¿Qué es IPSK? Claves Precompartidas de Identidad Explicadas
Esta guía técnica completa explica las Claves Precompartidas de Identidad (IPSK/DPSK), detallando cómo proporciona seguridad de nivel empresarial y direccionamiento dinámico de VLAN para unidades de vivienda múltiple (MDU) y alojamiento estudiantil sin la fricción de 802.1X.
Escucha esta guía
Ver transcripción del podcast
- Resumen Ejecutivo
- Análisis Técnico Detallado: ¿Qué es IPSK y cómo funciona?
- El Problema Arquitectónico con las PSK Compartidas
- La Solución IPSK
- Comparación: WPA2-Personal vs. IPSK vs. 802.1X
- Guía de Implementación: Despliegue de IPSK en Entornos MDU
- 1. Generación de Claves y Entropía
- 2. Aplicación del Límite de Dispositivos
- 3. Configuración de Direccionamiento Dinámico de VLAN
- 4. Integración con sistemas de gestión de propiedades (PMS)
- Mejores prácticas y estándares de la industria
- Solución de problemas y mitigación de riesgos
- Modos de falla comunes
- ROI e impacto empresarial
Escuche a nuestro arquitecto sénior de soluciones desglosar la arquitectura IPSK en esta sesión informativa de 10 minutos:
Resumen Ejecutivo
Para los administradores de propiedades y directores de TI que operan Unidades de Vivienda Múltiple (MDU), particularmente en alojamiento estudiantil, la gestión del acceso inalámbrico presenta un desafío único. Deben equilibrar la experiencia de incorporación de grado de consumidor que los residentes esperan con la seguridad, la rendición de cuentas y la segmentación de red de grado empresarial que exigen las normativas.
El WPA2-Personal estándar (una única contraseña compartida) no logra proporcionar la rendición de cuentas del usuario ni la segmentación dinámica de la red. Por el contrario, el 802.1X empresarial (RADIUS) ofrece una excelente seguridad, pero introduce una fricción significativa para la incorporación de dispositivos sin interfaz de usuario como consolas de videojuegos, televisores inteligentes y hardware IoT, comunes en entornos residenciales.
Claves Precompartidas de Identidad (IPSK), también conocidas como PSK Dinámicas (DPSK), cierra esta brecha. Proporciona la incorporación sin interrupciones de WPA2-Personal al tiempo que ofrece la rendición de cuentas por usuario, el direccionamiento dinámico de VLAN y la gestión granular del ciclo de vida, características típicamente reservadas para arquitecturas 802.1X. Esta guía detalla la mecánica técnica de IPSK, las estrategias de implementación y por qué es la arquitectura definitiva para las redes modernas de MDU y alojamiento estudiantil.
Análisis Técnico Detallado: ¿Qué es IPSK y cómo funciona?
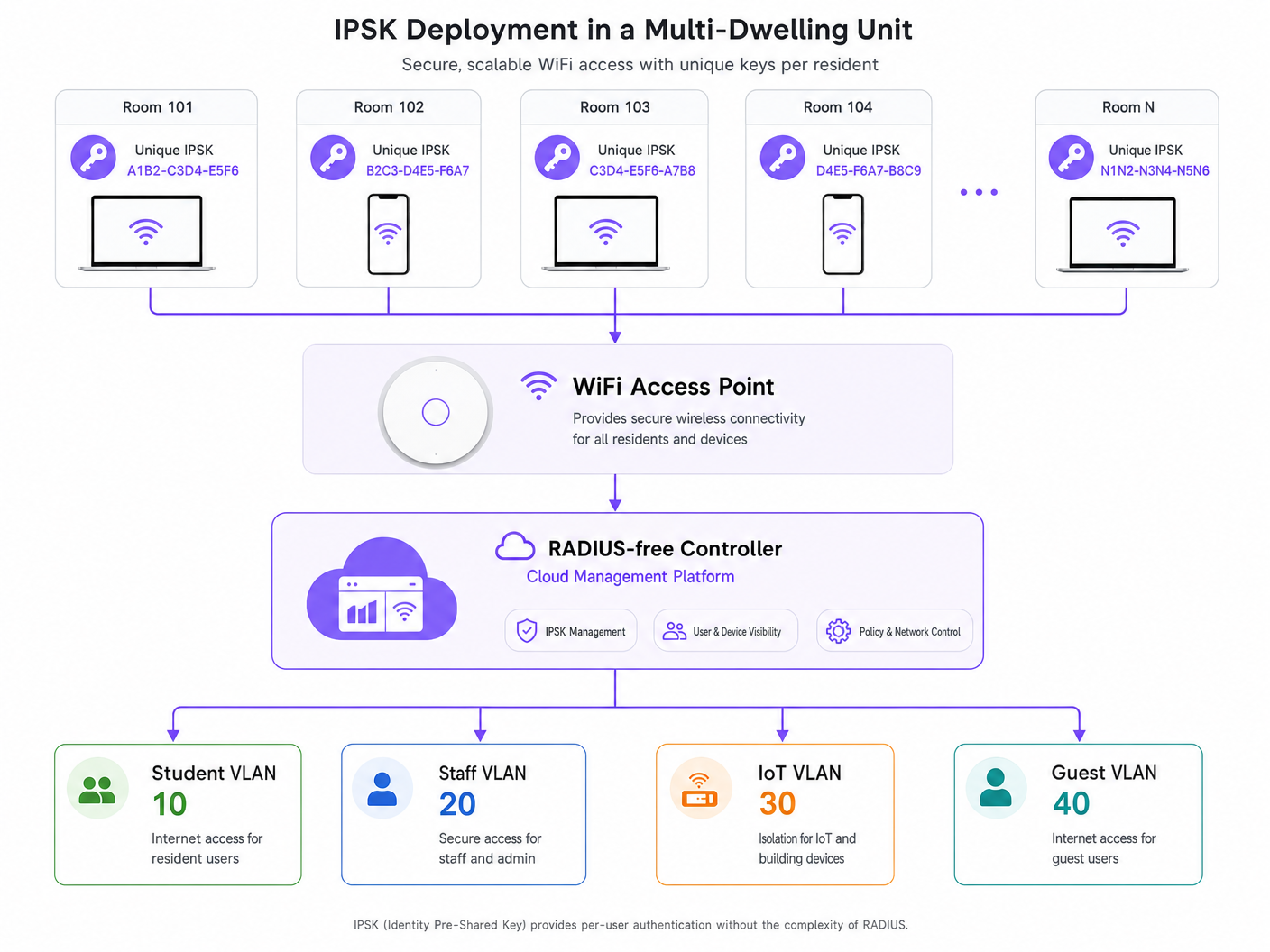
En su esencia, IPSK es un mecanismo de autenticación que permite que un único Service Set Identifier (SSID) admita múltiples Claves Precompartidas (PSK) únicas, donde cada clave está vinculada a una identidad específica (un usuario, una habitación o un grupo de dispositivos) a nivel del controlador.
El Problema Arquitectónico con las PSK Compartidas
En una implementación tradicional de WPA2-Personal, todos los clientes que se conectan al SSID utilizan la misma frase de contraseña. Esto crea varias vulnerabilidades arquitectónicas:
- Falta de Contexto de Identidad: La red no puede distinguir entre el tráfico del Residente A y el tráfico del Residente B en la capa de autenticación.
- Cero Segmentación de Red: Todos los dispositivos aterrizan en el mismo dominio de difusión (VLAN) a menos que se implementen anulaciones complejas basadas en MAC.
- Gestión del Ciclo de Vida Defectuosa: Revocar el acceso para un solo dispositivo comprometido o un residente que se marcha requiere cambiar la PSK global, forzando un evento de reconexión disruptivo en toda la red para todos los usuarios.
La Solución IPSK
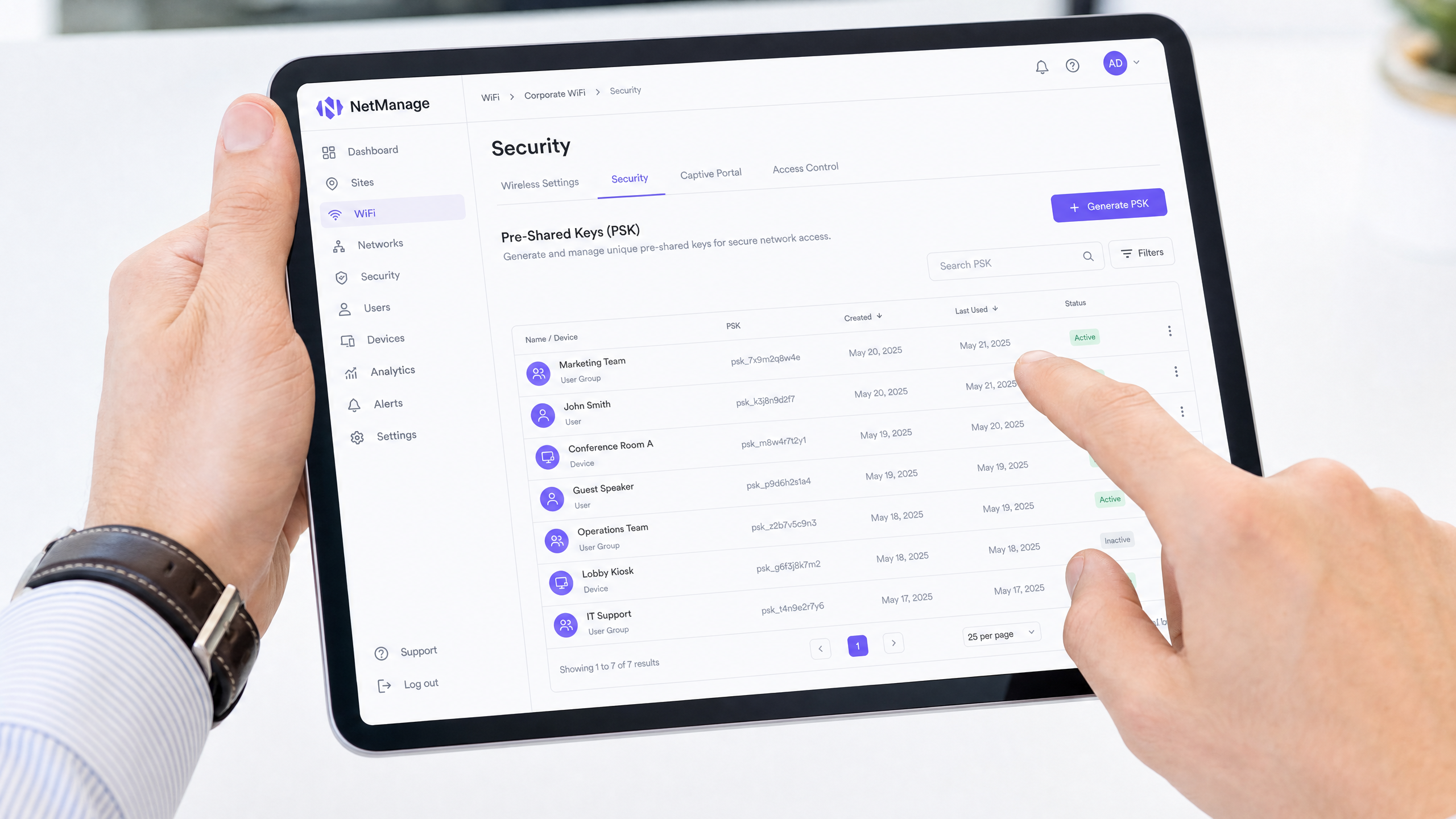
IPSK traslada la inteligencia del dispositivo de borde al controlador inalámbrico o a la plataforma de gestión en la nube.
Cuando un dispositivo se asocia con el SSID, presenta su PSK asignada. El punto de acceso reenvía esta solicitud al controlador. El controlador consulta su base de datos interna (o un proveedor de identidad externo a través de API) para validar la clave. Tras una validación exitosa, el controlador devuelve el perfil de autorización asociado con esa clave específica.
Este perfil de autorización típicamente dicta:
- Asignación de VLAN: Dirigir dinámicamente el dispositivo a un segmento de red específico (por ejemplo, VLAN 10 para la Habitación 101, VLAN 20 para la Habitación 102).
- Control de Acceso Basado en Roles (RBAC): Aplicar reglas de firewall específicas o Listas de Control de Acceso (ACL).
- Limitación de Tasa: Aplicar límites de ancho de banda por usuario o por habitación.
Debido a que la clave es única para el usuario, se logra una red basada en identidad sin requerir suplicantes 802.1X en los dispositivos cliente.
Comparación: WPA2-Personal vs. IPSK vs. 802.1X
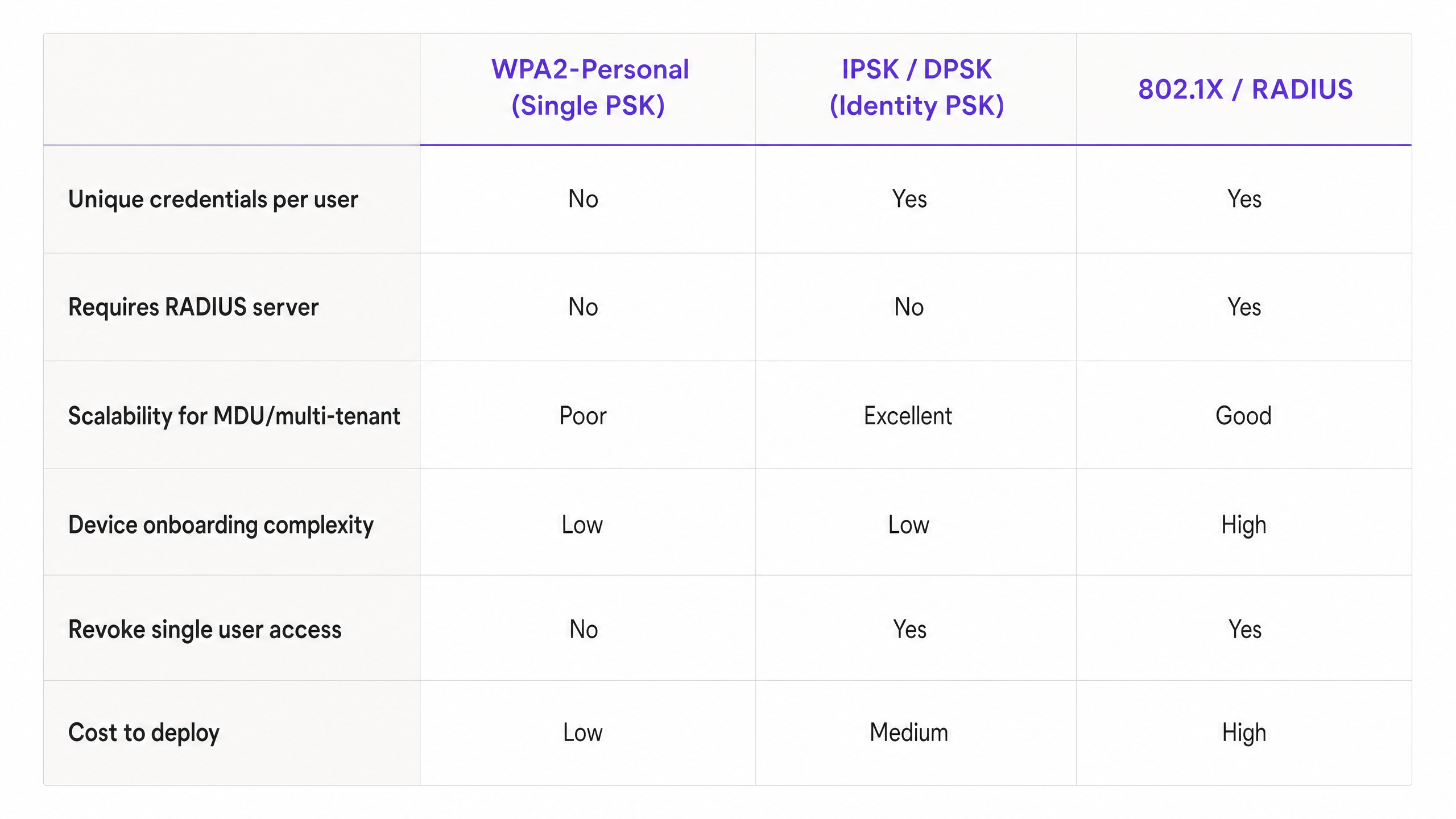
Comprender dónde encaja IPSK requiere compararlo con las alternativas. Si bien 802.1X sigue siendo el estándar de oro para espacios de oficina corporativos con alfombra (consulte nuestra guía sobre Office Wi Fi: Optimice Su Red Wi-Fi Moderna de Oficina ), a menudo es inapropiado para MDU debido a problemas de compatibilidad de dispositivos. IPSK ofrece los beneficios de seguridad de 802.1X con la simplicidad de WPA2-Personal.
Guía de Implementación: Despliegue de IPSK en Entornos MDU
El despliegue efectivo de IPSK requiere una planificación cuidadosa en torno a la generación, distribución y gestión del ciclo de vida de las claves.
1. Generación de Claves y Entropía
Las claves deben ser criptográficamente seguras. Evite usar números secuenciales, números de habitación o frases fáciles de adivinar. Genere claves programáticamente (mínimo 16-20 caracteres, alfanuméricos). Si está utilizando una plataforma como la solución Guest WiFi de Purple, esta generación puede automatizarse y vincularse al perfil del residente.
2. Aplicación del Límite de Dispositivos
Un paso de implementación crítico es aplicar un recuento máximo de dispositivos por IPSK. Si a un residente se le asigna una clave, debe estar restringido a un número razonable de autenticaciones concurrentes (por ejemplo, de 5 a 8 dispositivos). No aplicar esto permite que una sola clave filtrada sea utilizada por docenas de usuarios no autorizados, degradando el rendimiento de la red y comprometiendo el rastro de auditoría.
3. Configuración de Direccionamiento Dinámico de VLAN
Configure su controlador inalámbrico para mapear IPSK específicos a VLAN específicos. En un entorno de alojamiento estudiantil, la arquitectura típicamente se ve así:
- VLAN de Residentes: Ya sea una VLAN única por habitación (micro-segmentación) o una VLAN de residente compartida con aislamiento de cliente habilitado.
- VLAN de IoT: Para la gestión de edificios, termostatos inteligentes y balizas BLE (lea más sobre BLE Low Energy Explicado para Empresas ).
- VLAN de Personal/Administración: Acceso seguro para la gestión de propiedades.
EstoEl enfoque se detalla más a fondo en nuestra guía completa: Diseño de una arquitectura WiFi multi-inquilino para MDU .
4. Integración con sistemas de gestión de propiedades (PMS)
El verdadero ROI de IPSK se logra cuando el ciclo de vida de la clave está automatizado. Integre la API de su controlador inalámbrico con su PMS o base de datos de inquilinos.
- Aprovisionamiento: Cuando se firma un contrato de arrendamiento, una llamada a la API genera automáticamente una IPSK y la envía por correo electrónico al residente.
- Revocación: Cuando el contrato de arrendamiento finaliza, una llamada a la API revoca instantáneamente la clave, terminando el acceso a la red sin intervención de TI.
Mejores prácticas y estándares de la industria
- Transición a WPA3: Asegúrese de que su hardware sea compatible con WPA3-SAE (Simultaneous Authentication of Equals). WPA3 mejora significativamente la seguridad de las claves precompartidas al mitigar los ataques de diccionario fuera de línea y proporcionar secreto hacia adelante. Las implementaciones modernas de IPSK deben aprovechar WPA3 siempre que la compatibilidad del cliente lo permita.
- Aislamiento de clientes: Si está colocando a varios residentes en una VLAN compartida en lugar de VLAN por habitación, DEBE habilitar el Aislamiento de clientes (aislamiento de Capa 2) a nivel del AP para evitar movimientos laterales y ataques de igual a igual entre residentes.
- Cumplimiento: Para los operadores en los sectores de Hospitalidad o MDU, IPSK proporciona los registros de auditoría necesarios para cumplir con regulaciones como GDPR, ya que los flujos de red pueden atribuirse directamente a la credencial de un usuario específico.
Solución de problemas y mitigación de riesgos
Modos de falla comunes
1. Límites de escala del controlador Riesgo: Los controladores inalámbricos más antiguos o de nivel básico tienen límites estrictos en la cantidad de PSK únicos que pueden almacenar (por ejemplo, un máximo de 500 claves por SSID). Mitigación: Verifique la escala máxima de IPSK admitida por su hardware antes de la implementación. Para MDUs grandes, se requieren arquitecturas gestionadas en la nube (como Cisco Meraki o Aruba Central) o motores de políticas dedicados.
2. Latencia de Roaming Riesgo: Si la base de datos del controlador tarda en responder durante los eventos de roaming de AP a AP, las llamadas de voz y video se interrumpirán. Mitigación: Asegúrese de que la infraestructura del controlador esté localizada o sea altamente disponible. Habilite la Transición rápida de BSS (802.11r) si es compatible con su implementación de IPSK.
3. Acumulación de claves/claves obsoletas Riesgo: No revocar las claves cuando los residentes se van resulta en una base de datos inflada y una vulnerabilidad de seguridad masiva. Mitigación: Implemente la gestión automatizada del ciclo de vida mediante la integración de la API con su PMS. Realice auditorías trimestrales de las claves activas.
ROI e impacto empresarial
La transición a una arquitectura IPSK ofrece resultados empresariales medibles para los administradores de propiedades y los directores de TI:
- Reducción de la sobrecarga de soporte: La eliminación de problemas de configuración del suplicante 802.1X y la necesidad de bypass de autenticación MAC (MAB) para dispositivos sin interfaz reduce los tickets de Helpdesk hasta en un 60% durante el período crítico de incorporación de septiembre.
- Monetización mejorada: Al vincular la identidad al acceso a la red, los operadores pueden ofrecer paquetes de ancho de banda por niveles (por ejemplo, nivel básico incluido en el alquiler, nivel premium para jugadores).
- Análisis procesables: Con redes conscientes de la identidad, los administradores de propiedades pueden aprovechar WiFi Analytics para comprender la utilización del espacio, los tiempos de permanencia en áreas comunes y el compromiso general del edificio, de manera similar a las implementaciones en Retail y Transport .
IPSK no es solo una característica de seguridad; es la arquitectura fundamental que permite redes multi-inquilino seguras, escalables y manejables.
Definiciones clave
IPSK (Identity Pre-Shared Key)
An authentication method that allows multiple unique pre-shared keys to be used on a single SSID, with each key tied to a specific user policy or VLAN.
Used in MDUs to provide per-user security without the complexity of 802.1X.
DPSK (Dynamic Pre-Shared Key)
A vendor-specific (primarily Ruckus) term for the same underlying technology as IPSK.
You will encounter this term when evaluating different vendor data sheets.
Dynamic VLAN Steering
The process where a network controller automatically assigns a connecting device to a specific Virtual LAN based on the authentication credentials provided.
Essential for multi-tenant environments to isolate resident traffic from staff or IoT traffic on the same physical access points.
802.1X
The IEEE standard for port-based Network Access Control, requiring a RADIUS server and client supplicants.
The enterprise alternative to IPSK, but often unsuitable for residential environments due to headless device incompatibility.
Headless Device
A network-connected device lacking a web browser or advanced configuration interface (e.g., gaming consoles, smart TVs, IoT sensors).
These devices drive the requirement for IPSK, as they cannot navigate captive portals or configure 802.1X supplicants.
WPA3-SAE
Simultaneous Authentication of Equals, the secure key establishment protocol used in WPA3 to prevent offline dictionary attacks.
The modern security standard that should be paired with IPSK deployments on compatible hardware.
Client Isolation
A wireless network setting that prevents devices connected to the same AP from communicating directly with each other.
Mandatory security control if multiple residents are placed into a single shared VLAN.
MAC Authentication Bypass (MAB)
A fallback mechanism in 802.1X networks where a device's MAC address is used as its identity credential.
A cumbersome administrative process that IPSK eliminates by providing native PSK support for headless devices.
Ejemplos resueltos
A 400-bed student accommodation block currently uses a single WPA2-Personal password. Residents complain about poor performance, and IT cannot prevent departing students from continuing to use the network from the car park. They need to secure the network, segment traffic per room, and support gaming consoles without increasing helpdesk tickets.
Deploy an IPSK architecture on a single SSID. Integrate the wireless controller API with the property management system. Upon lease signing, generate a unique 20-character IPSK per resident. Configure the controller to dynamically steer each resident's key to a unique Per-Room VLAN. Set a device limit of 6 concurrent devices per key. Automate key revocation upon lease termination.
A boutique hotel wants to offer secure, segmented WiFi to guests but cannot rely on captive portals because guests increasingly travel with smart speakers and streaming sticks that cannot navigate web logins.
Implement IPSK tied to the hotel reservation system. When a guest checks in, the PMS triggers an API call to generate a unique IPSK valid only for the duration of their stay. The key is printed on the room key sleeve or sent via SMS. The network dynamically assigns their devices to a private VLAN for that specific room, allowing their phone to cast to the room's smart TV securely.
Preguntas de práctica
Q1. You are designing the network for a 200-unit build-to-rent property. The client wants to use 802.1X for maximum security. However, their demographic research shows residents bring an average of 3 headless devices (smart TVs, consoles) per unit. What is your architectural recommendation?
Sugerencia: Consider the operational overhead of onboarding 600 headless devices onto an 802.1X network.
Ver respuesta modelo
Recommend an IPSK architecture instead of 802.1X. While 802.1X provides excellent security, the 600 headless devices would require MAC Authentication Bypass (MAB), creating a massive administrative burden for the helpdesk. IPSK provides the necessary per-user accountability and VLAN segmentation while allowing headless devices to connect seamlessly using standard PSK methods.
Q2. During an IPSK deployment, the property manager requests that residents be allowed to choose their own custom WiFi passwords to improve the user experience. How do you respond?
Sugerencia: Think about cryptographic entropy and dictionary attacks.
Ver respuesta modelo
Advise strongly against this. User-selected passwords lack sufficient entropy and are vulnerable to dictionary attacks. In an IPSK environment, weak keys compromise the security of the entire SSID. Keys must be programmatically generated (minimum 16-20 random alphanumeric characters) and distributed securely via the property management system integration.
Q3. A network utilizing IPSK is experiencing IP address exhaustion in the main DHCP pool, despite the building only being at 60% occupancy. What configuration oversight likely caused this?
Sugerencia: Think about what happens if a key is shared freely.
Ver respuesta modelo
The network likely failed to enforce a Maximum Device Count per IPSK. Without a device limit, residents can share their unique key with non-residents or connect an unlimited number of devices, rapidly exhausting DHCP scopes and bandwidth. A strict concurrent device limit (e.g., 5-8 devices per key) must be enforced at the controller level.