prioritizing specific types of data.
Used to ensure business-critical corporate traffic is not degraded by heavy bandwidth usage on the guest network.
WPA3-SAE
Simultaneous Authentication of Equals, the secure key establishment protocol used in WPA3-Personal.
Provides forward secrecy for guest networks, replacing the vulnerable pre-shared key (PSK) method of WPA2.
Inter-VLAN Routing
The process of forwarding network traffic from one VLAN to another using a router or Layer 3 switch.
Must be explicitly disabled or heavily restricted via ACLs between guest and corporate VLANs to maintain isolation.
Exemplos Práticos
A 200-room hotel needs to deploy WiFi for both guests and administrative staff using the same physical access points. How should the network be architected to ensure PCI DSS compliance for the front desk POS terminals?
Deploy 802.1Q VLAN tagging across all switches and APs. Create VLAN 10 for Guests, VLAN 20 for Admin Staff, and VLAN 30 for POS terminals. The Guest SSID maps to VLAN 10 with client isolation enabled and routes directly to the internet via a captive portal. The Admin SSID maps to VLAN 20 with 802.1X authentication. The POS terminals are hardwired to access ports assigned to VLAN 30. The firewall must have strict ACLs explicitly denying any routing between VLAN 10/20 and VLAN 30.
A large retail chain is experiencing poor performance on their corporate inventory scanners because customers are streaming high-definition video on the free guest WiFi.
Implement QoS policies at the wireless controller and firewall levels. Apply a per-client bandwidth limit (e.g., 5 Mbps) on the Guest SSID. Configure the corporate SSID (used by scanners) with high-priority QoS tags (e.g., WMM Voice/Video categories) and guarantee a minimum bandwidth allocation for the corporate VLAN at the WAN edge.
Perguntas de Prática
Q1. You are deploying a new guest WiFi network for a hospital. The hospital requires guests to accept a Terms of Service policy before accessing the internet. Which authentication mechanism is most appropriate?
Dica: Consider how unmanaged devices interact with public networks versus managed corporate devices.
Ver resposta modelo
A Captive Portal is the correct mechanism. Unlike 802.1X which requires pre-configured certificates or credentials on managed devices, a captive portal intercepts the initial web request from any unmanaged device and redirects it to a splash page where the Terms of Service can be presented and accepted.
Q2. A network engineer has configured a new 'Guest' SSID with a WPA3 password, but guests are still receiving IP addresses from the internal corporate DHCP server (10.0.0.x). What is the architectural flaw?
Dica: Look at the Layer 2 configuration between the access point and the switch.
Ver resposta modelo
The SSID has not been mapped to a dedicated VLAN, or the access point is connected to an access port rather than a trunk port. Because VLAN tagging is missing or stripped, the guest traffic is falling into the native corporate VLAN broadcast domain, allowing it to reach the internal DHCP server.
Q3. To save costs, a retail manager suggests plugging a consumer-grade wireless router into the back-office switch to provide guest WiFi. Why is this a critical security risk?
Dica: Consider the capabilities of consumer hardware regarding network segmentation.
Ver resposta modelo
Consumer-grade routers typically do not support 802.1Q VLAN tagging. Plugging it directly into the back-office switch places guest traffic on the same Layer 2 network as the corporate devices (like POS systems). This eliminates network segmentation, exposing the corporate network to lateral movement and violating PCI DSS compliance.
Continue a ler esta série
O que é um Pedido de Sondagem? Compreender Como os Dispositivos Descobrem Redes
Este guia de referência técnica oferece uma análise aprofundada dos pedidos de sondagem IEEE 802.11, da varredura ativa versus passiva e do impacto da aleatorização de MAC na análise de locais. Apresenta estratégias de implementação acionáveis para arquitetos de rede otimizarem implementações de alta densidade, mitigarem tempestades de sondagem e garantirem a recolha de dados precisa e em conformidade com o GDPR, utilizando camadas de identidade autenticadas.
Como Corrigir WiFi Lento Sem Atualizar o Seu Plano de Internet
Um guia de referência técnica abrangente para gestores de TI e arquitetos de rede sobre como otimizar o desempenho de WiFi empresarial sem aumentar a largura de banda do ISP. Abrange a otimização de RF, gestão da densidade de clientes, implementação de QoS e como aproveitar a análise de WiFi para diagnosticar e resolver gargalos.
A Lista de Verificação para Migrar de NAC Legado para NAC Nativo da Nuvem
Este guia de referência técnica e autoritário fornece uma lista de verificação estruturada em três fases para migrar do Network Access Control (NAC) legado para uma arquitetura nativa da nuvem. Ele equipa gestores de TI e arquitetos de rede com estratégias acionáveis para gerir a integração de identidades, a paridade de políticas e a conformidade sem interromper as operações do local.