WiFi para invitados en hospitales: Experiencia del paciente y separación de la red
Esta guía autorizada detalla cómo los equipos de TI de hospitales pueden diseñar una red WiFi para invitados segura y de alto rendimiento que aísle estrictamente el tráfico de pacientes de las redes clínicas. Cubre la segmentación de VLAN, la planificación del ancho de banda, los protocolos de autenticación y el impacto directo del WiFi en las métricas de satisfacción del paciente.
🎧 Escuchar esta guía
Ver transcripción

Resumen Ejecutivo
El WiFi para invitados en hospitales es fundamentalmente diferente de las implementaciones en hostelería o comercio minorista. Mientras que una mala conexión en un hotel resulta en un huésped frustrado, una red hospitalaria mal configurada puede tender un puente entre el smartphone comprometido de un visitante y la infraestructura clínica crítica, como las plataformas EHR o las bombas de infusión.
Para los CIO de hospitales, los gerentes de TI clínicos y los arquitectos de red, el mandato es doble: ofrecer una experiencia de conectividad de nivel de consumidor que satisfaga las expectativas del paciente (y aumente las puntuaciones HCAHPS), al tiempo que se aplica un aislamiento de grado militar entre el dominio de difusión de invitados y la red clínica.
Esta guía proporciona prácticas de ingeniería accionables y neutrales respecto al proveedor para diseñar WiFi para invitados en hospitales. Examinaremos las estrategias de segmentación de Capa 2, la planificación de canales de RF en entornos clínicos densos, los protocolos de autenticación modernos (802.1X vs WPA3-SAE) y cómo medir el ROI de la conectividad del paciente.
Análisis Técnico Detallado: Diseño de la Separación de Red
La regla fundamental del diseño de redes sanitarias es el aislamiento absoluto: el tráfico clínico y el tráfico de invitados nunca deben compartir un dominio de difusión de Capa 2. Este principio se alinea con las salvaguardas técnicas de HIPAA y el NHS Data Security and Protection Toolkit.
Segmentación de VLAN y el Modelo de Tres Capas
El enfoque estándar para el aislamiento es la segmentación de VLAN a través de las capas de núcleo, distribución y acceso. Se asigna una VLAN dedicada (por ejemplo, VLAN 10) a los sistemas clínicos, mientras que una VLAN separada (por ejemplo, VLAN 20) transporta todo el tráfico de invitados. Estas VLAN se interconectan a través de la infraestructura de conmutación y terminan en un firewall de próxima generación (NGFW), donde el enrutamiento entre VLAN se bloquea explícitamente o se controla estrictamente mediante reglas de inspección de estado.
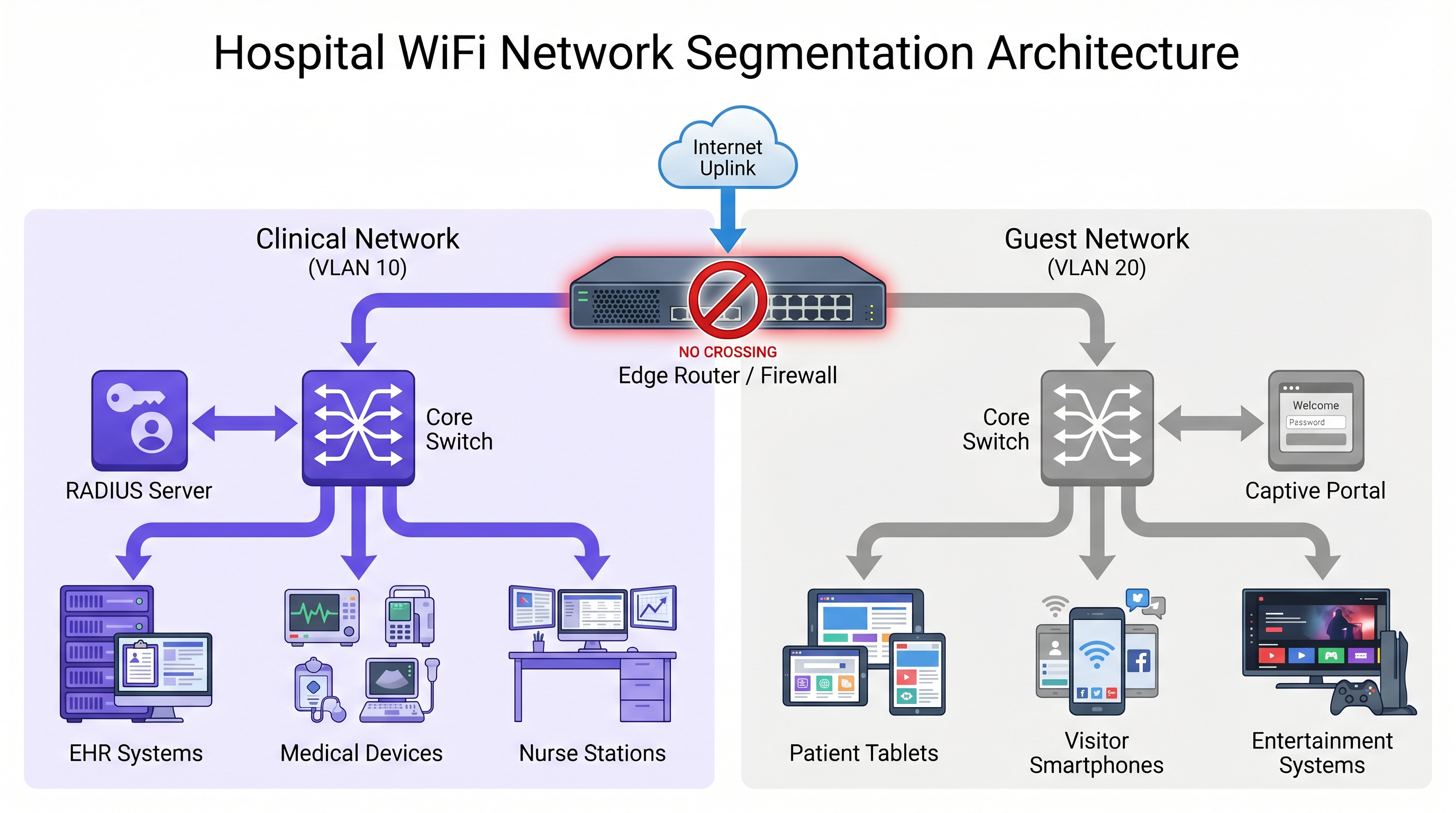
Sin embargo, depender únicamente de las VLAN a nivel de conmutador es insuficiente. La aplicación debe ocurrir en el borde:
- Puntos de Acceso con Doble SSID: Si los APs emiten SSIDs tanto clínicos como de invitados, el controlador de LAN inalámbrica (WLC) debe mapearlos a VLANs separadas con un aislamiento estricto.
- Aislamiento de AP / Aislamiento de Cliente: Esta característica debe estar habilitada por defecto en el SSID de invitados. Evita la comunicación cliente a cliente en la misma VLAN, asegurando que el dispositivo de un paciente no pueda sondear o atacar el dispositivo de otro paciente.
- Microsegmentación: Para dispositivos IoT médicos heredados que no pueden soportar la autenticación moderna, las políticas de control de acceso a la red (NAC) deben restringir su comunicación estrictamente a los servidores clínicos específicos que requieren, limitando el radio de impacto de un posible compromiso.
Estándares de Autenticación y Cifrado
Los modelos de autenticación deben divergir según el propósito de la red:
Red Clínica: Requiere autenticación IEEE 802.1X utilizando EAP-TLS (basado en certificados) o PEAP-MSCHAPv2 (basado en credenciales), respaldado por un servidor RADIUS. Las Claves Precompartidas (PSKs) nunca deben usarse en redes clínicas, ya que una única PSK comprometida expone todo el SSID.
Red de Invitados: El flujo de autenticación debe priorizar la accesibilidad para pacientes con diferentes niveles de conocimientos técnicos. Un Captive Portal con verificación por SMS o aceptación con un solo clic es ideal. Para asegurar el tráfico inalámbrico sin una gestión compleja de credenciales, implemente WPA3-SAE (Simultaneous Authentication of Equals). WPA3-SAE utiliza un intercambio de prueba de conocimiento cero, protegiendo contra ataques de diccionario fuera de línea incluso si se intercepta el handshake.
Diseño de RF y Planificación de Capacidad
Los entornos hospitalarios son hostiles a la RF, con paredes gruesas de hormigón, salas de radiología revestidas de plomo e interferencias significativas de equipos médicos.
La planificación del ancho de banda requiere cálculos realistas por cama. Una habitación de paciente moderna puede contener un smartphone, una tablet y un televisor inteligente. La transmisión de video HD requiere 5 Mbps, mientras que 4K requiere 25 Mbps. Las videollamadas a través de FaceTime o Teams demandan 1-3 Mbps simétricos.
Regla General: Planifique un mínimo de 25 Mbps de rendimiento disponible por cama. En una instalación de 200 camas con un 60% de uso concurrente en horas pico, la demanda agregada de invitados puede superar fácilmente los 3 Gbps.
Para la densidad de AP, implemente un punto de acceso por bahía de sala (por ejemplo, cada 4-6 camas) en lugar de uno por sala. Configure la banda de 5 GHz para dispositivos de invitados sensibles al rendimiento, reservando 2.4 GHz para IoT heredados y teléfonos clínicos más antiguos. La potencia de transmisión debe ajustarse de forma conservadora para permitir una superposición de celdas del 15-20%; la sobrepotencia de los APs causa interferencia cocanal y degrada el rendimiento general.
Guía de Implementación: Mejores Prácticas de Despliegue
La implementación de WiFi para invitados en hospitales requiere pruebas y validación rigurosas para garantizar el mantenimiento de la seguridad clínica.
- Realice Estudios de Sitio Predictivos y Activos: Nunca implemente sin un modelo predictivo, y siempre valide con un estudio activo después de la instalación. Mapee la cobertura a un objetivo de -65 dBm RSSI con una Relación Señal/Ruido (SNR) de al menos 25 dB.
- Implemente la Gestión del Ancho de Banda: Sin Calidad de Servicio (QoS) y limitación de velocidad, un solo usuario realizando descargas masivas puede saturar el enlace ascendente. Aplique límites de velocidad por cliente (por ejemplo, 5-10 Mbps de bajada) y utilice el marcado DSCP para priorizar el tráfico en tiempo real como VoIP y videollamadas sobre los datos masivos.
- Implemente un Captive Portal Robusto: El portal es la puerta de entrada digital. Debe ser adaptable a móviles, de carga rápida y cumplir con los estándares de accesibilidad. La integración con una plataforma como [Guest WiFi](/prod de Purpleucts/guest-wifi) garantiza una experiencia de marca al tiempo que captura valiosos análisis de uso.
- Pruebas de penetración obligatorias: Antes de la puesta en marcha, realice una prueba de enrutamiento inter-VLAN. Intente hacer ping o acceder a las subredes clínicas desde un dispositivo autenticado en la red de invitados. Cualquier conexión exitosa es una condición de fallo inmediato.
ROI e impacto empresarial
La satisfacción del paciente está directamente ligada a la financiación y reputación del hospital. En EE. UU., las puntuaciones HCAHPS (Hospital Consumer Assessment of Healthcare Providers and Systems) afectan a los reembolsos de Medicare. En el Reino Unido, el NHS Friends and Family Test cumple una función similar. Los pacientes ven cada vez más la WiFi fiable no como un lujo, sino como un servicio básico esencial para mantener el contacto con sus seres queridos y gestionar sus asuntos personales durante la recuperación.
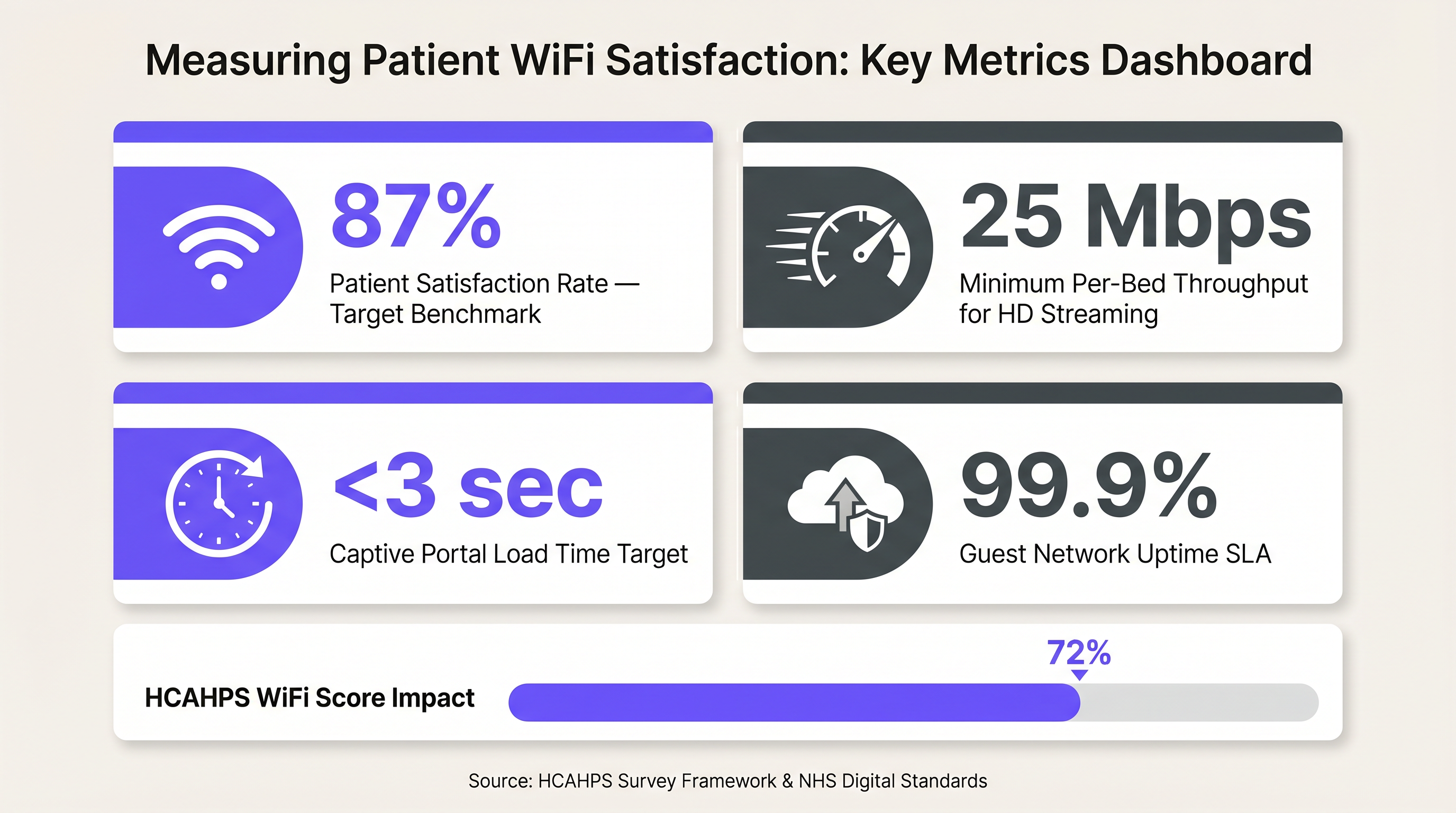
Más allá de la satisfacción, una red de invitados correctamente implementada proporciona datos procesables. La utilización de WiFi Analytics permite a los equipos de operaciones comprender los tiempos de permanencia, el flujo de visitantes y las horas pico de uso, lo que informa directamente la planificación de la capacidad y los modelos de personal. Cuando se combina con soluciones de Wayfinding , la red se transforma de un centro de costes en un activo estratégico que reduce las citas perdidas y mejora la experiencia general del visitante.
Términos clave y definiciones
VLAN Segmentation
The practice of dividing a single physical network into multiple distinct logical networks to isolate traffic.
Essential in hospitals to ensure a compromised guest device cannot access sensitive clinical systems.
AP Isolation (Client Isolation)
A wireless network setting that prevents devices connected to the same access point from communicating directly with each other.
Prevents malicious actors on the guest network from scanning or attacking other patients' devices.
IEEE 802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The mandatory authentication standard for clinical devices, replacing vulnerable Pre-Shared Keys (PSKs).
WPA3-SAE
Simultaneous Authentication of Equals, a secure key establishment protocol used in WPA3 that protects against offline dictionary attacks.
Provides robust over-the-air encryption for guest networks without requiring complex per-user credentials.
HCAHPS
Hospital Consumer Assessment of Healthcare Providers and Systems, a standardized survey of patients' perspectives of hospital care.
In the US, WiFi quality often influences the 'hospital environment' scores, which can impact Medicare reimbursements.
Micro-segmentation
A security technique that enables fine-grained security policies assigned to data center applications, down to the workload level.
Used to secure legacy medical IoT devices by restricting their network access only to necessary clinical servers.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
The primary interface for hospital guests, used to accept terms of service, verify identity, and collect analytics.
Layer 2 Broadcast Domain
A logical division of a computer network in which all nodes can reach each other by broadcast at the data link layer.
Clinical and guest traffic must never share the same broadcast domain to prevent lateral movement of threats.
Casos de éxito
A 400-bed acute care hospital is experiencing severe guest network congestion every evening between 6 PM and 9 PM. The network uses a single 1 Gbps internet uplink shared between clinical management traffic and guest access. Patients are complaining of dropped video calls, negatively impacting HCAHPS scores.
The IT team must implement a multi-layered bandwidth management strategy. First, deploy traffic shaping at the firewall to guarantee a minimum of 200 Mbps for clinical management traffic, preventing guest usage from starving critical systems. Second, implement per-client rate limiting on the WLC, capping guest devices at 8 Mbps download/2 Mbps upload. Finally, apply Application Visibility and Control (AVC) to block peer-to-peer file sharing and throttle streaming video to standard definition (SD) resolutions during peak hours.
A private clinic group is acquiring a legacy facility. The existing network infrastructure uses older access switches that do not support 802.1Q VLAN trunking reliably. The CIO wants to deploy a unified guest WiFi portal across all sites within 30 days, but the clinical network cannot be compromised.
Due to the hardware limitations preventing secure logical separation (VLANs), the team must implement physical separation. They should deploy a parallel, cloud-managed wireless infrastructure exclusively for guest access. This involves installing new APs cabled to dedicated, low-cost PoE switches that connect directly to a separate internet circuit, completely bypassing the legacy clinical LAN. The new APs will integrate with the group's centralized captive portal platform.
Análisis de escenarios
Q1. A vendor proposes installing a new fleet of smart infusion pumps. The pumps only support WPA2-Personal (Pre-Shared Key) and cannot utilize 802.1X certificates. How should the network architect integrate these devices securely?
💡 Sugerencia:Consider how to limit the blast radius if the PSK is compromised.
Mostrar enfoque recomendado
The architect must place the infusion pumps on a dedicated IoT VLAN, separate from both the main clinical workstation VLAN and the guest VLAN. Micro-segmentation or strict ACLs at the firewall should be applied so these pumps can only communicate with their specific management server, blocking all other lateral network access.
Q2. During a post-deployment audit, a security analyst connects a laptop to the 'Hospital_Guest' SSID and successfully pings the IP address of a nurse station thin client. What is the most likely configuration error?
💡 Sugerencia:Think about where traffic boundaries are enforced between logical networks.
Mostrar enfoque recomendado
The most likely error is a failure at the routing or firewall layer. While the VLANs may be defined on the switches, the inter-VLAN routing rules on the core router or firewall are either missing or overly permissive, allowing traffic to traverse from the guest subnet to the clinical subnet.
Q3. The hospital executive board wants to implement a complex, multi-page registration form on the guest WiFi captive portal to gather detailed demographic data for marketing. As the IT manager, what is your primary concern with this approach?
💡 Sugerencia:Consider the user demographic and the primary goal of patient connectivity.
Mostrar enfoque recomendado
The primary concern is user friction leading to a drop in patient satisfaction. Hospital patients may be elderly, distressed, or technically inexperienced. A complex portal will result in connection failures, increased IT helpdesk tickets, and lower HCAHPS/Friends and Family Test scores. The portal should prioritize a simple, one-click or SMS-verified login.
Conclusiones clave
- ✓Clinical and guest traffic must be strictly isolated into separate VLANs with no Layer 2 bridging.
- ✓Relying solely on switch VLANs is insufficient; enforce separation at the AP, WLC, and Firewall.
- ✓Use 802.1X for clinical authentication; use WPA3-SAE and simple captive portals for guests.
- ✓Plan for a minimum of 25 Mbps throughput per bed to support modern streaming and video calling.
- ✓Always perform inter-VLAN penetration testing before approving a network for go-live.
- ✓Reliable guest WiFi directly impacts hospital funding metrics like HCAHPS and Friends and Family Test scores.



