Configuración de políticas RADIUS para un control de acceso a la red granular
Esta guía autorizada proporciona a gerentes de TI, arquitectos de red y directores de operaciones de recintos un plan técnico completo para configurar políticas RADIUS y lograr un control de acceso a la red granular. Cubre la arquitectura 802.1X, la asignación dinámica de VLAN, la selección de métodos EAP y las estrategias de implementación por fases. Escenarios de implementación reales de la hostelería y el comercio minorista demuestran cómo estas técnicas ofrecen cumplimiento, seguridad y ROI operativo medibles.
Listen to this guide
View podcast transcript
- Resumen Ejecutivo
- Análisis Técnico Detallado
- La Arquitectura de Acceso Consciente del Contexto
- Asignación Dinámica de VLAN y Microsegmentación
- Selección del Método EAP
- Guía de Implementación
- Fase 1: Integración de la Fuente de Identidad
- Fase 2: Configuración de Políticas y Mapeo de Atributos
- Fase 3: Implementación por Fases y Monitoreo
- Mejores Prácticas
- Solución de Problemas y Mitigación de Riesgos
- Modos de Fallo Comunes
- ROI e Impacto Comercial

Resumen Ejecutivo
Para recintos empresariales —desde grandes complejos minoristas hasta estadios de alta densidad— la seguridad de la red y la experiencia del usuario están intrínsecamente ligadas. La configuración de políticas RADIUS para un control de acceso a la red granular proporciona el mecanismo para segmentar el tráfico dinámicamente, asegurando que los activos corporativos permanezcan aislados de las redes de invitados y de los dispositivos IoT vulnerables. Esto ya no es una mejora discrecional; es un requisito fundamental impulsado por mandatos de cumplimiento como PCI DSS y GDPR.
Esta guía ofrece un plan técnico detallado para implementar el control de acceso basado en RADIUS. Examinamos la arquitectura de la autenticación IEEE 802.1X, la mecánica de la asignación dinámica de VLAN a través de Atributos Específicos del Proveedor (VSAs), y la integración de proveedores de identidad como Active Directory, Entra ID y el proveedor de identidad OpenRoaming de Purple. Al ir más allá de las claves precompartidas (PSKs) básicas hacia la aplicación de políticas conscientes del contexto, los líderes de TI pueden mitigar riesgos, optimizar operaciones y aprovechar plataformas como Purple para transformar el WiFi de invitados de un centro de costos en un activo estratégico. El enfoque principal es en estrategias prácticas y neutrales al proveedor que ofrecen un ROI medible y resiliencia operativa.
Análisis Técnico Detallado
La Arquitectura de Acceso Consciente del Contexto
En su esencia, la configuración de políticas RADIUS para un control de acceso a la red granular se basa en el estándar IEEE 802.1X. Este marco facilita el control de acceso a la red basado en puertos, asegurando que solo los dispositivos autenticados y autorizados obtengan acceso a segmentos de red específicos. La arquitectura consta de tres componentes principales: el solicitante (dispositivo cliente), el autenticador (punto de acceso inalámbrico o switch) y el servidor de autenticación (RADIUS).
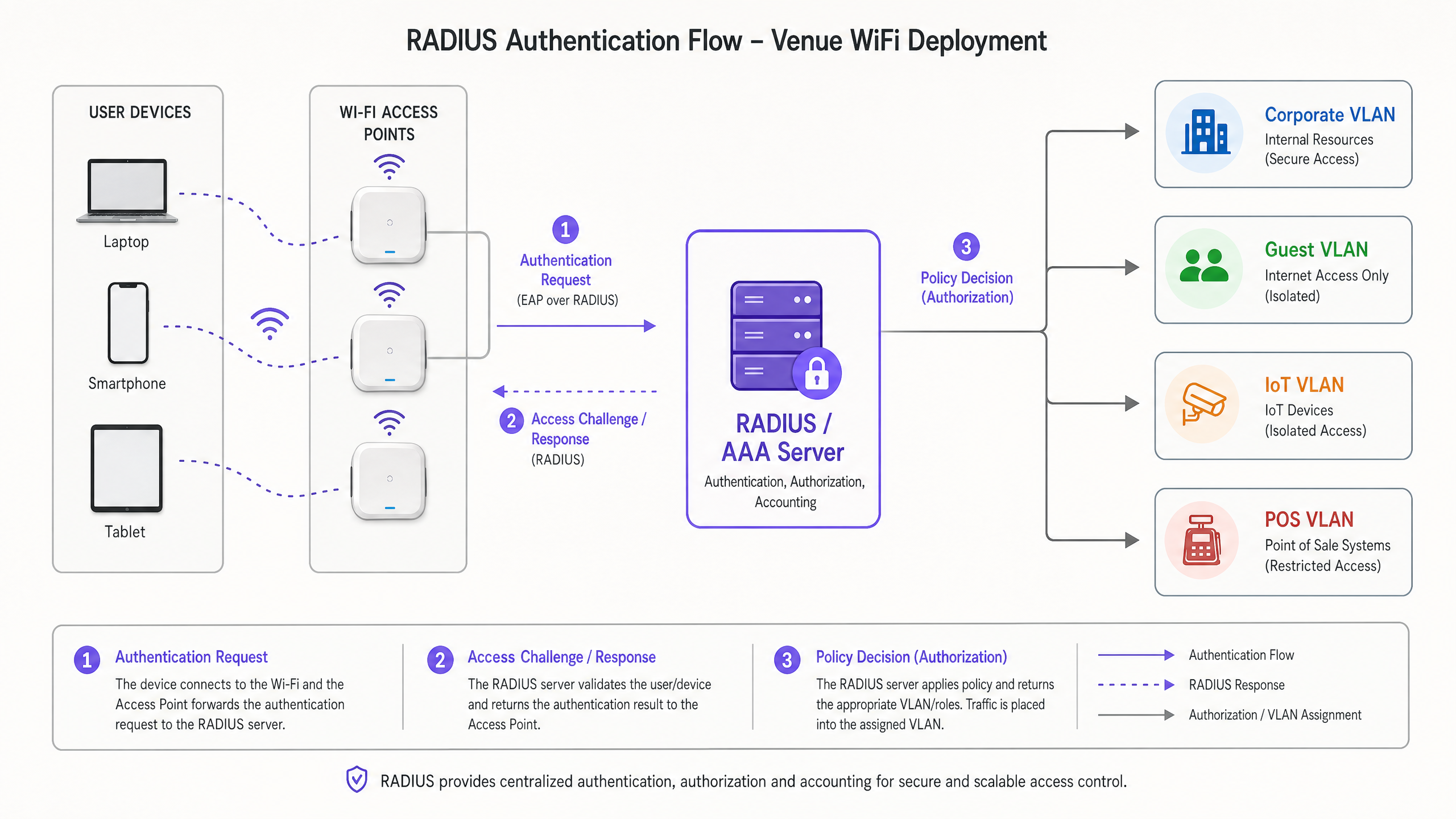
Cuando un dispositivo se conecta, el autenticador encapsula los mensajes del Protocolo de Autenticación Extensible (EAP) y los reenvía al servidor RADIUS. El servidor RADIUS evalúa las credenciales contra un almacén de identidades —como Active Directory, LDAP o un proveedor de identidad basado en la nube. Fundamentalmente, las implementaciones modernas de RADIUS no solo devuelven un mensaje de Access-Accept o Access-Reject. Devuelven Atributos Específicos del Proveedor (VSAs) que dictan el contexto de red del usuario: asignación de VLAN, aplicación de Listas de Control de Acceso (ACL) y parámetros de limitación de ancho de banda.
Para implementaciones empresariales, comprender Frecuencias Wi-Fi: Una Guía de Frecuencias Wi-Fi en 2026 es esencial, ya que las características de la capa física impactan directamente el rendimiento de los handshakes de autenticación en entornos de alta densidad.
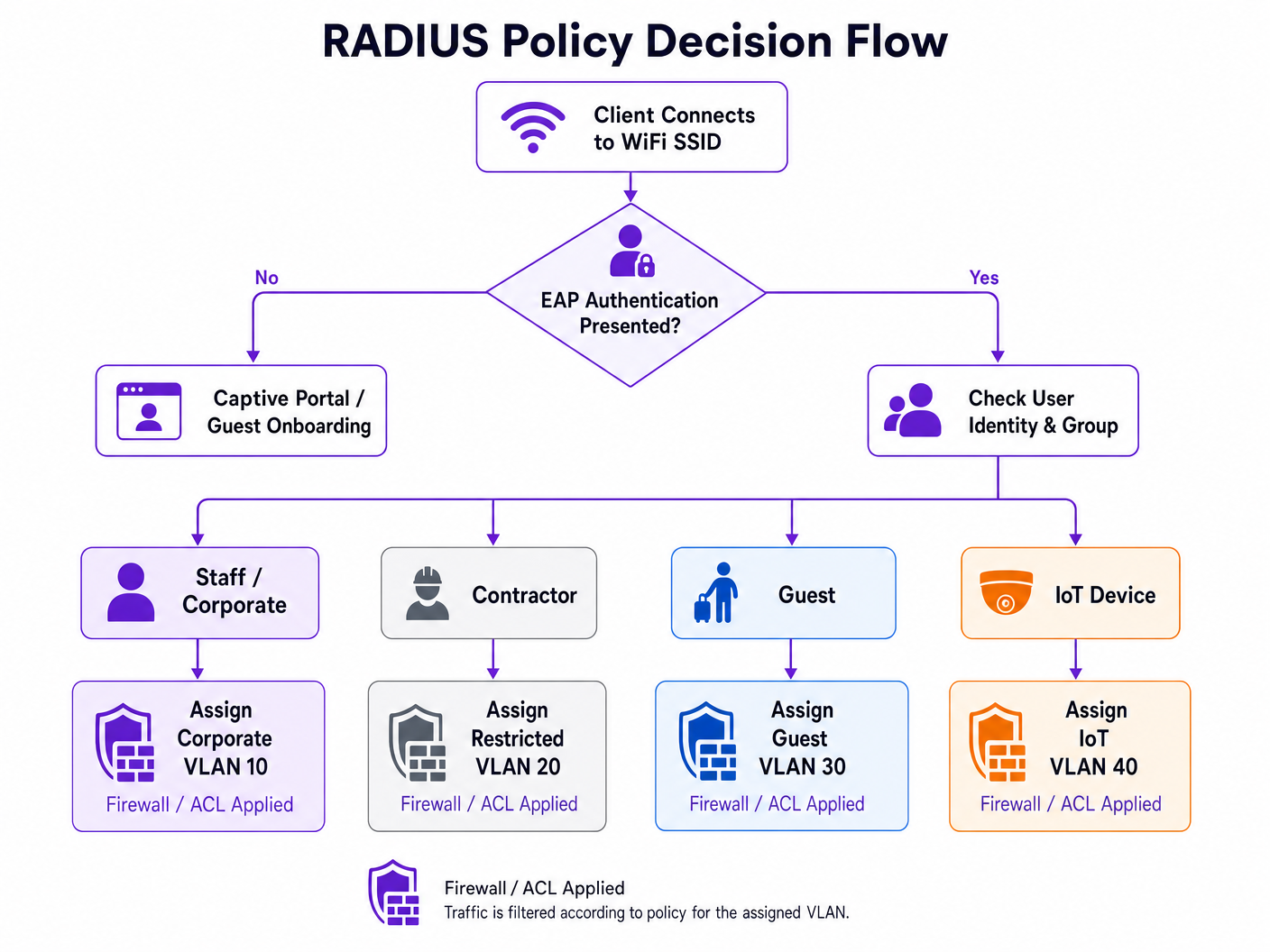
Asignación Dinámica de VLAN y Microsegmentación
La aplicación más potente de las políticas RADIUS es la asignación dinámica de VLAN. En lugar de transmitir múltiples SSIDs para diferentes grupos de usuarios —lo que degrada el rendimiento de RF debido a la sobrecarga de balizas— un único SSID habilitado para 802.1X puede servir a todos los usuarios corporativos. El servidor RADIUS determina la VLAN apropiada basándose en la membresía del grupo del usuario y factores contextuales.
Por ejemplo, cuando un miembro del equipo de finanzas se autentica, el servidor RADIUS instruye al punto de acceso para que coloque su tráfico en la VLAN 10. Cuando un dispositivo IoT se autentica a través de MAC Authentication Bypass (MAB), se coloca en una VLAN 40 aislada con ACLs estrictas. Este enfoque reduce drásticamente la superficie de ataque y simplifica el entorno de RF simultáneamente. Para implementaciones de proveedores específicos, consulte Cómo Configurar Políticas NAC para la Dirección de VLAN en Cisco Meraki .
Selección del Método EAP
La elección del método EAP tiene implicaciones significativas tanto para la postura de seguridad como para la complejidad operativa. La siguiente tabla resume las opciones clave:
| Método EAP | Mecanismo de Autenticación | Caso de Uso Recomendado | Nivel de Seguridad |
|---|---|---|---|
| EAP-TLS | Basado en certificado mutuo | Dispositivos corporativos gestionados con MDM | Más Alto |
| PEAP-MSCHAPv2 | Certificado de servidor + nombre de usuario/contraseña | BYOD, dispositivos del personal | Alto |
| EAP-TTLS | Certificado de servidor + credenciales internas | Entornos mixtos | Alto |
| MAB | Dirección MAC como credencial | IoT sin interfaz, dispositivos heredados | Bajo (usar con ACLs estrictas) |
Evite por completo los protocolos heredados como LEAP y EAP-MD5; son criptográficamente débiles y no deben aparecer en ninguna implementación moderna.
Guía de Implementación
La implementación de una infraestructura RADIUS robusta requiere una planificación meticulosa y una ejecución por fases. Los siguientes pasos describen un enfoque neutral al proveedor para configurar políticas RADIUS para un control de acceso a la red granular.
Fase 1: Integración de la Fuente de Identidad
La base de cualquier política es un directorio de identidades limpio y bien estructurado. Ya sea utilizando Active Directory local o soluciones nativas de la nube como Entra ID u Okta, los grupos del directorio deben mapearse directamente a sus segmentos de red previstos.
- Auditar Grupos Existentes: Asegúrese de que los grupos de usuarios sean lógicos y mutuamente excluyentes cuando sea posible. Elimine cuentas obsoletas y consolide grupos superpuestos.
- Definir Niveles de Acceso: Establezca niveles claros — Ejecutivo, Personal, Contratista, Invitado, IoT — con derechos de acceso documentados para cada uno.
- Integre Purple como Proveedor de Identidad: Para redes de cara al público, Purple actúa como un proveedor de identidad gratuito para servicios como OpenRoaming bajo la licencia Connect. Esto cierra la brecha sin problemas entre el acceso público a Guest WiFi y los marcos de autenticación seguros, eliminando la necesidad de un Captive Portal tradicional para los usuarios recurrentes.
Fase 2: Configuración de Políticas y Mapeo de Atributos
Configure el servidor RADIUS para evaluar las solicitudes entrantes basándose en múltiples factores contextuales, no solo en las credenciales.
- Protocolos de Autenticación: Exija EAP-TLS para dispositivos corporativos. Implemente PEAP-MSCHAPv2 para BYOD. Aplique estas políticas a través de la política RADIUS, rechazando las conexiones que intenten métodos más débiles.
- Coincidencia de Condiciones: Cree políticas que evalúen la
NAS-IP-Address(la IP del autenticador), laCalled-Station-Id(el SSID) y la hora del día. El perfil de acceso de un contratista a las 02:00 debería diferir sustancialmente de su perfil a las 09:00. - Perfiles de Aplicación: Defina los atributos RADIUS que se devolverán. Los atributos estándar de asignación de VLAN son:
Tunnel-Type=VLAN,Tunnel-Medium-Type=802yTunnel-Private-Group-Id=[VLAN_ID].
Fase 3: Implementación por Fases y Monitoreo
Nunca implemente la aplicación de 802.1X en toda una empresa simultáneamente.
- Modo de Monitoreo: Implemente políticas en modo de monitoreo o auditoría donde los fallos de autenticación se registran, pero el acceso aún se concede. Esto identifica suplicantes mal configurados y dispositivos heredados antes de que comience la aplicación.
- Aplicación Dirigida: Habilite la aplicación por ubicación o por departamento, resolviendo problemas antes de expandir el alcance.
- Integración de Análisis: Aproveche plataformas como WiFi Analytics de Purple para monitorear las tasas de éxito de autenticación, la duración de las sesiones y el comportamiento de roaming. Estos datos son críticos para identificar brechas de cobertura y cuellos de botella en la autenticación.
Mejores Prácticas
Al configurar políticas RADIUS para un control de acceso a la red granular, la adhesión a los estándares de la industria garantiza la estabilidad y seguridad a largo plazo.
Autenticación Basada en Certificados (EAP-TLS): Siempre que sea posible, implemente EAP-TLS. Elimina los riesgos asociados con el robo de credenciales y la fatiga de contraseñas. Las plataformas de Mobile Device Management (MDM) pueden automatizar el aprovisionamiento de certificados a escala.
Implementar Mitigación de Aleatorización de MAC: Los sistemas operativos móviles modernos utilizan la aleatorización de direcciones MAC para proteger la privacidad del usuario. Para implementaciones de Guest WiFi , asegúrese de que su Captive Portal y los sistemas de contabilidad RADIUS manejen los cambios de direcciones MAC de manera elegante, por ejemplo, confiando en tokens de sesión o perfiles de dispositivo persistentes generados durante la incorporación inicial.
Redundancia y Conmutación por Error: RADIUS es un componente crítico de la infraestructura. Implemente servidores RADIUS en clústeres de alta disponibilidad en ubicaciones geográficamente diversas. Configure los autenticadores con IPs de servidor primarias y secundarias, y establezca valores agresivos de tiempo de espera y reintento para minimizar los retrasos de autenticación durante los eventos de conmutación por error.
Aproveche los Datos Contextuales: Incorpore datos de ubicación en las decisiones de política. A un contratista se le podría conceder acceso a recursos internos cuando esté conectado a un AP en el bloque de ingeniería, pero restringido a acceso solo a internet cuando esté conectado en la cafetería. Las tecnologías discutidas en BLE Low Energy Explained for Enterprise pueden aumentar este contexto de ubicación con datos de posicionamiento de precisión.
Solución de Problemas y Mitigación de Riesgos
La complejidad de las implementaciones 802.1X introduce modos de fallo específicos. La mitigación proactiva de riesgos es esencial para mantener el tiempo de actividad.
Modos de Fallo Comunes
| Modo de Fallo | Causa Raíz | Mitigación |
|---|---|---|
| Fallo masivo de autenticación | Certificado de servidor RADIUS o CA raíz caducado | Gestión del ciclo de vida de los certificados con alertas automatizadas a los 90/60/30 días |
| Fallos de dispositivos individuales | Mala configuración del suplicante o CA raíz faltante | Perfiles inalámbricos enviados por MDM con almacén de confianza correcto |
| Tiempo de espera de EAP | Alta latencia WAN a RADIUS centralizado | Optimizar la ruta WAN; considerar RADIUS distribuido o proxy RADIUS |
| Fallos de dispositivos IoT | El dispositivo no es compatible con 802.1X | Implementar MAB con aislamiento estricto de VLAN y ACLs |
Para empresas distribuidas, la arquitectura discutida en SD WAN vs MPLS: The 2026 Enterprise Network Guide es directamente relevante para garantizar una conectividad de baja latencia a los servicios AAA centralizados en múltiples sitios.
ROI e Impacto Comercial
Invertir el esfuerzo de ingeniería requerido para configurar políticas RADIUS para un control de acceso a la red granular produce retornos sustanciales y medibles en múltiples dimensiones.
Reducción de la Carga Operativa: Consolidar múltiples SSIDs en una única red 802.1X con asignación dinámica de VLAN reduce la interferencia de RF, mejora el tiempo de aire disponible y simplifica la gestión continua. Los equipos reportan una reducción significativa en los tickets de soporte relacionados con la conectividad WiFi una vez que se implementa una implementación 802.1X estable.
Mejora de la Postura de Cumplimiento: Para sectores como Retail y Healthcare , la segmentación estricta de la red es un requisito regulatorio — PCI DSS y HIPAA respectivamente. Las políticas RADIUS proporcionan los controles verificables y auditables necesarios para pasar las auditorías de cumplimiento y evitar sanciones financieras sustanciales. Para las organizaciones del sector público, las obligaciones de GDPR en torno a la segregación de datos se abordan de manera similar.
Mejora de la Experiencia del Usuario: La autenticación segura y sin interrupciones — particularmente a través de EAP-TLS u OpenRoaming — elimina la fricción de los Captive Portals para los usuarios corporativos recurrentes y los invitados VIP. En lugares de Hospitality y Transport , esto impacta directamente en las métricas de satisfacción y la participación repetida.
Key Definitions
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorisation, and Accounting (AAA) management for users who connect and use a network service. Defined in RFC 2865.
The core engine for enterprise network access control, determining who gets on the network, what they can access, and logging the activity for audit purposes.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC). It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN, blocking all traffic until authentication is complete.
The standard that forces a device to prove its identity before it is allowed to send any data traffic on the network. The enforcement mechanism that makes RADIUS policies actionable.
EAP (Extensible Authentication Protocol)
An authentication framework frequently used in wireless networks and point-to-point connections. It provides a transport layer for authentication methods (EAP methods) such as TLS or MSCHAPv2.
The envelope that carries the actual authentication credentials between the client and the RADIUS server. The choice of EAP method determines the security level of the authentication exchange.
VSA (Vendor-Specific Attribute)
Attributes within a RADIUS message that allow vendors to support extended attributes not defined in the base RADIUS RFCs. Used to convey network policy instructions from the RADIUS server to the authenticator.
The mechanism by which RADIUS instructs network hardware to assign a user to a specific VLAN, apply a firewall role, or enforce bandwidth limits. Without VSAs, RADIUS can only permit or deny access.
Dynamic VLAN Assignment
The process where a RADIUS server instructs an access point or switch to place a user's traffic onto a specific Virtual LAN based on their identity, group membership, or contextual attributes.
The key technique for network micro-segmentation. Allows a single physical infrastructure to securely support multiple distinct user groups without broadcasting multiple SSIDs.
Supplicant
The software client on an end-user device (laptop, smartphone, IoT device) that initiates and negotiates the 802.1X authentication exchange with the network authenticator.
Built into modern operating systems (Windows, macOS, iOS, Android). Misconfigured supplicants — particularly incorrect certificate trust settings — are the most common source of 802.1X connectivity issues.
Authenticator
The network device (wireless access point or Ethernet switch) that acts as the enforcement point in an 802.1X deployment. It relays EAP messages between the supplicant and the RADIUS server, and enforces the policy decision.
The gatekeeper. The authenticator blocks all traffic from a port or wireless association until the RADIUS server returns an Access-Accept message, at which point it applies the returned VSAs.
MAB (MAC Authentication Bypass)
A fallback authentication method where the network device's MAC address is submitted as its credential to the RADIUS server. Used for devices that do not support 802.1X supplicants.
A necessary operational tool for legacy and headless IoT devices, but inherently less secure than cryptographic authentication. Should always be paired with strict VLAN isolation and ACLs.
EAP-TLS (EAP Transport Layer Security)
A certificate-based EAP method that provides mutual authentication between the client and the RADIUS server using X.509 certificates. Considered the most secure EAP method available.
The recommended authentication method for corporate-managed devices. Eliminates password-based credential risks entirely. Requires a PKI infrastructure and MDM for certificate provisioning.
Worked Examples
A large conference centre needs to provide secure, segmented WiFi access for event staff, exhibitors, and general attendees. They currently broadcast three separate SSIDs, which is causing significant co-channel interference and poor performance in high-density exhibition halls.
The venue transitions to a single, 802.1X-enabled SSID named 'Conference_Secure'. They implement a RADIUS server integrated with their event management database.
- Event staff authenticate using their corporate credentials via PEAP-MSCHAPv2. The RADIUS policy matches their Active Directory group and returns Tunnel-Private-Group-Id=10 (Staff VLAN), granting access to internal AV management systems.
- Exhibitors are provided unique, time-limited credentials tied to their stand booking. Upon authentication, the RADIUS server returns Tunnel-Private-Group-Id=20 (Exhibitor VLAN), which has ACLs permitting access to specific presentation servers and internet egress.
- General attendees use a separate open SSID with a captive portal integrated with Purple for marketing data collection, consent management, and basic internet access.
The result is a 40% reduction in management frame overhead, measurably improved throughput in exhibition halls, and a clear audit trail for compliance purposes.
A retail chain needs to secure thousands of wireless Point of Sale (POS) terminals across 500 locations. They are currently using WPA2-PSK, and IT is concerned about the operational risk of rotating the pre-shared key across 500 sites, as well as PCI DSS audit findings.
The IT team deploys a centralised RADIUS infrastructure and configures the POS terminals for EAP-TLS authentication.
- An MDM solution pushes a unique client certificate to each POS terminal during provisioning.
- The wireless access points at each store are configured to forward authentication requests to the central RADIUS servers over the SD-WAN fabric.
- The RADIUS policy verifies the client certificate against the internal PKI and returns attributes to place the device on the isolated POS VLAN (VLAN 50), satisfying PCI DSS network segmentation requirements.
- A certificate revocation list (CRL) is maintained, allowing IT to instantly quarantine a lost or stolen terminal by revoking its certificate — without impacting any other device.
Practice Questions
Q1. A hospital needs to deploy new wireless infusion pumps across three wards. These devices do not support 802.1X supplicants. The CISO requires that these devices are completely isolated from the corporate network and can only communicate with the specific clinical management server at 10.5.1.20. How should you configure the network access control policy?
Hint: Consider how devices without 802.1X capabilities can be identified and the principle of least privilege when defining the ACL.
View model answer
Implement MAC Authentication Bypass (MAB). Register the MAC addresses of all infusion pumps in the RADIUS database during the provisioning process. Create a specific RADIUS policy that matches these MAC addresses and returns VSAs assigning them to an isolated IoT VLAN (e.g., VLAN 60). Apply strict ACLs to this VLAN permitting outbound traffic only to 10.5.1.20 on the required clinical management ports, and blocking all other inter-VLAN and internet traffic. Additionally, configure DHCP snooping and dynamic ARP inspection on the IoT VLAN to prevent spoofing attacks.
Q2. Following a recent acquisition, an enterprise now has two distinct Active Directory domains: corp.acme.com and corp.legacy.com. They want all employees from both entities to use the same 'ACME_Corporate' SSID without migrating the legacy domain. How can RADIUS facilitate this?
Hint: Think about how RADIUS handles authentication routing based on the identity realm and how policy servers can proxy requests to different backend directories.
View model answer
Configure the RADIUS infrastructure (using a policy server such as Cisco ISE, Aruba ClearPass, or a RADIUS proxy) to evaluate the realm suffix provided in the user's EAP identity — for example, user@corp.acme.com versus user@corp.legacy.com . Create routing policies that forward authentication requests to the appropriate backend Active Directory domain based on the realm. Define standardised enforcement profiles that return consistent VLAN VSAs regardless of the backend domain, ensuring users from both entities receive the correct network placement. This approach avoids a disruptive directory migration while maintaining a unified user experience.
Q3. You are designing the WiFi for a 60,000-seat stadium. The client's current design specifies 8 separate SSIDs for different staff functions: Ticketing, Security, Concessions, Medical, Media, Operations, VIP, and Maintenance. What is your recommendation and why?
Hint: Consider the impact of management frame overhead on wireless performance in a high-density RF environment.
View model answer
Strongly advise against broadcasting 8 SSIDs. In a high-density environment, each SSID generates beacon frames on every access point at regular intervals, consuming significant airtime and reducing the capacity available for actual data traffic. The recommendation is to consolidate all staff functions onto a single 802.1X-enabled SSID. Utilise RADIUS dynamic VLAN assignment to segment the traffic on the backend — when a ticketing device authenticates, RADIUS places it on the Ticketing VLAN; when a medical device authenticates, it goes to the Medical VLAN with appropriate ACLs. This provides the required logical separation while optimising the physical RF environment. A separate open SSID with a captive portal can handle general public access.