Retail WiFi: From Traffic Analytics to Personalised In-Store Experiences
This technical reference guide details the architectural shift from legacy guest WiFi to intelligent edge platforms in retail environments. It provides actionable guidance for IT leaders on deploying identity-driven networks, integrating analytics with CRM systems, and driving measurable ROI through personalised in-store experiences. From RF design and captive portal optimisation to clienteling integration and GDPR compliance, this guide covers the full end-to-end deployment lifecycle.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- Architectural Overview: The Intelligent Edge
- Data Acquisition and Identity Resolution
- The Integration Imperative: Closing the Online-to-Offline Loop
- Implementation Guide
- Phase 1: Infrastructure Readiness and RF Design
- Phase 2: Captive Portal and Authentication Design
- Phase 3: Analytics Configuration and Integration
- Best Practices
- Troubleshooting & Risk Mitigation
- Common Failure Modes
- Security and Compliance Risks
- ROI & Business Impact
- Key Performance Indicators
- The ROI Model

Executive Summary
For retail and hospitality IT leaders, providing connectivity is no longer sufficient; the network must actively generate business value. This guide details the architectural transition from legacy cost-centre guest networks to revenue-generating intelligent edge platforms. By leveraging robust analytics and identity-driven access, venue operators can capture granular footfall data, integrate with CRM platforms, and execute personalised clienteling strategies at scale. We explore the technical deployment models, data flow architectures, and risk mitigation strategies required to deploy a resilient, compliant, and highly profitable omnichannel WiFi solution. The objective is to equip network architects and omnichannel directors with the precise frameworks needed to implement identity-based authentication, integrate existing tech stacks, and drive measurable ROI through targeted in-store personalisation.
Technical Deep-Dive
Architectural Overview: The Intelligent Edge
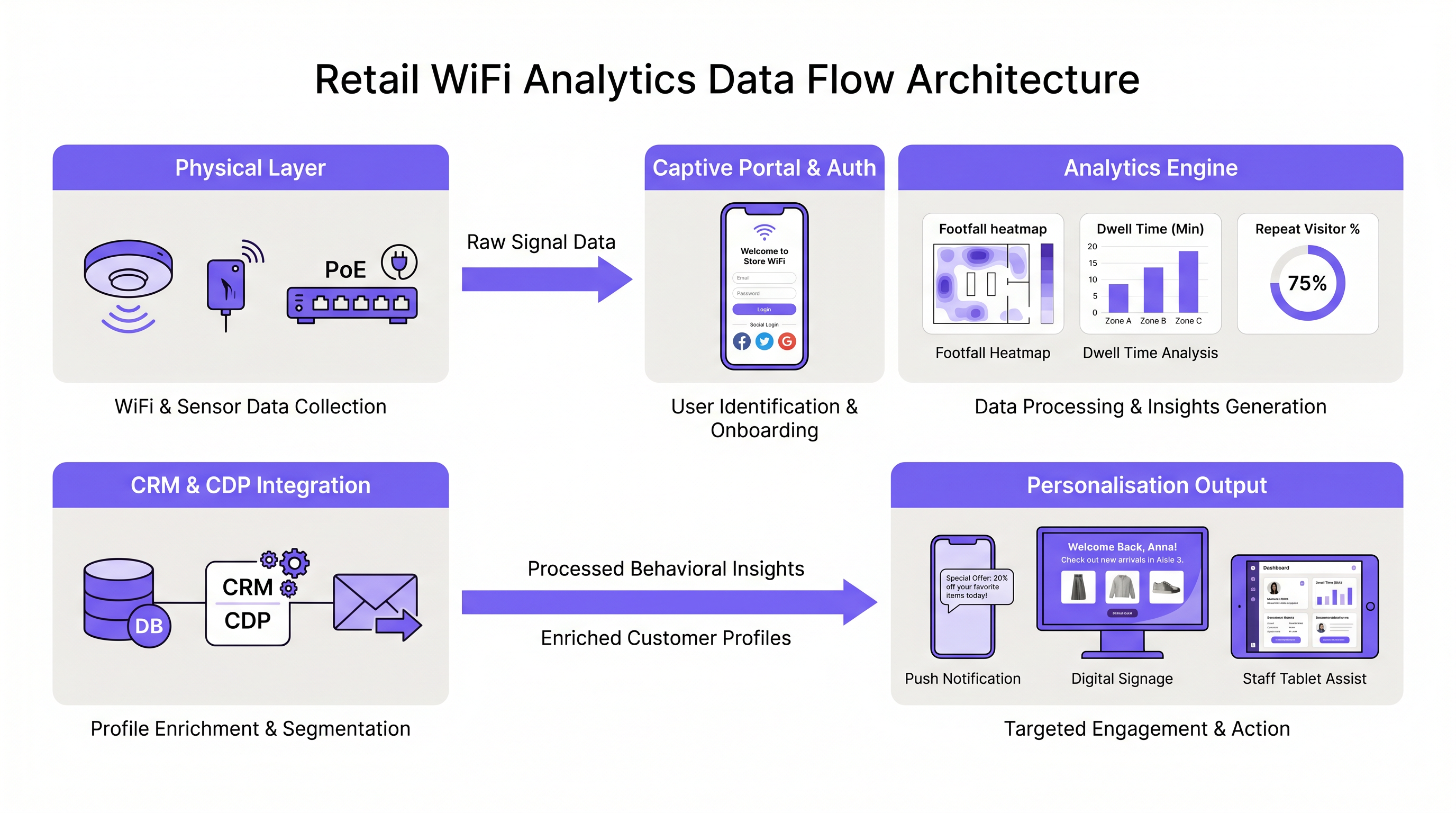
The transition to personalised in-store experiences requires a fundamental shift in how we view the network edge. It moves beyond simple packet forwarding to become a distributed sensor and identity management layer. This architecture typically comprises three core tiers.
The Physical Access Layer involves the deployment of high-density Access Points (APs) capable of both robust client connectivity and passive device scanning (probe requests). The density and placement of these APs are critical for accurate trilateration and location analytics. For enterprise-grade deployments, Wi-Fi 6 (802.11ax) or Wi-Fi 6E APs are recommended, providing the throughput and multi-user MIMO capabilities required in high-density retail environments.
The Identity and Policy Engine is where raw MAC addresses are translated into known customer profiles. Utilising a captive portal integrated with an identity provider (IdP), the system authenticates users via social logins, loyalty app credentials, or standard email registration. This tier enforces compliance (e.g., GDPR, CCPA) and manages consent, ensuring all data collection is lawful and auditable.
The Analytics and Integration Layer is the core intelligence engine. It aggregates presence data, dwell times, and user profiles, exposing this enriched data via APIs to the broader retail technology stack — CRM, CDP, marketing automation, and clienteling applications.
Data Acquisition and Identity Resolution
The foundation of in-store personalisation is accurate data acquisition. This involves capturing two distinct data streams.
Unauthenticated Presence Data leverages passive scanning of 802.11 probe requests to measure overall footfall, capture rates (passers-by vs. entrants), and aggregate dwell times. While MAC randomisation (e.g., iOS 14+, Android 10+) has materially impacted the persistence of this data for unique visitor tracking, it remains valuable for high-level trend analysis, zone occupancy, and queue management.
Authenticated Profile Data represents the critical pivot point. When a user connects to the Guest WiFi via the captive portal, the system associates the current (potentially randomised) MAC address with a persistent user identity (email, social ID, CRM ID). This process — often referred to as MAC binding or device onboarding — creates a unified customer view that persists across visits and channels.
The Integration Imperative: Closing the Online-to-Offline Loop
A standalone WiFi Analytics platform provides limited value. True personalisation requires deep, bi-directional integration with the existing enterprise architecture.
CRM and CDP Integration is the most critical integration point. The WiFi platform pushes real-time presence events (e.g., "High-value customer John Doe has entered Store 47") to the CRM. Conversely, the CRM can push segmentation data back to the WiFi platform to trigger personalised captive portal experiences, targeted digital signage content, or zone-specific push notifications.
Clienteling Applications represent the highest-value use case for high-touch retail environments. Real-time alerts routed to staff tablets or wearables provide associates with immediate access to a customer's purchase history, preferences, and loyalty tier as they walk through the door — transforming a generic interaction into a personalised service encounter.
Integrating platforms like HubSpot can significantly enhance this capability. For detailed guidance on this specific integration, refer to our guides on HubSpot এবং Guest WiFi: লিড সমৃদ্ধকরণ এবং বিভাজন or HubSpot और गेस्ट WiFi: लीड एनरिचमेंट और सेगमेंटेशन .
Implementation Guide
Deploying an intelligent Retail WiFi solution requires a phased, methodical approach to ensure stability, security, and measurable impact.
Phase 1: Infrastructure Readiness and RF Design
Before implementing analytics, the foundational RF environment must be optimised for both coverage and capacity.
Conduct a Predictive and Active Site Survey: Utilise industry-standard tools (e.g., Ekahau, Airmagnet) to design for high density, accounting for attenuation from specific retail fixtures (e.g., metal shelving, mirrors, glass partitions). A predictive model should be validated with a post-deployment active survey.
Optimise AP Placement for Location Services: If granular location tracking (trilateration) is required, AP placement must prioritise a perimeter-heavy design to ensure devices are "heard" by at least three APs simultaneously. A straight-line central-aisle deployment is insufficient for accurate location data.
Ensure Robust Backhaul: The increased data payload from analytics, real-time API calls, and rich media captive portals necessitates adequate WAN bandwidth and robust SD-WAN architectures. For more on this, see The Core SD WAN Benefits for Modern Businesses .
Phase 2: Captive Portal and Authentication Design
The captive portal is the primary digital touchpoint in the physical store. Its design directly impacts authentication rates — the percentage of visitors who provide identifiable data.
Frictionless Onboarding: Implement social login (Google, Facebook, Apple) to reduce friction to a single tap. If utilising email registration, keep form fields to an absolute minimum (Name, Email only). Every additional field reduces conversion by an estimated 10-15%.
Value Exchange: Clearly articulate the benefit of connecting. "Connect for 10% off today's purchase" or "Access exclusive in-store maps and new arrival alerts" consistently outperform generic "Free WiFi" prompts.
Compliance by Design: Ensure explicit, granular consent mechanisms for marketing communications and data processing, strictly adhering to GDPR Article 7 requirements. Consent must be freely given, specific, informed, and unambiguous.
Phase 3: Analytics Configuration and Integration
Define Zones and Geofences: Map the physical space into logical zones (e.g., "Menswear," "Checkout," "Window Display") within the analytics dashboard to track specific dwell times and conversion funnels. Zone-level data is significantly more actionable than store-level aggregates.
Configure API Webhooks: Set up real-time webhooks to push presence events to the CRM or clienteling application. Ensure the payload includes the unique customer identifier, the specific zone entered, and a timestamp. Implement retry logic with exponential backoff for resilience.
Establish Baselines: Run the system in "listen-only" mode for 2-4 weeks to establish baseline metrics for footfall, dwell time, and capture rates before launching active personalisation campaigns.
Best Practices
Based on deployments across thousands of enterprise venues — including major Hospitality chains, Transport hubs, and healthcare facilities — the following practices consistently drive superior outcomes.
Prioritise the Value Exchange. Customers will only surrender data if the perceived value is high. Generic "Free WiFi" is no longer a sufficient incentive. Tie connectivity to loyalty programmes or immediate in-store benefits to maximise authentication rates.
Segment Aggressively. Do not treat all connected users equally. Use the data gathered to create distinct segments (e.g., "Frequent Shoppers," "First-Time Visitors," "High Dwell/No Purchase") and tailor the digital and physical experience accordingly.
Embrace Profile-Based Authentication. Move away from shared PSKs (Pre-Shared Keys) or daily rotating passwords. Utilise identity-driven access (e.g., Passpoint/Hotspot 2.0 or MAC-based authentication tied to a CRM profile) to ensure seamless, secure reconnection for returning visitors.
Cross-Functional Alignment is Non-Negotiable. A successful deployment requires tight alignment between IT (infrastructure), Marketing (captive portal design and CRM), and Store Operations (clienteling and staff training). IT-only deployments consistently underperform.
Troubleshooting & Risk Mitigation
Common Failure Modes
The following table summarises the most frequently encountered failure modes and their mitigations:
| Failure Mode | Symptom | Root Cause | Mitigation |
|---|---|---|---|
| Empty Funnel | High passive footfall, low authentication | Complex portal, no value exchange, strong 5G coverage | Simplify login, improve value proposition, improve signage |
| Inaccurate Location Data | Devices "jumping" across zones | Collinear AP placement, insufficient AP density | Redesign RF for perimeter coverage and trilateration |
| Data Silo | Data collected but no downstream actions triggered | API rate limits, mismatched IDs, webhook failures | Establish consistent primary key (email), implement retry logic |
| Rogue AP Threat | Potential credential harvesting | Lack of WIDS/WIPS monitoring | Deploy and actively monitor WIDS/WIPS |
| PCI Scope Creep | Guest network traffic reaching POS systems | Inadequate network segmentation | Strict VLAN/firewall segmentation, regular penetration testing |
Security and Compliance Risks
Rogue APs and Evil Twins: Implement robust WIDS/WIPS (Wireless Intrusion Detection/Prevention Systems) to detect and mitigate unauthorised access points attempting to spoof the legitimate network and harvest credentials. This is a mandatory control in any PCI-scoped environment.
Data Privacy Violations: Failure to obtain explicit consent or properly anonymise passive data can lead to severe regulatory fines under GDPR (up to 4% of global annual turnover). Ensure the captive portal flow is regularly audited by legal and compliance teams.
PCI DSS Scope Creep: Ensure the guest/analytics network is logically and physically segmented from the corporate network handling Point of Sale (POS) transactions. Utilise dedicated VLANs with strict ACLs and firewall rules to maintain PCI DSS compliance.
ROI & Business Impact
The shift from a cost-centre to a revenue-generating asset requires a robust framework for measuring ROI.
Key Performance Indicators
The following KPIs form the core measurement framework for a retail WiFi personalisation deployment:
| KPI | Definition | Target Benchmark |
|---|---|---|
| Capture Rate | % of passers-by who enter the store | Baseline + trend |
| Authentication Rate | % of in-store visitors who connect and authenticate | >35% of connected devices |
| Dwell Time by Zone | Average time spent in defined store zones | Baseline + trend |
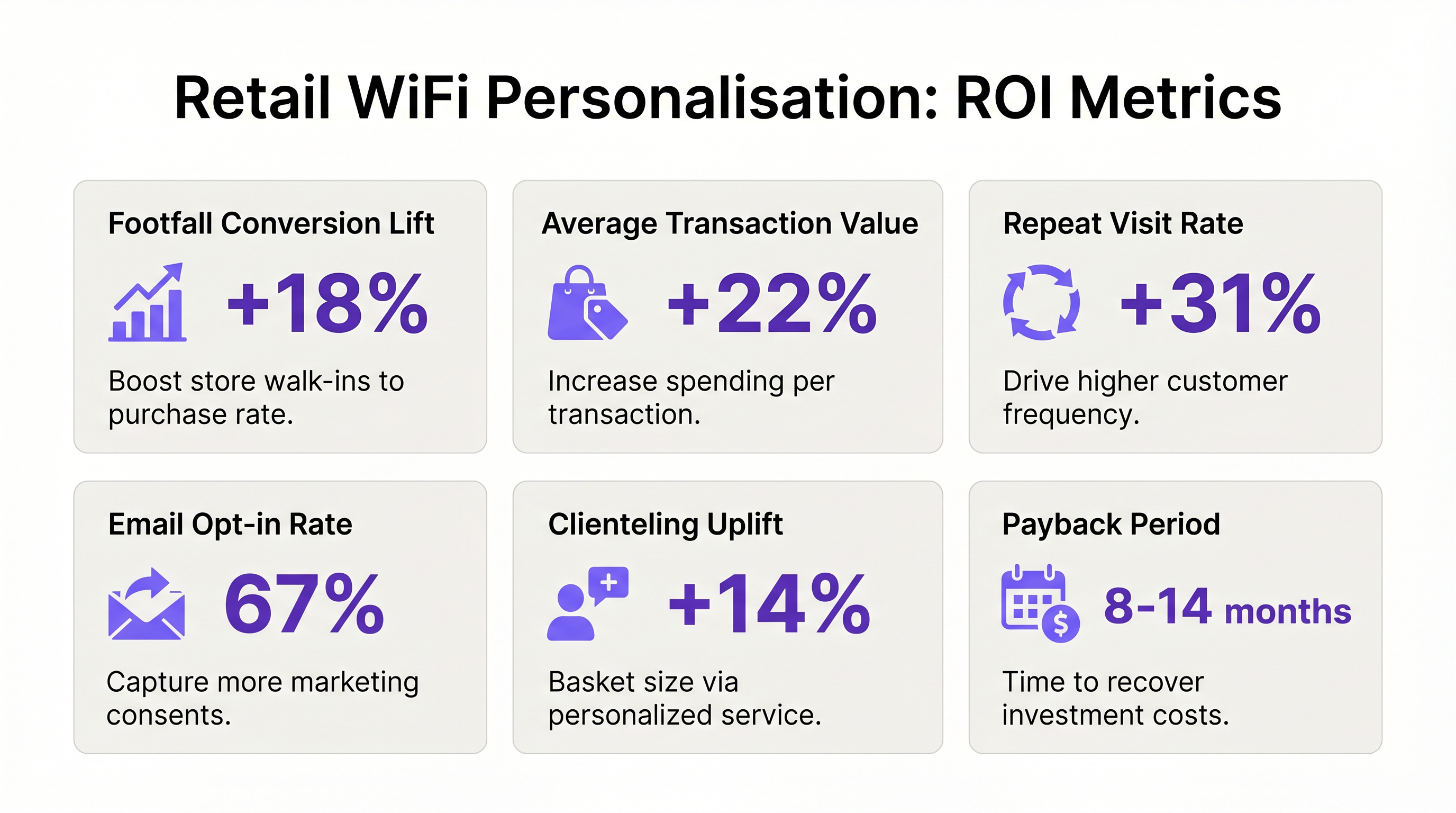
| Clienteling Uplift | ATV increase when associate uses presence data | +10-20% |
| Database Growth Rate | Net-new compliant profiles added per month | Depends on footfall volume |
| Email Opt-in Rate | % of authenticated users who consent to marketing | >60% |
The ROI Model
A standard ROI model for retail WiFi personalisation typically focuses on three primary drivers.
Increased Marketing Reach quantifies the value of net-new email and SMS opt-ins acquired via the captive portal, calculated based on the organisation's average revenue per subscriber and the incremental reach delivered to previously unknown customers.
Enhanced In-Store Conversion measures the incremental revenue generated by targeted in-store promotions — for example, a push notification sent when a customer dwells in the shoe department for more than five minutes, or a clienteling alert that enables a personalised upsell.
Operational Efficiency captures the cost savings from optimising staff scheduling based on predictive footfall analytics, ensuring peak staffing aligns with peak visitor traffic rather than just historical transaction volume.
Typical payback periods for enterprise retail WiFi personalisation deployments range from 8 to 14 months, with ongoing annual returns driven by the compounding value of the growing first-party data asset.
Key Terms & Definitions
MAC Binding
The process of associating a potentially randomised or ephemeral device MAC address with a persistent, known user identity (e.g., email address) during the captive portal authentication process.
Critical for tracking returning visitors and building unified customer profiles despite OS-level privacy features like MAC randomisation in iOS 14+ and Android 10+.
Passpoint (Hotspot 2.0)
A Wi-Fi Alliance standard that enables seamless, secure, and automatic authentication to WiFi networks without requiring user interaction or a captive portal, often utilising credentials from a mobile operator or loyalty application.
Used to create frictionless, secure connectivity for high-value returning customers, bypassing captive portal fatigue and MAC randomisation issues.
Trilateration
The process of determining absolute or relative locations of points by measurement of distances, using the geometry of circles, spheres or triangles. In WiFi, it uses signal strength (RSSI) from at least three APs to locate a device.
Essential for granular in-store location tracking, zone analysis, and heatmapping. Requires perimeter-heavy AP placement to function accurately.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before network access is granted. Typically used for authentication, payment, or accepting terms of use.
The primary digital touchpoint for customer acquisition and first-party data collection in a physical venue. Authentication rate is the key performance metric.
Probe Request
A management frame transmitted by a client device (such as a smartphone) to discover available 802.11 networks in its proximity, broadcast on all channels.
The foundation of passive footfall analytics, allowing venues to count and track devices even if they do not connect to the network. Accuracy is impacted by MAC randomisation.
Clienteling
A retail technique used by sales associates to establish long-term relationships with key customers based on data about their preferences, behaviours, and purchase history.
WiFi presence data acts as the real-time trigger for clienteling applications, alerting staff when a specific customer enters the store and surfacing relevant profile data.
WIDS/WIPS
Wireless Intrusion Detection System / Wireless Intrusion Prevention System. Security infrastructure that monitors the radio spectrum for unauthorised access points (rogue APs) and wireless attacks.
Crucial for maintaining PCI DSS compliance and protecting the integrity of the guest network against evil twin attacks and credential harvesting.
Webhook
An HTTP-based callback mechanism that allows one application to send real-time data to another application as soon as a specified event occurs, rather than requiring the receiving application to poll for updates.
The primary mechanism for pushing real-time WiFi presence events (e.g., 'User X entered Zone Y') to a CRM or clienteling system. Must include retry logic and error handling for production deployments.
Capture Rate
The ratio of people who enter a venue to the total number of people who pass by the venue exterior, expressed as a percentage.
A key retail performance metric that can be measured using WiFi passive scanning data at the perimeter versus interior of a venue.
Case Studies
A national fashion retail chain with 500 locations wants to implement real-time clienteling. When a 'VIP' loyalty member enters a store, the store manager's tablet must receive an alert with the customer's purchase history within 30 seconds. How should the network and integration architecture be designed?
- Authentication: Implement Passpoint (Hotspot 2.0) tied to the retailer's loyalty app. This ensures the VIP's device connects automatically and securely without a captive portal prompt upon entering the store, eliminating friction for the highest-value customers. 2. Edge Processing: The local AP or Controller detects the association event and forwards the payload (MAC address + Location Zone) to the central WiFi Analytics platform via a local MQTT broker or direct API call. 3. Identity Resolution: The Analytics platform resolves the MAC address to the persistent Customer ID via its internal binding database, established during the customer's initial loyalty app registration. 4. Webhook Integration: The Analytics platform fires a real-time webhook payload (containing Customer ID, Store ID, and Zone) to the central CRM/CDP. The webhook endpoint must respond within 200ms to avoid timeout failures. 5. Clienteling App Routing: The CRM identifies the VIP status, retrieves the last 10 purchase records and stated preferences, and pushes an immediate push notification to the specific store manager's tablet application via a dedicated API channel. Total end-to-end latency target: under 15 seconds.
A large conference centre is experiencing a high volume of 'walk-by' traffic detected by passive scanning, but a very low authentication rate (under 8%) on their captive portal. The marketing team needs to increase the first-party database size by 40% within six months. What technical and strategic steps should the IT team take?
- RF Audit: Conduct an active survey to ensure the guest network signal strength is sufficient outside the venue perimeter to trigger the native OS Captive Portal Assistant (CPA) on iOS and Android devices immediately upon association. A signal below -75 dBm at the entrance will prevent the CPA from triggering reliably. 2. Portal Optimisation: Reduce the captive portal form from its current 5 fields (Name, Email, Phone, Postcode, DOB) to 2 fields (Name, Email) or implement one-click Social Login (Google/Apple). Each removed field is estimated to increase conversion by 10-15%. 3. Value Exchange Implementation: Work with marketing to rebrand the SSID from 'VenueGuest_WiFi' to a benefit-led name. Configure the captive portal to immediately deliver a digital discount code or exclusive content upon successful authentication. 4. Signage and Awareness: Deploy physical QR code signage at all high-traffic entry points linking directly to the captive portal URL, bypassing the CPA dependency entirely for users on cellular. 5. Measurement: Implement A/B testing on portal variants to continuously optimise conversion rates, tracking authentication rate as the primary KPI.
Scenario Analysis
Q1. A retail client wants to trigger a personalised digital signage advertisement when a specific demographic (loyalty members aged 25-34) dwells in the 'New Arrivals' zone for more than 2 minutes. What is the most critical integration point required to achieve this, and what data must flow between systems?
💡 Hint:Consider where the demographic data lives versus where the location and dwell time data is generated.
Show Recommended Approach
The critical integration point is a real-time, bi-directional API link between the WiFi Analytics platform (which holds the location and dwell time data) and the CRM/CDP (which holds the demographic and loyalty tier data). The WiFi platform must fire a webhook upon the 2-minute dwell threshold being reached in the 'New Arrivals' zone, containing the Customer ID and zone name. The CRM must instantly evaluate the user's demographic profile and loyalty status. If the criteria are met, the CRM (or a connected CMS) must push the specific content variant to the digital signage controller for that zone. The entire chain must complete within 10-15 seconds to be contextually relevant.
Q2. You are reviewing the RF design for a new 2,000 sq metre flagship retail store. The primary goal is highly accurate location tracking for heatmapping and zone dwell time analysis. The initial design shows 8 APs placed in two straight lines down the centre of the store to maximise coverage with the fewest APs. What is your recommendation, and why?
💡 Hint:Review the mathematical principles of trilateration and what AP geometry is required.
Show Recommended Approach
The design must be rejected and reworked. A straight-line 'hallway' deployment provides coverage but makes accurate trilateration impossible, as any device on the floor can only be measured linearly — the geometry does not allow for accurate 2D positioning. The design must be changed to a perimeter-heavy layout, with APs positioned along the walls and corners of the store. This ensures that any device on the floor is within the optimal listening range of at least three non-collinear APs, providing the angular diversity required for accurate trilateration. The total AP count may need to increase to achieve both coverage and location accuracy simultaneously.
Q3. Following a recent iOS update that aggressively randomises MAC addresses even while connected to a network, a client reports that their 'Repeat Visitor' metric has dropped by 60% in the analytics dashboard, even though overall footfall appears steady. How do you diagnose and resolve this?
💡 Hint:How do we move away from relying on hardware identifiers as the primary key for identity?
Show Recommended Approach
The root cause is clear: the analytics platform is using the device MAC address as the primary identifier for unique and repeat visitor tracking. With persistent MAC randomisation now active, each visit by the same device appears as a new, unique visitor. The solution is to shift to Profile-Based Authentication as the primary identity mechanism. Configure the network to utilise Passpoint (Hotspot 2.0) or an app-based SDK, where the device authenticates via a secure certificate or profile tied to their user account, rather than relying on the hardware MAC address. For authenticated users, the repeat visit metric should be recalculated based on the persistent Customer ID rather than the MAC address. Passive (unauthenticated) footfall metrics will remain impacted and should be treated as directional trend data only.
Key Takeaways
- ✓Retail WiFi must transition from a cost-centre utility to a revenue-generating sensor and identity management layer.
- ✓Accurate personalisation requires integrating physical presence data with persistent CRM profiles via MAC binding at the captive portal.
- ✓Frictionless onboarding and a clear value exchange are the primary drivers of high authentication rates — this is a UX and marketing problem, not a network problem.
- ✓Real-time webhooks enable immediate in-store actions, including staff clienteling alerts, targeted push notifications, and dynamic digital signage.
- ✓RF design for location analytics requires perimeter-heavy AP placement to enable accurate trilateration — central-aisle deployments are insufficient.
- ✓Profile-based authentication (Passpoint) is the correct long-term solution to MAC randomisation for returning customers.
- ✓Typical payback periods for enterprise retail WiFi personalisation deployments range from 8 to 14 months, with compounding returns from the growing first-party data asset.



