Evaluación de Postura NAC: Garantizando el Cumplimiento de Dispositivos Administrados Antes del Acceso a la Red
Esta guía de referencia técnica ofrece una inmersión profunda en la Evaluación de Postura NAC, detallando la arquitectura, los estándares y las estrategias de implementación necesarias para hacer cumplir el cumplimiento de los dispositivos administrados. Equipa a los gerentes de TI y arquitectos de red con información práctica para mitigar riesgos y asegurar el acceso a la red en entornos empresariales multisitio.
Listen to this guide
View podcast transcript
- Resumen Ejecutivo
- Inmersión Técnica Profunda
- La Arquitectura de la Evaluación de Postura
- El Papel de IEEE 802.1X y EAP-TLS
- Categorías de Verificación de Postura
- WPA3-Enterprise y Fuerza Criptográfica
- Guía de Implementación
- Fase 1: Preparación de la Infraestructura y Diseño de PKI
- Fase 2: Modo de Monitoreo (Fase de Visibilidad)
- Fase 3: Aplicación Segmentada
- Fase 4: Arquitectura de Remediación
- Mejores Prácticas
- Solución de Problemas y Mitigación de Riesgos
- Modos de Fallo Comunes
- ROI e Impacto Empresarial

Resumen Ejecutivo
Para los líderes de TI empresariales que gestionan entornos complejos y multisitio, la identidad por sí sola ya no es una métrica suficiente para el acceso a la red. Saber quién se conecta es secundario a conocer el estado de seguridad del dispositivo que están utilizando. La evaluación de postura de Control de Acceso a la Red (NAC) es el mecanismo que cierra esta brecha, asegurando que solo los dispositivos administrados y conformes obtengan acceso a la infraestructura corporativa antes de que transmitan un solo paquete de tráfico de producción.
Esta guía proporciona una referencia técnica completa sobre el diseño, la implementación y la gestión de la evaluación de postura NAC. Exploramos la arquitectura subyacente —incluyendo 802.1X, RADIUS y EAP-TLS—, evaluamos las ventajas y desventajas entre la interrogación basada en agente y sin agente, y delineamos una estrategia de implementación por fases que minimiza la interrupción operativa. Ya sea que esté asegurando una sede corporativa, una red minorista distribuida o las operaciones internas en la hostelería, implementar una evaluación de postura robusta es un paso crítico en la mitigación de riesgos y la aplicación del cumplimiento.
Escuche nuestro podcast de resumen técnico de 10 minutos a continuación para obtener una visión general ejecutiva de los conceptos centrales y los errores comunes de implementación.
Inmersión Técnica Profunda
La Arquitectura de la Evaluación de Postura
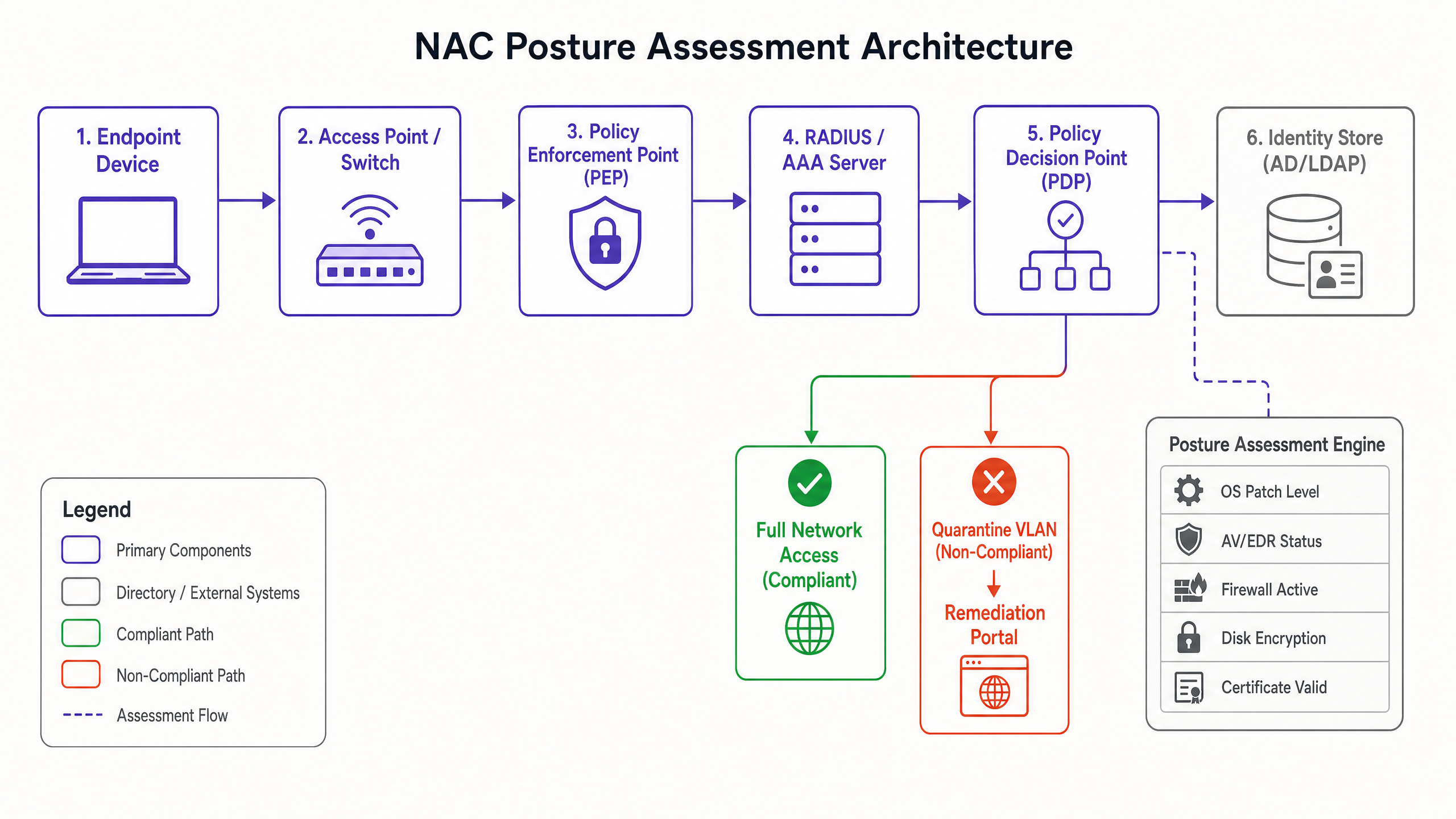
El Control de Acceso a la Red rige la conectividad de los dispositivos, pero la evaluación de postura es la interrogación específica del estado de seguridad de un dispositivo. La arquitectura se basa en tres componentes principales que trabajan en conjunto:
- Punto de Aplicación de Políticas (PEP): Este es el guardián físico o lógico —típicamente un punto de acceso inalámbrico, un puerto de switch o un controlador de LAN inalámbrica. El PEP controla físicamente el flujo de tráfico basándose en las instrucciones del motor de políticas.
- Punto de Decisión de Políticas (PDP): A menudo integrado dentro de un servidor RADIUS o AAA, el PDP es el cerebro de la arquitectura NAC. Recibe datos de postura, los evalúa contra las políticas de cumplimiento definidas y emite directivas de aplicación al PEP.
- Motor de Evaluación de Postura: Este componente recopila los datos de salud reales del punto final. Puede ser un agente ejecutándose localmente en el dispositivo o un mecanismo sin agente que aprovecha protocolos de red (por ejemplo, SNMP, WMI) o integraciones de API con plataformas de Gestión de Dispositivos Móviles (MDM).
El Papel de IEEE 802.1X y EAP-TLS
La base del NAC empresarial es el estándar IEEE 802.1X, que define el control de acceso a la red basado en puertos. Dentro de este marco, se definen tres roles:
- Solicitante: El dispositivo de punto final que intenta conectarse.
- Autenticador: El PEP (switch o punto de acceso) que facilita la conexión.
- Servidor de Autenticación: El servidor RADIUS que valida las credenciales.
La comunicación entre el Solicitante y el Servidor de Autenticación se realiza a través del Protocolo de Autenticación Extensible (EAP), tunelizado a través del Autenticador. Para dispositivos corporativos administrados, EAP-TLS es el estándar de oro. Exige autenticación mutua utilizando certificados digitales X.509, asegurando que tanto el dispositivo como la red verifiquen criptográficamente sus identidades. Esto previene el robo de credenciales y los ataques de puntos de acceso no autorizados.
Categorías de Verificación de Postura
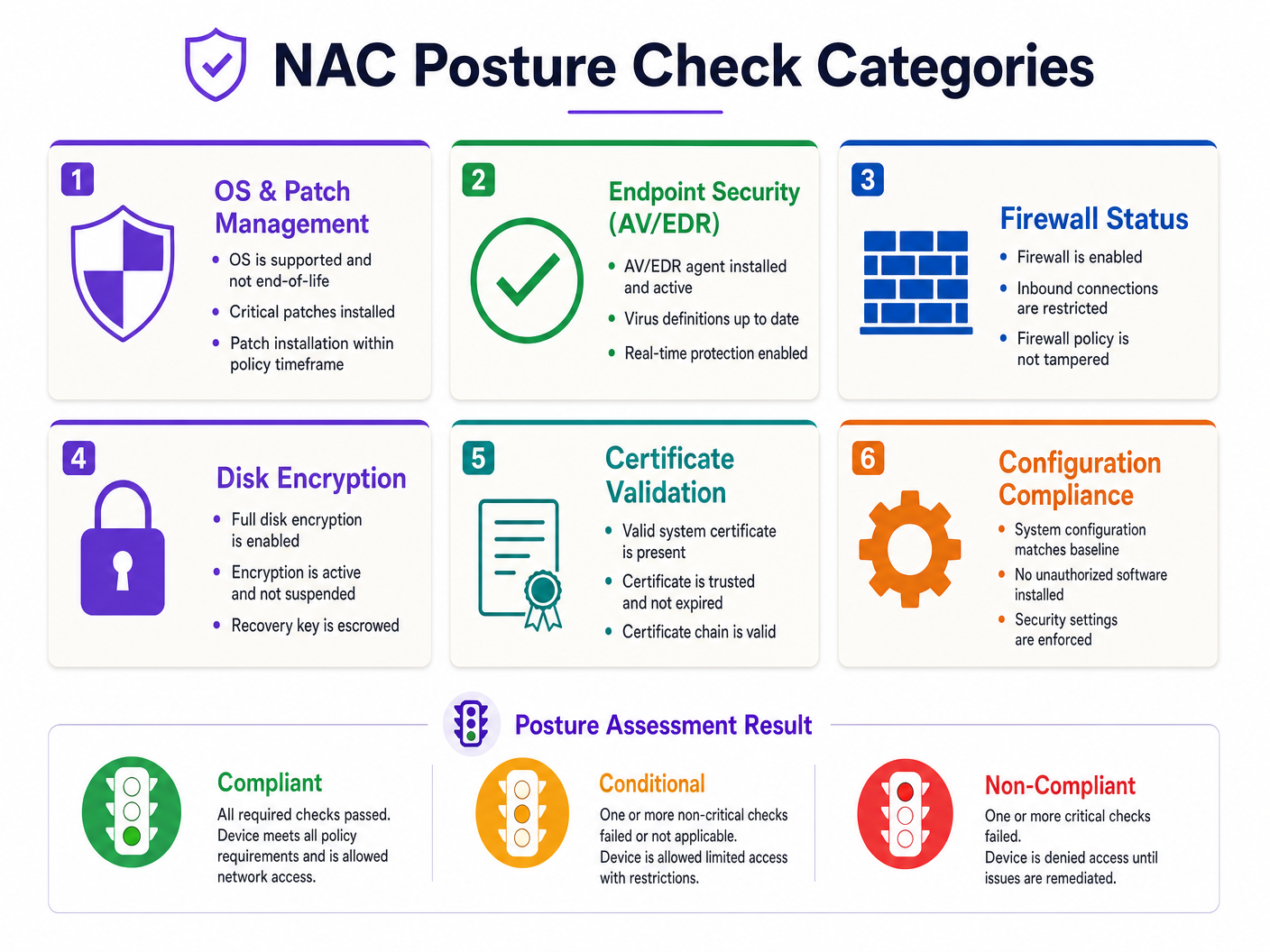
Cuando un dispositivo intenta conectarse, el motor de evaluación de postura evalúa varios vectores críticos:
- Gestión de SO y Parches: Verificando que el sistema operativo sea compatible y que los parches críticos se apliquen dentro del SLA definido.
- Seguridad de Punto Final (AV/EDR): Confirmando que los agentes antivirus o de Detección y Respuesta de Punto Final aprobados estén instalados, activos y con definiciones actualizadas.
- Estado del Firewall: Asegurando que el firewall basado en host esté habilitado y que su política no haya sido alterada.
- Cifrado de Disco: Validando que el cifrado de disco completo (por ejemplo, BitLocker, FileVault) esté activo y no en un estado suspendido.
- Validación de Certificado: Verificando la presencia y validez del certificado de máquina requerido.
- Cumplimiento de Configuración: Asegurando que la línea base de seguridad del dispositivo coincida con la política corporativa (por ejemplo, temporizadores de bloqueo de pantalla, almacenamiento masivo USB deshabilitado).
WPA3-Enterprise y Fuerza Criptográfica
A medida que la seguridad de la red evoluciona, también lo hacen los estándares criptográficos subyacentes. WPA3-Enterprise, particularmente cuando opera en modo de 192 bits, proporciona mejoras significativas sobre WPA2. Exige el uso de GCMP-256 para el cifrado y HMAC-SHA-384 para la integridad. Para organizaciones que manejan datos sensibles —como entornos de Retail sujetos a PCI DSS o instalaciones de Healthcare bajo una estricta gobernanza de datos—, la transición a WPA3-Enterprise es un paso necesario para preparar la infraestructura de red para el futuro.
Guía de Implementación
La implementación de la evaluación de postura NAC requiere una planificación cuidadosa para evitar interrupciones generalizadas de la red. Se recomienda el siguiente enfoque por fases para entornos empresariales:
Fase 1: Preparación de la Infraestructura y Diseño de PKI
Antes de habilitar las verificaciones de postura, asegúrese de que su infraestructura subyacente pueda respaldar la arquitectura. Si se implementa EAP-TLS, una Infraestructura de Clave Pública (PKI) robusta es innegociable. Los certificados deben aprovisionarse y renovarse automáticamente a través de su MDM o Política de Grupo. La gestión manual de certificados conducirá inevitablemente a fallos de conectividad cuando los certificados caduquen.
Fase 2: Modo de Monitoreo (Fase de Visibilidad)
La fase más crítica de cualquier implementación de NAC es el Modo de Monitoreo. En esta fase, el sistema NAC evalúa la postura del dispositivo y registra los resultados, pero no aplica la política. El PEP permite acceso completo independientemente del resultado de la postura.
Ejecute el Modo de Monitoreo durante un mínimo de 2 a 4 semanas. Esto proporciona visibilidad sobre el estado real de cumplimiento de su infraestructura. Identificará dispositivos que fallan las comprobaciones debido a agentes defectuosos, reinicios pendientes o configuraciones erróneas. Utilice estos datos para remediar la infraestructura de forma proactiva.
Fase 3: Aplicación Segmentada
Una vez que la línea base de cumplimiento sea aceptable, comience la aplicación. Los dispositivos se categorizan en tres estados según la evaluación de la política:
- Conforme: El dispositivo pasa todas las comprobaciones críticas y se asigna a la VLAN de producción con todo el acceso necesario.
- Condicional: El dispositivo falla una comprobación no crítica (por ejemplo, una actualización menor del sistema operativo está pendiente). Se le puede conceder acceso restringido (por ejemplo, solo a internet) y se notifica al usuario para que lo remedie en un plazo específico.
- No Conforme: El dispositivo falla una comprobación crítica (por ejemplo, AV deshabilitado). El PEP asigna el dispositivo a una VLAN de Cuarentena.
Fase 4: Arquitectura de Remediación
La VLAN de Cuarentena debe estar estrictamente aislada. Solo debe permitir el tráfico a un portal de remediación, servidores de actualización necesarios (por ejemplo, Windows Update, servidores de definiciones de AV) y recursos internos de soporte de TI. Si un dispositivo en cuarentena puede enrutar tráfico a subredes de producción, la arquitectura NAC ha fallado.
Mejores Prácticas
- Evaluación Continua: El NAC heredado evalúa la postura solo en el momento de la conexión. Las implementaciones modernas deben admitir la evaluación continua, reevaluando la postura a intervalos definidos o en respuesta a eventos (por ejemplo, una alerta de EDR), y actualizando dinámicamente el nivel de acceso del dispositivo a través de Cambio de Autorización (CoA).
- Con Agente vs. Sin Agente: Para dispositivos corporativos gestionados, un enfoque basado en agente proporciona la visibilidad más profunda y capacidades de monitoreo continuo. La interrogación sin agente es adecuada para dispositivos no gestionados o entornos donde la implementación de un agente es administrativamente prohibitiva.
- MAC Authentication Bypass (MAB): Los dispositivos incapaces de 802.1X (por ejemplo, impresoras antiguas, sensores IoT) requieren MAB. Sin embargo, MAB es inherentemente inseguro ya que las direcciones MAC pueden ser suplantadas. Los dispositivos MAB deben ser perfilados exhaustivamente y colocados en VLANs estrictamente controladas y aisladas.
- Alinearse con Estándares: Base sus políticas de postura en marcos establecidos como los CIS Benchmarks. Esto asegura que sus comprobaciones de cumplimiento sean neutrales al proveedor y estén alineadas con las mejores prácticas de la industria.
- Aislar el Tráfico de Invitados: La evaluación de la postura de NAC corporativa nunca debe cruzarse con las redes de acceso público. Para lugares que requieren ambos, utilice una plataforma dedicada de Guest WiFi , como la solución WiFi Analytics de Purple, para gestionar el acceso público en una infraestructura completamente separada.
Solución de Problemas y Mitigación de Riesgos
Modos de Fallo Comunes
- La Aplicación 'Big Bang': La transición del acceso abierto directamente a una aplicación estricta en toda la infraestructura simultáneamente es una receta garantizada para la interrupción operativa. Siempre utilice implementaciones por fases por sitio o departamento.
- Fallos de PKI: Los certificados raíz o intermedios caducados, o el fallo de la infraestructura de la Lista de Revocación de Certificados (CRL) / Protocolo de Estado de Certificado en Línea (OCSP), causarán fallos de autenticación generalizados. Implemente un monitoreo robusto para su PKI.
- Bucles de Remediación: Asegúrese de que los dispositivos en la VLAN de Cuarentena realmente tengan el acceso de red necesario para descargar las actualizaciones requeridas para cumplir con la normativa. Si no pueden alcanzar los servidores de actualización, permanecerán permanentemente en cuarentena.
ROI e Impacto Empresarial
La implementación de la evaluación de la postura NAC ofrece un valor empresarial medible más allá de las métricas de seguridad brutas:
- Mitigación de Riesgos: Al garantizar que solo los dispositivos saludables accedan a la red, la propagación lateral de malware y ransomware se reduce significativamente, disminuyendo la probabilidad de costosas filtraciones de datos.
- Verificación de Cumplimiento: Para sectores altamente regulados como Hospitality y Transport , la evaluación automatizada de la postura proporciona evidencia continua de cumplimiento con estándares como PCI DSS y GDPR, simplificando los procesos de auditoría.
- Eficiencia Operativa: La automatización del proceso de cuarentena y remediación reduce la carga de trabajo del servicio de asistencia de TI, permitiendo a los ingenieros centrarse en iniciativas estratégicas en lugar de limpiar manualmente los puntos finales infectados.
Key Definitions
802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol that ensures a device must authenticate before the switch port or access point allows any IP traffic to pass.
EAP-TLS
Extensible Authentication Protocol - Transport Layer Security. An authentication framework that uses X.509 digital certificates for mutual authentication.
The recommended standard for managed corporate devices, as it relies on cryptographic certificates rather than easily compromised passwords.
Posture Assessment
The process of evaluating the security state and configuration of an endpoint device against a defined corporate policy.
Ensures that a device is not only authenticated but is also 'healthy' (patched, encrypted, protected) before being granted network access.
Policy Enforcement Point (PEP)
The network device (switch, wireless controller, or access point) that physically blocks or allows traffic based on the NAC policy.
The component that actually executes the 'allow' or 'quarantine' command issued by the NAC server.
Policy Decision Point (PDP)
The central server or engine (often a RADIUS server) that evaluates authentication requests and posture data to determine access rights.
The brain of the operation that holds the rulebase and decides what level of access a specific device should receive.
MAC Authentication Bypass (MAB)
A fallback authentication method that uses a device's MAC address as its credential when it cannot perform 802.1X.
Used for headless devices like printers or IoT sensors. It is inherently weak and must be combined with strict network segmentation.
Change of Authorization (CoA)
A RADIUS extension that allows the NAC server to dynamically change the authorization state of an active session.
Crucial for continuous assessment; if a device becomes non-compliant while connected, CoA allows the NAC server to instantly move it to a quarantine VLAN without requiring a disconnect.
Quarantine VLAN
A strictly isolated network segment designed to hold non-compliant devices, providing access only to remediation resources.
Prevents an infected or vulnerable device from communicating with production systems while it downloads necessary updates or patches.
Worked Examples
A 400-room hotel requires corporate staff laptops to securely access the back-of-house property management system (PMS). However, the venue also hosts numerous unmanaged IoT devices (smart thermostats, digital signage) that cannot run a NAC agent.
Implement an 802.1X EAP-TLS policy for all corporate staff laptops, enforcing strict posture checks (AV active, disk encrypted, patched). These devices are dynamically assigned to the Corporate VLAN upon successful compliance. For the IoT devices, implement MAC Authentication Bypass (MAB) combined with deep device profiling. Ensure these MAB devices are placed in isolated, dedicated IoT VLANs with ACLs restricting their access solely to the specific controllers they need to communicate with. Under no circumstances should the IoT VLAN route to the Corporate VLAN or the PMS.
A retail chain is rolling out new point-of-sale (POS) terminals across 50 locations. The IT team wants to enforce posture compliance to meet PCI DSS requirements but is concerned about disrupting store operations during the rollout.
Deploy the NAC architecture in Monitor Mode for 30 days. During this period, the NAC system will authenticate the POS terminals and evaluate their posture against the PCI DSS baseline (e.g., firewall active, no unauthorized software) but will log failures without blocking access. The IT team reviews the logs weekly, identifies terminals failing the checks, and remediates them via the MDM platform. Once the compliance rate reaches 100%, the policy is switched to Enforcement Mode site-by-site during maintenance windows.
Practice Questions
Q1. A recently deployed NAC solution in a corporate office is causing widespread connectivity issues. Devices that were compliant yesterday are now being placed in the Quarantine VLAN. The IT helpdesk reports that the devices appear healthy, with AV running and patches applied. What is the most likely architectural failure?
Hint: Consider the lifecycle of the credentials used in EAP-TLS.
View model answer
The most likely cause is a failure in the Public Key Infrastructure (PKI). If the machine certificates used for EAP-TLS authentication have expired, or if the NAC server cannot reach the Certificate Revocation List (CRL) or OCSP responder, the authentication will fail regardless of the device's actual security posture. The NAC system defaults to a fail-closed or quarantine state.
Q2. You are designing the VLAN architecture for a new NAC deployment. The security team insists that the Quarantine VLAN must allow access to the corporate proxy server so users can browse the internet while their devices remediate. Is this a sound design?
Hint: Evaluate the risk of allowing a potentially compromised device access to shared infrastructure.
View model answer
No, this is a flawed design. Allowing a quarantined device access to the corporate proxy introduces significant risk. If the device is infected with malware, it could use the proxy to establish command-and-control communication or attempt to pivot to other internal systems accessible via the proxy. The Quarantine VLAN must be strictly isolated, permitting access only to specific remediation servers (e.g., Windows Update, AV definition servers) and the remediation portal itself.
Q3. A hospital IT team needs to secure network access for a fleet of new wireless medical infusion pumps. These devices do not support 802.1X supplicants and cannot run a posture agent. How should network access be controlled for these devices?
Hint: Consider alternative authentication methods and the principle of least privilege.
View model answer
The devices must be authenticated using MAC Authentication Bypass (MAB). Because MAB is inherently weak (MAC addresses can be spoofed), the network access must be heavily restricted. The infusion pumps should be placed in a dedicated, isolated Medical IoT VLAN. Access Control Lists (ACLs) must be applied to this VLAN, permitting communication only with the specific central management servers required for their operation, and blocking all other lateral movement or internet access.