Automatización de la revocación de certificados con OCSP y CRL en un entorno NAC
Esta guía de referencia técnica proporciona a los gerentes de TI y arquitectos de red un desglose completo de la automatización de la revocación de certificados en un entorno de Control de Acceso a la Red (NAC). Explora las compensaciones arquitectónicas entre OCSP y CRL, ofrece una guía de implementación neutral respecto al proveedor y describe el impacto comercial de la aplicación de políticas en tiempo real.
Listen to this guide
View podcast transcript
- Resumen Ejecutivo
- Análisis Técnico Detallado
- Arquitectura de la Lista de Revocación de Certificados (CRL)
- Arquitectura del Protocolo de Estado de Certificado en Línea (OCSP)
- Integración con Plataformas de Invitados y Análisis
- Guía de Implementación
- Paso 1: Definir el Disparador de Revocación
- Paso 2: Configurar la infraestructura de revocación
- Paso 3: Establecer la política de respaldo
- Paso 4: Definir el comportamiento ante fallos
- Mejores prácticas
- Solución de problemas y mitigación de riesgos
- ROI e impacto empresarial

Resumen Ejecutivo
Para los directores de TI empresariales y arquitectos de red que gestionan entornos de alta densidad —como locales de Hostelería , propiedades Minoristas y despliegues del sector público— la gestión del ciclo de vida de los certificados es una frontera de seguridad crítica. Si bien IEEE 802.1X proporciona una autenticación robusta para dispositivos corporativos y BYOD, el mecanismo por el cual se revoca la confianza a menudo se pasa por alto hasta que ocurre una brecha.
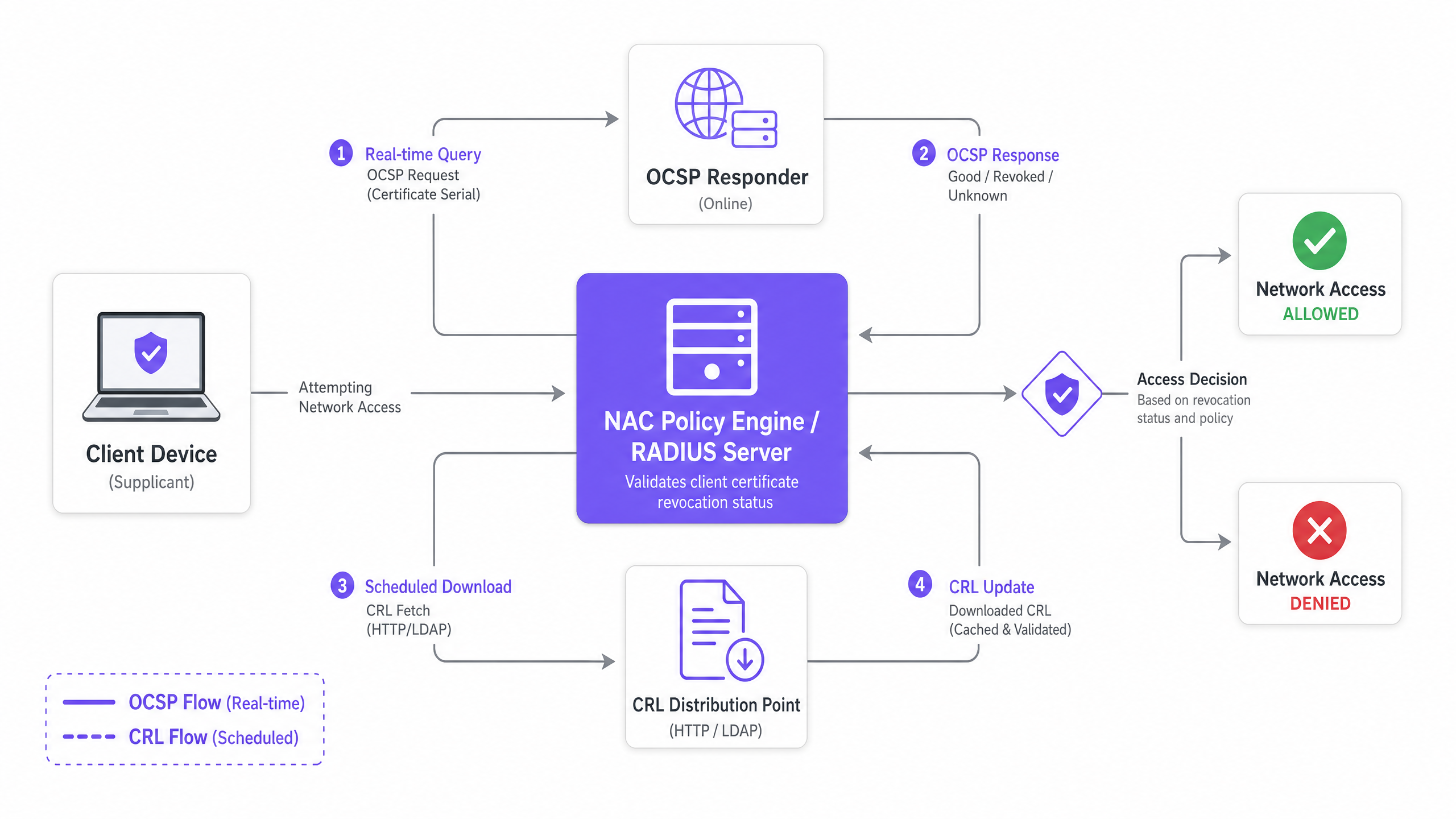
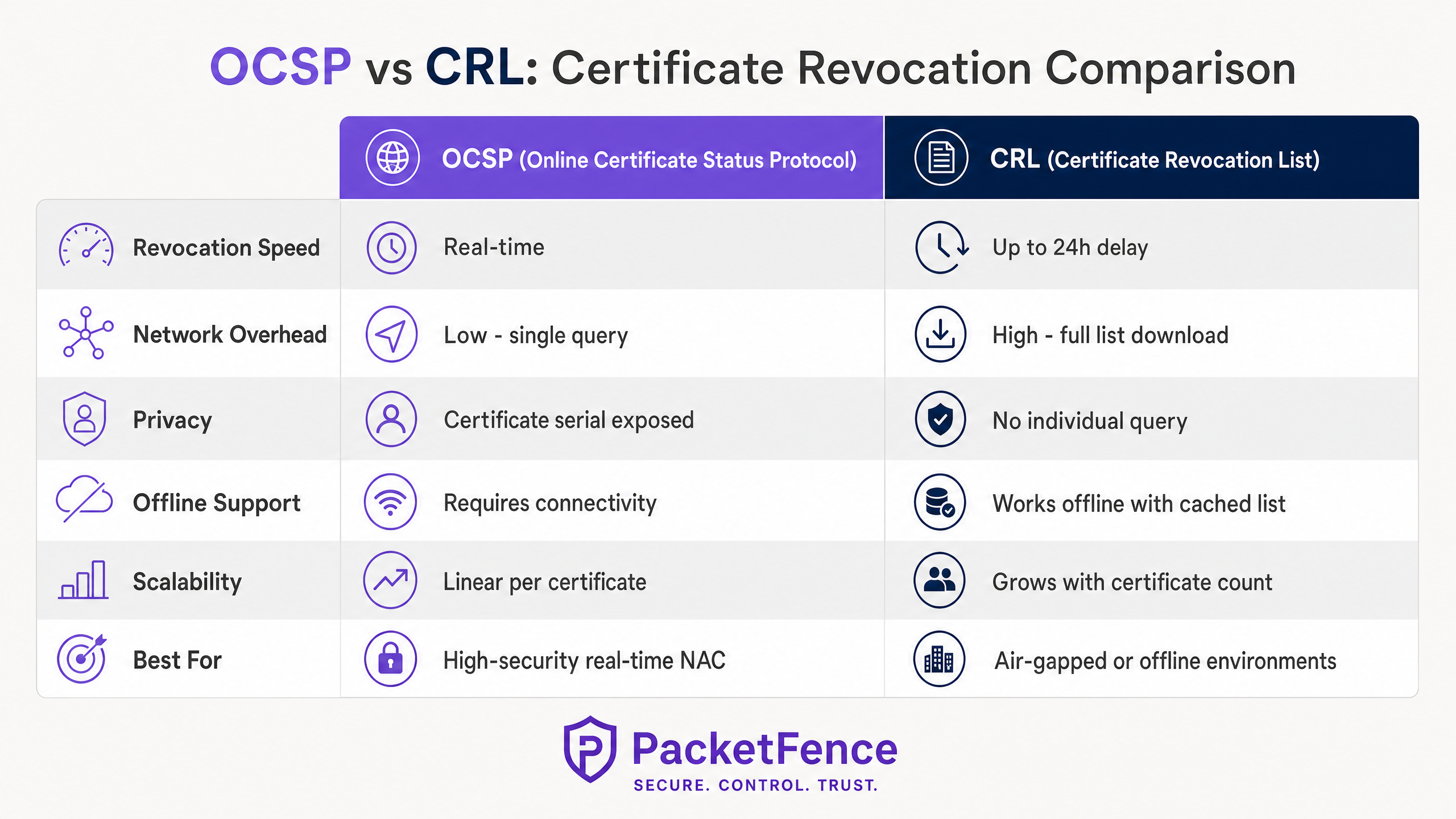
La automatización de la revocación de certificados con el Protocolo de Estado de Certificado en Línea (OCSP) y las Listas de Revocación de Certificados (CRL) dentro de un entorno de Control de Acceso a la Red (NAC) cierra la brecha entre la deshabilitación de puntos finales y la aplicación de políticas de red. Esta guía explora la mecánica arquitectónica de la revocación automatizada, comparando las capacidades en tiempo real de OCSP con la resiliencia fuera de línea de CRL.
Al integrar su plataforma de Gestión de Dispositivos Móviles (MDM), Autoridad de Certificación (CA) y motor de políticas NAC, las organizaciones pueden lograr un acceso a la red de confianza cero donde los dispositivos comprometidos o deshabilitados se les niega la entrada instantáneamente. Esta referencia técnica proporciona una guía de despliegue práctica, estrategias de mitigación de riesgos y explora cómo esta postura de seguridad orientada al personal complementa la infraestructura orientada al público como las plataformas Guest WiFi y WiFi Analytics de Purple.
Análisis Técnico Detallado
En cualquier red empresarial que aproveche IEEE 802.1X con EAP-TLS, los dispositivos se autentican utilizando certificados digitales en lugar de credenciales compartidas. Este enfoque es fundamental para las arquitecturas de seguridad modernas, proporcionando una identidad vinculada al dispositivo que se integra sin problemas con las plataformas MDM a través de protocolos como SCEP (para más información, consulte El Papel de SCEP y NAC en la Infraestructura MDM Moderna ). Sin embargo, los certificados tienen un ciclo de vida definido. Cuando un dispositivo se pierde, un usuario es desvinculado o una clave privada se ve comprometida, la infraestructura de red debe ser instruida explícitamente para dejar de confiar en ese certificado.
Esta instrucción de revocación se entrega a través de dos mecanismos principales: CRL y OCSP.
Arquitectura de la Lista de Revocación de Certificados (CRL)
Una CRL es un archivo firmado digitalmente publicado por la Autoridad de Certificación que contiene los números de serie de todos los certificados revocados que aún no han expirado. El motor de políticas NAC (actuando como servidor RADIUS) descarga periódicamente esta lista desde un Punto de Distribución de CRL (CDP) a través de HTTP o LDAP.
Durante el handshake EAP-TLS, el servidor RADIUS verifica el número de serie del certificado del cliente entrante contra su CRL almacenada localmente. Si el número de serie está presente, la autenticación es rechazada.
Características Arquitectónicas:
- Resiliencia Fuera de Línea: Debido a que el servidor RADIUS almacena en caché la CRL, la verificación de revocación continúa incluso si la CA o el CDP se vuelven inalcanzables.
- Latencia: El principal inconveniente es la latencia entre la revocación y la aplicación. Si un certificado se revoca a las 09:00 y el intervalo de actualización de la CRL es de 24 horas, el dispositivo comprometido conserva el acceso a la red hasta la próxima descarga.
- Sobrecarga de Rendimiento: En entornos con decenas de miles de certificados, los archivos CRL pueden crecer a varios megabytes, creando una tensión en el ancho de banda durante los ciclos de actualización.
Arquitectura del Protocolo de Estado de Certificado en Línea (OCSP)
OCSP aborda las limitaciones de latencia de CRL al permitir la verificación de revocación en tiempo real. En lugar de descargar una lista completa, el servidor RADIUS envía una consulta dirigida que contiene el número de serie del certificado a un respondedor OCSP. El respondedor devuelve un estado firmado: Bueno, Revocado o Desconocido.
Características Arquitectónicas:
- Aplicación en Tiempo Real: Las decisiones de revocación se propagan instantáneamente. Una vez que la CA actualiza el respondedor OCSP, el siguiente intento de autenticación por parte del dispositivo comprometido fallará.
- Dependencia de Disponibilidad: El motor de políticas NAC depende de que el respondedor OCSP esté altamente disponible. Si el respondedor es inalcanzable, el administrador de red debe definir una política de fallo: "fallo abierto" (permitir el acceso, comprometiendo la seguridad) o "fallo cerrado" (denegar el acceso, comprometiendo la disponibilidad).
- OCSP Stapling: Para mitigar la carga y las preocupaciones de privacidad, OCSP Stapling permite que el dispositivo cliente obtenga la respuesta OCSP firmada y la adjunte al handshake TLS, aunque el soporte del suplicante varía.
Integración con Plataformas de Invitados y Análisis
Mientras que OCSP y CRL manejan los rigurosos requisitos de seguridad de los dispositivos del personal y corporativos, las redes orientadas al público requieren arquitecturas diferentes. Para los lugares públicos, la integración de un NAC robusto para el personal con una plataforma pública dedicada como Purple garantiza una cobertura integral. La plataforma de Purple gestiona la autenticación de Captive Portal, la aceptación de los términos de servicio y la captura de datos para el segmento público, mientras que la infraestructura de red subyacente (a menudo los mismos puntos de acceso físicos y conmutadores) aplica 802.1X y OCSP para los SSID corporativos. Comprender el entorno de radio es crucial para ambos segmentos; consulte Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 para la planificación del espectro.
Guía de Implementación
El despliegue de la revocación automatizada de certificados requiere coordinación entre los dominios PKI, MDM y NAC. Siga estos pasos de implementación neutrales respecto al proveedor para establecer un pipeline de revocación resiliente.
Paso 1: Definir el Disparador de Revocación
La automatización comienza en la capa de gestión de puntos finales. Configure su plataforma MDM (por ejemplo, Microsoft Intune, Jamf Pro) para activar una llamada a la API de revocación a su Autoridad de Certificación cuando se cumplan condiciones específicas:
- Dispositivo dado de baja del MDM
- Dispositivo marcado como no conforme
- Cuenta de usuario deshabilitada en el servicio de directorio
Paso 2: Configurar la infraestructura de revocación
Para implementaciones de CRL:
- Configure la CA para publicar la CRL en un CDP de alta disponibilidad (por ejemplo, un servidor web interno con balanceo de carga).
- Establezca el intervalo de publicación de la CRL según su tolerancia al riesgo (por ejemplo, cada 4 horas).
- Configure el servidor RADIUS para obtener la CRL en un intervalo ligeramente más corto que el intervalo de publicación para asegurar que la caché esté siempre actualizada.
Para implementaciones de OCSP:
- Implemente al menos dos respondedores OCSP detrás de un balanceador de carga para asegurar una alta disponibilidad.
- Configure la CA para enviar actualizaciones de revocación a los respondedores OCSP de inmediato.
- Configure el servidor RADIUS para consultar la IP virtual OCSP con balanceo de carga durante la autenticación EAP-TLS.
Paso 3: Establecer la política de respaldo
No dependa de un solo mecanismo. Configure su servidor RADIUS para usar OCSP como verificación de revocación principal, con un respaldo a una CRL almacenada localmente si el respondedor OCSP no es accesible. Esto proporciona una aplicación en tiempo real en condiciones normales y resiliencia fuera de línea durante interrupciones de infraestructura.
Paso 4: Definir el comportamiento ante fallos
Si tanto OCSP como la CRL en caché no están disponibles, el servidor RADIUS debe decidir cómo manejar la solicitud de autenticación.
- Entornos de alta seguridad (por ejemplo, Salud ): Configure "fallo cerrado". Deniegue el acceso para evitar que se conecten dispositivos potencialmente comprometidos.
- Entornos estándar (por ejemplo, centros de Transporte ): Configure "fallo abierto" con alertas. Permita el acceso para mantener la continuidad operativa, pero genere una alerta de alta prioridad para el SOC.
Mejores prácticas
- Implementar CRL Delta: Si depende de CRL en un entorno grande, implemente CRL Delta. Estos archivos contienen solo los cambios de revocación desde la última CRL Base completa publicada, lo que reduce significativamente el tamaño de descarga y el consumo de ancho de banda.
- Monitorear la latencia de OCSP: Las consultas OCSP ocurren en línea durante el handshake EAP-TLS. Si el respondedor OCSP tarda 500 ms en responder, la autenticación se retrasa 500 ms. Monitoree la latencia del respondedor y escale horizontalmente si los tiempos de respuesta se degradan.
- Certificados de corta duración: Considere reducir los períodos de validez de los certificados (por ejemplo, de 1 año a 7 días) mediante la renovación automatizada SCEP/EST. Los certificados de corta duración expiran naturalmente rápido, lo que reduce la dependencia de una infraestructura de revocación robusta.
- Alinear con la estrategia de red más amplia: Asegúrese de que su implementación de NAC se alinee con su arquitectura de red de área amplia. Para obtener información sobre el diseño WAN moderno, consulte SD WAN vs MPLS: La Guía de Red Empresarial 2026 .
Solución de problemas y mitigación de riesgos
El modo de fallo más común en la revocación automatizada es una tubería CA-a-NAC rota que resulta en un evento de "fallo cerrado" que bloquea a los usuarios legítimos.
Riesgo: Interrupción del respondedor OCSP Mitigación: Implemente respondedores en un clúster activo-activo en múltiples dominios de fallo. Implemente verificaciones de estado exhaustivas en el balanceador de carga que verifiquen la capacidad del respondedor para consultar la base de datos de la CA, no solo la disponibilidad del puerto TCP 80.
Riesgo: Caché CRL obsoleta Mitigación: Los servidores RADIUS pueden fallar al descargar la última CRL debido a particiones de red o interrupciones de CDP. Implemente monitoreo que alerte si la CRL almacenada localmente es más antigua que el intervalo de publicación definido.
Riesgo: Revocación MDM incompleta Mitigación: Si el MDM no logra activar la llamada de revocación a la CA, el certificado permanece válido. Implemente un script de conciliación que compare periódicamente la lista de dispositivos activos del MDM con la lista de certificados válidos de la CA, revocando automáticamente cualquier discrepancia.
ROI e impacto empresarial
La automatización de la revocación de certificados transforma la seguridad de un proceso reactivo y manual en un mecanismo de defensa proactivo y automatizado.
- Reducción de riesgos: Al eliminar la ventana de exposición entre el compromiso del dispositivo y el aislamiento de la red, las organizaciones reducen significativamente el riesgo de movimiento lateral y exfiltración de datos. Esto es crucial para mantener el cumplimiento con marcos como PCI DSS y GDPR.
- Eficiencia operativa: La automatización de la tubería de revocación elimina la necesidad de que el personal de soporte actualice manualmente las configuraciones de RADIUS o las bases de datos de CA cuando un empleado se va, ahorrando cientos de horas anualmente en grandes empresas.
- Estrategia de acceso unificado: Un entorno NAC robusto para dispositivos corporativos permite a los equipos de TI implementar con confianza servicios paralelos, como el WiFi para invitados basado en análisis de Purple o los servicios basados en ubicación (consulte BLE Low Energy Explained for Enterprise ), sabiendo que la infraestructura central es segura.
Escuche nuestro informe técnico sobre este tema a continuación:
Key Definitions
EAP-TLS (Extensible Authentication Protocol - Transport Layer Security)
The most secure standard for 802.1X network authentication, requiring both the client and the server to present digital certificates to prove their identity.
IT teams deploy EAP-TLS to eliminate the risks associated with password-based authentication, ensuring only managed, certificate-bearing devices can connect to the corporate network.
OCSP (Online Certificate Status Protocol)
An internet protocol used for obtaining the revocation status of an X.509 digital certificate in real-time.
Crucial for environments requiring immediate enforcement of access policies, such as when an employee is terminated and their device must be instantly disconnected.
CRL (Certificate Revocation List)
A periodically published, digitally signed list of certificate serial numbers that have been revoked by the issuing Certificate Authority.
Used as a primary revocation mechanism in offline or air-gapped networks, or as a highly resilient fallback mechanism for OCSP.
OCSP Stapling
A mechanism where the client device fetches its own OCSP response and 'staples' it to the TLS handshake, presenting it to the RADIUS server.
Reduces the load on the RADIUS server and OCSP Responder, and improves privacy by preventing the CA from seeing exactly when and where a device is authenticating.
Delta CRL
A smaller revocation list containing only the certificates revoked since the last full Base CRL was published.
Essential for large deployments to prevent network congestion, as full CRLs can become massive and consume significant bandwidth during refresh cycles.
CDP (CRL Distribution Point)
The location, typically an HTTP or LDAP URL, where the Certificate Authority publishes the CRL for clients and RADIUS servers to download.
IT teams must ensure the CDP is highly available and reachable from all NAC policy engines; if the CDP goes down, the RADIUS servers cannot update their caches.
Fail Open / Fail Closed
The policy decision dictating what happens when the revocation infrastructure (OCSP or CDP) is unreachable. Fail Open allows access; Fail Closed denies access.
A critical business decision balancing security posture against operational uptime. Requires sign-off from both IT operations and the CISO.
SCEP (Simple Certificate Enrollment Protocol)
A protocol used by MDM platforms to automate the issuance of digital certificates to managed devices without user intervention.
The starting point of the automated lifecycle. SCEP issues the certificate, and the MDM later triggers the CA to revoke it when the device is retired.
Worked Examples
A 500-bed hospital network is migrating from credential-based 802.1X to certificate-based EAP-TLS for all medical IoT devices and staff laptops. The CISO mandates that if a device is reported stolen, its network access must be terminated within 5 minutes. The network team is concerned about the RADIUS server load if it has to constantly query external services. How should the revocation architecture be designed?
The hospital must deploy OCSP to meet the 5-minute revocation SLA, as CRL refresh intervals cannot reliably meet this target without causing severe network overhead. To address the network team's load concerns, the architecture should implement OCSP Responders locally within the hospital's data centre, positioned close to the RADIUS servers to minimise latency. The RADIUS servers should be configured to query the local OCSP VIP. To ensure resilience, the RADIUS servers must be configured with a fallback to a locally cached CRL, updated hourly. The failure policy must be set to 'fail closed' due to the healthcare environment's strict compliance requirements.
A global retail chain with 1,200 stores uses SCEP to provision certificates to point-of-sale (POS) tablets. The stores have limited WAN bandwidth. The IT director wants to implement certificate revocation but is concerned that downloading large CRL files across 1,200 branch RADIUS servers will saturate the WAN links. What is the optimal deployment strategy?
The retail chain should implement a hybrid approach utilising Delta CRLs and OCSP Stapling. First, the CA should be configured to publish a Base CRL weekly and a Delta CRL (containing only recent revocations) every 4 hours. The branch RADIUS servers will only download the small Delta CRLs during the day, minimising WAN impact. Alternatively, if the POS tablets' EAP supplicants support it, OCSP Stapling should be enabled. This shifts the burden of fetching the OCSP response from the branch RADIUS server to the tablet itself, which can fetch the response directly from the central CA over standard HTTPS, bypassing the RADIUS server's processing overhead entirely.
Practice Questions
Q1. Your organisation is deploying 802.1X across 50 remote branch offices. The WAN links to the central data centre are highly congested and frequently drop packets. You need to implement certificate revocation for the branch corporate laptops. Which architecture should you choose?
Hint: Consider the impact of packet loss on real-time protocols versus the resilience of cached data.
View model answer
You should implement a CRL-based architecture, specifically using Base and Delta CRLs. Because the WAN links are congested and unreliable, real-time OCSP queries will frequently time out, causing authentication delays or failures. By configuring the branch RADIUS servers to download and cache Delta CRLs during off-peak hours, the local RADIUS server can perform revocation checks instantly against its cache, even if the WAN link drops entirely during the authentication attempt.
Q2. A security audit reveals that when your primary OCSP Responder goes offline for maintenance, all corporate users are completely locked out of the WiFi network. The business demands that maintenance should not impact user connectivity, but the CISO refuses to change the policy to 'Fail Open'. How do you resolve this?
Hint: If you cannot change the failure policy, you must change the availability of the service.
View model answer
You must implement high availability for the OCSP service. Deploy at least one additional OCSP Responder and place both behind a load balancer. Configure the RADIUS server to query the load balancer's Virtual IP (VIP). During maintenance, you can drain connections from the primary responder, take it offline, and the load balancer will seamlessly route all OCSP queries to the secondary responder, satisfying both the business uptime requirement and the CISO's 'Fail Closed' mandate.
Q3. You have configured your MDM to automatically revoke certificates when a device is marked as 'lost'. You test the system by marking a test iPad as lost. The MDM confirms the revocation, but 10 minutes later, the iPad successfully connects to the corporate WiFi. The RADIUS server is configured to use a CRL published every 24 hours. What is the root cause and how do you fix it?
Hint: Trace the timeline of the revocation data from the CA to the RADIUS server's enforcement engine.
View model answer
The root cause is latency in the CRL publication and refresh cycle. While the MDM successfully told the CA to revoke the certificate, the CA will not publish that updated status to the CRL Distribution Point until the next 24-hour cycle, and the RADIUS server will not download it until its own cache expires. To fix this, you must either migrate to OCSP for real-time checking, or drastically reduce the CRL publication and download intervals (e.g., to 1 hour) to meet your required enforcement timeline.