Bloqueo de Malware y Phishing en el Borde de la Red
Esta guía de referencia técnica describe la arquitectura, la implementación y el impacto comercial de la protección contra amenazas a nivel de red para asegurar dispositivos de invitados y IoT no administrados en el borde de la red. Ofrece orientación práctica para que los líderes de TI bloqueen el malware y el phishing de forma proactiva.
Escucha esta guía
Ver transcripción del podcast
- Resumen Ejecutivo
- Análisis Técnico Detallado
- La Arquitectura de la Protección del Borde de la Red
- Componentes Clave
- Guía de Implementación
- Paso 1: Segmentación de la Red
- Paso 2: Configuración de la Puerta de Enlace
- Paso 3: Definición de Políticas
- Mejores Prácticas
- Solución de Problemas y Mitigación de Riesgos
- Manejo de DNS Cifrado
- Bloqueo Excesivo de Tráfico Legítimo
- ROI e Impacto Comercial

Resumen Ejecutivo
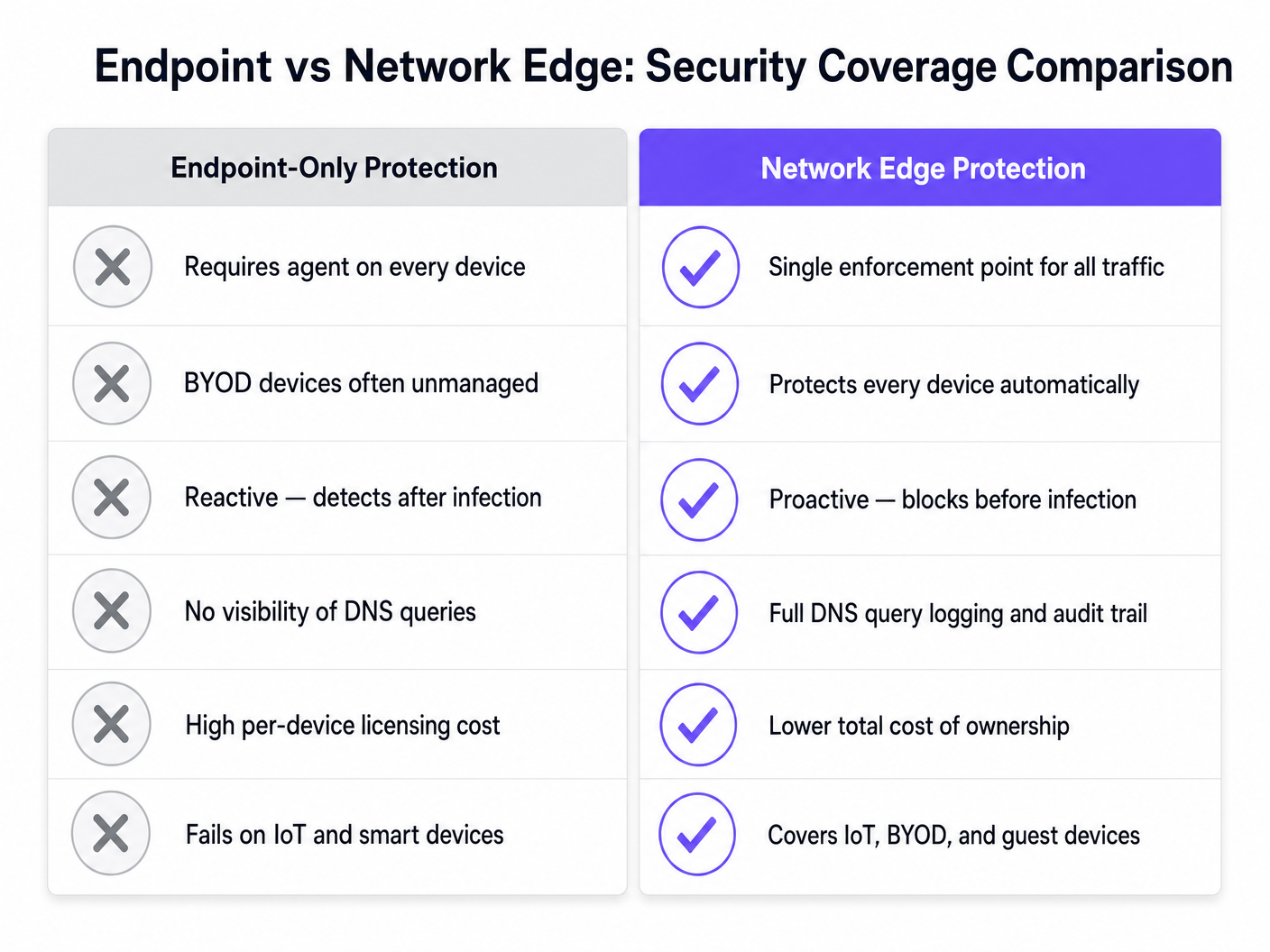
Para los CTOs y arquitectos de red que gestionan lugares con gran afluencia, asegurar los dispositivos no administrados es un desafío operativo crítico. No se pueden implementar agentes de punto final en los smartphones de los invitados, ni se puede confiar en que los usuarios eviten enlaces maliciosos. Esta guía detalla cómo la implementación de protección contra amenazas a nivel de red detiene el malware y el phishing en el borde de la red antes de que llegue a los dispositivos de los invitados. Al aplicar políticas de seguridad en la puerta de enlace mediante el filtrado de DNS y la integración de inteligencia de amenazas, los lugares pueden asegurar el tráfico BYOD, IoT y de invitados de forma proactiva. Este enfoque reduce la sobrecarga de respuesta a incidentes, garantiza el cumplimiento de estándares como GDPR y PCI DSS, y mantiene un entorno seguro para los usuarios de Guest WiFi en los sectores de Hostelería , Comercio Minorista y Transporte .
Análisis Técnico Detallado
La Arquitectura de la Protección del Borde de la Red
La protección contra malware en el borde de la red traslada el punto de aplicación de la seguridad del punto final a la puerta de enlace. Cuando un dispositivo se conecta a la red de un lugar e intenta resolver un dominio, la consulta DNS es interceptada por la puerta de enlace del borde. En lugar de la resolución estándar, la consulta se evalúa contra fuentes de inteligencia de amenazas actualizadas continuamente.
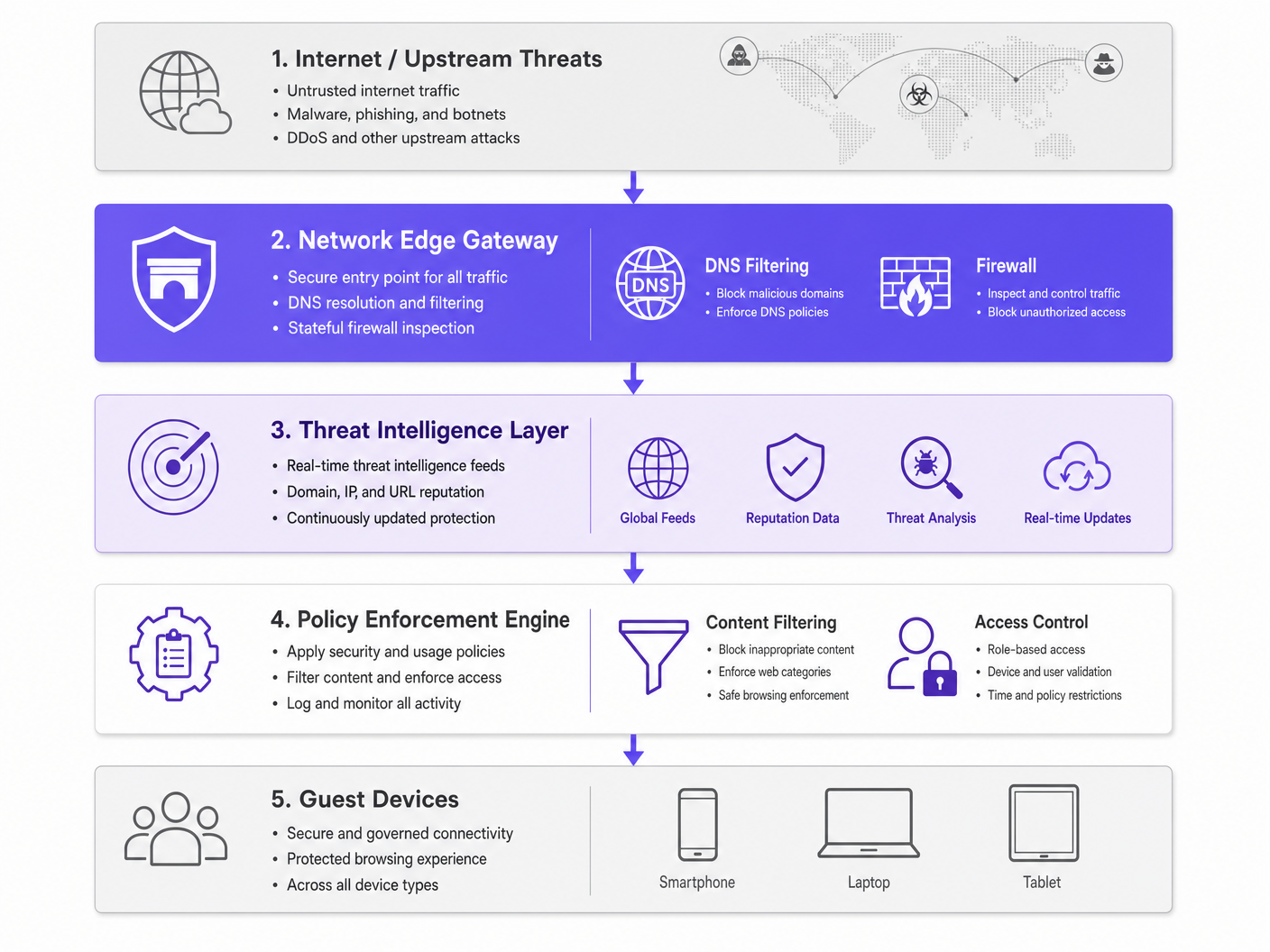
Si el dominio está asociado con la distribución de malware, campañas de phishing o infraestructura de comando y control (C2) de botnets, la solicitud DNS es redirigida a un sumidero. La conexión se interrumpe antes de que la carga maliciosa pueda descargarse. Este bloqueo proactivo previene el movimiento lateral y protege la reputación IP del lugar.
Componentes Clave
- Motor de Filtrado de DNS: Inspecciona todas las solicitudes DNS salientes. Es fundamental configurar este motor para bloquear los resolvedores DoH (DNS over HTTPS) públicos conocidos y evitar que los usuarios eludan el DNS seguro del lugar.
- Integración de Inteligencia de Amenazas: Se suscribe a fuentes globales que categorizan dominios en tiempo real basándose en la reputación, el estado de dominio recién registrado y la actividad maliciosa conocida.
- Aplicación de Políticas: Aplica reglas granulares basadas en roles de usuario (por ejemplo, personal vs. invitado) y categorías de contenido, garantizando el Cumplimiento IWF para Redes WiFi Públicas en el Reino Unido .
Guía de Implementación
La implementación de la protección del borde de la red requiere un enfoque por fases para minimizar las interrupciones y maximizar la cobertura de seguridad.
Paso 1: Segmentación de la Red
Asegúrese de que su red esté correctamente segmentada utilizando VLANs. El tráfico de invitados, el personal corporativo, los dispositivos IoT y los sistemas POS deben residir en segmentos aislados. Esto limita el radio de impacto si un dispositivo se ve comprometido antes de unirse a la red.
Paso 2: Configuración de la Puerta de Enlace
Configure sus routers de borde o firewalls para reenviar todo el tráfico DNS al servicio seguro de filtrado de DNS. Implemente reglas de firewall para bloquear el tráfico saliente en el puerto 53 (DNS) y el puerto 853 (DoT) a cualquier destino que no sean los resolvedores seguros aprobados. Para más información sobre la optimización de redes modernas, consulte Office Wi Fi: Optimize Your Modern Office Wi-Fi Network .
Paso 3: Definición de Políticas
Establezca políticas de referencia. Bloquee categorías maliciosas conocidas a nivel global. Para el filtrado de contenido, aplique políticas específicas basadas en el tipo de lugar; por ejemplo, un filtrado más estricto en entornos de Atención Médica en comparación con el comercio minorista general.
Mejores Prácticas
- Aplicación de Políticas Granulares: Evite bloqueos generales que generen tickets de soporte. Utilice control de acceso basado en roles (RBAC) integrado con su proveedor de identidad (por ejemplo, la licencia Connect de Purple).
- Registro Exhaustivo: Mantenga un registro de auditoría completo de las consultas DNS y las amenazas bloqueadas. Esto es esencial para la respuesta a incidentes y la elaboración de informes de cumplimiento. Consulte Explain what is audit trail for IT Security in 2026 para conocer los requisitos detallados.
- Monitoreo Continuo: Aproveche WiFi Analytics para monitorear el rendimiento de la red y los eventos de seguridad en tiempo real.
Solución de Problemas y Mitigación de Riesgos
Manejo de DNS Cifrado
Los sistemas operativos modernos utilizan cada vez más DoH y DoT, que cifran las consultas DNS y pueden eludir el filtrado de borde tradicional. Para mitigar esto, mantenga una lista de bloqueo actualizada de resolvedores DoH públicos conocidos (por ejemplo, 8.8.8.8, 1.1.1.1) para forzar a los dispositivos a recurrir al DNS seguro proporcionado por el lugar a través del puerto estándar 53.
Bloqueo Excesivo de Tráfico Legítimo
Las fuentes de inteligencia de amenazas agresivas pueden ocasionalmente marcar dominios legítimos, especialmente los recién registrados utilizados para campañas de marketing. Establezca un proceso rápido de inclusión en listas blancas y capacite al equipo de operaciones de TI para resolver rápidamente los falsos positivos.
ROI e Impacto Comercial
El caso de negocio para la protección contra malware en el borde de la red se basa en la mitigación de riesgos y la eficiencia operativa. Al bloquear amenazas en la puerta de enlace, los lugares eliminan los costos de licencia por dispositivo asociados con la seguridad de punto final para dispositivos BYOD y de invitados. Además, reduce drásticamente las horas del servicio de asistencia de TI dedicadas a investigar dispositivos comprometidos o a lidiar con direcciones IP en listas negras. La conectividad segura y confiable resultante mejora la experiencia del invitado y protege la reputación de la marca del lugar.
Definiciones clave
Network Edge
The boundary where a local network connects to the internet, typically managed by a router, firewall, or gateway.
This is the optimal location to deploy security controls for unmanaged devices, as all traffic must pass through it.
DNS Filtering
The process of blocking access to certain websites or IP addresses by intercepting DNS queries and evaluating them against a policy or threat feed.
Used to proactively stop devices from connecting to malicious domains before any data is transferred.
Sinkholing
Redirecting malicious traffic to a safe, controlled IP address instead of its intended destination.
When a guest device tries to reach a malware server, the edge gateway sinkholes the request, preventing infection.
Threat Intelligence Feed
A continuously updated stream of data regarding potential or current cyber threats, including known malicious domains and IP addresses.
Edge gateways use these feeds to make real-time decisions on whether to allow or block traffic.
DoH (DNS over HTTPS)
A protocol for performing remote Domain Name System resolution via the HTTPS protocol, encrypting the data.
While good for privacy, DoH can bypass corporate edge filtering unless known DoH resolvers are explicitly blocked.
VLAN Segmentation
Dividing a single physical network into multiple logical networks to isolate traffic.
Essential for separating untrusted guest traffic from sensitive corporate or POS systems.
BYOD (Bring Your Own Device)
The practice of allowing employees or guests to use their personal devices on the organisation's network.
BYOD devices are typically unmanaged, making endpoint security impossible and necessitating network edge protection.
Audit Trail
A chronological record of system activities, including DNS queries and blocked connections.
Required for compliance with frameworks like PCI DSS and GDPR to prove security controls are active.
Ejemplos resueltos
A 500-room hotel needs to secure guest WiFi while ensuring IoT devices (smart TVs, room controls) are protected from external command-and-control servers.
Deploy a network edge gateway with DNS filtering. Segment the network into Guest, IoT, and Corporate VLANs. Configure the gateway to intercept all DNS queries from the IoT and Guest VLANs, forwarding them to the secure DNS service. Apply a strict policy for the IoT VLAN that only allows resolution of known, required domains (allowlisting), while applying a standard threat-blocking policy for the Guest VLAN.
A large retail chain experiences frequent IP blacklisting due to guest devices sending spam while connected to the in-store WiFi.
Implement network edge malware protection with active threat intelligence feeds. Configure the firewall to block outbound SMTP (port 25) for all guest traffic. Enable DNS filtering to sinkhole requests to known botnet and spam-distribution domains.
Preguntas de práctica
Q1. A stadium network administrator notices that while DNS filtering is enabled, some guest devices are still reaching known malicious domains. What is the most likely cause and how should it be addressed?
Sugerencia: Consider modern protocols that might bypass standard port 53 filtering.
Ver respuesta modelo
The devices are likely using encrypted DNS protocols like DNS over HTTPS (DoH) or DNS over TLS (DoT), which bypass standard port 53 filtering. The administrator should update firewall rules to block known public DoH/DoT resolvers and block outbound traffic on port 853, forcing devices to fall back to the venue's secure DNS.
Q2. When deploying network edge protection in a hospital environment, how should the policies differ between the guest WiFi and the medical IoT device VLAN?
Sugerencia: Think about the concept of least privilege and predictable behavior.
Ver respuesta modelo
The guest WiFi should use a standard threat-blocking policy (blocking malware, phishing, and inappropriate content per IWF guidelines) but generally allow internet access. The medical IoT VLAN should use a strict 'default deny' policy with an allowlist, permitting communication only with specific, required vendor servers. IoT devices have predictable traffic patterns, making allowlisting highly effective.
Q3. A retail client wants to implement edge filtering but is concerned about blocking legitimate marketing campaign domains that are newly registered. What process should be implemented?
Sugerencia: Focus on operational workflows and balancing security with business needs.
Ver respuesta modelo
Implement a rapid allowlisting workflow. While 'Newly Registered Domains' is a common threat category, the IT team should have a process to quickly verify and allowlist domains provided by the marketing team before campaigns launch, ensuring security does not impede business operations.