Hospital Guest WiFi: Patient Experience and Network Separation
This authoritative guide details how hospital IT teams can architect secure, high-performance guest WiFi that strictly isolates patient traffic from clinical networks. It covers VLAN segmentation, bandwidth planning, authentication protocols, and the direct impact of WiFi on patient satisfaction metrics.
🎧 Listen to this Guide
View Transcript

Executive Summary
Hospital guest WiFi is fundamentally different from hospitality or retail deployments. Whilst a poor connection in a hotel results in a frustrated guest, a misconfigured hospital network can bridge the gap between a visitor's compromised smartphone and critical clinical infrastructure like EHR platforms or infusion pumps.
For hospital CIOs, clinical IT managers, and network architects, the mandate is twofold: deliver a consumer-grade connectivity experience that meets patient expectations (and boosts HCAHPS scores), whilst enforcing military-grade isolation between the guest broadcast domain and the clinical network.
This guide provides actionable, vendor-neutral engineering practices for designing hospital guest WiFi. We will examine Layer 2 segmentation strategies, RF channel planning in dense clinical environments, modern authentication protocols (802.1X vs WPA3-SAE), and how to measure the ROI of patient connectivity.
Technical Deep-Dive: Designing Network Separation
The foundational rule of healthcare network design is absolute isolation: clinical traffic and guest traffic must never share a Layer 2 broadcast domain. This principle aligns with HIPAA technical safeguards and the NHS Data Security and Protection Toolkit.
VLAN Segmentation and the Three-Tier Model
The standard approach to isolation is VLAN segmentation across the core, distribution, and access layers. A dedicated VLAN (e.g., VLAN 10) is assigned to clinical systems, whilst a separate VLAN (e.g., VLAN 20) carries all guest traffic. These VLANs are trunked across the switching infrastructure and terminated at a next-generation firewall (NGFW), where inter-VLAN routing is either explicitly blocked or tightly controlled via stateful inspection rules.
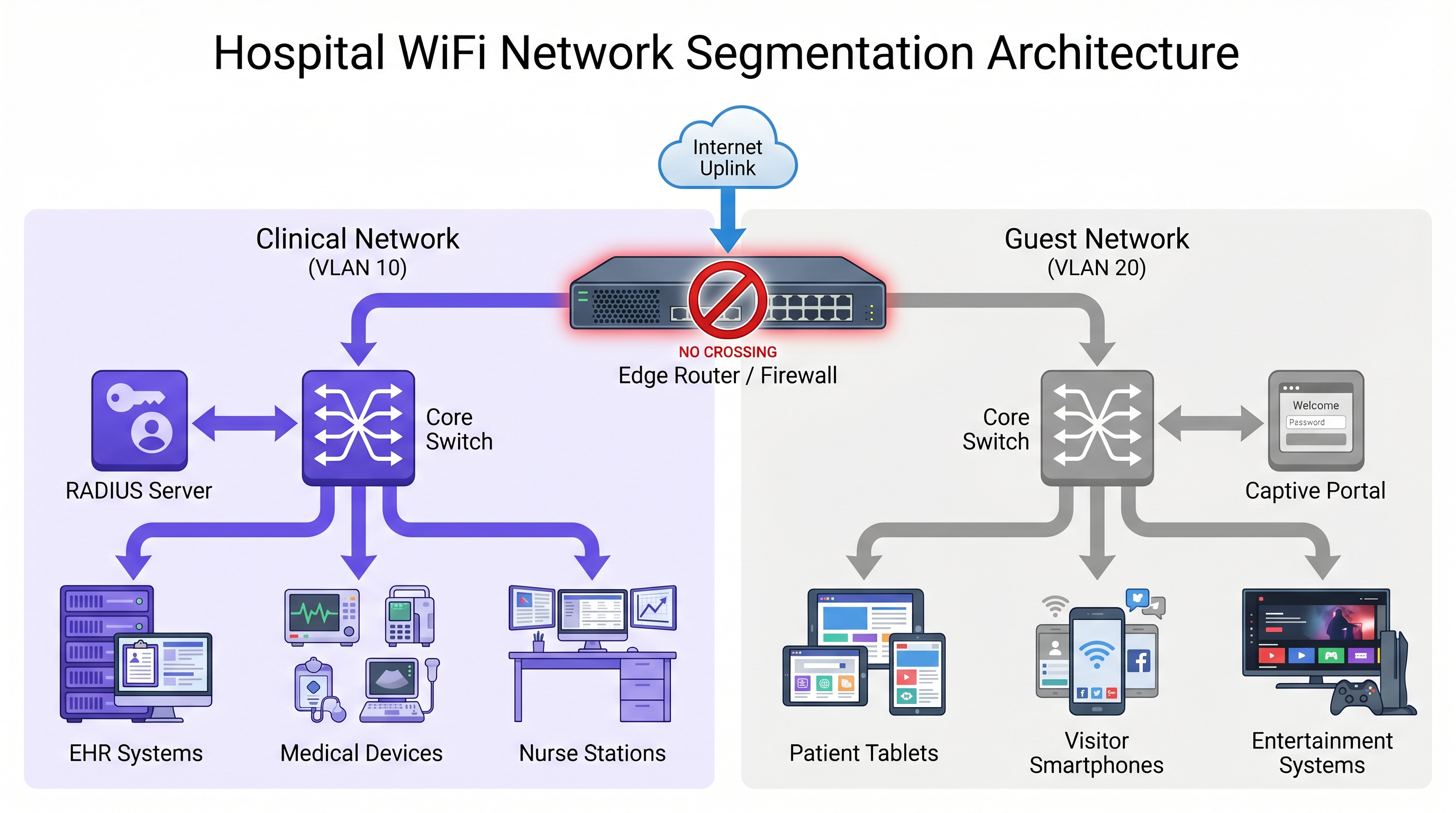
However, relying solely on switch-level VLANs is insufficient. Enforcement must occur at the edge:
- Dual-SSID Access Points: If APs broadcast both clinical and guest SSIDs, the wireless LAN controller (WLC) must map these to separate VLANs with strict isolation.
- AP Isolation / Client Isolation: This feature must be enabled by default on the guest SSID. It prevents client-to-client communication on the same VLAN, ensuring a patient's device cannot probe or attack another patient's device.
- Micro-segmentation: For legacy medical IoT devices that cannot support modern authentication, network access control (NAC) policies should restrict their communication strictly to the specific clinical servers they require, limiting the blast radius of a potential compromise.
Authentication and Encryption Standards
Authentication models must diverge based on the network's purpose:
Clinical Network: Require IEEE 802.1X authentication using EAP-TLS (certificate-based) or PEAP-MSCHAPv2 (credential-based), backed by a RADIUS server. Pre-Shared Keys (PSKs) must never be used on clinical networks, as a single compromised PSK exposes the entire SSID.
Guest Network: The authentication flow must prioritise accessibility for patients of varying technical proficiencies. A captive portal with SMS verification or one-click acceptance is ideal. To secure over-the-air traffic without complex credential management, deploy WPA3-SAE (Simultaneous Authentication of Equals). WPA3-SAE uses a zero-knowledge proof exchange, protecting against offline dictionary attacks even if the handshake is intercepted.
RF Design and Capacity Planning
Hospital environments are RF-hostile, featuring thick concrete walls, lead-lined radiology rooms, and significant interference from medical equipment.
Bandwidth planning requires realistic per-bed calculations. A modern patient room may contain a smartphone, a tablet, and a smart TV. Streaming HD video requires 5 Mbps, whilst 4K requires 25 Mbps. Video calling via FaceTime or Teams demands 1-3 Mbps symmetrical.
Rule of Thumb: Plan for a minimum of 25 Mbps of available throughput per bed. In a 200-bed facility with 60% concurrent usage at peak hours, aggregate guest demand can easily exceed 3 Gbps.
For AP density, deploy one access point per ward bay (e.g., every 4-6 beds) rather than one per ward. Configure the 5 GHz band for throughput-sensitive guest devices, reserving 2.4 GHz for legacy IoT and older clinical handsets. Transmit power should be tuned conservatively to allow 15-20% cell overlap; overpowering APs causes co-channel interference and degrades overall throughput.
Implementation Guide: Deployment Best Practices
Deploying hospital guest WiFi requires rigorous testing and validation to ensure clinical safety is maintained.
- Conduct Predictive and Active Site Surveys: Never deploy without a predictive model, and always validate with an active survey post-installation. Map coverage to a target of -65 dBm RSSI with a Signal-to-Noise Ratio (SNR) of at least 25 dB.
- Implement Bandwidth Management: Without Quality of Service (QoS) and rate limiting, a single user running bulk downloads can saturate the uplink. Enforce per-client rate limits (e.g., 5-10 Mbps down) and use DSCP marking to prioritise real-time traffic like VoIP and video calls over bulk data.
- Deploy a Robust Captive Portal: The portal is the digital front door. It must be mobile-responsive, fast-loading, and compliant with accessibility standards. Integrating with a platform like Purple's Guest WiFi ensures a branded experience while capturing valuable usage analytics.
- Mandatory Penetration Testing: Before go-live, conduct an inter-VLAN routing test. Attempt to ping or reach clinical subnets from a device authenticated on the guest network. Any successful connection is an immediate failure condition.
ROI & Business Impact
Patient satisfaction is directly tied to hospital funding and reputation. In the US, HCAHPS (Hospital Consumer Assessment of Healthcare Providers and Systems) scores impact Medicare reimbursements. In the UK, the NHS Friends and Family Test serves a similar function. Patients increasingly view reliable WiFi not as a luxury, but as a basic utility essential for maintaining contact with loved ones and managing their personal affairs during recovery.
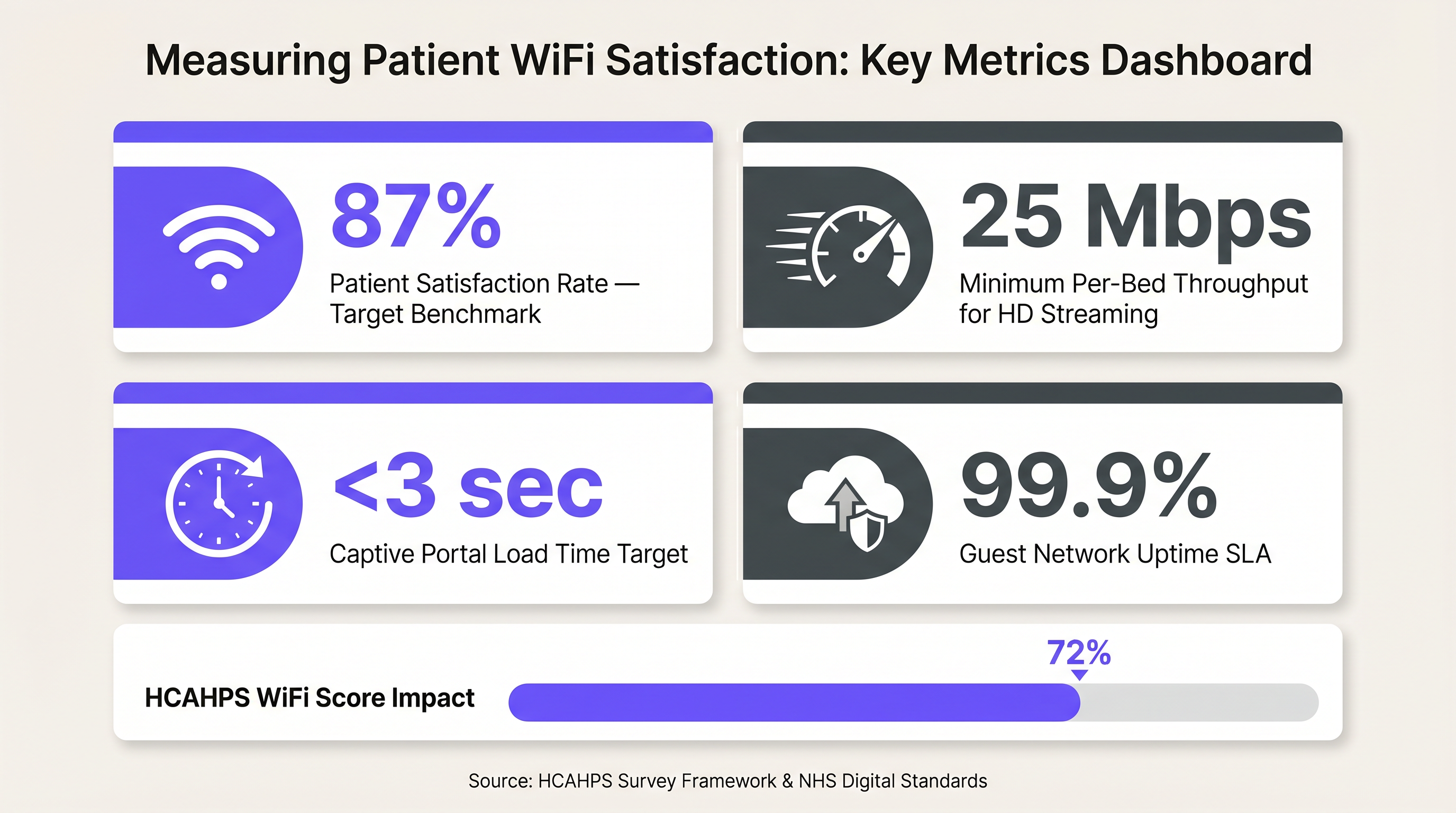
Beyond satisfaction, a properly implemented guest network provides actionable data. Utilising WiFi Analytics allows operations teams to understand dwell times, visitor flow, and peak usage hours, directly informing capacity planning and staffing models. When paired with Wayfinding solutions, the network transforms from a cost centre into a strategic asset that reduces missed appointments and improves the overall visitor experience.
Key Terms & Definitions
VLAN Segmentation
The practice of dividing a single physical network into multiple distinct logical networks to isolate traffic.
Essential in hospitals to ensure a compromised guest device cannot access sensitive clinical systems.
AP Isolation (Client Isolation)
A wireless network setting that prevents devices connected to the same access point from communicating directly with each other.
Prevents malicious actors on the guest network from scanning or attacking other patients' devices.
IEEE 802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The mandatory authentication standard for clinical devices, replacing vulnerable Pre-Shared Keys (PSKs).
WPA3-SAE
Simultaneous Authentication of Equals, a secure key establishment protocol used in WPA3 that protects against offline dictionary attacks.
Provides robust over-the-air encryption for guest networks without requiring complex per-user credentials.
HCAHPS
Hospital Consumer Assessment of Healthcare Providers and Systems, a standardized survey of patients' perspectives of hospital care.
In the US, WiFi quality often influences the 'hospital environment' scores, which can impact Medicare reimbursements.
Micro-segmentation
A security technique that enables fine-grained security policies assigned to data center applications, down to the workload level.
Used to secure legacy medical IoT devices by restricting their network access only to necessary clinical servers.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
The primary interface for hospital guests, used to accept terms of service, verify identity, and collect analytics.
Layer 2 Broadcast Domain
A logical division of a computer network in which all nodes can reach each other by broadcast at the data link layer.
Clinical and guest traffic must never share the same broadcast domain to prevent lateral movement of threats.
Case Studies
A 400-bed acute care hospital is experiencing severe guest network congestion every evening between 6 PM and 9 PM. The network uses a single 1 Gbps internet uplink shared between clinical management traffic and guest access. Patients are complaining of dropped video calls, negatively impacting HCAHPS scores.
The IT team must implement a multi-layered bandwidth management strategy. First, deploy traffic shaping at the firewall to guarantee a minimum of 200 Mbps for clinical management traffic, preventing guest usage from starving critical systems. Second, implement per-client rate limiting on the WLC, capping guest devices at 8 Mbps download/2 Mbps upload. Finally, apply Application Visibility and Control (AVC) to block peer-to-peer file sharing and throttle streaming video to standard definition (SD) resolutions during peak hours.
A private clinic group is acquiring a legacy facility. The existing network infrastructure uses older access switches that do not support 802.1Q VLAN trunking reliably. The CIO wants to deploy a unified guest WiFi portal across all sites within 30 days, but the clinical network cannot be compromised.
Due to the hardware limitations preventing secure logical separation (VLANs), the team must implement physical separation. They should deploy a parallel, cloud-managed wireless infrastructure exclusively for guest access. This involves installing new APs cabled to dedicated, low-cost PoE switches that connect directly to a separate internet circuit, completely bypassing the legacy clinical LAN. The new APs will integrate with the group's centralized captive portal platform.
Scenario Analysis
Q1. A vendor proposes installing a new fleet of smart infusion pumps. The pumps only support WPA2-Personal (Pre-Shared Key) and cannot utilize 802.1X certificates. How should the network architect integrate these devices securely?
💡 Hint:Consider how to limit the blast radius if the PSK is compromised.
Show Recommended Approach
The architect must place the infusion pumps on a dedicated IoT VLAN, separate from both the main clinical workstation VLAN and the guest VLAN. Micro-segmentation or strict ACLs at the firewall should be applied so these pumps can only communicate with their specific management server, blocking all other lateral network access.
Q2. During a post-deployment audit, a security analyst connects a laptop to the 'Hospital_Guest' SSID and successfully pings the IP address of a nurse station thin client. What is the most likely configuration error?
💡 Hint:Think about where traffic boundaries are enforced between logical networks.
Show Recommended Approach
The most likely error is a failure at the routing or firewall layer. While the VLANs may be defined on the switches, the inter-VLAN routing rules on the core router or firewall are either missing or overly permissive, allowing traffic to traverse from the guest subnet to the clinical subnet.
Q3. The hospital executive board wants to implement a complex, multi-page registration form on the guest WiFi captive portal to gather detailed demographic data for marketing. As the IT manager, what is your primary concern with this approach?
💡 Hint:Consider the user demographic and the primary goal of patient connectivity.
Show Recommended Approach
The primary concern is user friction leading to a drop in patient satisfaction. Hospital patients may be elderly, distressed, or technically inexperienced. A complex portal will result in connection failures, increased IT helpdesk tickets, and lower HCAHPS/Friends and Family Test scores. The portal should prioritize a simple, one-click or SMS-verified login.
Key Takeaways
- ✓Clinical and guest traffic must be strictly isolated into separate VLANs with no Layer 2 bridging.
- ✓Relying solely on switch VLANs is insufficient; enforce separation at the AP, WLC, and Firewall.
- ✓Use 802.1X for clinical authentication; use WPA3-SAE and simple captive portals for guests.
- ✓Plan for a minimum of 25 Mbps throughput per bed to support modern streaming and video calling.
- ✓Always perform inter-VLAN penetration testing before approving a network for go-live.
- ✓Reliable guest WiFi directly impacts hospital funding metrics like HCAHPS and Friends and Family Test scores.



