Acceso Seguro para Invitados: Implementación de NAC para Dispositivos No Administrados
Esta guía de referencia técnica autorizada detalla la arquitectura, el despliegue y las consideraciones de cumplimiento para implementar el Control de Acceso a la Red (NAC) y asegurar los dispositivos de invitados no administrados. Ofrece orientación práctica para que los líderes de TI logren un acceso seguro para invitados sin comprometer la infraestructura corporativa.
Listen to this guide
View podcast transcript
- Resumen Ejecutivo
- Análisis Técnico Detallado: Arquitectura NAC para Dispositivos No Administrados
- La Arquitectura de Tres Niveles
- WPA3 y Cifrado Inalámbrico Oportunista (OWE)
- Aleatorización de Direcciones MAC y Vinculación de Identidad
- Guía de Implementación
- Paso 1: Definir la Segmentación de Red y las VLAN
- Paso 2: Desplegar y Configurar la Infraestructura RADIUS
- Paso 3: Configurar el Captive Portal y el Flujo de Identidad
- Paso 4: Pruebas y Validación de Extremo a Extremo
- Mejores Prácticas y Cumplimiento
- Solución de Problemas y Mitigación de Riesgos
- ROI e Impacto Comercial

Resumen Ejecutivo
Para los entornos empresariales —ya sea en hostelería, comercio minorista o el sector público—, proporcionar acceso WiFi sin interrupciones a invitados y contratistas es una necesidad comercial. Sin embargo, los dispositivos no administrados presentan una superficie de ataque significativa. Cada smartphone, tablet y dispositivo IoT que se conecta a su red es una entidad desconocida, que opera fuera del control de su infraestructura de Gestión de Dispositivos Móviles (MDM). El desafío para los líderes de TI es facilitar este acceso mientras se segmentan estrictamente estos dispositivos de los activos corporativos y se garantiza el cumplimiento de marcos como PCI DSS y GDPR.
Esta guía ofrece una inmersión profunda en la implementación del Control de Acceso a la Red (NAC) específicamente para dispositivos no administrados. Vamos más allá de las claves precompartidas básicas para explorar la segmentación de red impulsada por la identidad y aplicada por políticas. Al aprovechar los captive portals integrados con motores de políticas respaldados por RADIUS, las organizaciones pueden aplicar posturas de seguridad rigurosas sin introducir una fricción inaceptable en la experiencia del usuario. Cubriremos el diseño arquitectónico, las metodologías de despliegue y la integración de plataformas como Guest WiFi para gestionar la identidad y el consentimiento a escala.
Análisis Técnico Detallado: Arquitectura NAC para Dispositivos No Administrados
El Control de Acceso a la Red es la aplicación de acceso basado en políticas a los recursos de la red. Si bien el 802.1X tradicional con EAP-TLS es el estándar de oro para dispositivos administrados —a menudo dependiendo del despliegue de certificados a través de SCEP (ver El Papel de SCEP y NAC en la Infraestructura MDM Moderna )—, este enfoque no es viable para invitados transitorios. Los dispositivos no administrados requieren una arquitectura que equilibre una seguridad robusta con una incorporación de baja fricción.
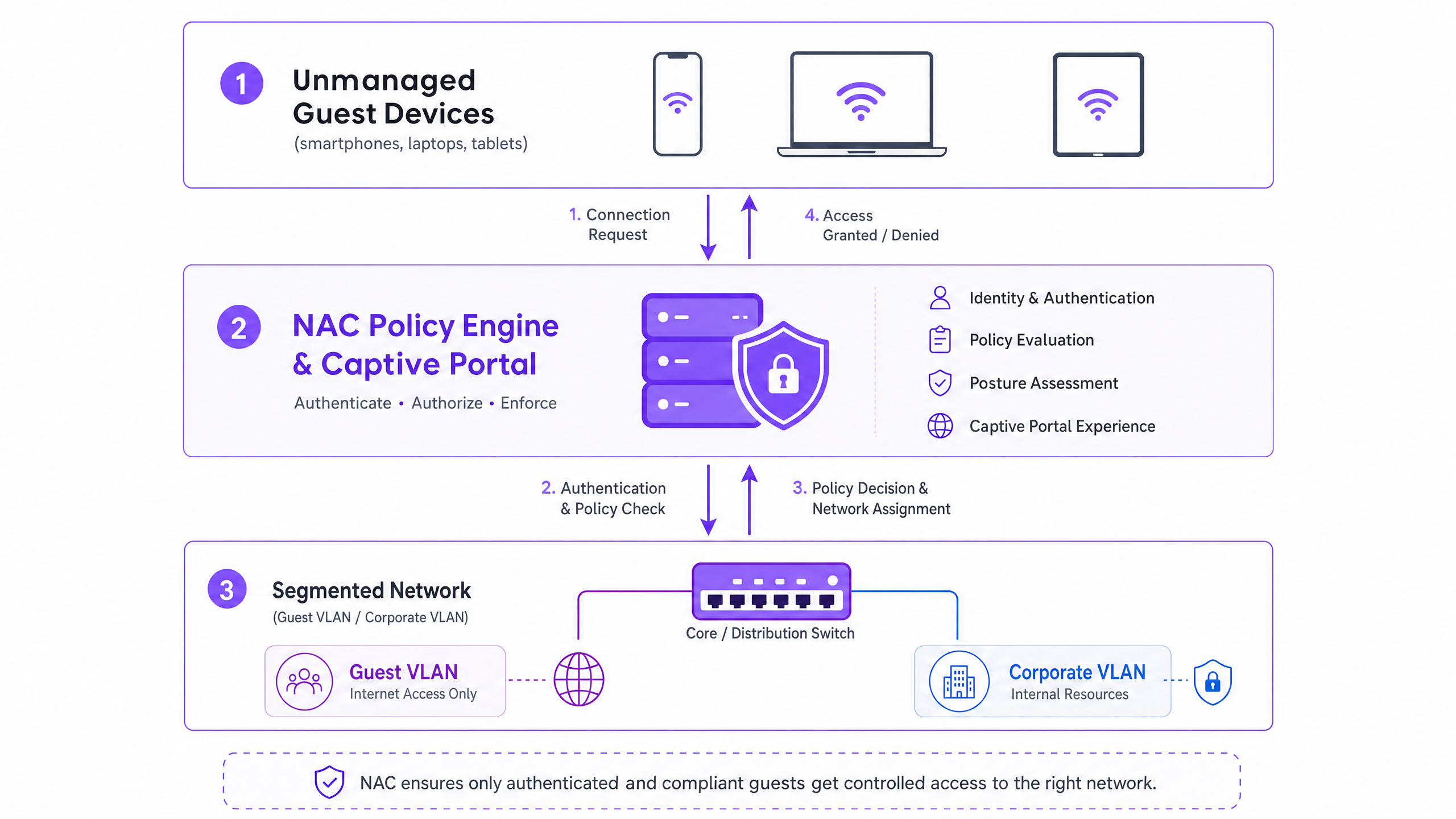
La Arquitectura de Tres Niveles
La arquitectura para un acceso seguro de invitados comprende tres capas funcionales:
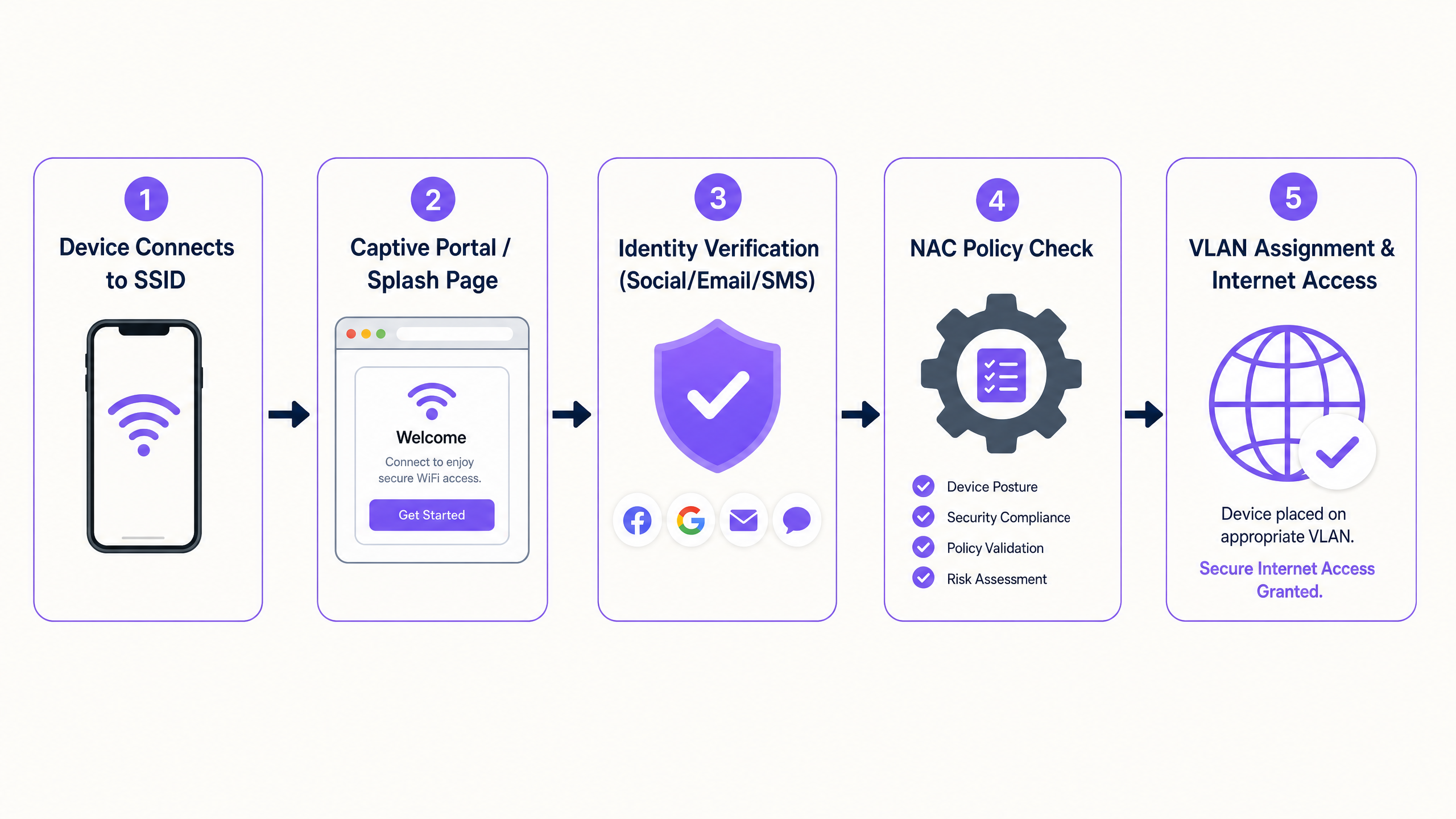
- Autenticación y Captura de Identidad: Dado que 802.1X es poco práctico para dispositivos no administrados, la capa de autenticación se basa en un captive portal. Esta interfaz basada en web intercepta la solicitud inicial HTTP/HTTPS, redirigiendo al usuario a un flujo de autenticación. Aquí, plataformas como Guest WiFi de Purple operan como el proveedor de identidad, capturando credenciales a través de inicio de sesión social, verificación de correo electrónico o SMS.
- Motor de Políticas (RADIUS/NAC): Una vez establecida la identidad, el motor de políticas evalúa la solicitud contra las reglas de acceso definidas. El sistema determina el segmento de red apropiado basándose en la identidad autenticada, el tipo de dispositivo o la hora del día.
- Aplicación en el Borde de la Red: Los puntos de acceso inalámbricos y los switches de borde aplican la decisión de la política. El sistema NAC se comunica a través del protocolo RADIUS. Tras una autenticación exitosa, se devuelve un mensaje
Access-Acceptcon atributos específicos de asignación de VLAN, colocando el dispositivo en el segmento designado.
WPA3 y Cifrado Inalámbrico Oportunista (OWE)
La transición a WPA3 es fundamental para la seguridad inalámbrica moderna. Mientras que WPA3-SAE reemplaza el vulnerable WPA2-PSK para redes personales, WPA3-OWE (Cifrado Inalámbrico Oportunista) es el estándar para redes de invitados públicas. OWE proporciona cifrado de datos individualizado entre el dispositivo cliente y el punto de acceso sin requerir una contraseña. Esto elimina la vulnerabilidad de transmisión en texto claro inherente a los SSID de invitados abiertos tradicionales, proporcionando una base segura incluso antes de que se aplique la política NAC.
Aleatorización de Direcciones MAC y Vinculación de Identidad
Los sistemas operativos modernos (iOS 14+, Android 10+, Windows 10) implementan la aleatorización de direcciones MAC para proteger la privacidad del usuario. Los dispositivos generan una dirección MAC única y aleatoria para cada SSID al que se conectan. Esto rompe fundamentalmente las políticas NAC heredadas que dependen de la dirección MAC como un identificador persistente para los invitados recurrentes.
La solución arquitectónica es cambiar el modelo de identidad del dispositivo al usuario. Cuando un invitado se autentica a través del captive portal, la sesión debe vincularse a su identidad verificada (por ejemplo, correo electrónico o número de teléfono) en lugar de a la dirección MAC efímera. La plataforma WiFi Analytics de Purple gestiona esto de forma nativa, manteniendo perfiles de usuario persistentes y registros de cumplimiento en todas las sesiones, independientemente de la rotación de la dirección MAC.
Guía de Implementación
El despliegue de NAC para dispositivos no administrados requiere un enfoque sistemático para garantizar la seguridad sin interrumpir las operaciones.
Paso 1: Definir la Segmentación de Red y las VLAN
Antes de configurar las políticas NAC, la segmentación de red subyacente debe ser rigurosa.
- VLAN de Preautenticación (Cuarentena): Los dispositivos se colocan aquí al establecer la conexión inicial. Esta VLAN solo debe permitir la resolución DNS y el tráfico HTTP/HTTPS destinado a las direcciones IP del captive portal. Todo el demás tráfico debe ser descartado.
- VLAN de Invitados: Después de la autenticación, los dispositivos se mueven aquí. Esta VLAN debe tener acceso directo a internet, pero debe denegar estrictamente todo el enrutamiento a subredes corporativas (espacio RFC 1918) y a otros clientes invitados (aislamiento de clientes).
- VLAN de Contratistas/Proveedores: Un segmento separado para terceros conocidos que requieren acceso a recursos internos específicos, controlado por ACL de firewall granulares.
Paso 2: Desplegar y Configurar la Infraestructura RADIUS
El servidor RADIUS actúa como intermediario entre el borde de su red y el proveedor de identidad. Para despliegues empresariales, integrar un servicio RADIUS alojado en la nube con su plataforma de captive portal reduce la sobrecarga operativa y mejora la redundancia. Asegúrese de que los secretos compartidos de RADIUS sean criptográficamente fuertes y se roten de acuerdo con su política de seguridad.
Paso 3: Configurar el Captive Portal y el Flujo de Identidad
Configure el Captive Portal para gestionar el flujo de autenticación. Esto incluye la configuración del "walled garden" (la lista de direcciones IP y dominios accesibles antes de la autenticación) para asegurar que el portal se cargue correctamente. Es crucial que el DNS funcione dentro de la VLAN de preautenticación.
Paso 4: Pruebas y Validación de Extremo a Extremo
Las pruebas deben validar tanto la experiencia del usuario como los límites de seguridad. Verifique que un dispositivo de prueba complete exitosamente el flujo del Captive Portal y reciba la asignación de VLAN correcta a través de los atributos RADIUS. Lo más importante es validar la segmentación: intente hacer ping o enrutar tráfico desde la VLAN de Invitados a una dirección IP corporativa conocida. Esto debe fallar.
Mejores Prácticas y Cumplimiento
- Cumplimiento PCI DSS: Para establecimientos en Retail y Hospitality , PCI DSS exige un aislamiento estricto del Entorno de Datos del Titular de la Tarjeta (CDE). El WiFi para invitados debe estar física o lógicamente separado del CDE, sin permitir enrutamiento. NAC aplica esto en la capa de acceso.
- GDPR y Privacidad de Datos: Al capturar datos de invitados a través del portal, se debe obtener el consentimiento explícito. El Captive Portal debe presentar términos de uso y políticas de privacidad claros. La plataforma subyacente debe admitir políticas automatizadas de retención de datos y solicitudes de acceso de los interesados.
- Gestión de Sesiones: Implemente tiempos de espera de sesión adecuados. Para entornos minoristas, un tiempo de espera de 2 a 4 horas es típico. Para hospitality, alinee la duración de la sesión con la estancia del huésped. Siempre configure un tiempo de espera por inactividad (por ejemplo, 30 minutos) para eliminar sesiones inactivas y liberar concesiones DHCP.
Solución de Problemas y Mitigación de Riesgos
- Mala Configuración de Split-Tunnel: El riesgo más grave es una regla de firewall mal configurada que permite el tráfico de la VLAN de Invitados a la red corporativa. La auditoría automatizada regular de las ACL del firewall es esencial.
- Fallas en la Resolución de DNS: Si los invitados se quejan de que "la página de inicio de sesión no carga", el problema es casi siempre el DNS. Asegúrese de que el alcance DHCP para la VLAN de preautenticación proporcione un servidor DNS confiable y que el firewall permita el tráfico DNS (puerto UDP 53) a ese servidor.
- Manejo de Tiempos de Espera de RADIUS (Fail-Closed): Configure los puntos de acceso para que "fallen cerrados" si el servidor RADIUS deja de ser accesible. Las configuraciones de "fail-open" otorgan acceso no autenticado durante una interrupción, lo que representa un riesgo de seguridad inaceptable.
ROI e Impacto Comercial
La implementación de acceso seguro para invitados a través de NAC ofrece un valor comercial medible:
- Mitigación de Riesgos: Reducción cuantificable de la superficie de ataque al asegurar que los dispositivos no administrados no puedan sondear los activos corporativos.
- Eficiencia Operativa: La incorporación automatizada reduce los tickets de soporte de TI relacionados con el acceso de invitados.
- Adquisición de Datos: Al utilizar plataformas como Purple, el proceso de incorporación segura captura simultáneamente datos de primera parte, alimentando la plataforma de WiFi Analytics para impulsar el ROI de marketing.
Key Definitions
Network Access Control (NAC)
A security framework that enforces policy-based access to network resources, evaluating identity and posture before granting access.
Used to ensure that unmanaged guest devices are properly segmented and authenticated before accessing the network.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted.
The primary authentication mechanism for unmanaged devices that cannot use 802.1X certificates.
RADIUS
Remote Authentication Dial-In User Service; a networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management.
The protocol used by the NAC policy engine to communicate VLAN assignments to the wireless access points.
Dynamic VLAN Assignment
The process of assigning a network device to a specific Virtual Local Area Network based on authentication credentials rather than the physical port or SSID.
Allows a single guest SSID to securely serve different types of users (guests, contractors) by placing them on different network segments.
WPA3-OWE
Opportunistic Wireless Encryption; a WiFi standard that provides individualized data encryption for open networks without requiring a password.
Secures the wireless transmission for guest networks, preventing passive eavesdropping on public SSIDs.
MAC Address Randomisation
A privacy feature in modern operating systems where the device generates a temporary MAC address for each wireless network it connects to.
Breaks legacy systems that use MAC addresses to track returning guests, necessitating identity-based authentication.
Walled Garden
A restricted environment that controls the user's access to web content and services prior to full authentication.
Required to allow unauthenticated devices to access the captive portal and necessary identity providers (like Facebook or Google) during the login process.
Client Isolation
A wireless network security feature that prevents devices connected to the same access point from communicating directly with each other.
Essential for guest networks to prevent infected guest devices from spreading malware to other guests.
Worked Examples
A large retail chain is rolling out guest WiFi across 500 stores. They need to ensure PCI compliance for their Point of Sale (POS) systems while allowing guests to connect and authenticate via a captive portal. How should the network be segmented and authenticated?
The implementation requires strict logical separation using VLANs and firewall ACLs. 1. The POS systems are placed on a dedicated, highly restricted Corporate VLAN (e.g., VLAN 10). 2. A Pre-Authentication VLAN (VLAN 20) is created for unauthenticated guests, allowing only DNS and HTTPS traffic to the captive portal domain. 3. A Guest VLAN (VLAN 30) is created for authenticated guests, allowing outbound internet access but explicitly denying all RFC 1918 (internal) IP addresses. The NAC system uses RADIUS to move devices from VLAN 20 to VLAN 30 upon successful portal authentication.
A hospital provides WiFi for patients and visitors but is experiencing issues where returning patients must re-authenticate every day because their smartphones randomize their MAC addresses. How can the IT team provide a seamless experience without compromising security?
The IT team must shift the authentication binding from the MAC address to the user identity. They implement a captive portal integrated with a platform like Purple Guest WiFi. When a patient first connects, they authenticate via SMS or email. The platform creates a persistent user profile. Even when the device generates a new MAC address on subsequent visits, the platform recognizes the user upon re-authentication and seamlessly applies the correct NAC policy without requiring a full re-registration.
Practice Questions
Q1. A hotel IT manager is configuring the pre-authentication VLAN for a new captive portal deployment. Guests are reporting that their devices connect to the WiFi, but the login page never appears. What is the most likely configuration error?
Hint: Consider what network services a device needs before it can load a web page via a domain name.
View model answer
The most likely error is a DNS resolution failure within the pre-authentication VLAN. Before a device can load the captive portal, it must resolve the portal's domain name. The DHCP scope for the pre-authentication VLAN must provide a valid DNS server, and the firewall must allow UDP port 53 traffic to that server prior to authentication.
Q2. You are designing the network policy for a stadium. The requirement is to provide internet access to fans while ensuring that the stadium's ticketing scanners (which connect to the same physical access points) have access to internal servers. How do you achieve this securely?
Hint: How can a single physical infrastructure support different logical networks based on identity?
View model answer
Implement dynamic VLAN assignment using 802.1X for the ticketing scanners and a captive portal for the fans. The ticketing scanners authenticate via certificates (802.1X) and are assigned by the RADIUS server to a secure Operations VLAN. Fans connect to an open (or OWE) SSID, authenticate via the captive portal, and are assigned by RADIUS to an isolated Guest VLAN with internet-only access.
Q3. During a security audit, it is discovered that devices on the Guest WiFi can ping the management IP addresses of the network switches. What specific configuration is missing or misconfigured?
Hint: Think about how traffic is controlled between different network segments.
View model answer
The firewall or Layer 3 switch is missing the necessary Access Control Lists (ACLs) to restrict routing from the Guest VLAN. A rule must be implemented that explicitly denies traffic originating from the Guest VLAN subnet destined for any internal subnets (RFC 1918 space), followed by a rule permitting traffic to the internet (0.0.0.0/0).