Políticas BYOD Seguras para Redes WiFi del Personal
Esta guía autorizada proporciona a los líderes de TI un marco neutral en cuanto a proveedores para incorporar de forma segura los dispositivos personales del personal. Detalla las decisiones arquitectónicas críticas —incluyendo la segmentación de red, la autenticación EAP-TLS y la integración de MDM— necesarias para soportar BYOD sin comprometer la infraestructura corporativa central.
Escucha esta guía
Ver transcripción del podcast

Resumen Ejecutivo
El entorno empresarial moderno exige flexibilidad, y la expectativa del personal de acceso Bring Your Own Device (BYOD) ya no es negociable. Sin embargo, la integración de dispositivos personales no gestionados en las redes inalámbricas corporativas introduce riesgos significativos de seguridad y cumplimiento. Esta guía de referencia técnica proporciona a los arquitectos de red y directores de TI un marco robusto para implementar políticas BYOD seguras para las redes WiFi del personal. Describimos las decisiones arquitectónicas críticas, centrándonos en la segmentación de red, la autenticación IEEE 802.1X y la integración de Mobile Device Management (MDM). Al alejarse de las contraseñas compartidas y la autenticación basada en MAC hacia la identidad basada en certificados (EAP-TLS) y el cifrado WPA3-Enterprise, las organizaciones pueden proporcionar conectividad sin interrupciones sin comprometer su infraestructura central. Ya sea que opere en Retail , Healthcare , Hospitality o Transport , esta guía ofrece las mejores prácticas neutrales en cuanto a proveedores necesarias para asegurar el borde de su red mientras apoya la productividad del personal.
Escuche nuestro podcast complementario para un resumen ejecutivo sobre estos conceptos:
Análisis Técnico Detallado
Arquitectura de Red y Segmentación
El principio fundamental de cualquier implementación BYOD segura es una segmentación de red rigurosa. Los dispositivos personales nunca deben residir en la misma Virtual Local Area Network (VLAN) que la infraestructura corporativa, los sistemas de punto de venta (POS) o las bases de datos sensibles. Una VLAN BYOD dedicada actúa como una capa intermedia segura, lógicamente aislada tanto del núcleo corporativo como de la red Guest WiFi .
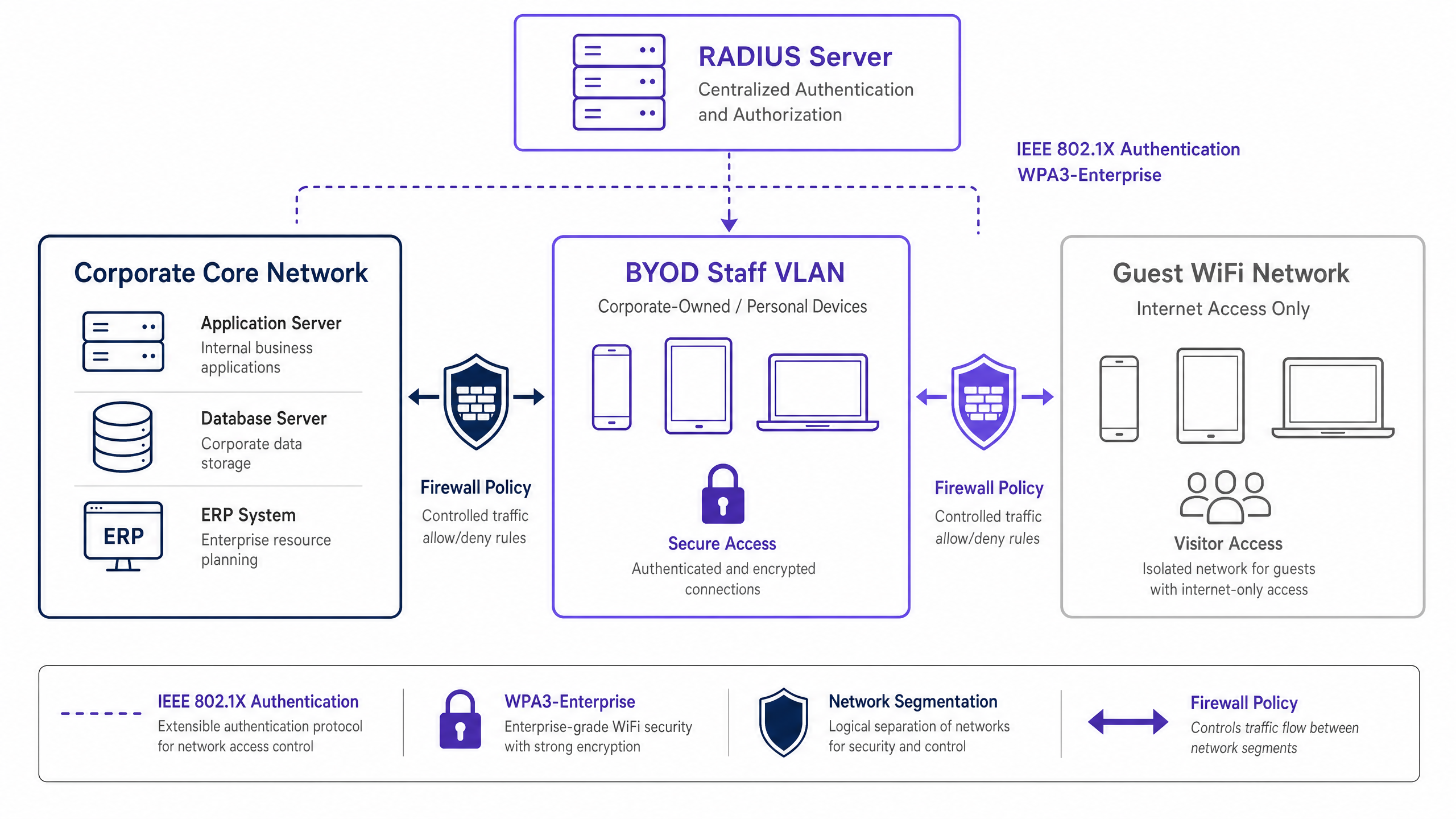
Esta segmentación asegura que, incluso si el dispositivo personal de un miembro del personal se ve comprometido, la amenaza está contenida. El acceso desde la VLAN BYOD a los recursos corporativos internos debe regirse por estrictas Listas de Control de Acceso (ACLs) del firewall, operando bajo un principio de denegación por defecto con permisos explícitos solo para los servicios requeridos (por ejemplo, portales de intranet o aplicaciones específicas en la nube).
Autenticación: El Estándar IEEE 802.1X
Asegurar el perímetro BYOD requiere una autenticación robusta. El estándar IEEE 802.1X proporciona control de acceso a la red basado en puertos, asegurando que los dispositivos sean autenticados antes de obtener acceso a la capa de red. Dentro del marco 802.1X, el Extensible Authentication Protocol with Transport Layer Security (EAP-TLS) es el estándar de oro para entornos BYOD.
EAP-TLS se basa en la autenticación mutua basada en certificados. En lugar de contraseñas vulnerables, el dispositivo presenta un certificado digital emitido por la Infraestructura de Clave Pública (PKI) de la organización. El servidor RADIUS valida este certificado, asegurando que tanto el dispositivo como la identidad del usuario sean verificados. Este enfoque mitiga los riesgos asociados con el robo de credenciales, el phishing y la sobrecarga operativa de los restablecimientos de contraseña.
Cifrado y Cumplimiento
Los datos en tránsito deben protegerse contra la interceptación. WPA3-Enterprise es el estándar actual para asegurar el tráfico inalámbrico, superando a WPA2 al eliminar vulnerabilidades como el ataque KRACK. WPA3-Enterprise exige el modo de seguridad de 192 bits para entornos altamente sensibles y proporciona secreto hacia adelante a través de Simultaneous Authentication of Equals (SAE). La implementación de WPA3-Enterprise es cada vez más un requisito obligatorio para los marcos de cumplimiento, incluyendo PCI DSS 4.0 y varios estándares de protección de datos de atención médica.
Además, el cumplimiento requiere una visibilidad integral. Cada evento de conexión en la red BYOD debe registrarse, capturando la identidad del dispositivo, la identidad del usuario, la marca de tiempo y la asignación de VLAN. Esta pista de auditoría es crítica para demostrar el cumplimiento de regulaciones como el Artículo 32 de GDPR. Para más contexto sobre los requisitos de registro, consulte nuestra guía sobre Explain what is audit trail for IT Security in 2026 .
Guía de Implementación
La implementación de una red BYOD segura requiere coordinación entre la política, la gestión de identidades y la infraestructura de red.

Implementación Paso a Paso
- Definición de Políticas: Antes de alterar la infraestructura, defina la política BYOD. Determine los grupos de usuarios elegibles, los tipos de dispositivos aprobados y los recursos corporativos específicos accesibles desde la VLAN BYOD. Obtenga la aprobación de los líderes legales, de RRHH y de seguridad.
- Integración de MDM y Aprovisionamiento de Certificados: Aproveche su plataforma Mobile Device Management (MDM) (por ejemplo, Intune, Jamf) para aprovisionar certificados EAP-TLS a los dispositivos del personal. Utilice el Simple Certificate Enrollment Protocol (SCEP) para automatizar esta entrega. El MDM también sirve como motor de aplicación para las comprobaciones de postura del dispositivo (por ejemplo, verificar los niveles de parches del sistema operativo y el estado de cifrado) antes de que se conceda el acceso a la red.
- Configuración de RADIUS: Configure el servidor RADIUS con políticas específicas para dispositivos BYOD. Cuando un dispositivo BYOD se autentica correctamente a través de su certificado, el servidor RADIUS debe devolver un atributo de asignación dinámica de VLAN (por ejemplo,
Tunnel-Private-Group-ID) para colocar el dispositivo en la VLAN BYOD aislada. - Configuración de la Infraestructura Inalámbrica: Implemente la asignación dinámica de VLAN en su Service Set Identifier (SSID) corporativo existente. Esto proporciona una experiencia de usuario fluida —el personal "se conectan a una red, y la infraestructura los dirige a la VLAN adecuada según su identidad autenticada.
- Firewall y Control de Acceso: Aplique ACLs estrictas en el límite entre la VLAN BYOD y el núcleo corporativo. Documente cada regla de permiso y establezca un proceso de revisión trimestral para evitar la expansión descontrolada del alcance.
- Monitoreo y Análisis: Integre los registros de conexión BYOD con su sistema de Gestión de Información y Eventos de Seguridad (SIEM). Utilice plataformas como WiFi Analytics para monitorear el rendimiento de la red, la distribución de dispositivos y posibles anomalías.
Mejores Prácticas
- Abandone la Autenticación Basada en MAC: Los sistemas operativos móviles modernos (iOS, Android) aleatorizan las direcciones MAC para proteger la privacidad del usuario. Esto rompe la autenticación y el seguimiento tradicionales basados en MAC. Confíe exclusivamente en la identidad basada en certificados (EAP-TLS) vinculada al usuario, no a la dirección de hardware.
- Aplique la Evaluación de Postura: Una política BYOD está incompleta sin verificaciones de postura. Asegúrese de que su solución de Control de Acceso a la Red (NAC) consulte al MDM para verificar que los dispositivos cumplan con las líneas de base de seguridad mínimas (por ejemplo, no liberados, bloqueo de pantalla habilitado) antes de otorgar acceso. Los dispositivos no conformes deben ser dirigidos a una VLAN de remediación.
- Automatice la Gestión del Ciclo de Vida de los Certificados: Los certificados caducan. Configure su MDM para renovar automáticamente los certificados mucho antes de su vencimiento (por ejemplo, 30 días antes) para evitar fallas masivas de conectividad. Además, integre la revocación de certificados con su proceso de desvinculación de RRHH para terminar el acceso inmediatamente cuando un empleado se va.
- Mantenga un Aislamiento Estricto: Asegure un aislamiento absoluto entre la VLAN BYOD y la red de invitados. Un dispositivo comprometido en la red de invitados no debe tener una ruta de movimiento lateral hacia los dispositivos del personal. Para solucionar problemas de acceso de invitados, consulte Solving the Connected but No Internet Error on Guest WiFi .
Solución de Problemas y Mitigación de Riesgos
- Expansión Descontrolada del Alcance de las Reglas del Firewall: El modo de falla más común en las implementaciones BYOD es la erosión gradual de la segmentación de la red. Las reglas de acceso temporales se vuelven permanentes, fusionando efectivamente las redes BYOD y corporativas. Mitigación: Implemente un proceso riguroso de gestión de cambios para las reglas del firewall BYOD y realice revisiones trimestrales obligatorias.
- Interrupciones por Caducidad de Certificados: La falta de gestión de los ciclos de vida de los certificados provoca caídas repentinas de conectividad para grandes grupos de personal. Mitigación: Implemente la renovación automatizada a través de SCEP/MDM y configure alertas proactivas para las caducidades inminentes.
- Desvinculación Incompleta: El acceso persistente para exempleados es una vulnerabilidad de seguridad crítica. Mitigación: Automatice la revocación del certificado del usuario en la PKI en el momento en que su estado cambie en el sistema de RRHH.
ROI e Impacto Empresarial
La implementación de una arquitectura BYOD segura requiere una inversión inicial en infraestructura NAC, MDM y RADIUS. Sin embargo, el retorno de la inversión (ROI) es sustancial:
- Mitigación de Riesgos: Al aislar los dispositivos no gestionados, la organización reduce drásticamente la superficie de ataque para ransomware y el movimiento lateral, protegiendo los activos críticos y evitando costosas filtraciones de datos.
- Eficiencia Operativa: La autenticación basada en certificados elimina la sobrecarga del servicio de asistencia de TI asociada con los restablecimientos de contraseñas y la gestión de credenciales compartidas.
- Productividad del Personal: Proporcionar acceso seguro y sin interrupciones a los recursos necesarios en dispositivos personales mejora la satisfacción y la productividad del personal, particularmente en entornos dinámicos como pisos de venta o salas de hospital.
- Garantía de Cumplimiento: El registro de auditoría completo y el cifrado robusto aseguran que la organización cumpla con los requisitos regulatorios, evitando posibles multas y daños a la reputación.
A medida que las organizaciones expanden su huella digital, la conectividad segura sigue siendo primordial. Iniciativas como la integración de ciudades inteligentes, impulsadas por líderes de la industria (ver Purple Appoints Iain Fox as VP Growth – Public Sector to Drive Digital Inclusion and Smart City Innovation ), dependen de arquitecturas de seguridad fundamentales robustas. Además, garantizar una navegación fluida dentro de grandes recintos, respaldada por características como Purple Launches Offline Maps Mode for Seamless, Secure Navigation to WiFi Hotspots , depende de una infraestructura de red subyacente confiable y segura.
Definiciones clave
IEEE 802.1X
An IEEE standard for port-based Network Access Control (PNAC). It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol used to authenticate staff devices before they are allowed onto the BYOD network.
EAP-TLS (Extensible Authentication Protocol-Transport Layer Security)
An EAP method that relies on client and server certificates to establish a secure mutual authentication tunnel.
Considered the most secure authentication method for BYOD, as it eliminates the reliance on vulnerable user passwords.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The backend server that evaluates the 802.1X requests from access points and decides whether to grant a device access to the network.
Dynamic VLAN Assignment
A network configuration where the RADIUS server dictates which VLAN a user or device should be placed in upon successful authentication, rather than hardcoding the VLAN to the SSID.
Allows organizations to broadcast a single SSID while securely separating traffic (e.g., corporate vs. BYOD) based on the user's identity.
MAC Address Randomization
A privacy feature in modern mobile OSs where the device uses a randomly generated MAC address instead of its true hardware address when scanning for or connecting to networks.
This feature renders legacy MAC-based authentication methods obsolete, forcing a shift to identity-based authentication like 802.1X.
MDM (Mobile Device Management)
Software that allows IT administrators to control, secure, and enforce policies on smartphones, tablets, and other endpoints.
Used in BYOD deployments to push network certificates to devices and verify their security posture (e.g., patch level) before allowing network access.
WPA3-Enterprise
The latest generation of Wi-Fi security, providing robust encryption and requiring 802.1X authentication for enterprise networks.
Mandatory for modern secure deployments to protect data in transit against advanced cryptographic attacks.
Posture Assessment
The process of evaluating a device's security state (e.g., OS version, antivirus status, encryption) before granting it network access.
Ensures that a staff member's personal device isn't harboring malware or running an outdated OS before it connects to the BYOD VLAN.
Ejemplos resueltos
A 400-bed hospital needs to allow nursing staff to use personal smartphones to access a secure internal scheduling application, but these devices must be strictly isolated from the clinical network containing patient records (EHR) and medical devices.
The hospital implements a dedicated BYOD VLAN. They deploy an MDM solution to push EAP-TLS certificates to staff smartphones. The wireless infrastructure uses 802.1X authentication; when a nurse connects, the RADIUS server validates the certificate and assigns the device to the BYOD VLAN. A firewall sits between the BYOD VLAN and the clinical network, with a strict default-deny policy. A single explicit permit rule allows HTTPS traffic from the BYOD VLAN to the specific IP address of the scheduling application server.
A national retail chain with 150 stores wants store managers to access inventory dashboards on their personal tablets. The chain currently uses WPA2-Personal with a shared password for staff WiFi, which is frequently shared with non-managers.
The retailer phases out the shared password SSID. They implement a centralized RADIUS server and integrate it with their Azure AD. They use their MDM to deploy certificates to approved manager tablets. The stores broadcast a single corporate SSID. Managers authenticate via 802.1X (EAP-TLS) and are dynamically assigned to a 'Manager BYOD' VLAN, which has firewall rules permitting access to the centralized inventory dashboard. Non-managers without certificates cannot connect.
Preguntas de práctica
Q1. Your organization is rolling out a BYOD program. The network team proposes using WPA2-Personal with a complex, rotating pre-shared key (PSK) that changes monthly, arguing it is simpler to deploy than 802.1X. As the IT Director, how should you respond?
Sugerencia: Consider the requirements for individual accountability and the operational overhead of offboarding an employee mid-month.
Ver respuesta modelo
Reject the proposal. A PSK, even a rotating one, provides no per-device or per-user accountability. If an employee leaves mid-month, the key must be changed immediately, disrupting all other users. You must mandate IEEE 802.1X (preferably EAP-TLS) to ensure individual authentication, enabling immediate, targeted revocation of access without affecting the rest of the staff.
Q2. A staff member reports they cannot connect their new personal iPhone to the BYOD network. Your RADIUS logs show authentication failures, but the user insists they have the correct profile installed. The logs indicate the device is presenting a different MAC address on each connection attempt. What is the root cause and the architectural fix?
Sugerencia: Modern mobile operating systems implement privacy features that affect layer 2 identification.
Ver respuesta modelo
The root cause is MAC address randomization, a default privacy feature in modern iOS and Android devices. The architectural fix is to completely decouple authentication and policy enforcement from MAC addresses. The network must rely solely on the cryptographic identity provided by the EAP-TLS certificate for authentication and subsequent session tracking.
Q3. During a security audit, the auditor notes that the BYOD VLAN has a firewall rule permitting all traffic (Any/Any) to the corporate subnet housing the HR database, citing a temporary requirement from six months ago that was never removed. What process failure occurred, and how is it remediated?
Sugerencia: Focus on the lifecycle of firewall rules and the principle of least privilege.
Ver respuesta modelo
The failure is 'firewall rule scope creep' and a lack of lifecycle management for access controls. The remediation is two-fold: First, immediately remove the Any/Any rule and replace it with an explicit permit only for the required ports/protocols (if access is still needed). Second, implement a mandatory quarterly review process for all ACLs governing traffic between the BYOD VLAN and the corporate core to ensure temporary rules are purged.