Secure Guest Access: Implementing NAC for Unmanaged Devices
This authoritative technical reference guide details the architecture, deployment, and compliance considerations for implementing Network Access Control (NAC) to secure unmanaged guest devices. It provides actionable guidance for IT leaders to achieve secure guest access without compromising corporate infrastructure.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive: NAC Architecture for Unmanaged Devices
- The Three-Tiered Architecture
- WPA3 and Opportunistic Wireless Encryption (OWE)
- MAC Address Randomisation and Identity Binding
- Implementation Guide
- Step 1: Define Network Segmentation and VLANs
- Step 2: Deploy and Configure RADIUS Infrastructure
- Step 3: Configure the Captive Portal and Identity Flow
- Step 4: End-to-End Testing and Validation
- Best Practices and Compliance
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
For enterprise venues—whether in hospitality, retail, or the public sector—providing seamless WiFi access to guests and contractors is a commercial necessity. However, unmanaged devices present a significant attack surface. Every smartphone, tablet, and IoT device connecting to your network is an unknown entity, operating outside the control of your Mobile Device Management (MDM) infrastructure. The challenge for IT leaders is to facilitate this access while strictly segmenting these devices from corporate assets and ensuring compliance with frameworks like PCI DSS and GDPR.
This guide provides a deep-dive into implementing Network Access Control (NAC) specifically for unmanaged devices. We move beyond basic pre-shared keys to explore identity-driven, policy-enforced network segmentation. By leveraging captive portals integrated with RADIUS-backed policy engines, organisations can enforce rigorous security postures without introducing unacceptable friction to the user experience. We will cover architectural design, deployment methodologies, and the integration of platforms like Guest WiFi to manage identity and consent at scale.
Technical Deep-Dive: NAC Architecture for Unmanaged Devices
Network Access Control is the enforcement of policy-based access to network resources. While traditional 802.1X with EAP-TLS is the gold standard for managed devices—often relying on certificate deployment via SCEP (see The Role of SCEP and NAC in Modern MDM Infrastructure )—this approach is unworkable for transient guests. Unmanaged devices require an architecture that balances robust security with low-friction onboarding.
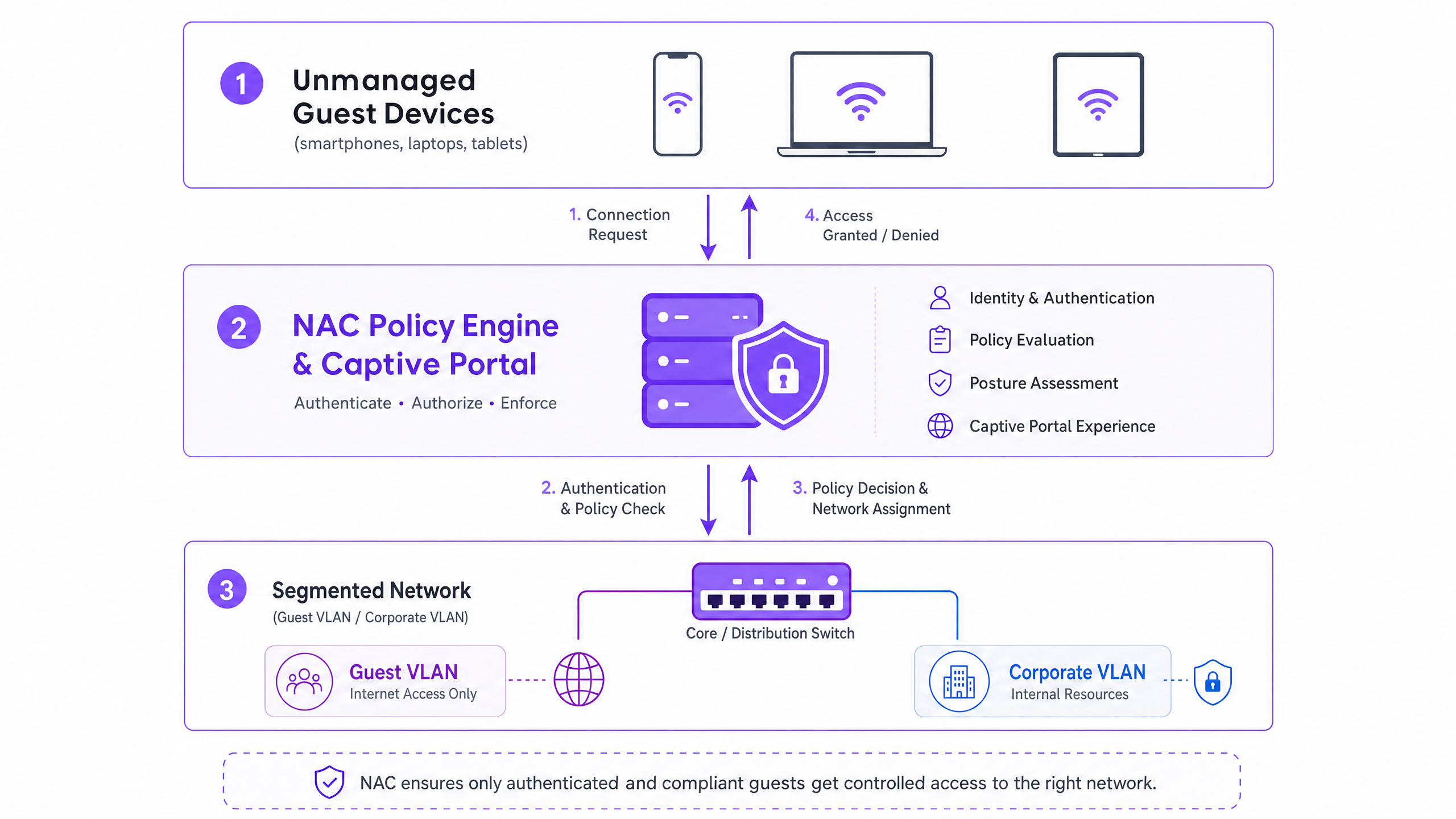
The Three-Tiered Architecture
The architecture for secure guest access comprises three functional layers:
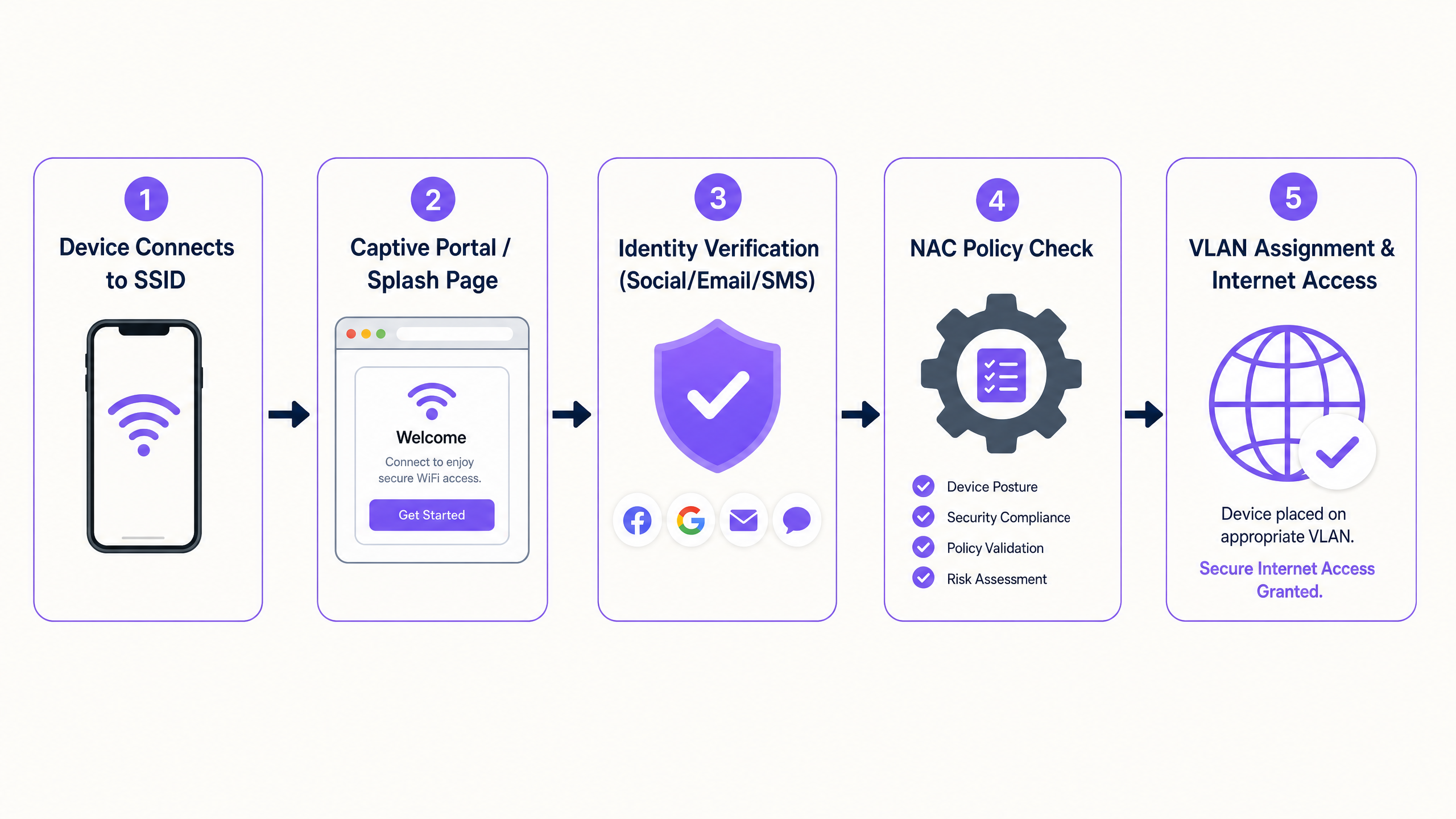
- Authentication and Identity Capture: Because 802.1X is impractical for unmanaged devices, the authentication layer relies on a captive portal. This web-based interface intercepts the initial HTTP/HTTPS request, redirecting the user to an authentication flow. Here, platforms like Purple's Guest WiFi operate as the identity provider, capturing credentials via social login, email verification, or SMS.
- Policy Engine (RADIUS/NAC): Once identity is established, the policy engine evaluates the request against defined access rules. The system determines the appropriate network segment based on the authenticated identity, device type, or time of day.
- Network Edge Enforcement: The wireless access points and edge switches enforce the policy decision. The NAC system communicates via the RADIUS protocol. Upon successful authentication, an
Access-Acceptmessage is returned with specific VLAN assignment attributes, placing the device onto the designated segment.
WPA3 and Opportunistic Wireless Encryption (OWE)
The transition to WPA3 is critical for modern wireless security. While WPA3-SAE replaces the vulnerable WPA2-PSK for personal networks, WPA3-OWE (Opportunistic Wireless Encryption) is the standard for public guest networks. OWE provides individualised data encryption between the client device and the access point without requiring a password. This eliminates the cleartext transmission vulnerability inherent in traditional open guest SSIDs, providing a secure baseline before the NAC policy is even applied.
MAC Address Randomisation and Identity Binding
Modern operating systems (iOS 14+, Android 10+, Windows 10) implement MAC address randomisation to protect user privacy. Devices generate a unique, randomised MAC address for each SSID they connect to. This fundamentally breaks legacy NAC policies that rely on the MAC address as a persistent identifier for returning guests.
The architectural solution is to shift the identity model from the device to the user. When a guest authenticates via the captive portal, the session must be bound to their verified identity (e.g., email or phone number) rather than the ephemeral MAC address. Purple's WiFi Analytics platform handles this natively, maintaining persistent user profiles and compliance records across sessions, regardless of MAC address rotation.
Implementation Guide
Deploying NAC for unmanaged devices requires a systematic approach to ensure security without disrupting operations.
Step 1: Define Network Segmentation and VLANs
Before configuring the NAC policies, the underlying network segmentation must be rigorous.
- Pre-Authentication VLAN (Quarantine): Devices are placed here upon initial connection. This VLAN must only allow DNS resolution and HTTP/HTTPS traffic destined for the captive portal IP addresses. All other traffic must be dropped.
- Guest VLAN: Post-authentication, devices are moved here. This VLAN must have direct internet access but strictly deny all routing to corporate subnets (RFC 1918 space) and other guest clients (client isolation).
- Contractor/Vendor VLAN: A separate segment for known third parties requiring access to specific internal resources, controlled by granular firewall ACLs.
Step 2: Deploy and Configure RADIUS Infrastructure
The RADIUS server acts as the intermediary between your network edge and the identity provider. For enterprise deployments, integrating a cloud-hosted RADIUS service with your captive portal platform reduces operational overhead and improves redundancy. Ensure that RADIUS shared secrets are cryptographically strong and rotated according to your security policy.
Step 3: Configure the Captive Portal and Identity Flow
Configure the captive portal to handle the authentication flow. This includes setting up the walled garden (the list of IP addresses and domains accessible pre-authentication) to ensure the portal loads correctly. Crucially, DNS must function within the pre-authentication VLAN.
Step 4: End-to-End Testing and Validation
Testing must validate both the user experience and the security boundaries. Verify that a test device successfully completes the captive portal flow and receives the correct VLAN assignment via RADIUS attributes. Most importantly, validate the segmentation: attempt to ping or route traffic from the Guest VLAN to a known corporate IP address. This must fail.
Best Practices and Compliance
- PCI DSS Compliance: For venues in Retail and Hospitality , PCI DSS mandates strict isolation of the Cardholder Data Environment (CDE). Guest WiFi must be physically or logically separated from the CDE, with no routing permitted. NAC enforces this at the access layer.
- GDPR and Data Privacy: When capturing guest data via the portal, explicit consent must be obtained. The captive portal must present clear terms of use and privacy policies. The underlying platform must support automated data retention policies and subject access requests.
- Session Management: Implement appropriate session timeouts. For retail environments, a 2-4 hour timeout is typical. For hospitality, align the session duration with the guest's stay. Always configure an idle timeout (e.g., 30 minutes) to clear stale sessions and free up DHCP leases.
Troubleshooting & Risk Mitigation
- Split-Tunnel Misconfiguration: The most severe risk is a misconfigured firewall rule allowing traffic from the Guest VLAN into the corporate network. Regular automated auditing of firewall ACLs is essential.
- DNS Resolution Failures: If guests complain that the "login page won't load," the issue is almost always DNS. Ensure the DHCP scope for the pre-authentication VLAN provides a reliable DNS server and that the firewall allows DNS traffic (UDP port 53) to that server.
- RADIUS Timeout Handling (Fail-Closed): Configure access points to "fail-closed" if the RADIUS server becomes unreachable. "Fail-open" configurations grant unauthenticated access during an outage, representing an unacceptable security risk.
ROI & Business Impact
Implementing secure guest access via NAC delivers measurable business value:
- Risk Mitigation: Quantifiable reduction in the attack surface by ensuring unmanaged devices cannot probe corporate assets.
- Operational Efficiency: Automated onboarding reduces IT helpdesk tickets related to guest access.
- Data Acquisition: By utilizing platforms like Purple, the secure onboarding process simultaneously captures first-party data, feeding into the WiFi Analytics platform to drive marketing ROI.
Key Definitions
Network Access Control (NAC)
A security framework that enforces policy-based access to network resources, evaluating identity and posture before granting access.
Used to ensure that unmanaged guest devices are properly segmented and authenticated before accessing the network.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted.
The primary authentication mechanism for unmanaged devices that cannot use 802.1X certificates.
RADIUS
Remote Authentication Dial-In User Service; a networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management.
The protocol used by the NAC policy engine to communicate VLAN assignments to the wireless access points.
Dynamic VLAN Assignment
The process of assigning a network device to a specific Virtual Local Area Network based on authentication credentials rather than the physical port or SSID.
Allows a single guest SSID to securely serve different types of users (guests, contractors) by placing them on different network segments.
WPA3-OWE
Opportunistic Wireless Encryption; a WiFi standard that provides individualized data encryption for open networks without requiring a password.
Secures the wireless transmission for guest networks, preventing passive eavesdropping on public SSIDs.
MAC Address Randomisation
A privacy feature in modern operating systems where the device generates a temporary MAC address for each wireless network it connects to.
Breaks legacy systems that use MAC addresses to track returning guests, necessitating identity-based authentication.
Walled Garden
A restricted environment that controls the user's access to web content and services prior to full authentication.
Required to allow unauthenticated devices to access the captive portal and necessary identity providers (like Facebook or Google) during the login process.
Client Isolation
A wireless network security feature that prevents devices connected to the same access point from communicating directly with each other.
Essential for guest networks to prevent infected guest devices from spreading malware to other guests.
Worked Examples
A large retail chain is rolling out guest WiFi across 500 stores. They need to ensure PCI compliance for their Point of Sale (POS) systems while allowing guests to connect and authenticate via a captive portal. How should the network be segmented and authenticated?
The implementation requires strict logical separation using VLANs and firewall ACLs. 1. The POS systems are placed on a dedicated, highly restricted Corporate VLAN (e.g., VLAN 10). 2. A Pre-Authentication VLAN (VLAN 20) is created for unauthenticated guests, allowing only DNS and HTTPS traffic to the captive portal domain. 3. A Guest VLAN (VLAN 30) is created for authenticated guests, allowing outbound internet access but explicitly denying all RFC 1918 (internal) IP addresses. The NAC system uses RADIUS to move devices from VLAN 20 to VLAN 30 upon successful portal authentication.
A hospital provides WiFi for patients and visitors but is experiencing issues where returning patients must re-authenticate every day because their smartphones randomize their MAC addresses. How can the IT team provide a seamless experience without compromising security?
The IT team must shift the authentication binding from the MAC address to the user identity. They implement a captive portal integrated with a platform like Purple Guest WiFi. When a patient first connects, they authenticate via SMS or email. The platform creates a persistent user profile. Even when the device generates a new MAC address on subsequent visits, the platform recognizes the user upon re-authentication and seamlessly applies the correct NAC policy without requiring a full re-registration.
Practice Questions
Q1. A hotel IT manager is configuring the pre-authentication VLAN for a new captive portal deployment. Guests are reporting that their devices connect to the WiFi, but the login page never appears. What is the most likely configuration error?
Hint: Consider what network services a device needs before it can load a web page via a domain name.
View model answer
The most likely error is a DNS resolution failure within the pre-authentication VLAN. Before a device can load the captive portal, it must resolve the portal's domain name. The DHCP scope for the pre-authentication VLAN must provide a valid DNS server, and the firewall must allow UDP port 53 traffic to that server prior to authentication.
Q2. You are designing the network policy for a stadium. The requirement is to provide internet access to fans while ensuring that the stadium's ticketing scanners (which connect to the same physical access points) have access to internal servers. How do you achieve this securely?
Hint: How can a single physical infrastructure support different logical networks based on identity?
View model answer
Implement dynamic VLAN assignment using 802.1X for the ticketing scanners and a captive portal for the fans. The ticketing scanners authenticate via certificates (802.1X) and are assigned by the RADIUS server to a secure Operations VLAN. Fans connect to an open (or OWE) SSID, authenticate via the captive portal, and are assigned by RADIUS to an isolated Guest VLAN with internet-only access.
Q3. During a security audit, it is discovered that devices on the Guest WiFi can ping the management IP addresses of the network switches. What specific configuration is missing or misconfigured?
Hint: Think about how traffic is controlled between different network segments.
View model answer
The firewall or Layer 3 switch is missing the necessary Access Control Lists (ACLs) to restrict routing from the Guest VLAN. A rule must be implemented that explicitly denies traffic originating from the Guest VLAN subnet destined for any internal subnets (RFC 1918 space), followed by a rule permitting traffic to the internet (0.0.0.0/0).