PCI DSS Compliance for Retail WiFi Networks
This technical reference guide details the PCI DSS v4.0 requirements that apply specifically to retail WiFi networks, covering network segmentation architecture, encryption standards, authentication controls, and audit trail requirements. It provides actionable implementation guidance for IT managers and network architects who need to secure payment data while safely supporting separate guest and corporate wireless access.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- The PCI DSS v4.0 Wireless Scope
- Understanding the Cardholder Data Environment Boundary
- Network Architecture and Segmentation
- Encryption and Authentication Standards
- Implementation Guide
- Phase 1: Discovery and Scope Definition
- Phase 2: Segmentation Implementation
- Phase 3: Encryption Upgrade
- Phase 4: 802.1X and RADIUS Deployment
- Phase 5: Wireless Intrusion Detection
- Phase 6: Logging and Monitoring
- Best Practices
- Troubleshooting & Risk Mitigation
- Common Audit Findings
- ROI & Business Impact

Executive Summary
For IT managers and network architects operating across Retail , Hospitality , Transport , and public-sector venues, deploying wireless networks presents a critical compliance challenge: how to provide robust Guest WiFi and operational connectivity without inadvertently expanding the Cardholder Data Environment (CDE) scope. Under PCI DSS v4.0, any wireless network connected to the CDE, or transmitting payment data, is fully in scope for compliance audits — and the penalties for non-compliance are significant.
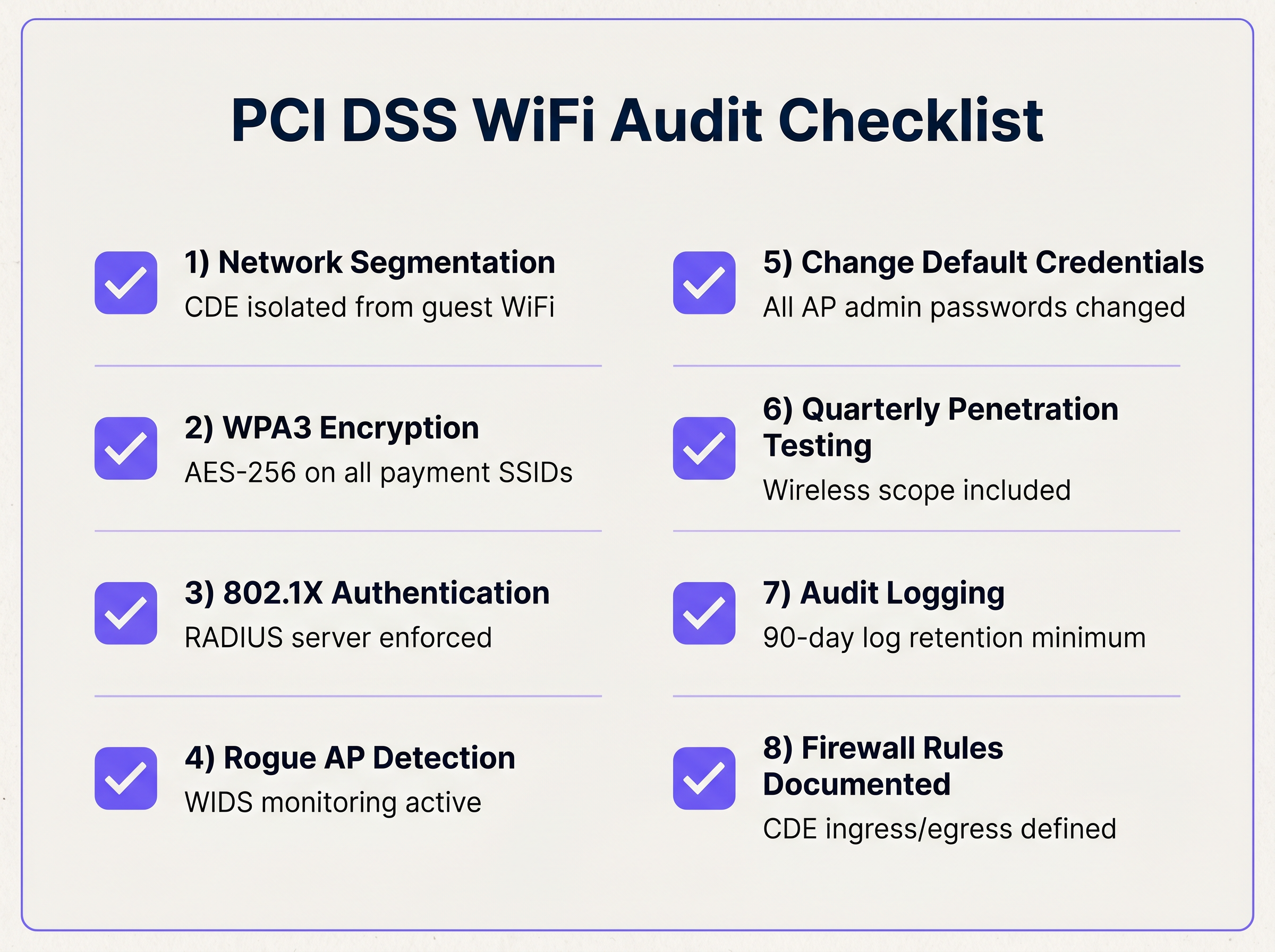
This guide outlines the technical requirements for isolating payment traffic, enforcing robust encryption standards (WPA3/AES-256), implementing 802.1X authentication, and maintaining continuous monitoring for rogue wireless devices. By adopting strict logical and physical network segmentation, retail IT teams can drastically reduce their compliance burden while maintaining high-performance connectivity for both point-of-sale (POS) systems and customer engagement platforms such as WiFi Analytics . The key principle is straightforward: keep payment traffic entirely separate from guest and corporate traffic, and validate that separation rigorously.
Technical Deep-Dive
The PCI DSS v4.0 Wireless Scope
PCI DSS v4.0 addresses wireless networks across several requirements. The most directly relevant are Requirement 2 (secure configurations and default credentials), Requirement 4 (encryption in transit), Requirement 6 (secure systems and software), Requirement 10 (audit logging), and Requirement 11 (security testing, including rogue wireless detection). The fundamental principle underpinning all of these is that wireless networks are inherently untrusted transmission media.
If a wireless network is used to transmit cardholder data — for example, mobile POS tablets on a retail shop floor — it is part of the CDE. If a wireless network, such as a guest WiFi network, shares the same physical hardware as the payment network but is logically segmented from the CDE, the segmentation controls themselves are in scope and must be rigorously tested and documented. This distinction is critical: the mere presence of a guest network on the same access point infrastructure does not automatically create a compliance failure, but it does create a compliance obligation to prove that the segmentation is effective.
Understanding the Cardholder Data Environment Boundary
Before designing any wireless architecture, the IT team must precisely define the CDE boundary. The CDE includes all systems that store, process, or transmit Primary Account Numbers (PANs), cardholder names, expiry dates, service codes, and Sensitive Authentication Data such as CVV2 values and PIN blocks. Any system that connects to a CDE system — even if it does not itself handle payment data — is also considered in scope unless robust segmentation controls isolate it.
In a typical retail environment, the CDE includes the POS terminals and their associated back-end servers, the payment gateway connections, and any wireless network over which payment data travels. The guest WiFi network, the corporate staff network, and any IoT devices such as digital signage or environmental sensors are out of scope — but only if they are properly isolated.
Network Architecture and Segmentation
The most effective strategy for containing PCI DSS scope is robust network segmentation. The goal is to ensure that a compromise of the public or corporate WiFi network cannot provide an attacker with a route into the payment network.
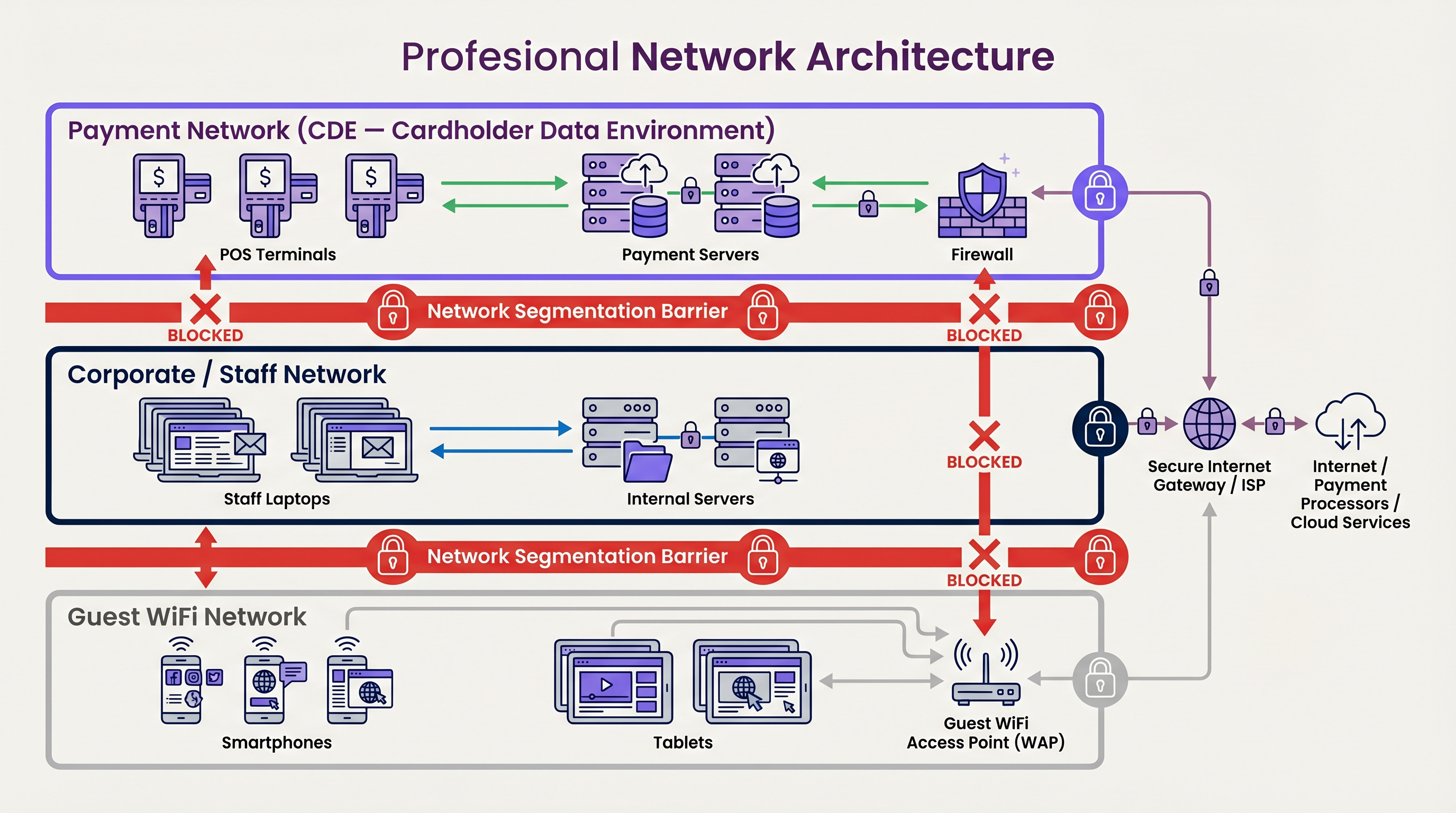
VLAN Isolation is the foundational control. Guest, Corporate, and Payment traffic must reside on separate VLANs with no routable paths between them. In a properly configured environment, the Guest VLAN has a single route to the internet via the firewall, and no route to any internal subnet. The Payment VLAN has a tightly controlled route to the payment gateway and to internal payment servers, with all other traffic explicitly denied.
Firewall Rules must enforce strict ingress and egress policies. The firewall ruleset should follow a default-deny posture: all traffic is blocked unless explicitly permitted. Permitted traffic flows should be documented in a network diagram and reviewed at least annually. Any rule that permits traffic into the CDE VLAN must be justified, documented, and approved by the security team.
Dedicated Hardware is an optional but recommended control for high-risk environments. Using dedicated access points and switches for the CDE eliminates the theoretical risk of VLAN hopping attacks, where a misconfigured switch port could bridge two VLANs. In practice, VLAN hopping via double-tagging attacks is rare on modern enterprise switches, but the risk is not zero. For organisations processing very high transaction volumes, or those operating in sectors with elevated threat profiles, dedicated hardware provides an additional layer of assurance.
Inter-VLAN Routing Validation must be performed after any network change. A simple test — attempting to ping a CDE device from the Guest VLAN — should fail completely. Penetration testers will perform more sophisticated validation, including attempts to exploit VLAN hopping vulnerabilities and testing for any misconfigured access control lists.
Encryption and Authentication Standards
Requirement 4.2.1 mandates strong cryptography for the transmission of cardholder data over open, public networks. Wireless networks are explicitly classified as open, public networks for this purpose.
WEP and WPA/WPA2-TKIP are strictly prohibited. These protocols have known cryptographic weaknesses that allow an attacker with passive monitoring capability to decrypt captured traffic within minutes. Any SSID still using these protocols must be upgraded immediately.
WPA3-Enterprise is the required standard for SSIDs transmitting payment data. WPA3-Enterprise uses CCMP-256 (AES-256 in Counter Mode with CBC-MAC) for data encryption and requires 802.1X authentication. It also provides Protected Management Frames (PMF) by default, which prevents deauthentication attacks — a common technique used by attackers to force clients to reconnect and capture authentication handshakes.
IEEE 802.1X Authentication is the mechanism that replaces shared Pre-Shared Keys with individual device and user authentication. In an 802.1X deployment, the access point acts as an authenticator, forwarding authentication requests to a RADIUS server. The RADIUS server validates the credentials — which may be a username/password pair, a client certificate, or both — and returns an Access-Accept or Access-Reject response. Only authenticated devices are granted network access.
EAP-TLS (Extensible Authentication Protocol with Transport Layer Security) is the gold standard for enterprise wireless authentication. It requires both the client and the RADIUS server to present valid X.509 certificates, providing mutual authentication. This eliminates the risk of a rogue RADIUS server tricking clients into connecting to a malicious network. Deploying EAP-TLS requires a Public Key Infrastructure (PKI) to issue and manage client certificates, which represents a meaningful operational investment but provides the strongest available authentication assurance.
Implementation Guide
Phase 1: Discovery and Scope Definition
Before implementing any controls, the IT team must map the current wireless footprint comprehensively. This means identifying every access point, wireless controller, and SSID currently in operation. For each SSID, determine whether any device connecting to it handles payment data. This discovery phase often reveals unexpected scope items — for example, a legacy SSID that was never decommissioned, or a vendor-managed wireless network for a payment terminal that the internal IT team was unaware of.
Document the findings in a network diagram that clearly shows the CDE boundary, all VLANs, all firewall rules, and all wireless SSIDs. This diagram is a mandatory deliverable for the PCI DSS assessment.
Phase 2: Segmentation Implementation
Configure the network switches and wireless controllers to map each SSID to its dedicated VLAN. Apply Access Control Lists at the switch and firewall level to enforce the default-deny posture. Test the segmentation by attempting to route traffic between VLANs — all such attempts should fail.
For organisations deploying modern SD-WAN architectures, the segmentation principles are identical, though the implementation mechanism differs. SD-WAN platforms can enforce policy-based routing that keeps payment traffic on dedicated, encrypted tunnels entirely separate from guest traffic. For more on this architecture, see The Core SD WAN Benefits for Modern Businesses .
Phase 3: Encryption Upgrade
Upgrade all CDE-facing SSIDs to WPA3-Enterprise. Configure the wireless controller to reject any client attempting to negotiate a lower encryption standard. If legacy devices on the payment network cannot support WPA3, deploy a separate SSID using WPA2-Enterprise with AES (not TKIP) as a time-limited fallback, and establish a hardware refresh timeline to eliminate the legacy devices.
Phase 4: 802.1X and RADIUS Deployment
Deploy a RADIUS server — either on-premises or as a cloud-managed service — and configure the wireless controller to forward authentication requests. Issue client certificates to all payment-network devices using an internal Certificate Authority. Configure the RADIUS server to reject authentication attempts from devices without a valid certificate.
Phase 5: Wireless Intrusion Detection
Enable WIDS/WIPS on the wireless controller. Configure the system to alert on: unauthorized SSIDs broadcasting on your premises, devices using your SSID name but not your BSSID (a common indicator of an evil twin attack), and access points physically connected to your network but not registered in the controller inventory.
Phase 6: Logging and Monitoring
Forward all wireless controller logs, RADIUS authentication logs, and firewall logs to a centralised SIEM. Verify that the log forwarding is working correctly by checking that recent authentication events appear in the SIEM within the expected time window. Configure alerts for authentication failures, VLAN policy violations, and rogue AP detections.
Best Practices
Change Default Credentials Without Exception. Requirement 2.1.1 is non-negotiable. Every access point, wireless controller, RADIUS server, and network switch must have its factory-default credentials changed before deployment. Maintain a credential management process that enforces complexity requirements and regular rotation.
Disable Unused Management Protocols. Telnet, HTTP, and SNMPv1/v2 transmit credentials and data in cleartext. Disable these protocols on all network hardware and use SSH, HTTPS, and SNMPv3 exclusively for management access.
Implement Port Security on Wired Switches. Requirement 1.3.2 requires controls to prevent unauthorized devices from connecting to the network. Enabling 802.1X on wired switch ports ensures that a rogue access point plugged into a network jack cannot gain network access without authenticating.
Conduct Regular Penetration Testing. PCI DSS Requirement 11.4 mandates annual penetration testing that includes the wireless environment. The test must validate that segmentation controls are effective — not just that they are configured. A penetration tester should actively attempt to breach the CDE from the Guest VLAN and document the results.
Maintain a Wireless Device Inventory. Keep an up-to-date inventory of all authorised wireless access points, including their MAC addresses, physical locations, and firmware versions. This inventory is essential for identifying rogue devices and for demonstrating control over the wireless environment to auditors.
Troubleshooting & Risk Mitigation
Common Audit Findings
VLAN Misconfiguration is the most common wireless-related finding. A single typo in a switch port configuration — for example, assigning a trunk port to the wrong native VLAN — can bridge the Guest and CDE VLANs, instantly bringing the entire public network into PCI scope. Mitigate this by using configuration management tools that enforce standardised templates across all switches, and by running automated configuration audits after every change.
Rogue Access Points remain a persistent risk. Employees plugging consumer-grade routers into corporate network jacks to improve WiFi coverage in a stockroom or back office can bypass all enterprise security controls. A WIDS provides continuous detection, but the root cause — employees who do not understand the security implications — must be addressed through security awareness training.
Legacy Device Retention is a significant compliance risk. Keeping WPA2-TKIP enabled on a single SSID to support one legacy barcode scanner compromises the security of every device on that SSID. The business case for retiring legacy hardware must be made in terms of compliance risk: the cost of a hardware refresh is almost always lower than the cost of a PCI DSS finding.
Insufficient Log Retention is frequently cited in audits. Many organisations have logging in place but have not verified that logs are being forwarded to the SIEM and retained for the required periods. Requirement 10.5.1 mandates a minimum of 90 days of active retention and 12 months of total retention. Verify this configuration explicitly and test it by querying the SIEM for events from 91 days ago.
Failure to Include Wireless in Penetration Test Scope is a common oversight. Penetration testing contracts often default to external and internal network testing, with wireless as an optional add-on. Ensure that the wireless environment — including validation of VLAN segmentation — is explicitly included in the scope of work.
ROI & Business Impact
Implementing a PCI-compliant wireless architecture requires upfront investment in enterprise-grade hardware, RADIUS infrastructure, PKI for certificate management, and WIDS/WIPS licensing. For a mid-sized retail chain with fifty locations, this investment can be substantial. However, the ROI calculation is straightforward when measured against the cost of non-compliance.
A single PCI DSS compliance violation can result in fines from card brands ranging from $5,000 to $100,000 per month until the issue is remediated. A data breach originating from an insecure wireless network carries additional costs: forensic investigation, mandatory notification to affected cardholders, potential litigation, and reputational damage that can take years to recover from. The Ponemon Institute's annual Cost of a Data Breach report consistently places the average cost of a retail data breach in the millions.
Beyond risk mitigation, a properly segmented wireless architecture enables the business to deploy revenue-generating tools without compliance risk. A secure, isolated Guest WiFi network allows the marketing team to leverage customer engagement and analytics platforms — including integrations such as HubSpot এবং Guest WiFi: লিড সমৃদ্ধকরণ এবং বিভাজন — without any risk of payment data exposure. Purple's Guest WiFi platform operates entirely on the guest-facing side of the network, cleanly separated from the payment infrastructure. This means retailers can capture first-party customer data, run loyalty programmes, and deliver personalised marketing — all while maintaining a hardened, auditable security posture.
For healthcare venues managing both patient WiFi and clinical device networks, the same segmentation principles apply, as explored in our Healthcare industry resources. The clean separation of operational and public networks is a universal architectural principle that pays dividends across compliance frameworks.
Key Terms & Definitions
Cardholder Data Environment (CDE)
The people, processes, and technology that store, process, or transmit cardholder data or sensitive authentication data, including any system connected to such systems.
IT teams must precisely define the CDE boundary before designing any wireless architecture. Everything inside the boundary is subject to the full set of PCI DSS controls.
Network Segmentation
The practice of isolating the CDE from the remainder of the corporate and public network using logical controls (VLANs, firewalls, ACLs) or physical controls (dedicated hardware).
Effective segmentation is the primary method for reducing the scope, cost, and complexity of a PCI DSS audit. Without it, the entire network is in scope.
WPA3-Enterprise
The latest Wi-Fi security protocol, providing AES-256 encryption via CCMP-256 and requiring 802.1X authentication backed by a RADIUS server. Also mandates Protected Management Frames (PMF) by default.
Mandatory for securing modern wireless payment networks. Replaces WPA2-Enterprise as the recommended standard under PCI DSS v4.0.
IEEE 802.1X
An IEEE standard for port-based network access control, providing an authentication mechanism to devices wishing to attach to a LAN or WLAN. Requires a supplicant (client), authenticator (AP or switch), and authentication server (RADIUS).
Replaces shared Pre-Shared Keys with individual user and device authentication, ensuring accountability and enabling granular access control on the payment network.
WIDS / WIPS
Wireless Intrusion Detection System / Wireless Intrusion Prevention System. Sensors that monitor the radio spectrum for unauthorized access points, rogue clients, and malicious wireless activity such as deauthentication attacks.
Required to satisfy PCI DSS Requirement 11.2.1 for detecting and responding to unauthorized wireless devices. Best practice is continuous monitoring rather than quarterly manual scans.
Rogue Access Point
An unauthorized wireless access point connected to the corporate network, either intentionally by an attacker or inadvertently by an employee, that bypasses enterprise security controls.
A primary vector for network compromise in retail environments. IT teams must have automated detection tools and a documented response procedure.
VLAN Hopping
An attack technique where a device on one VLAN gains unauthorized access to traffic on another VLAN, typically by exploiting misconfigured switch trunk ports or native VLAN settings.
A critical risk if the Guest WiFi VLAN is not properly isolated from the CDE VLAN. Mitigated by disabling DTP, setting explicit native VLANs, and using dedicated trunk ports.
RADIUS Server
Remote Authentication Dial-In User Service. A centralized authentication, authorization, and accounting (AAA) server that verifies credentials before granting network access, used as the backend for 802.1X authentication.
The required infrastructure for deploying 802.1X on the wireless payment network. Can be deployed on-premises or consumed as a cloud-managed service.
EAP-TLS
Extensible Authentication Protocol with Transport Layer Security. A mutual authentication method that uses X.509 certificates on both the client and the RADIUS server, providing the strongest available wireless authentication assurance.
The gold standard for enterprise wireless authentication on payment networks. Requires a PKI to issue and manage client certificates but eliminates the risk of credential theft or rogue RADIUS server attacks.
Protected Management Frames (PMF)
An IEEE 802.11w feature that encrypts and authenticates wireless management frames, preventing deauthentication and disassociation attacks.
Mandatory in WPA3. Should also be enabled on WPA2-Enterprise deployments to prevent attackers from forcing clients to reconnect and capturing authentication handshakes.
Case Studies
A 200-room hotel needs to provide high-speed guest WiFi while also supporting mobile POS tablets for poolside drink orders. Currently, both use the same WPA2-PSK network. The IT architect has been asked to redesign this for PCI DSS v4.0 compliance without replacing the existing access point hardware.
Step 1: Audit the existing wireless controller to confirm it supports multiple SSIDs mapped to separate VLANs and WPA3-Enterprise. Step 2: Create two SSIDs: 'Hotel_Guest' mapped to VLAN 10 and 'Hotel_Ops' mapped to VLAN 20. Step 3: Configure the core firewall with an explicit deny rule blocking all traffic from VLAN 10 to VLAN 20. VLAN 10 receives only a default route to the internet. Step 4: Upgrade 'Hotel_Ops' to WPA3-Enterprise. Deploy a RADIUS server (cloud-managed or on-premises) and issue client certificates to each POS tablet via an internal CA. Step 5: Enable WIDS on the wireless controller to monitor for rogue APs. Step 6: Commission a penetration test to validate that a device on VLAN 10 cannot reach any device on VLAN 20. Document the test results as audit evidence.
A 50-store retail chain is deploying a new guest WiFi analytics platform to capture customer footfall data and support loyalty programme sign-ups. The IT security manager is concerned that deploying the platform will expand the PCI DSS scope. How should the architecture be designed to prevent this?
The guest WiFi analytics platform must be deployed entirely within the Guest VLAN, which has no route to the CDE. The platform's servers — whether cloud-hosted or on-premises — must not be co-located on any subnet that contains payment systems. The SSID used for guest access must be isolated from the Payment SSID at both the VLAN and firewall level. The captive portal and data collection components of the analytics platform should communicate only with the internet (for cloud-hosted platforms) or with a dedicated analytics server on a separate, non-CDE VLAN. A network diagram showing the data flows for both the guest analytics platform and the payment network must be reviewed by the QSA to confirm that the two environments do not intersect.
Scenario Analysis
Q1. A retail chain is deploying a new mobile POS system across 30 stores. The vendor recommends using a hidden SSID with WPA2-PSK for quick deployment across all locations. As the network architect, do you approve this design? Justify your decision.
💡 Hint:Consider the security value of hidden SSIDs, the scalability of PSK key management, and the PCI DSS requirements for authentication on payment networks.
Show Recommended Approach
No. This design must be rejected on two grounds. First, hidden SSIDs provide zero security benefit — they are trivially discoverable by any wireless packet analyser and create operational complexity without any compensating control. Second, and more critically, WPA2-PSK uses a single shared key across all devices. If one tablet is compromised, stolen, or if the key is shared inappropriately, the entire payment network is exposed. PCI DSS requires individual device authentication for payment networks. The design must be revised to use WPA3-Enterprise (or WPA2-Enterprise with AES as a fallback) with 802.1X authentication backed by a RADIUS server, with each device issued a unique client certificate.
Q2. During a PCI DSS assessment, the QSA notes that the guest WiFi and the payment network share the same physical access points. The QSA asks for evidence that the two networks are properly segmented. What evidence do you provide?
💡 Hint:PCI DSS permits shared physical hardware. The question is about what evidence is required to demonstrate effective logical segmentation.
Show Recommended Approach
Provide the following: (1) A network diagram showing the two SSIDs mapped to separate VLANs, the VLAN configuration on the switches, and the firewall rules denying traffic between the Guest VLAN and the CDE VLAN. (2) The wireless controller configuration showing SSID-to-VLAN mappings. (3) The firewall ruleset showing explicit deny rules for inter-VLAN traffic. (4) The results of the most recent penetration test, which should include a specific test case where the tester attempted to access CDE resources from the Guest VLAN and confirmed that all such attempts were blocked.
Q3. Your WIDS generates an alert for a rogue access point with a signal strength suggesting it is physically inside your store. Investigation reveals the MAC address is not in your authorised AP inventory. What are your immediate response steps, and what documentation is required?
💡 Hint:Consider the incident response requirements under PCI DSS Requirement 12, and the difference between a rogue AP connected to your network versus a neighbouring network bleeding into your space.
Show Recommended Approach
Immediate steps: (1) Use the WIDS triangulation data to physically locate the device. (2) Determine whether the device is physically connected to your network infrastructure by checking switch port MAC address tables. (3) If connected to your network, isolate the switch port immediately and preserve the device for forensic investigation. (4) If not connected to your network (e.g., a neighbouring business or a customer's personal hotspot), classify it as an external device in the WIDS to prevent future false positives. Documentation required: Log the alert timestamp, the investigation steps taken, the findings, and the remediation actions in the security incident log. This documentation is mandatory audit evidence under Requirement 12.10.
Key Takeaways
- ✓Any wireless network transmitting payment data, or connected to the Cardholder Data Environment, is fully in scope for PCI DSS v4.0 — define your CDE boundary precisely before designing your wireless architecture.
- ✓Robust VLAN segmentation and firewall rules are mandatory to isolate the payment network from guest and corporate WiFi — validate this segmentation with penetration testing, not just configuration review.
- ✓WEP, WPA-TKIP, and WPA2-PSK are prohibited on payment networks — deploy WPA3-Enterprise with 802.1X authentication and individual device certificates.
- ✓Continuous WIDS/WIPS monitoring is essential for detecting rogue access points — quarterly manual scans are the minimum requirement, not the recommended practice.
- ✓Change all default vendor credentials on every piece of network hardware before deployment — this is a non-negotiable PCI DSS requirement with no compensating controls.
- ✓Proper network segmentation enables safe deployment of guest analytics and marketing platforms like Purple WiFi without expanding PCI compliance scope.
- ✓Audit log retention must meet PCI DSS minimums: 90 days active, 12 months total — verify this configuration explicitly and test it regularly.



