WiFi familiar: Mejores prácticas para centros comerciales
Esta guía de referencia técnica proporciona metodologías accionables para implementar el filtrado de URL basado en categorías en redes WiFi de invitados en entornos minoristas. Detalla la arquitectura de red, la definición de políticas y las estrategias de mitigación de riesgos para garantizar el cumplimiento y proteger la reputación de la marca.
Escucha esta guía
Ver transcripción del podcast
- Resumen Ejecutivo
- Análisis Técnico Detallado
- Arquitectura de Filtrado DNS
- Segmentación y Aislamiento de Red
- Estándares de Cifrado y Autenticación
- Guía de Implementación
- 1. Auditoría y Línea Base
- 2. Definir la Política de Categorías
- 3. Abordar DNS sobre HTTPS (DoH)
- 4. Aplicación y Manejo de Excepciones
- Mejores Prácticas
- Solución de Problemas y Mitigación de Riesgos
- Bloqueo Excesivo (Falsos Positivos)
- Elusión de DoH
- Problemas con el Captive Portal
- ROI e Impacto Comercial

Resumen Ejecutivo
Proporcionar WiFi público en entornos minoristas requiere equilibrar una conectividad fluida con una sólida mitigación de riesgos. Para los centros comerciales, implementar WiFi familiar no es simplemente una característica, es un requisito básico para las operaciones del lugar. Esta guía detalla la arquitectura técnica, las metodologías de implementación y las mejores prácticas operativas para el filtrado de URL basado en categorías en redes de invitados. Al aplicar controles de contenido a nivel de DNS, los gerentes de TI y los arquitectos de red pueden garantizar el cumplimiento, proteger la reputación de la marca y proporcionar un entorno de navegación seguro para todos los grupos demográficos. Además, una implementación de Guest WiFi correctamente estructurada transforma un centro de costos en un activo estratégico, capturando datos de primera parte que impulsan la lealtad y los ingresos, al tiempo que mitiga el riesgo de tráfico malicioso y acceso a contenido inapropiado.
Análisis Técnico Detallado
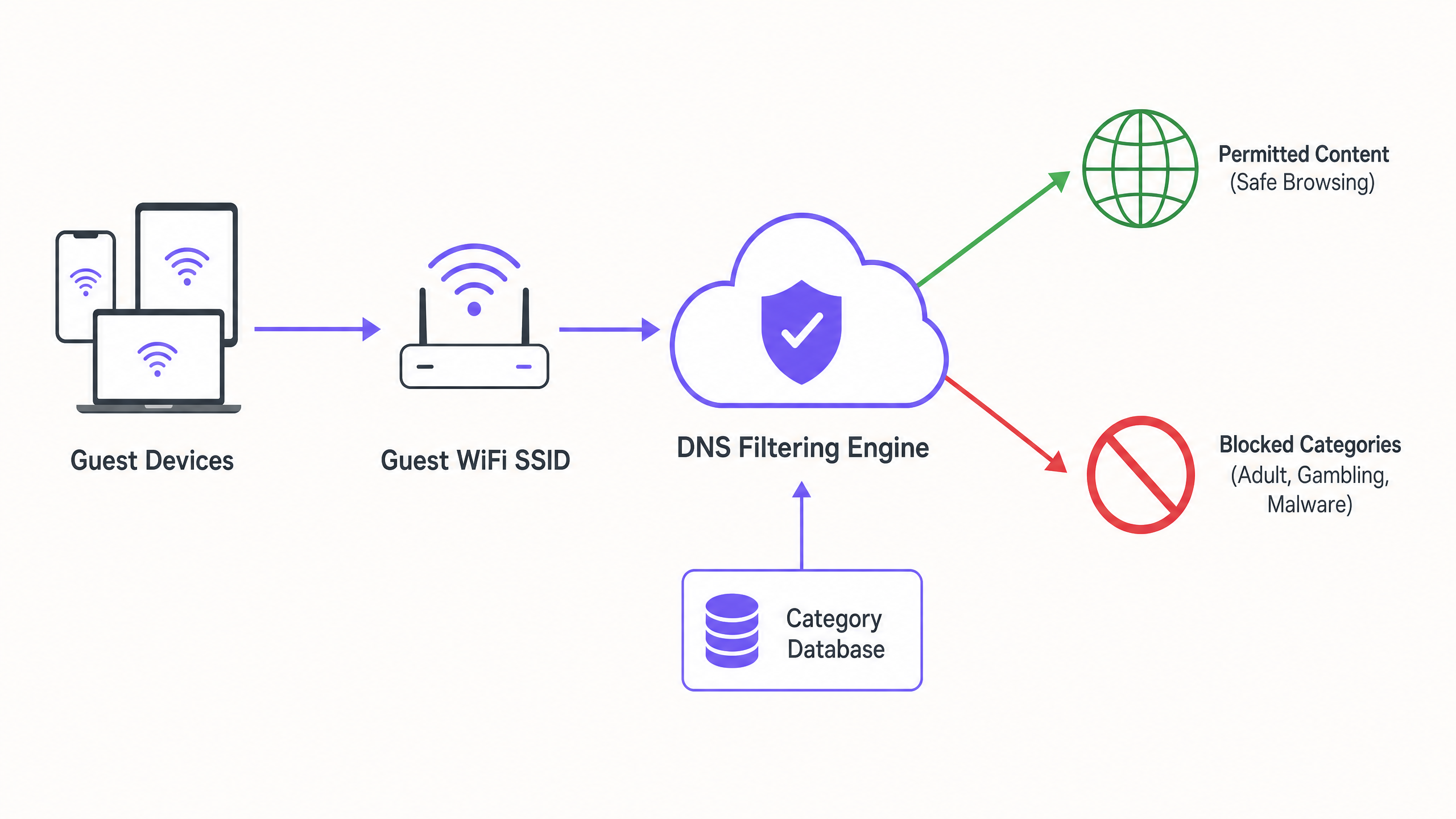
Arquitectura de Filtrado DNS
En el núcleo de una red familiar se encuentra el filtrado DNS basado en categorías. A diferencia del filtrado de URL a nivel de aplicación o la inspección profunda de paquetes (DPI), que requieren una sobrecarga de procesamiento significativa y a menudo rompen el cifrado SSL, el filtrado DNS opera en la capa de red. Cuando un dispositivo cliente intenta resolver un dominio, la consulta es interceptada por un motor de filtrado DNS basado en la nube. El motor coteja el dominio solicitado con una base de datos de URL categorizadas que se actualiza continuamente. Si el dominio cae en una categoría prohibida (por ejemplo, malware, contenido para adultos), la resolución se bloquea y el usuario es redirigido a una página de bloqueo.
Este enfoque ofrece un alto rendimiento y baja latencia, lo que lo hace altamente escalable para entornos densos como centros comerciales donde miles de conexiones concurrentes son comunes. Es crucial comprender ¿Qué es el filtrado DNS? Cómo bloquear contenido dañino en Guest WiFi para diseñarlo correctamente.
Segmentación y Aislamiento de Red
Un requisito de seguridad fundamental es el aislamiento completo de la red de invitados de la infraestructura corporativa. El SSID de invitados debe operar en una VLAN dedicada con un ámbito DHCP separado. El tráfico debe enrutarse a través del motor de filtrado DNS antes de salir a internet. Esta segmentación previene el movimiento lateral en caso de que un dispositivo de invitado se vea comprometido y asegura que las políticas de tráfico de invitados no impacten inadvertidamente las operaciones de back-office.
Estándares de Cifrado y Autenticación
Para la infraestructura inalámbrica, WPA3 es el estándar actual para un cifrado robusto, que protege contra ataques de diccionario fuera de línea en claves precompartidas. Si bien WPA2 sigue siendo prevalente, las nuevas implementaciones deben exigir soporte para WPA3. La autenticación se maneja típicamente a través de un Captive Portal, que cumple un doble propósito: aceptación de los términos de servicio y captura de datos. La integración de esto con una plataforma de WiFi Analytics permite a los operadores del lugar recopilar datos de primera parte basados en el consentimiento en cumplimiento con GDPR y otros marcos de privacidad regionales.
Guía de Implementación
La implementación del filtrado basado en categorías requiere un enfoque por fases para minimizar la interrupción del tráfico legítimo.
1. Auditoría y Línea Base
Antes de implementar reglas de bloqueo, audite la arquitectura de red existente para confirmar el aislamiento adecuado de la VLAN. Implemente el motor de filtrado DNS en 'modo de monitoreo' durante dos a cuatro semanas. Este período de línea base proporciona visibilidad de los patrones de tráfico reales en la red de invitados, lo que permite a los equipos de TI identificar servicios legítimos que podrían categorizarse incorrectamente de forma inadvertida.
2. Definir la Política de Categorías
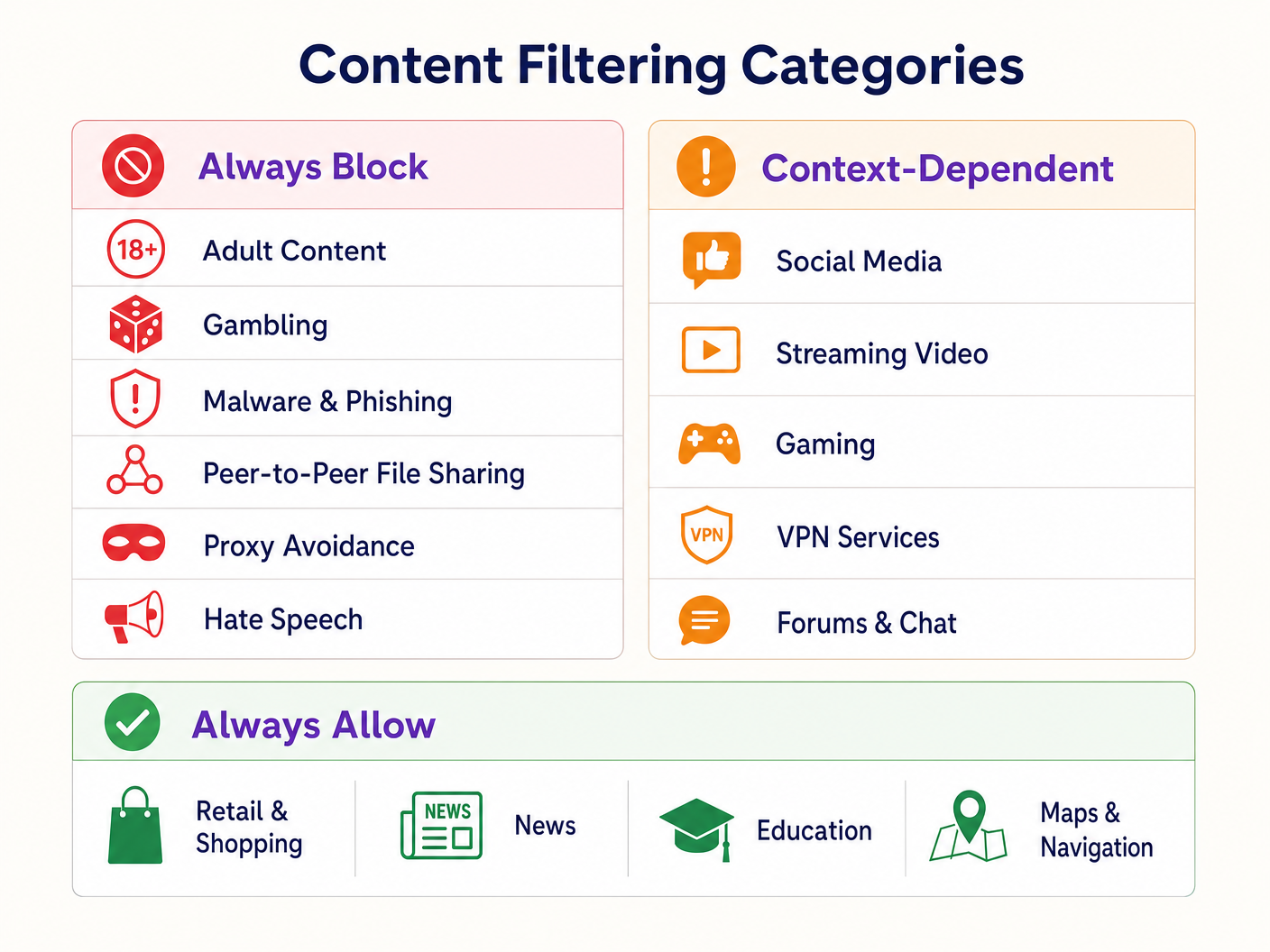
Establezca un marco de política escalonado:
- Bloquear Siempre: Contenido para adultos, juegos de azar, malware, phishing, intercambio de archivos peer-to-peer (P2P) y herramientas para evitar proxies.
- Dependiente del Contexto: Redes sociales, transmisión de video y juegos. Estos requieren alineación con los objetivos operativos del lugar (por ejemplo, conservación de ancho de banda vs. fomento del tiempo de permanencia).
- Permitir Siempre: Dominios de Retail , noticias, educación y navegación.
3. Abordar DNS sobre HTTPS (DoH)
Los navegadores modernos recurren cada vez más a DNS sobre HTTPS (DoH), cifrando las consultas DNS y eludiendo el filtrado a nivel de red. Para aplicar la política de filtrado, el firewall perimetral debe configurarse para bloquear el tráfico saliente del puerto 443 a proveedores DoH conocidos (por ejemplo, 1.1.1.1 de Cloudflare, 8.8.8.8 de Google). Esto obliga a los dispositivos cliente a recurrir al resolvedor DNS proporcionado por la red.
4. Aplicación y Manejo de Excepciones
Transición del modo de monitoreo al modo de aplicación. Configure una página de bloqueo clara y con la marca que informe al usuario por qué se restringió el contenido y proporcione un mecanismo para informar falsos positivos. Establezca un flujo de trabajo documentado para revisar y incluir en la lista blanca los dominios solicitados por los inquilinos minoristas o la administración del lugar.
Mejores Prácticas
- Comunicación Proactiva: Informe a los inquilinos minoristas sobre la política de filtrado antes de su aplicación para evitar interrupciones en sus aplicaciones operativas.
- Revisiones Periódicas de Políticas: El panorama de amenazas y los patrones de uso de internet evolucionan. Programe revisiones trimestrales de la política de categorías y la precisión de la base de datos del motor de filtrado.
- Aprovechar los Captive Portals: Utilice el Captive Portal no solo para el control de acceso, sino como un punto de contacto estratégico. Asegúrese de que el diseño del portal se alinee con la marca del lugar y articule claramente los términos de uso con respecto a crestricciones de contenido.
- Monitorear la Utilización del Ancho de Banda: Si bien el filtrado DNS evita el acceso a contenido específico, la gestión del ancho de banda sigue siendo necesaria. Implemente la limitación de velocidad por cliente para garantizar una distribución equitativa de los recursos, especialmente en áreas de alta densidad. Lea más sobre la optimización del rendimiento en nuestra guía sobre Office Wi Fi: Optimice su Red Wi-Fi Moderna de Oficina .
Solución de Problemas y Mitigación de Riesgos
Bloqueo Excesivo (Falsos Positivos)
El modo de fallo más común es una política inicial excesivamente agresiva que resulta en el bloqueo de dominios legítimos. La mitigación se basa en la fase de monitoreo inicial para establecer una línea de base del tráfico y un proceso de inclusión en listas blancas (whitelisting) receptivo.
Elusión de DoH
Si los usuarios acceden con éxito a contenido bloqueado, verifique que las reglas del firewall que bloquean los resolvedores DoH conocidos estén activas y actualizadas. No bloquear DoH hace que el filtrado DNS a nivel de red sea ineficaz.
Problemas con el Captive Portal
En entornos con características de RF complejas, los dispositivos pueden tener dificultades para mantener la conexión el tiempo suficiente para completar la autenticación del Captive Portal. Asegure una densidad de AP adecuada y una planificación de canales óptima. Consulte Wi Fi Frequencies: A Guide to Wi-Fi Frequencies in 2026 para obtener estrategias detalladas de planificación de RF.
ROI e Impacto Comercial
La implementación de WiFi familiar a través del filtrado DNS ofrece un valor comercial medible:
- Mitigación de Riesgos: Reduce significativamente la probabilidad de multas regulatorias y daños a la reputación asociados con el acceso a contenido ilegal o inapropiado en la red del establecimiento.
- Optimización del Ancho de Banda: El bloqueo del intercambio de archivos P2P y la transmisión de video no autorizada preserva el ancho de banda para casos de uso legítimos, aplazando costosas actualizaciones de circuitos.
- Captura de Datos Mejorada: Una red de invitados segura y confiable fomenta mayores tasas de suscripción en el Captive Portal, enriqueciendo el CRM del establecimiento con datos propios accionables para campañas de marketing dirigidas.
- Satisfacción del Inquilino: Proporcionar un entorno de red limpio y de alto rendimiento apoya las iniciativas digitales de los inquilinos minoristas y mejora la experiencia general del cliente.
Escuche nuestro podcast de información técnica a continuación para obtener más detalles sobre estrategias de implementación y errores comunes:
Definiciones clave
DNS Filtering
The process of blocking access to specific websites by preventing the resolution of their domain names into IP addresses based on categorized databases.
The primary mechanism for enforcing family-friendly content policies efficiently at scale.
VLAN Isolation
The practice of logically separating network traffic into distinct broadcast domains.
Essential for security, ensuring guest traffic cannot interact with corporate or back-office systems.
Captive Portal
A web page that a user must view and interact with before access is granted to a public network.
Used for terms-of-service acceptance and collecting consent-based first-party data.
DNS over HTTPS (DoH)
A protocol for performing remote Domain Name System resolution via the HTTPS protocol.
A significant challenge for network administrators as it encrypts DNS queries, bypassing standard network-level filtering.
WPA3
The third generation of Wi-Fi Protected Access, offering improved encryption and protection against offline dictionary attacks.
The current standard for securing wireless networks, particularly important for public or guest SSIDs.
False Positive
In the context of content filtering, a legitimate website that is incorrectly categorized and blocked by the filtering engine.
Requires a responsive whitelisting process to minimize disruption to venue operations or tenant businesses.
Deep Packet Inspection (DPI)
A form of computer network packet filtering that examines the data part of a packet as it passes an inspection point.
Often too resource-intensive for high-density guest networks compared to DNS filtering.
First-Party Data
Information a company collects directly from its customers and owns.
A key ROI driver for guest WiFi deployments, captured via the captive portal with user consent.
Ejemplos resueltos
A large shopping centre with 150 retail units is experiencing network congestion and complaints from parents regarding inappropriate content access on the open guest WiFi.
- Implement VLAN isolation for the guest SSID. 2. Deploy a cloud-based DNS filtering engine. 3. Configure a strict block policy for Adult, Gambling, Malware, and P2P categories. 4. Block outbound DoH traffic at the firewall. 5. Implement a captive portal requiring terms-of-service acceptance.
A hotel IT manager needs to implement family-friendly WiFi across public areas but must ensure corporate guests can still access necessary VPN services.
- Deploy DNS filtering with a baseline policy blocking Adult, Malware, and Gambling categories. 2. Explicitly allow the 'VPN Services' category in the filtering policy. 3. Monitor traffic logs to identify any specific corporate VPN endpoints that might be miscategorized and whitelist them proactively.
Preguntas de práctica
Q1. A retail tenant complains that their new inventory management web application is being blocked on the shopping centre's guest network. What is the immediate next step?
Sugerencia: Consider the false-positive resolution workflow.
Ver respuesta modelo
Review the DNS filtering logs to identify which category the tenant's application domain is currently assigned to. If it is a false positive (e.g., miscategorized as 'Proxy Avoidance'), add the specific domain to the global whitelist and notify the tenant.
Q2. During the monitoring phase of a new DNS filtering deployment, you notice a high volume of traffic to Cloudflare's 1.1.1.1. What does this indicate and how should you respond?
Sugerencia: Think about encrypted DNS protocols.
Ver respuesta modelo
This indicates client devices are using DNS over HTTPS (DoH) to bypass the network's DNS resolver. You must configure the perimeter firewall to block outbound port 443 traffic to known DoH provider IP addresses to force fallback to standard DNS.
Q3. A stadium IT director wants to implement family-friendly WiFi but is concerned about the performance impact of inspecting all traffic during a match day with 50,000 concurrent users. What architecture do you recommend?
Sugerencia: Compare network-layer vs. application-layer filtering.
Ver respuesta modelo
Recommend cloud-based DNS filtering rather than on-premise Deep Packet Inspection (DPI). DNS filtering only intercepts the initial domain resolution request, adding negligible latency, whereas DPI requires significant processing overhead to inspect the payload of every packet, which would bottleneck under stadium-density loads.