सुरक्षित अतिथी प्रवेश: व्यवस्थापित नसलेल्या उपकरणांसाठी NAC लागू करणे
हे अधिकृत तांत्रिक संदर्भ मार्गदर्शक व्यवस्थापित नसलेल्या अतिथी उपकरणांना सुरक्षित करण्यासाठी नेटवर्क ॲक्सेस कंट्रोल (NAC) लागू करण्याच्या आर्किटेक्चर, डिप्लॉयमेंट आणि अनुपालन विचारांचे तपशीलवार वर्णन करते. हे आयटी नेत्यांना कॉर्पोरेट पायाभूत सुविधांना धोका न देता सुरक्षित अतिथी प्रवेश मिळवण्यासाठी कृतीयोग्य मार्गदर्शन प्रदान करते.
Listen to this guide
View podcast transcript
- कार्यकारी सारांश
- तांत्रिक सखोल अभ्यास: व्यवस्थापित नसलेल्या उपकरणांसाठी NAC आर्किटेक्चर
- त्रि-स्तरीय आर्किटेक्चर
- WPA3 आणि संधीसाधू वायरलेस एन्क्रिप्शन (OWE)
- MAC ॲड्रेस रँडमायझेशन आणि ओळख बंधन
- अंमलबजावणी मार्गदर्शक
- पायरी 1: नेटवर्क सेगमेंटेशन आणि VLANs परिभाषित करा
- पायरी 2: RADIUS पायाभूत सुविधा डिप्लॉय आणि कॉन्फिगर करा
- पायरी 3: Captive Portal आणि ओळख प्रवाह कॉन्फिगर करा
- पायरी 4: एंड-टू-एंड चाचणी आणि प्रमाणीकरण
- उत्तम कार्यपद्धती आणि अनुपालन
- समस्यानिवारण आणि जोखीम कमी करणे
- ROI आणि व्यवसायावर परिणाम

कार्यकारी सारांश
हॉस्पिटॅलिटी, रिटेल किंवा सार्वजनिक क्षेत्रातील एंटरप्राइझ ठिकाणांसाठी, अतिथी आणि कंत्राटदारांना अखंड WiFi प्रवेश प्रदान करणे ही व्यावसायिक गरज आहे. तथापि, व्यवस्थापित नसलेली उपकरणे एक महत्त्वपूर्ण हल्ला पृष्ठभाग (attack surface) सादर करतात. तुमच्या नेटवर्कशी कनेक्ट होणारे प्रत्येक स्मार्टफोन, टॅबलेट आणि IoT उपकरण एक अज्ञात घटक आहे, जे तुमच्या मोबाईल डिव्हाइस मॅनेजमेंट (MDM) पायाभूत सुविधांच्या नियंत्रणाबाहेर कार्य करते. आयटी नेत्यांसाठी आव्हान हे आहे की, कॉर्पोरेट मालमत्तेपासून या उपकरणांना काटेकोरपणे वेगळे ठेवून आणि PCI DSS व GDPR सारख्या फ्रेमवर्कचे अनुपालन सुनिश्चित करून हा प्रवेश सुलभ करणे.
हे मार्गदर्शक विशेषतः व्यवस्थापित नसलेल्या उपकरणांसाठी नेटवर्क ॲक्सेस कंट्रोल (NAC) लागू करण्याबद्दल सखोल माहिती देते. आम्ही मूलभूत प्री-शेअर्ड कीजच्या पलीकडे जाऊन ओळख-आधारित, धोरण-सक्तीचे नेटवर्क सेगमेंटेशन शोधतो. RADIUS-समर्थित धोरण इंजिनसह एकत्रित Captive Portal चा लाभ घेऊन, संस्था वापरकर्त्याच्या अनुभवात अस्वीकार्य अडथळा न आणता कठोर सुरक्षा स्थिती लागू करू शकतात. आम्ही आर्किटेक्चरल डिझाइन, डिप्लॉयमेंट पद्धती आणि मोठ्या प्रमाणावर ओळख व संमती व्यवस्थापित करण्यासाठी Guest WiFi सारख्या प्लॅटफॉर्मचे एकत्रीकरण कव्हर करू.
तांत्रिक सखोल अभ्यास: व्यवस्थापित नसलेल्या उपकरणांसाठी NAC आर्किटेक्चर
नेटवर्क ॲक्सेस कंट्रोल म्हणजे नेटवर्क संसाधनांमध्ये धोरण-आधारित प्रवेशाची अंमलबजावणी. पारंपारिक 802.1X EAP-TLS सह व्यवस्थापित उपकरणांसाठी सुवर्ण मानक असले तरी—बहुतेकदा SCEP द्वारे प्रमाणपत्र डिप्लॉयमेंटवर अवलंबून असते (पहा The Role of SCEP and NAC in Modern MDM Infrastructure )—हा दृष्टिकोन तात्पुरत्या अतिथींसाठी अव्यवहार्य आहे. व्यवस्थापित नसलेल्या उपकरणांना अशा आर्किटेक्चरची आवश्यकता असते जे मजबूत सुरक्षा आणि कमी-घर्षण ऑनबोर्डिंगमध्ये संतुलन साधते.
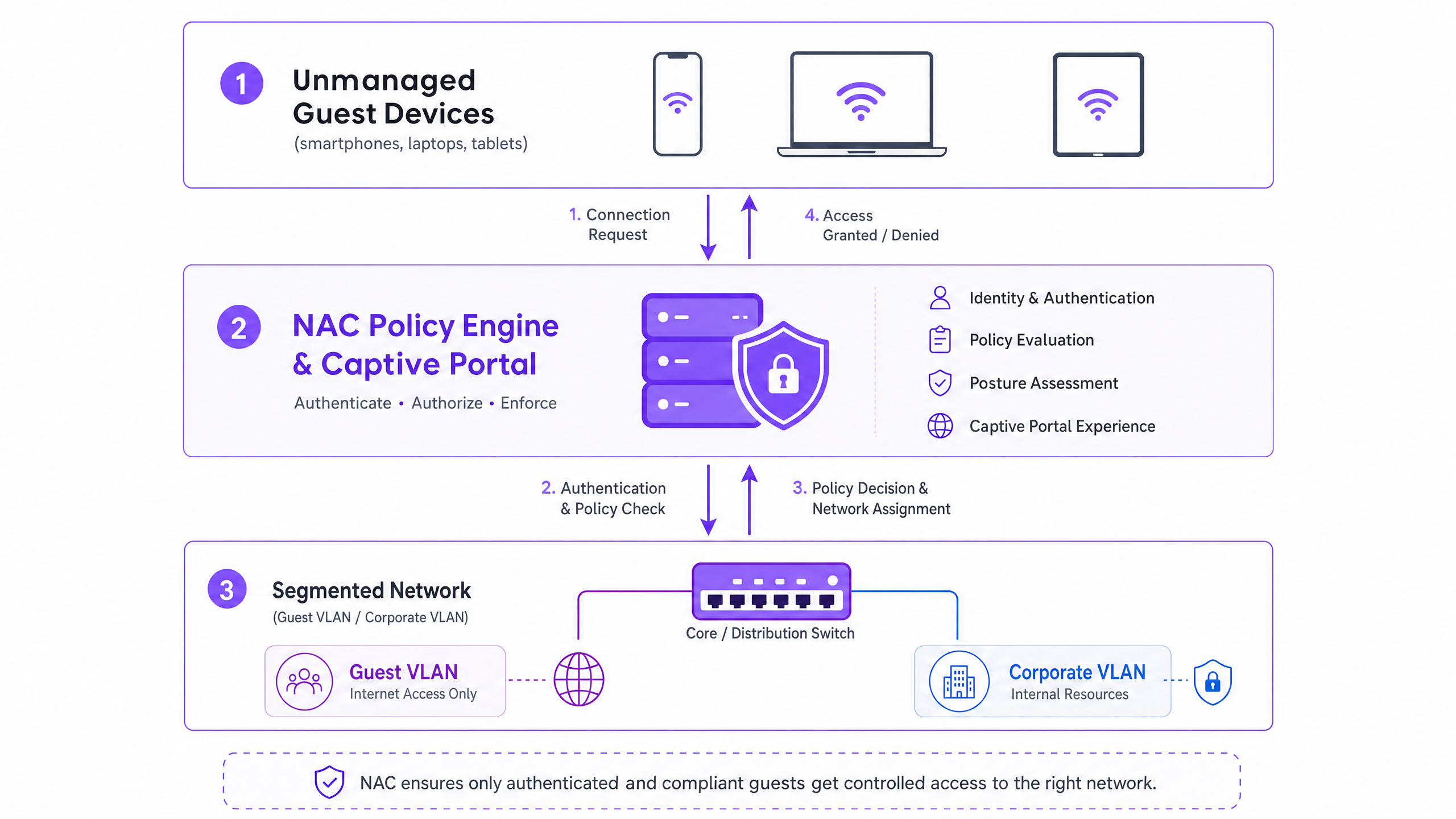
त्रि-स्तरीय आर्किटेक्चर
सुरक्षित अतिथी प्रवेशासाठी आर्किटेक्चरमध्ये तीन कार्यात्मक स्तर समाविष्ट आहेत:
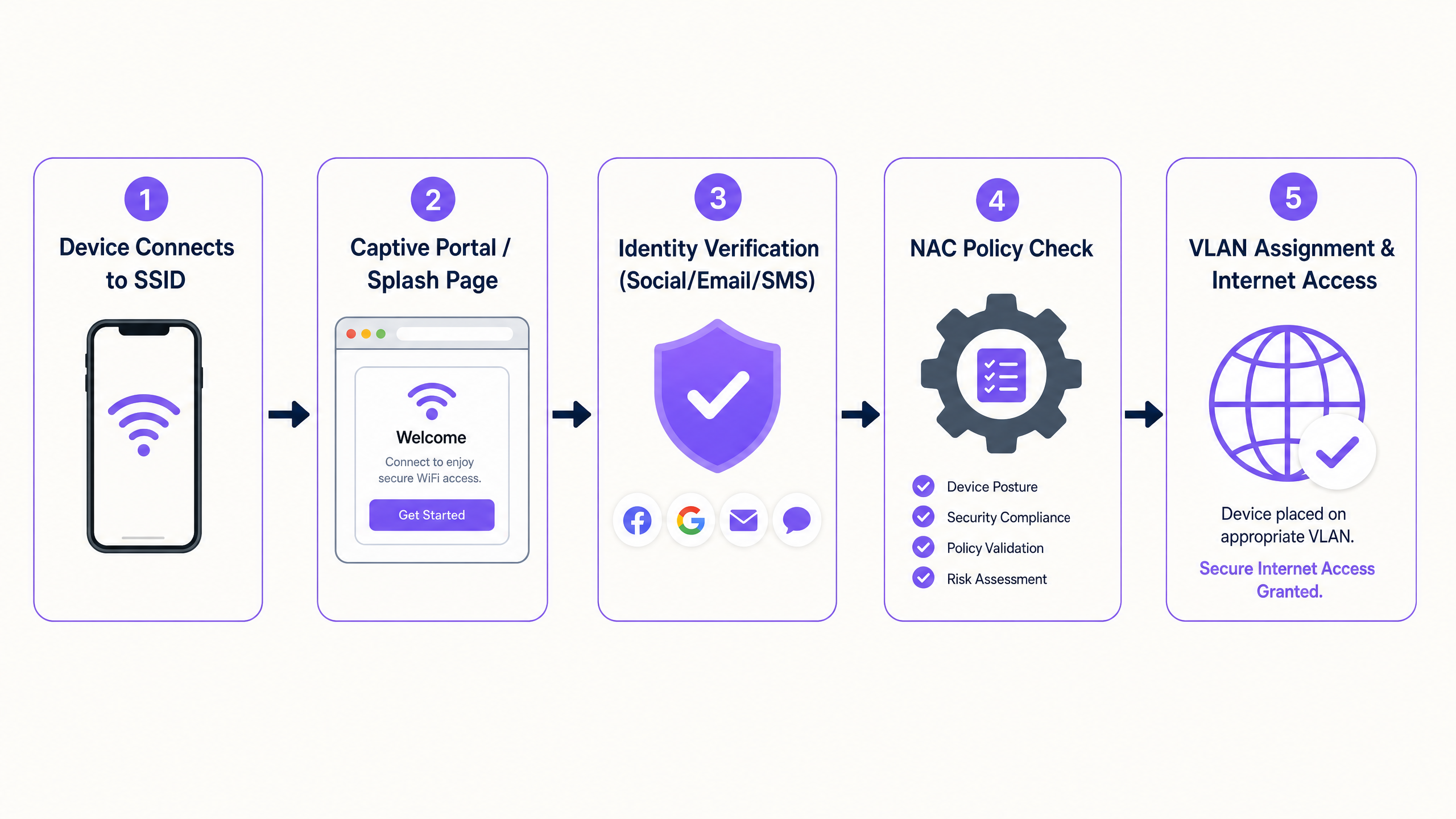
- प्रमाणीकरण आणि ओळख कॅप्चर: 802.1X व्यवस्थापित नसलेल्या उपकरणांसाठी अव्यवहार्य असल्याने, प्रमाणीकरण स्तर Captive Portal वर अवलंबून असतो. हा वेब-आधारित इंटरफेस प्रारंभिक HTTP/HTTPS विनंतीला अडवतो, वापरकर्त्याला प्रमाणीकरण प्रवाहाकडे पुनर्निर्देशित करतो. येथे, Purple च्या Guest WiFi सारखे प्लॅटफॉर्म ओळख प्रदाता म्हणून कार्य करतात, सामाजिक लॉगिन, ईमेल पडताळणी किंवा SMS द्वारे क्रेडेन्शियल्स कॅप्चर करतात.
- धोरण इंजिन (RADIUS/NAC): एकदा ओळख स्थापित झाल्यावर, धोरण इंजिन परिभाषित प्रवेश नियमांविरुद्ध विनंतीचे मूल्यांकन करते. प्रणाली प्रमाणीकृत ओळख, डिव्हाइस प्रकार किंवा दिवसाच्या वेळेनुसार योग्य नेटवर्क सेगमेंट निर्धारित करते.
- नेटवर्क एज अंमलबजावणी: वायरलेस ॲक्सेस पॉइंट आणि एज स्विच धोरणाच्या निर्णयाची अंमलबजावणी करतात. NAC प्रणाली RADIUS प्रोटोकॉलद्वारे संवाद साधते. यशस्वी प्रमाणीकरणानंतर, विशिष्ट VLAN असाइनमेंट ॲट्रिब्यूट्ससह
Access-Acceptसंदेश परत केला जातो, ज्यामुळे डिव्हाइस नियुक्त सेगमेंटवर ठेवले जाते.
WPA3 आणि संधीसाधू वायरलेस एन्क्रिप्शन (OWE)
आधुनिक वायरलेस सुरक्षेसाठी WPA3 मध्ये संक्रमण महत्त्वाचे आहे. WPA3-SAE वैयक्तिक नेटवर्कसाठी असुरक्षित WPA2-PSK ची जागा घेते, तर WPA3-OWE (Opportunistic Wireless Encryption) सार्वजनिक अतिथी नेटवर्कसाठी मानक आहे. OWE क्लायंट डिव्हाइस आणि ॲक्सेस पॉइंट दरम्यान पासवर्डची आवश्यकता नसताना वैयक्तिक डेटा एन्क्रिप्शन प्रदान करते. हे पारंपारिक ओपन गेस्ट SSIDs मध्ये असलेल्या क्लियरटेक्स्ट ट्रान्समिशन असुरक्षिततेला दूर करते, NAC धोरण लागू होण्यापूर्वीच एक सुरक्षित आधाररेखा प्रदान करते.
MAC ॲड्रेस रँडमायझेशन आणि ओळख बंधन
आधुनिक ऑपरेटिंग सिस्टम (iOS 14+, Android 10+, Windows 10) वापरकर्त्याच्या गोपनीयतेचे संरक्षण करण्यासाठी MAC ॲड्रेस रँडमायझेशन लागू करतात. उपकरणे प्रत्येक SSID साठी एक अद्वितीय, यादृच्छिक MAC ॲड्रेस तयार करतात ज्याला ते कनेक्ट होतात. हे मूलभूतपणे जुन्या NAC धोरणांना खंडित करते जे परत येणाऱ्या अतिथींसाठी MAC ॲड्रेसवर एक कायमस्वरूपी ओळखकर्ता म्हणून अवलंबून असतात.
आर्किटेक्चरल सोल्यूशन म्हणजे ओळख मॉडेल डिव्हाइसवरून वापरकर्त्याकडे बदलणे. जेव्हा एखादा अतिथी Captive Portal द्वारे प्रमाणीकरण करतो, तेव्हा सत्र त्यांच्या सत्यापित ओळखीशी (उदा. ईमेल किंवा फोन नंबर) बांधले जाणे आवश्यक आहे, तात्पुरत्या MAC ॲड्रेसऐवजी. Purple चे WiFi Analytics प्लॅटफॉर्म हे मूळतः हाताळते, MAC ॲड्रेस रोटेशनची पर्वा न करता, सत्रांमध्ये कायमस्वरूपी वापरकर्ता प्रोफाइल आणि अनुपालन रेकॉर्ड राखते.
अंमलबजावणी मार्गदर्शक
व्यवस्थापित नसलेल्या उपकरणांसाठी NAC डिप्लॉय करण्यासाठी ऑपरेशन्समध्ये व्यत्यय न आणता सुरक्षा सुनिश्चित करण्यासाठी एक पद्धतशीर दृष्टिकोन आवश्यक आहे.
पायरी 1: नेटवर्क सेगमेंटेशन आणि VLANs परिभाषित करा
NAC धोरणे कॉन्फिगर करण्यापूर्वी, अंतर्निहित नेटवर्क सेगमेंटेशन कठोर असणे आवश्यक आहे.
- पूर्व-प्रमाणीकरण VLAN (क्वारंटाईन): प्रारंभिक कनेक्शनवर उपकरणे येथे ठेवली जातात. या VLAN ने केवळ DNS रिझोल्यूशन आणि Captive Portal IP ॲड्रेससाठी असलेले HTTP/HTTPS ट्रॅफिकला परवानगी दिली पाहिजे. इतर सर्व ट्रॅफिक वगळले पाहिजे.
- अतिथी VLAN: प्रमाणीकरणानंतर, उपकरणे येथे हलविली जातात. या VLAN ला थेट इंटरनेट प्रवेश असणे आवश्यक आहे परंतु कॉर्पोरेट सबनेट (RFC 1918 स्पेस) आणि इतर अतिथी क्लायंट्स (क्लायंट आयसोलेशन) साठी सर्व राउटिंगला काटेकोरपणे नकार दिला पाहिजे.
- कंत्राटदार/विक्रेता VLAN: विशिष्ट अंतर्गत संसाधनांमध्ये प्रवेश आवश्यक असलेल्या ज्ञात तृतीय पक्षांसाठी एक वेगळा सेगमेंट, जो ग्रॅन्युलर फायरवॉल ACLs द्वारे नियंत्रित असतो.
पायरी 2: RADIUS पायाभूत सुविधा डिप्लॉय आणि कॉन्फिगर करा
RADIUS सर्व्हर तुमच्या नेटवर्क एज आणि ओळख प्रदाता यांच्यातील मध्यस्थ म्हणून कार्य करतो. एंटरप्राइझ डिप्लॉयमेंटसाठी, क्लाउड-होस्टेड RADIUS सेवेला तुमच्या Captive Portal प्लॅटफॉर्मसह एकत्रित केल्याने ऑपरेशनल ओव्हरहेड कमी होतो आणि रिडंडंसी सुधारते. RADIUS शेअर केलेले रहस्ये क्रिप्टोग्राफिकदृष्ट्या मजबूत आहेत आणि तुमच्या सुरक्षा धोरणानुसार फिरवले जातात याची खात्री करा.
पायरी 3: Captive Portal आणि ओळख प्रवाह कॉन्फिगर करा
प्रमाणीकरण प्रवाह हाताळण्यासाठी Captive Portal कॉन्फिगर करा. यामध्ये पोर्टल योग्यरित्या लोड होईल याची खात्री करण्यासाठी वॉल्ड गार्डन (प्रमाणीकरणापूर्वी प्रवेशयोग्य IP पत्ते आणि डोमेनची यादी) सेट करणे समाविष्ट आहे. महत्त्वाचे म्हणजे, प्रमाणीकरणापूर्वीच्या VLAN मध्ये DNS कार्य करणे आवश्यक आहे.
पायरी 4: एंड-टू-एंड चाचणी आणि प्रमाणीकरण
चाचणीने वापरकर्त्याचा अनुभव आणि सुरक्षा मर्यादा दोन्ही प्रमाणित केल्या पाहिजेत. चाचणी उपकरण Captive Portal प्रवाह यशस्वीरित्या पूर्ण करते आणि RADIUS ॲट्रिब्यूट्सद्वारे योग्य VLAN असाइनमेंट प्राप्त करते याची पडताळणी करा. सर्वात महत्त्वाचे म्हणजे, सेगमेंटेशन प्रमाणित करा: गेस्ट VLAN मधून ज्ञात कॉर्पोरेट IP पत्त्यावर पिंग करण्याचा किंवा ट्रॅफिक रूट करण्याचा प्रयत्न करा. हे अयशस्वी झाले पाहिजे.
उत्तम कार्यपद्धती आणि अनुपालन
- PCI DSS अनुपालन: Retail आणि Hospitality मधील ठिकाणांसाठी, PCI DSS कार्डहोल्डर डेटा एन्व्हायर्नमेंट (CDE) चे कठोर अलगीकरण अनिवार्य करते. गेस्ट WiFi CDE पासून भौतिक किंवा तार्किकदृष्ट्या वेगळे असले पाहिजे, ज्यात कोणतेही राउटिंग करण्याची परवानगी नाही. NAC ॲक्सेस लेयरवर याची अंमलबजावणी करते.
- GDPR आणि डेटा गोपनीयता: पोर्टलद्वारे अतिथी डेटा कॅप्चर करताना, स्पष्ट संमती घेणे आवश्यक आहे. Captive Portal ने वापराच्या स्पष्ट अटी आणि गोपनीयता धोरणे सादर करणे आवश्यक आहे. अंतर्निहित प्लॅटफॉर्मने स्वयंचलित डेटा रिटेन्शन धोरणे आणि विषय ॲक्सेस विनंत्यांना समर्थन दिले पाहिजे.
- सेशन व्यवस्थापन: योग्य सेशन टाइमआउट्स लागू करा. रिटेल वातावरणासाठी, 2-4 तासांचा टाइमआउट सामान्य आहे. हॉस्पिटॅलिटीसाठी, सेशनचा कालावधी अतिथीच्या मुक्कामाशी जुळवा. जुने सेशन्स साफ करण्यासाठी आणि DHCP लीज मोकळे करण्यासाठी नेहमी निष्क्रिय टाइमआउट (उदा. 30 मिनिटे) कॉन्फिगर करा.
समस्यानिवारण आणि जोखीम कमी करणे
- स्प्लिट-टनल गैर-कॉन्फिगरेशन: सर्वात गंभीर धोका म्हणजे कॉर्पोरेट नेटवर्कमध्ये गेस्ट VLAN मधून ट्रॅफिकला परवानगी देणारा चुकीचा कॉन्फिगर केलेला फायरवॉल नियम. फायरवॉल ACLs चे नियमित स्वयंचलित ऑडिटिंग आवश्यक आहे.
- DNS रिझोल्यूशन अपयश: जर अतिथींनी "लॉगिन पेज लोड होत नाही" अशी तक्रार केली, तर समस्या जवळजवळ नेहमीच DNS असते. प्रमाणीकरणापूर्वीच्या VLAN साठी DHCP स्कोप एक विश्वसनीय DNS सर्व्हर प्रदान करतो आणि फायरवॉल त्या सर्व्हरवर DNS ट्रॅफिकला (UDP पोर्ट 53) परवानगी देतो याची खात्री करा.
- RADIUS टाइमआउट हाताळणी (फेल-क्लोज्ड): RADIUS सर्व्हर पोहोचण्यायोग्य नसल्यास ॲक्सेस पॉइंट्सना "फेल-क्लोज्ड" करण्यासाठी कॉन्फिगर करा. "फेल-ओपन" कॉन्फिगरेशन आउटेज दरम्यान अप्रमाणित प्रवेश देतात, जे एक अस्वीकार्य सुरक्षा धोका दर्शवते.
ROI आणि व्यवसायावर परिणाम
NAC द्वारे सुरक्षित अतिथी प्रवेश लागू केल्याने मोजता येण्याजोगा व्यावसायिक मूल्य मिळते:
- जोखीम कमी करणे: व्यवस्थापित नसलेली उपकरणे कॉर्पोरेट मालमत्ता तपासू शकत नाहीत याची खात्री करून हल्ल्याच्या पृष्ठभागात मोजता येण्याजोगी घट.
- कार्यक्षमतेत वाढ: स्वयंचलित ऑनबोर्डिंगमुळे अतिथी प्रवेशाशी संबंधित IT हेल्पडेस्क तिकिटे कमी होतात.
- डेटा संपादन: Purple सारख्या प्लॅटफॉर्मचा वापर करून, सुरक्षित ऑनबोर्डिंग प्रक्रिया एकाच वेळी फर्स्ट-पार्टी डेटा कॅप्चर करते, जो मार्केटिंग ROI वाढवण्यासाठी WiFi Analytics प्लॅटफॉर्ममध्ये फीड केला जातो.
Key Definitions
Network Access Control (NAC)
A security framework that enforces policy-based access to network resources, evaluating identity and posture before granting access.
Used to ensure that unmanaged guest devices are properly segmented and authenticated before accessing the network.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted.
The primary authentication mechanism for unmanaged devices that cannot use 802.1X certificates.
RADIUS
Remote Authentication Dial-In User Service; a networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management.
The protocol used by the NAC policy engine to communicate VLAN assignments to the wireless access points.
Dynamic VLAN Assignment
The process of assigning a network device to a specific Virtual Local Area Network based on authentication credentials rather than the physical port or SSID.
Allows a single guest SSID to securely serve different types of users (guests, contractors) by placing them on different network segments.
WPA3-OWE
Opportunistic Wireless Encryption; a WiFi standard that provides individualized data encryption for open networks without requiring a password.
Secures the wireless transmission for guest networks, preventing passive eavesdropping on public SSIDs.
MAC Address Randomisation
A privacy feature in modern operating systems where the device generates a temporary MAC address for each wireless network it connects to.
Breaks legacy systems that use MAC addresses to track returning guests, necessitating identity-based authentication.
Walled Garden
A restricted environment that controls the user's access to web content and services prior to full authentication.
Required to allow unauthenticated devices to access the captive portal and necessary identity providers (like Facebook or Google) during the login process.
Client Isolation
A wireless network security feature that prevents devices connected to the same access point from communicating directly with each other.
Essential for guest networks to prevent infected guest devices from spreading malware to other guests.
Worked Examples
A large retail chain is rolling out guest WiFi across 500 stores. They need to ensure PCI compliance for their Point of Sale (POS) systems while allowing guests to connect and authenticate via a captive portal. How should the network be segmented and authenticated?
The implementation requires strict logical separation using VLANs and firewall ACLs. 1. The POS systems are placed on a dedicated, highly restricted Corporate VLAN (e.g., VLAN 10). 2. A Pre-Authentication VLAN (VLAN 20) is created for unauthenticated guests, allowing only DNS and HTTPS traffic to the captive portal domain. 3. A Guest VLAN (VLAN 30) is created for authenticated guests, allowing outbound internet access but explicitly denying all RFC 1918 (internal) IP addresses. The NAC system uses RADIUS to move devices from VLAN 20 to VLAN 30 upon successful portal authentication.
A hospital provides WiFi for patients and visitors but is experiencing issues where returning patients must re-authenticate every day because their smartphones randomize their MAC addresses. How can the IT team provide a seamless experience without compromising security?
The IT team must shift the authentication binding from the MAC address to the user identity. They implement a captive portal integrated with a platform like Purple Guest WiFi. When a patient first connects, they authenticate via SMS or email. The platform creates a persistent user profile. Even when the device generates a new MAC address on subsequent visits, the platform recognizes the user upon re-authentication and seamlessly applies the correct NAC policy without requiring a full re-registration.
Practice Questions
Q1. A hotel IT manager is configuring the pre-authentication VLAN for a new captive portal deployment. Guests are reporting that their devices connect to the WiFi, but the login page never appears. What is the most likely configuration error?
Hint: Consider what network services a device needs before it can load a web page via a domain name.
View model answer
The most likely error is a DNS resolution failure within the pre-authentication VLAN. Before a device can load the captive portal, it must resolve the portal's domain name. The DHCP scope for the pre-authentication VLAN must provide a valid DNS server, and the firewall must allow UDP port 53 traffic to that server prior to authentication.
Q2. You are designing the network policy for a stadium. The requirement is to provide internet access to fans while ensuring that the stadium's ticketing scanners (which connect to the same physical access points) have access to internal servers. How do you achieve this securely?
Hint: How can a single physical infrastructure support different logical networks based on identity?
View model answer
Implement dynamic VLAN assignment using 802.1X for the ticketing scanners and a captive portal for the fans. The ticketing scanners authenticate via certificates (802.1X) and are assigned by the RADIUS server to a secure Operations VLAN. Fans connect to an open (or OWE) SSID, authenticate via the captive portal, and are assigned by RADIUS to an isolated Guest VLAN with internet-only access.
Q3. During a security audit, it is discovered that devices on the Guest WiFi can ping the management IP addresses of the network switches. What specific configuration is missing or misconfigured?
Hint: Think about how traffic is controlled between different network segments.
View model answer
The firewall or Layer 3 switch is missing the necessary Access Control Lists (ACLs) to restrict routing from the Guest VLAN. A rule must be implemented that explicitly denies traffic originating from the Guest VLAN subnet destined for any internal subnets (RFC 1918 space), followed by a rule permitting traffic to the internet (0.0.0.0/0).