La Pila Tecnológica de WiFi para Invitados: Una Guía del Comprador para Marcas Multi-Sitio
Una guía técnica completa para operadores de recintos multi-sitio que detalla las seis capas de una pila tecnológica de WiFi para invitados moderna. Proporciona criterios de evaluación accionables para APs, controladores de red, autenticación RADIUS, captive portals, analíticas e integración CRM, ayudando a los líderes de TI a navegar las decisiones de construir vs. comprar.
🎧 Escucha esta guía
Ver transcripción
- Resumen Ejecutivo
- Análisis Técnico Detallado: Las Seis Capas de la Pila
- Capa 1: Puntos de Acceso e Infraestructura de RF
- Capa 2: Controlador de Red y SD-WAN
- Capa 3: Autenticación RADIUS y AAA
- Capa 4: Captive Portal y Página de Bienvenida
- Capa 5: Analíticas y Plataforma de Datos
- Capa 6: Integración de CRM y Marketing
- Guía de Implementación
- Enfoque 1: Construya su Propia Pila
- Enfoque 2: Integración de las mejores soluciones
- Enfoque 3: Plataforma Unificada (El Enfoque Purple)
- Mejores Prácticas
- Solución de Problemas y Mitigación de Riesgos
- ROI e Impacto Comercial

Resumen Ejecutivo
Para los líderes de TI que gestionan recintos multi-sitio —desde propiedades Minoristas y grupos Hoteleros hasta instalaciones de Salud y centros de Transporte — el WiFi para invitados ha evolucionado de una comodidad básica a un activo estratégico. Una pila tecnológica de WiFi para invitados moderna se encuentra en la intersección de las operaciones de red, el cumplimiento de datos y la inteligencia del cliente.
Sin embargo, muchas organizaciones luchan con paisajes de proveedores fragmentados, creando silos de datos, cuellos de botella de integración y riesgos de cumplimiento. Esta guía del comprador disecciona las seis capas críticas de la pila tecnológica de WiFi para invitados. Proporciona un marco de evaluación neutral para el proveedor para ayudar a los CTOs y arquitectos de red a evaluar su infraestructura actual, comprender los puntos de integración y tomar decisiones informadas sobre si construir, comprar o integrar su plataforma de WiFi para Invitados .
Análisis Técnico Detallado: Las Seis Capas de la Pila
Una arquitectura robusta de WiFi para invitados se construye sobre seis capas distintas. Evaluar estas capas de forma aislada es un error arquitectónico común; el verdadero valor reside en la integración entre ellas.
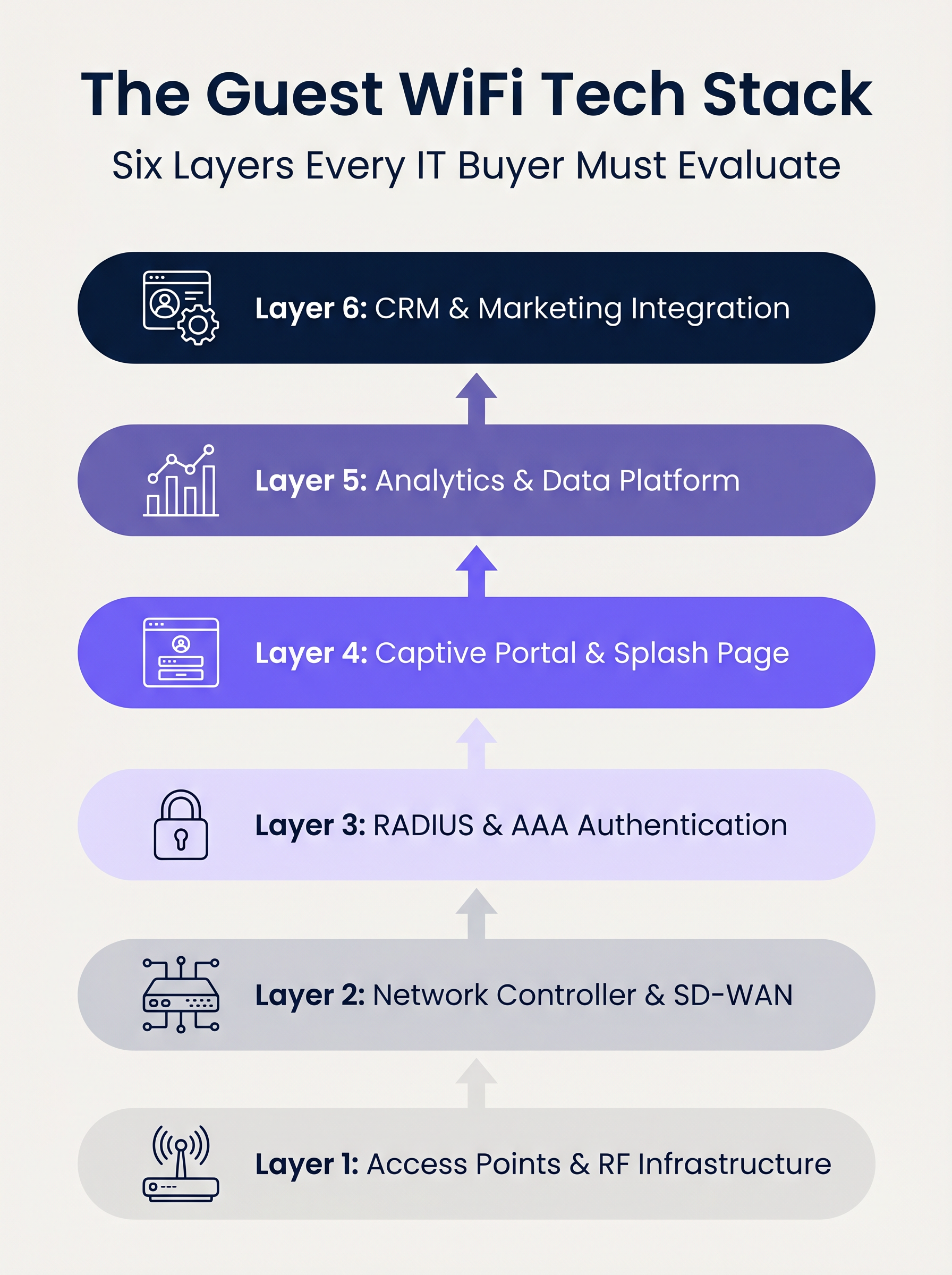
Capa 1: Puntos de Acceso e Infraestructura de RF
La base de la pila es el hardware de radiofrecuencia. En implementaciones empresariales, proveedores como Cisco Meraki, Aruba, Ruckus y Extreme Networks dominan. Al evaluar APs para implementaciones multi-sitio, el rendimiento bruto es secundario a las capacidades de gestión centralizada y el aprovisionamiento sin contacto.
Consideraciones Clave:
- Estándares: Wi-Fi 6 (802.11ax) es la base. Wi-Fi 6E debe especificarse para entornos de alta densidad (por ejemplo, estadios) donde la congestión del espectro es una limitación principal.
- Seguridad: El soporte WPA3 es obligatorio, particularmente para recintos dentro del alcance de PCI DSS.
- Integración: El controlador de AP debe exponer APIs robustas para una integración perfecta con las capas de autenticación y analíticas superiores.
Capa 2: Controlador de Red y SD-WAN
Esta capa gestiona la orquestación, la aplicación de políticas y la segmentación del tráfico. La transición de MPLS heredado a arquitecturas SD-WAN ha transformado la gestión de redes multi-sitio. SD-WAN permite la definición centralizada de políticas con salida a internet local, permitiendo a los administradores aplicar límites de ancho de banda y filtrado de contenido de manera uniforme en toda la propiedad. Para una comprensión más profunda de estos cambios arquitectónicos, revise Los Beneficios Clave de SD-WAN para Empresas Modernas .
Capa 3: Autenticación RADIUS y AAA
La Autenticación, Autorización y Contabilidad (AAA) es frecuentemente el eslabón más débil en las implementaciones para invitados. Confiar en redes abiertas o simples Claves Pre-Compartidas (PSKs) expone el recinto a riesgos significativos de seguridad y cumplimiento.
La implementación de IEEE 802.1X con un backend RADIUS robusto permite la autenticación por usuario y la contabilidad de sesiones. Aunque FreeRADIUS es una opción de código abierto viable, las implementaciones empresariales suelen requerir un servicio RADIUS gestionado y alojado en la nube para manejar la escala, la redundancia y la integración con el captive portal.
Capa 4: Captive Portal y Página de Bienvenida
El captive portal es la intersección del acceso a la red y la experiencia de marca. Un portal técnicamente sólido debe manejar los asistentes de red cautiva específicos del dispositivo (por ejemplo, Apple CNA) sin problemas, sin depender de técnicas obsoletas como el secuestro de DNS sobre HTTP.
Además, el portal es el mecanismo principal para capturar el consentimiento del usuario bajo marcos como GDPR y CCPA. Debe soportar OAuth 2.0 para inicios de sesión sociales y generar registros de consentimiento inmutables y listos para auditoría.
Capa 5: Analíticas y Plataforma de Datos
Esta capa transforma la telemetría de red en inteligencia accionable. Las analíticas de presencia rastrean el tiempo de permanencia y el flujo de visitantes, pero el valor estratégico reside en la resolución de identidad —vincular una dirección MAC de dispositivo a un perfil de usuario autenticado.
Con iOS 14 y Android 10 implementando la aleatorización de direcciones MAC por defecto, depender únicamente de identificadores de dispositivo es obsoleto. Las analíticas basadas en identidad proporcionan información precisa y conforme. Para una visión completa de cómo estos datos generan valor, explore nuestras capacidades de WiFi Analytics y nuestra guía específica sobre WiFi Minorista: De Analíticas de Tráfico a Experiencias Personalizadas en Tienda .
Capa 6: Integración de CRM y Marketing
La capa superior convierte los datos de red en resultados de negocio a través de integraciones API bidireccionales con plataformas como Salesforce, HubSpot o Plataformas de Datos del Cliente (CDPs) a medida. Los webhooks en tiempo real deben activar flujos de trabajo automatizados —como actualizaciones de puntos de lealtad o mensajes personalizados— en el momento en que un invitado conocido se autentica en la red.
Guía de Implementación
Al implementar una pila de WiFi para invitados multi-sitio, los líderes de TI se enfrentan a una decisión arquitectónica fundamental: Construir, Comprar o Integrar.
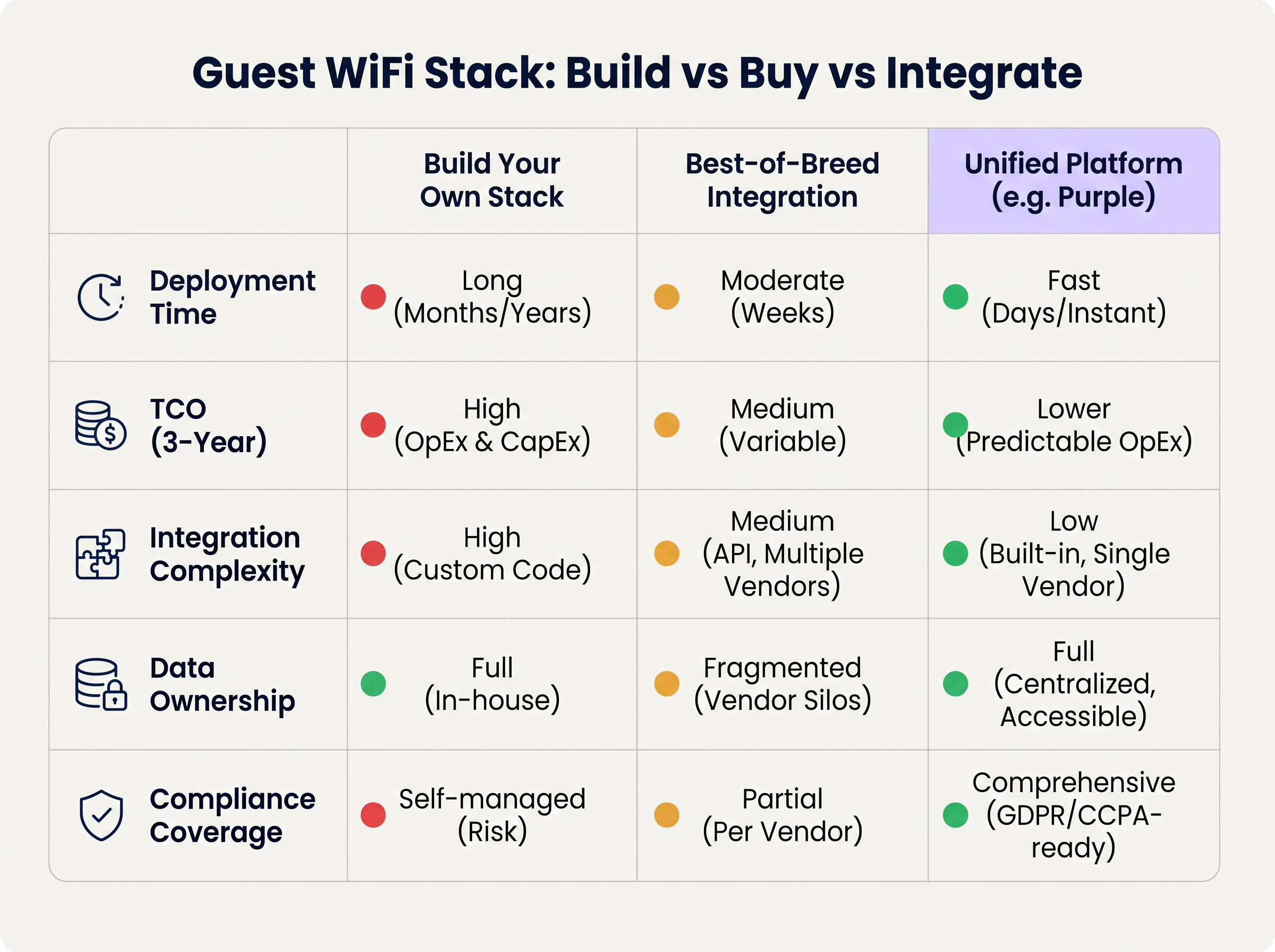
Enfoque 1: Construya su Propia Pila
Unir un proveedor de AP, un servidor RADIUS personalizado, un captive portal a medida y una tubería de analíticas propia ofrece el máximo control, pero requiere importantes recursos de ingeniería. El Costo Total de Propiedad (TCO) está fuertemente inclinado hacia el mantenimiento continuo, la gestión de cumplimiento y las actualizaciones de API.
Enfoque 2: Integración de las mejores soluciones
Seleccionar el proveedor óptimo en cada capa e integrarlos a través de APIs es común en organizaciones de TI maduras. Sin embargo, la complejidad de la integración es alta. Las actualizaciones de los proveedores pueden romper las conexiones de la API, los modelos de datos a menudo divergen y la resolución de problemas a través de múltiples mesas de soporte aumenta el Tiempo Medio de Resolución (MTTR).
Enfoque 3: Plataforma Unificada (El Enfoque Purple)
Una plataforma unificada se superpone a la infraestructura existente de Capa 1 y Capa 2, consolidando la autenticación, el captive portal, los análisis y la integración de CRM en una única solución. Este enfoque reduce drásticamente el tiempo de implementación, disminuye el TCO a través de OpEx predecibles y centraliza la gestión del cumplimiento. Purple, por ejemplo, se integra sin problemas con más de 90 proveedores de AP, evitando la dependencia de hardware y ofreciendo análisis de nivel empresarial.
Mejores Prácticas
- Desacoplar el Portal del Hardware: Evite usar el captive portal nativo proporcionado por su proveedor de AP. Separar la capa del portal asegura que conserve sus datos de invitados y flujos de trabajo personalizados incluso si migra a un proveedor de hardware diferente en el futuro.
- Implementar Segmentación Estricta de VLAN: Mantenga un mínimo de tres SSIDs por sitio: Corporativo (802.1X), Invitado (Captive Portal) e IoT (VLAN Aislada). Asegúrese de que la VLAN de invitados no tenga ruta a la red corporativa y restrinja el tráfico mediante políticas estrictas de firewall.
- Diseñar para la Identidad, No para los Dispositivos: Diseñe su canal de análisis en torno a perfiles de usuario autenticados en lugar de direcciones MAC para prepararse contra los cambios continuos de privacidad a nivel del sistema operativo.
Solución de Problemas y Mitigación de Riesgos
- Fallos en la Aleatorización de MAC: Si los análisis muestran recuentos de visitantes inflados artificialmente con bajas tasas de repetición, es probable que la aleatorización de MAC esté sesgando los datos. Mitigación: Aplique la autenticación del captive portal para anclar los análisis a la identidad del usuario.
- Captive Portal No se Activa: A menudo causado por la aplicación estricta de HTTPS (HSTS) en el dispositivo cliente o por un manejo inadecuado del Asistente de Red Cautiva del sistema operativo. Mitigación: Asegúrese de que la infraestructura del portal utilice certificados SSL válidos e intercepte correctamente las URL específicas utilizadas por Apple y Google para detectar redes cautivas.
- Auditorías de Cumplimiento: Las pilas fragmentadas a menudo fallan en las auditorías de GDPR debido a políticas inconsistentes de retención de datos entre proveedores. Mitigación: Centralice la gestión del consentimiento y la retención de datos dentro de una plataforma unificada que actúe como la única fuente de verdad.
ROI e Impacto Comercial
El ROI de una pila moderna de WiFi para invitados se mide en dos vectores: eficiencia de TI y valor comercial.
- Eficiencia de TI: La gestión centralizada y un enfoque de plataforma unificada reducen los tiempos de implementación de meses a días. La incorporación automatizada y el aprovisionamiento sin contacto reducen los tickets de soporte de Nivel 1 relacionados con el acceso a la red hasta en un 40%.
- Valor Comercial: Al capturar datos de primera mano e integrarlos con sistemas CRM, los establecimientos pueden atribuir directamente los ingresos a las campañas de marketing impulsadas por WiFi. En entornos minoristas, la autenticación basada en perfiles y el compromiso dirigido pueden aumentar significativamente el valor de vida del cliente, transformando la red de un centro de costos en un activo generador de ingresos.
Términos clave y definiciones
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC) that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
Essential for securing corporate networks and advanced guest deployments, moving beyond simple shared passwords.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The backend engine that validates user credentials and tracks session data in a secure guest WiFi deployment.
Captive Network Assistant (CNA)
The pseudo-browser built into mobile operating systems (iOS, Android) that automatically detects a captive portal and prompts the user to log in.
If a WiFi platform does not interact correctly with the CNA, users will experience a broken login flow and assume the network is down.
MAC Randomisation
A privacy feature in modern mobile OSs where the device broadcasts a fake, rotating MAC address to public networks rather than its true hardware address.
This feature breaks legacy presence analytics systems that rely on MAC addresses to count unique visitors and track dwell time.
Identity Resolution
The process of matching a network connection event to a known, authenticated customer profile within a database.
The critical step that turns anonymous network traffic into actionable marketing intelligence.
Zero-Touch Provisioning (ZTP)
A deployment method where network devices (like APs) automatically download their configuration from a central controller the moment they are plugged in.
Crucial for multi-site operators to deploy infrastructure rapidly without requiring highly skilled engineers on-site.
WPA3
The latest generation of Wi-Fi security, providing enhanced cryptographic strength and better protection against brute-force attacks.
A mandatory requirement for any modern network deployment, especially those processing payments or handling sensitive data.
Webhook
A method for augmenting or altering the behaviour of a web page or web application with custom callbacks, triggered by specific events.
Used to push real-time data from the WiFi platform to a CRM (e.g., triggering a welcome email the moment a guest connects).
Casos de éxito
A 200-site retail chain needs to upgrade its legacy guest WiFi. They currently use Cisco Meraki APs with the native Meraki splash page, but marketing cannot export the data easily, and IT is concerned about GDPR compliance regarding data retention.
The chain should retain their Meraki Layer 1/2 infrastructure to avoid massive CapEx. They must deploy a unified Layer 4-6 platform (like Purple) via API integration with the Meraki dashboard. The new architecture will use Meraki for RF delivery and SD-WAN routing, while the unified platform handles the captive portal, RADIUS authentication, and consent capture. The platform will automatically enforce a 12-month data retention policy to satisfy GDPR requirements and provide a bi-directional API sync to their central CRM.
A large stadium complex experiences severe captive portal timeouts and authentication failures during half-time when 15,000 users attempt to connect simultaneously.
The issue is a bottleneck at the Layer 3 (RADIUS) and Layer 4 (Portal) infrastructure, which cannot handle the concurrent connection spikes. The solution requires migrating from an on-premise RADIUS server to an auto-scaling cloud RADIUS service. Additionally, the AP configuration must be optimised to aggressively drop weak client connections (Minimum Bitrate requirements) to preserve airtime, and the captive portal must be served via a robust CDN to handle the burst in HTTP requests.
Análisis de escenarios
Q1. You are the IT Director for a 50-site hospital trust. You need to deploy guest WiFi that captures user demographics, but you are subject to strict data sovereignty and compliance audits. A vendor proposes a solution where the APs handle authentication and send data directly to their proprietary cloud analytics tool. Do you accept?
💡 Sugerencia:Consider the implications of hardware lock-in and audit requirements for data processing agreements.
Mostrar enfoque recomendado
Reject the proposal. Relying on the AP vendor's proprietary cloud tool creates hardware lock-in and fragments compliance management. Instead, implement a unified platform that overlays the AP infrastructure. This ensures you maintain ownership of the data, can enforce granular consent and retention policies centrally, and can switch AP hardware in the future without losing your compliance architecture or historical data.
Q2. A retail brand wants to trigger an immediate push notification via their mobile app when a high-tier loyalty member walks into a store. They currently rely on MAC address tracking from their APs to detect presence. Why will this fail, and how should it be architected?
💡 Sugerencia:Think about modern mobile OS privacy features and the difference between presence and identity.
Mostrar enfoque recomendado
This will fail because iOS and Android use MAC randomisation, meaning the APs will see a different, fake MAC address each time the device connects, making it impossible to reliably identify the loyalty member passively. The architecture must shift to identity resolution via authentication. The user must authenticate via the captive portal (or via an integration like OpenRoaming/Passpoint), binding their session to their profile. Once authenticated, the WiFi platform can use a webhook to signal the CRM/App backend to trigger the notification.
Q3. During a network refresh, you are evaluating Wi-Fi 6 vs Wi-Fi 6E for a chain of small coffee shops (max capacity 40 people). The Wi-Fi 6E access points are 40% more expensive. Which do you choose?
💡 Sugerencia:Consider the primary benefit of the 6 GHz band and the density of the environment.
Mostrar enfoque recomendado
Choose Wi-Fi 6. Wi-Fi 6E introduces the 6 GHz band, which is highly beneficial for relieving spectrum congestion in ultra-high-density environments like stadiums or large auditoriums. For a small coffee shop with a maximum capacity of 40 concurrent users, spectrum congestion is unlikely to be a critical issue. Wi-Fi 6 provides sufficient throughput and efficiency features (like OFDMA) at a lower CapEx, improving the overall ROI of the deployment.
Conclusiones clave
- ✓A modern guest WiFi stack consists of six layers: AP infrastructure, Network Controller, RADIUS, Captive Portal, Analytics, and CRM Integration.
- ✓Evaluating these layers in isolation leads to integration complexity, data silos, and compliance risks.
- ✓Mobile OS MAC randomisation means analytics must be anchored to authenticated user identities, not device MAC addresses.
- ✓Decoupling the captive portal and analytics platform from the physical access points prevents hardware lock-in and protects historical data.
- ✓For most multi-site operators, a Unified Platform approach delivers the fastest time-to-value and lowest TCO compared to building in-house or integrating multiple vendors.
- ✓Robust compliance architecture (GDPR/CCPA) requires centralised consent capture and automated data retention policies.



