Gast-WiFi im Krankenhaus: Patientenerfahrung und Netzwerktrennung
Dieser maßgebliche Leitfaden beschreibt, wie IT-Teams in Krankenhäusern sicheres, leistungsstarkes Gast-WiFi aufbauen können, das den Patientenverkehr streng von klinischen Netzwerken isoliert. Er behandelt VLAN-Segmentierung, Bandbreitenplanung, Authentifizierungsprotokolle und den direkten Einfluss von WiFi auf die Patientenzufriedenheit.
🎧 Diesen Leitfaden anhören
Transkript anzeigen
- Zusammenfassung für Führungskräfte
- Technischer Deep-Dive: Architektur der Netzwerktrennung
- VLAN-Segmentierung und das Drei-Schichten-Modell
- Authentifizierungs- und Verschlüsselungsstandards
- RF-Design und Kapazitätsplanung
- Implementierungsleitfaden: Best Practices für die Bereitstellung
- ROI & Geschäftlicher Nutzen

Zusammenfassung für Führungskräfte
Gast-WiFi im Krankenhaus unterscheidet sich grundlegend von Installationen im Gastgewerbe oder Einzelhandel. Während eine schlechte Verbindung in einem Hotel zu einem frustrierten Gast führt, kann ein falsch konfiguriertes Krankenhausnetzwerk die Lücke zwischen dem kompromittierten Smartphone eines Besuchers und kritischer klinischer Infrastruktur wie EHR-Plattformen oder Infusionspumpen schließen.
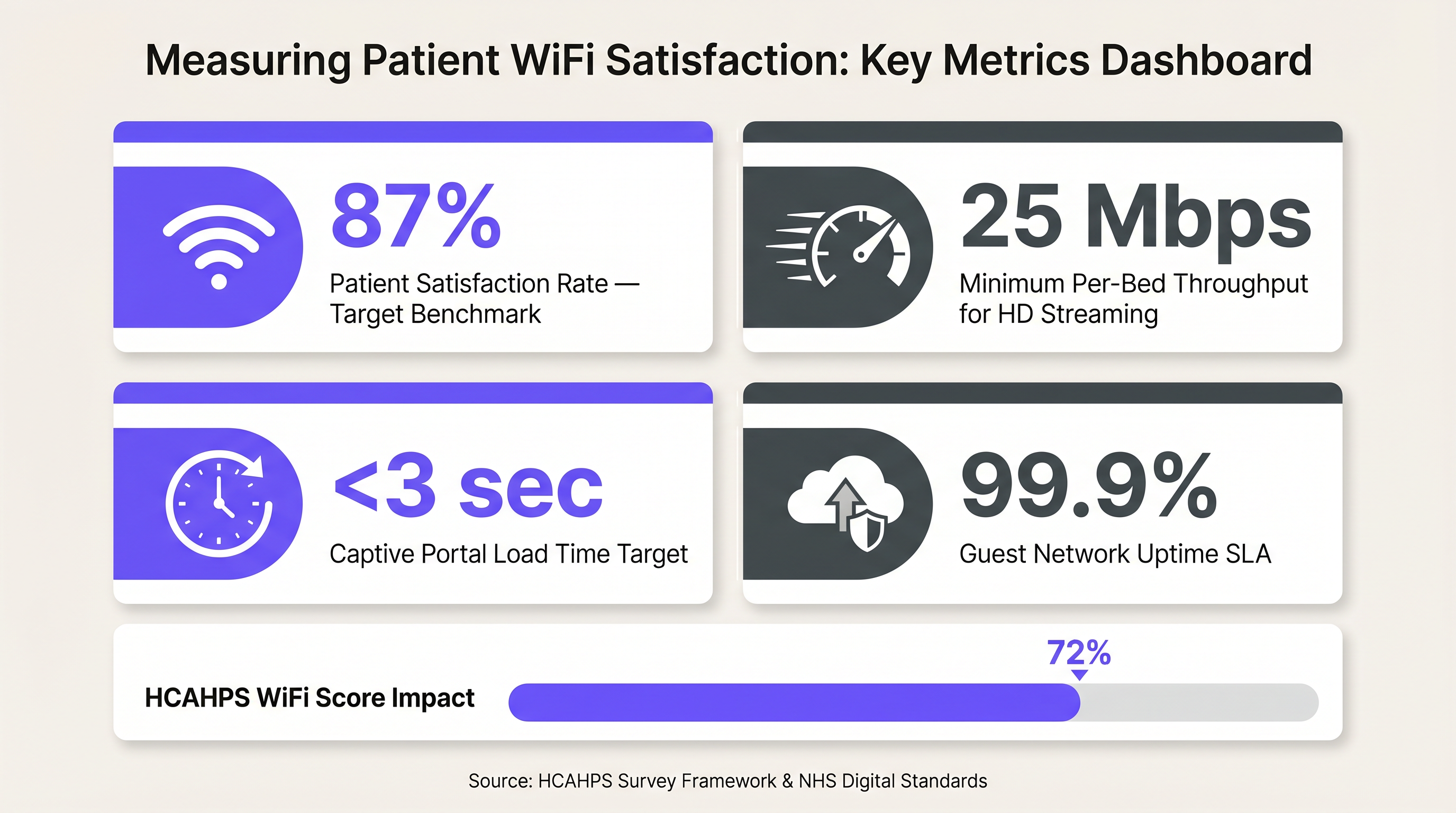
Für Krankenhaus-CIOs, klinische IT-Manager und Netzwerkarchitekten ist der Auftrag zweifach: ein Konnektivitätserlebnis auf Verbraucherniveau zu bieten, das die Patientenerwartungen erfüllt (und die HCAHPS-Werte steigert), während gleichzeitig eine militärische Isolation zwischen der Gast-Broadcast-Domäne und dem klinischen Netzwerk durchgesetzt wird.
Dieser Leitfaden bietet umsetzbare, herstellerunabhängige technische Praktiken für die Architektur von Gast-WiFi im Krankenhaus. Wir werden Layer-2-Segmentierungsstrategien, RF-Kanalplanung in dichten klinischen Umgebungen, moderne Authentifizierungsprotokolle (802.1X vs. WPA3-SAE) und die Messung des ROI der Patientenkonnektivität untersuchen.
Technischer Deep-Dive: Architektur der Netzwerktrennung
Die grundlegende Regel des Netzwerkdesigns im Gesundheitswesen ist die absolute Isolation: Klinischer Verkehr und Gastverkehr dürfen niemals eine Layer-2-Broadcast-Domäne teilen. Dieses Prinzip stimmt mit den technischen Sicherheitsvorkehrungen von HIPAA und dem NHS Data Security and Protection Toolkit überein.
VLAN-Segmentierung und das Drei-Schichten-Modell
Der Standardansatz zur Isolation ist die VLAN-Segmentierung über die Core-, Distributions- und Zugriffsschichten. Ein dediziertes VLAN (z.B. VLAN 10) wird klinischen Systemen zugewiesen, während ein separates VLAN (z.B. VLAN 20) den gesamten Gastverkehr transportiert. Diese VLANs werden über die Switching-Infrastruktur getrunkt und an einer Next-Generation Firewall (NGFW) terminiert, wo das Inter-VLAN-Routing entweder explizit blockiert oder über Stateful-Inspection-Regeln streng kontrolliert wird.
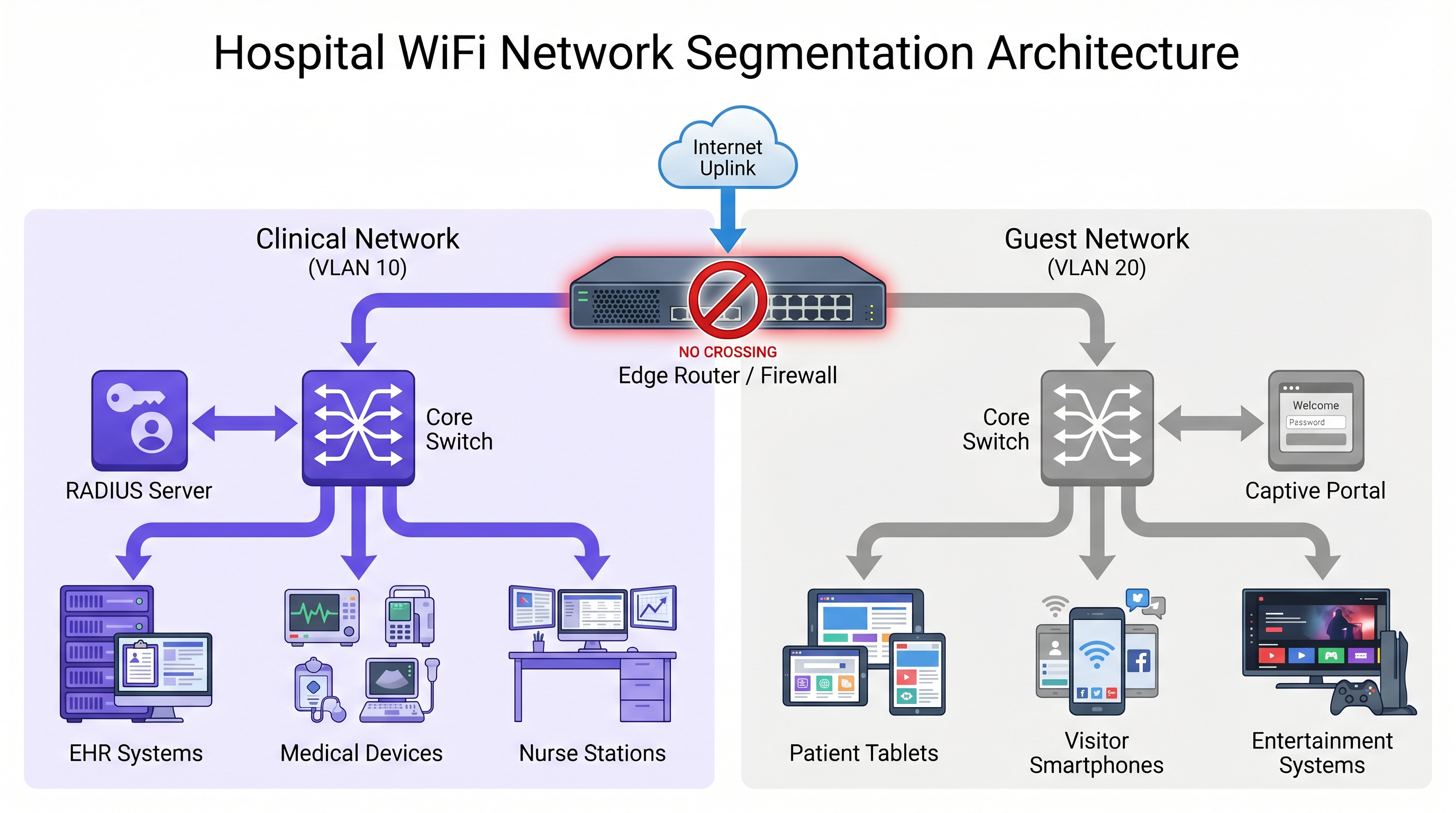
Das alleinige Vertrauen auf VLANs auf Switch-Ebene ist jedoch unzureichend. Die Durchsetzung muss am Edge erfolgen:
- Dual-SSID Access Points: Wenn APs sowohl klinische als auch Gast-SSIDs senden, muss der Wireless LAN Controller (WLC) diese mit strenger Isolation separaten VLANs zuordnen.
- AP-Isolation / Client-Isolation: Diese Funktion muss standardmäßig auf der Gast-SSID aktiviert sein. Sie verhindert die Client-zu-Client-Kommunikation im selben VLAN und stellt sicher, dass das Gerät eines Patienten das Gerät eines anderen Patienten nicht ausspionieren oder angreifen kann.
- Mikro-Segmentierung: Für ältere medizinische IoT-Geräte, die keine moderne Authentifizierung unterstützen können, sollten Network Access Control (NAC)-Richtlinien ihre Kommunikation streng auf die spezifischen klinischen Server beschränken, die sie benötigen, um den Explosionsradius eines potenziellen Kompromisses zu begrenzen.
Authentifizierungs- und Verschlüsselungsstandards
Authentifizierungsmodelle müssen je nach Netzwerkanwendungszweck divergieren:
Klinisches Netzwerk: Erfordert IEEE 802.1X-Authentifizierung unter Verwendung von EAP-TLS (zertifikatbasiert) oder PEAP-MSCHAPv2 (anmeldeinformationenbasiert), unterstützt durch einen RADIUS-Server. Pre-Shared Keys (PSKs) dürfen niemals in klinischen Netzwerken verwendet werden, da ein einziger kompromittierter PSK die gesamte SSID offenlegt.
Gast-Netzwerk: Der Authentifizierungsfluss muss die Zugänglichkeit für Patienten mit unterschiedlichen technischen Kenntnissen priorisieren. Ein Captive Portal mit SMS-Verifizierung oder Ein-Klick-Akzeptanz ist ideal. Um den Over-the-Air-Verkehr ohne komplexe Anmeldeinformationsverwaltung zu sichern, setzen Sie WPA3-SAE (Simultaneous Authentication of Equals) ein. WPA3-SAE verwendet einen Zero-Knowledge-Proof-Austausch, der vor Offline-Wörterbuchangriffen schützt, selbst wenn der Handshake abgefangen wird.
RF-Design und Kapazitätsplanung
Krankenhausumgebungen sind RF-feindlich, mit dicken Betonwänden, bleiverkleideten Radiologieräumen und erheblichen Interferenzen durch medizinische Geräte.
Die Bandbreitenplanung erfordert realistische Berechnungen pro Bett. Ein modernes Patientenzimmer kann ein Smartphone, ein Tablet und einen Smart-TV enthalten. Das Streamen von HD-Videos erfordert 5 Mbit/s, während 4K 25 Mbit/s benötigt. Videoanrufe über FaceTime oder Teams erfordern 1-3 Mbit/s symmetrisch.
Faustregel: Planen Sie mindestens 25 Mbit/s verfügbaren Durchsatz pro Bett ein. In einer Einrichtung mit 200 Betten und 60 % gleichzeitiger Nutzung zu Spitzenzeiten kann der gesamte Gastbedarf leicht 3 Gbit/s überschreiten.
Für die AP-Dichte setzen Sie einen Access Point pro Stationsbucht (z.B. alle 4-6 Betten) ein, anstatt einen pro Station. Konfigurieren Sie das 5-GHz-Band für durchsatzempfindliche Gastgeräte und reservieren Sie 2,4 GHz für ältere IoT-Geräte und ältere klinische Handsets. Die Sendeleistung sollte konservativ eingestellt werden, um eine Zellüberlappung von 15-20 % zu ermöglichen; übermäßig starke APs verursachen Gleichkanalinterferenzen und verschlechtern den Gesamtdurchsatz.
Implementierungsleitfaden: Best Practices für die Bereitstellung
Die Bereitstellung von Gast-WiFi im Krankenhaus erfordert strenge Tests und Validierungen, um die klinische Sicherheit zu gewährleisten.
- Führen Sie prädiktive und aktive Standortbegehungen durch: Niemals ohne ein prädiktives Modell bereitstellen und immer mit einer aktiven Begehung nach der Installation validieren. Ordnen Sie die Abdeckung einem Ziel von -65 dBm RSSI mit einem Signal-Rausch-Verhältnis (SNR) von mindestens 25 dB zu.
- Implementieren Sie Bandbreitenmanagement: Ohne Quality of Service (QoS) und Ratenbegrenzung kann ein einzelner Benutzer, der Massen-Downloads durchführt, den Uplink sättigen. Erzwingen Sie Ratenbegrenzungen pro Client (z.B. 5-10 Mbit/s Downstream) und verwenden Sie DSCP-Markierung, um Echtzeitverkehr wie VoIP- und Videoanrufe gegenüber Massendaten zu priorisieren.
- Stellen Sie ein robustes Captive Portal bereit: Das Portal ist die digitale Eingangstür. Es muss mobilfreundlich, schnell ladend und mit Barrierefreiheitsstandards konform sein. Die Integration mit einer Plattform wie Purple's Gast-WiFi sorgt für ein markengerechtes Erlebnis und erfasst gleichzeitig wertvolle Nutzungsanalysen.
- Obligatorischer Penetrationstest: Führen Sie vor der Inbetriebnahme einen Inter-VLAN-Routing-Test durch. Versuchen Sie, klinische Subnetze von einem im Gastnetzwerk authentifizierten Gerät aus anzupingen oder zu erreichen. Jede erfolgreiche Verbindung ist ein sofortiger Fehlerzustand.
ROI & Geschäftlicher Nutzen
Die Patientenzufriedenheit ist direkt an die Krankenhausfinanzierung und den Ruf gebunden. In den USA beeinflussen HCAHPS-Werte (Hospital Consumer Assessment of Healthcare Providers and Systems) die Medicare-Erstattungen. Im Vereinigten Königreich erfüllt der NHS Friends and Family Test eine ähnliche Funktion. Patienten betrachten zuverlässiges WiFi zunehmend nicht als Luxus, sondern als grundlegende Notwendigkeit, um während der Genesung den Kontakt zu Angehörigen aufrechtzuerhalten und persönliche Angelegenheiten zu regeln.
Über die Zufriedenheit hinaus liefert ein ordnungsgemäß implementiertes Gastnetzwerk verwertbare Daten. Die Nutzung von WiFi Analytics ermöglicht es den Betriebsteams, Verweildauern, Besucherströme und Spitzenzeiten zu verstehen, was direkt in die Kapazitätsplanung und Personalmodelle einfließt. In Kombination mit Wayfinding -Lösungen verwandelt sich das Netzwerk von einem Kostenfaktor in einen strategischen Vermögenswert, der verpasste Termine reduziert und das gesamte Besuchererlebnis verbessert.
Schlüsselbegriffe & Definitionen
VLAN Segmentation
The practice of dividing a single physical network into multiple distinct logical networks to isolate traffic.
Essential in hospitals to ensure a compromised guest device cannot access sensitive clinical systems.
AP Isolation (Client Isolation)
A wireless network setting that prevents devices connected to the same access point from communicating directly with each other.
Prevents malicious actors on the guest network from scanning or attacking other patients' devices.
IEEE 802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The mandatory authentication standard for clinical devices, replacing vulnerable Pre-Shared Keys (PSKs).
WPA3-SAE
Simultaneous Authentication of Equals, a secure key establishment protocol used in WPA3 that protects against offline dictionary attacks.
Provides robust over-the-air encryption for guest networks without requiring complex per-user credentials.
HCAHPS
Hospital Consumer Assessment of Healthcare Providers and Systems, a standardized survey of patients' perspectives of hospital care.
In the US, WiFi quality often influences the 'hospital environment' scores, which can impact Medicare reimbursements.
Micro-segmentation
A security technique that enables fine-grained security policies assigned to data center applications, down to the workload level.
Used to secure legacy medical IoT devices by restricting their network access only to necessary clinical servers.
Captive Portal
A web page that the user of a public-access network is obliged to view and interact with before access is granted.
The primary interface for hospital guests, used to accept terms of service, verify identity, and collect analytics.
Layer 2 Broadcast Domain
A logical division of a computer network in which all nodes can reach each other by broadcast at the data link layer.
Clinical and guest traffic must never share the same broadcast domain to prevent lateral movement of threats.
Fallstudien
A 400-bed acute care hospital is experiencing severe guest network congestion every evening between 6 PM and 9 PM. The network uses a single 1 Gbps internet uplink shared between clinical management traffic and guest access. Patients are complaining of dropped video calls, negatively impacting HCAHPS scores.
The IT team must implement a multi-layered bandwidth management strategy. First, deploy traffic shaping at the firewall to guarantee a minimum of 200 Mbps for clinical management traffic, preventing guest usage from starving critical systems. Second, implement per-client rate limiting on the WLC, capping guest devices at 8 Mbps download/2 Mbps upload. Finally, apply Application Visibility and Control (AVC) to block peer-to-peer file sharing and throttle streaming video to standard definition (SD) resolutions during peak hours.
A private clinic group is acquiring a legacy facility. The existing network infrastructure uses older access switches that do not support 802.1Q VLAN trunking reliably. The CIO wants to deploy a unified guest WiFi portal across all sites within 30 days, but the clinical network cannot be compromised.
Due to the hardware limitations preventing secure logical separation (VLANs), the team must implement physical separation. They should deploy a parallel, cloud-managed wireless infrastructure exclusively for guest access. This involves installing new APs cabled to dedicated, low-cost PoE switches that connect directly to a separate internet circuit, completely bypassing the legacy clinical LAN. The new APs will integrate with the group's centralized captive portal platform.
Szenarioanalyse
Q1. A vendor proposes installing a new fleet of smart infusion pumps. The pumps only support WPA2-Personal (Pre-Shared Key) and cannot utilize 802.1X certificates. How should the network architect integrate these devices securely?
💡 Hinweis:Consider how to limit the blast radius if the PSK is compromised.
Empfohlenen Ansatz anzeigen
The architect must place the infusion pumps on a dedicated IoT VLAN, separate from both the main clinical workstation VLAN and the guest VLAN. Micro-segmentation or strict ACLs at the firewall should be applied so these pumps can only communicate with their specific management server, blocking all other lateral network access.
Q2. During a post-deployment audit, a security analyst connects a laptop to the 'Hospital_Guest' SSID and successfully pings the IP address of a nurse station thin client. What is the most likely configuration error?
💡 Hinweis:Think about where traffic boundaries are enforced between logical networks.
Empfohlenen Ansatz anzeigen
The most likely error is a failure at the routing or firewall layer. While the VLANs may be defined on the switches, the inter-VLAN routing rules on the core router or firewall are either missing or overly permissive, allowing traffic to traverse from the guest subnet to the clinical subnet.
Q3. The hospital executive board wants to implement a complex, multi-page registration form on the guest WiFi captive portal to gather detailed demographic data for marketing. As the IT manager, what is your primary concern with this approach?
💡 Hinweis:Consider the user demographic and the primary goal of patient connectivity.
Empfohlenen Ansatz anzeigen
The primary concern is user friction leading to a drop in patient satisfaction. Hospital patients may be elderly, distressed, or technically inexperienced. A complex portal will result in connection failures, increased IT helpdesk tickets, and lower HCAHPS/Friends and Family Test scores. The portal should prioritize a simple, one-click or SMS-verified login.
Wichtigste Erkenntnisse
- ✓Clinical and guest traffic must be strictly isolated into separate VLANs with no Layer 2 bridging.
- ✓Relying solely on switch VLANs is insufficient; enforce separation at the AP, WLC, and Firewall.
- ✓Use 802.1X for clinical authentication; use WPA3-SAE and simple captive portals for guests.
- ✓Plan for a minimum of 25 Mbps throughput per bed to support modern streaming and video calling.
- ✓Always perform inter-VLAN penetration testing before approving a network for go-live.
- ✓Reliable guest WiFi directly impacts hospital funding metrics like HCAHPS and Friends and Family Test scores.



