A Pilha Tecnológica de WiFi para Convidados: Um Guia do Comprador para Marcas Multi-Locais
Um guia técnico abrangente para operadores de locais multi-site, detalhando as seis camadas de uma pilha tecnológica moderna de WiFi para convidados. Ele fornece critérios de avaliação acionáveis para APs, controladores de rede, autenticação RADIUS, captive portals, análises e integração de CRM, ajudando líderes de TI a navegar nas decisões de construir vs. comprar.
🎧 Ouça este Guia
Ver Transcrição
- Resumo Executivo
- Análise Técnica Aprofundada: As Seis Camadas da Pilha
- Camada 1: Access Points e Infraestrutura de RF
- Camada 2: Controlador de Rede e SD-WAN
- Camada 3: Autenticação RADIUS e AAA
- Camada 4: Captive Portal e Página de Boas-Vindas
- Camada 5: Análise e Plataforma de Dados
- Camada 6: Integração de CRM e Marketing
- Guia de Implementação
- Abordagem 1: Construa Sua Própria Pilha
- Abordagem 2: Integração Best-of-Breed
- Abordagem 3: Plataforma Unificada (A Abordagem Purple)
- Melhores Práticas
- Solução de Problemas e Mitigação de Riscos
- ROI e Impacto nos Negócios

Resumo Executivo
Para líderes de TI que gerenciam locais multi-site — desde propriedades de Varejo e grupos de Hotelaria até instalações de Saúde e centros de Transporte — o WiFi para convidados evoluiu de uma comodidade básica para um ativo estratégico. Uma pilha tecnológica moderna de WiFi para convidados está na intersecção de operações de rede, conformidade de dados e inteligência do cliente.
No entanto, muitas organizações enfrentam dificuldades com cenários de fornecedores fragmentados, criando silos de dados, gargalos de integração e riscos de conformidade. Este guia do comprador dissecou as seis camadas críticas da pilha tecnológica de WiFi para convidados. Ele fornece uma estrutura de avaliação neutra em relação ao fornecedor para ajudar CTOs e arquitetos de rede a avaliar sua infraestrutura atual, entender os pontos de integração e tomar decisões informadas sobre construir, comprar ou integrar sua plataforma de WiFi para Convidados .
Análise Técnica Aprofundada: As Seis Camadas da Pilha
Uma arquitetura robusta de WiFi para convidados é construída sobre seis camadas distintas. Avaliar essas camadas isoladamente é uma falha arquitetônica comum; o verdadeiro valor reside na integração entre elas.
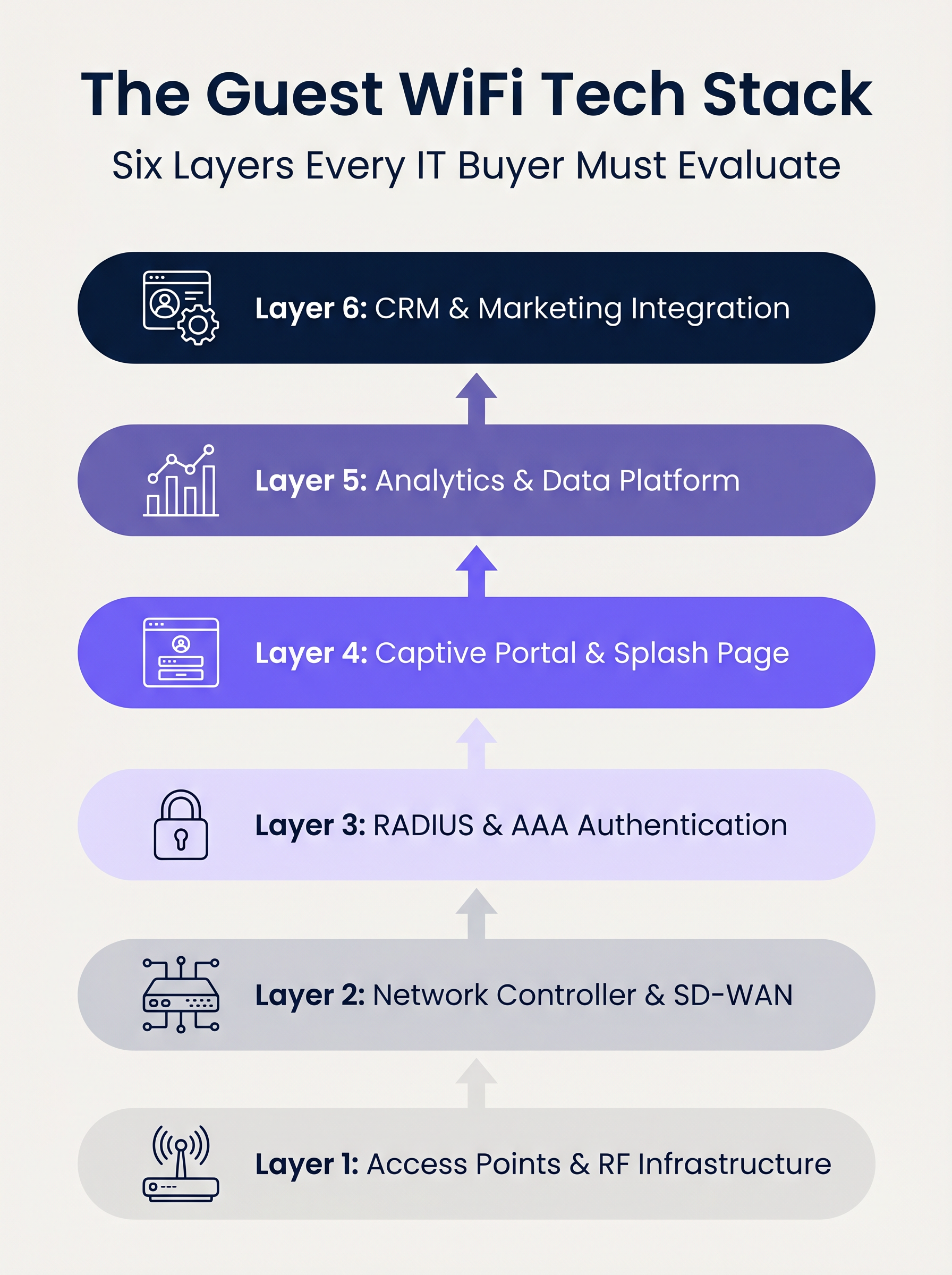
Camada 1: Access Points e Infraestrutura de RF
A base da pilha é o hardware de radiofrequência. Em implantações corporativas, fornecedores como Cisco Meraki, Aruba, Ruckus e Extreme Networks dominam. Ao avaliar APs para implantações multi-site, a taxa de transferência bruta é secundária em relação às capacidades de gerenciamento centralizado e provisionamento zero-touch.
Principais Considerações:
- Padrões: Wi-Fi 6 (802.11ax) é a linha de base. Wi-Fi 6E deve ser especificado para ambientes de alta densidade (por exemplo, estádios) onde o congestionamento do espectro é uma restrição primária.
- Segurança: O suporte a WPA3 é obrigatório, particularmente para locais dentro do escopo PCI DSS.
- Integração: O controlador de AP deve expor APIs robustas para integração perfeita com camadas de autenticação e análise upstream.
Camada 2: Controlador de Rede e SD-WAN
Esta camada lida com orquestração, aplicação de políticas e segmentação de tráfego. A transição de MPLS legado para arquiteturas SD-WAN transformou o gerenciamento de rede multi-site. SD-WAN permite a definição centralizada de políticas com saída de internet local, permitindo que os administradores apliquem limites de largura de banda e filtragem de conteúdo uniformemente em toda a propriedade. Para uma compreensão mais aprofundada dessas mudanças arquitetônicas, revise Os Principais Benefícios do SD-WAN para Empresas Modernas .
Camada 3: Autenticação RADIUS e AAA
Autenticação, Autorização e Contabilidade (AAA) é frequentemente o elo mais fraco em implantações para convidados. Confiar em redes abertas ou em chaves pré-compartilhadas (PSKs) simples expõe o local a riscos significativos de segurança e conformidade.
A implementação do IEEE 802.1X com um backend RADIUS robusto permite a autenticação por usuário e a contabilidade de sessão. Embora o FreeRADIUS seja uma opção de código aberto viável, as implantações corporativas geralmente exigem um serviço RADIUS gerenciado e hospedado na nuvem para lidar com escala, redundância e integração com o captive portal.
Camada 4: Captive Portal e Página de Boas-Vindas
O captive portal é a intersecção entre o acesso à rede e a experiência da marca. Um portal tecnicamente sólido deve lidar com assistentes de rede cativa específicos do dispositivo (por exemplo, Apple CNA) de forma transparente, sem depender de técnicas obsoletas como sequestro de DNS via HTTP.
Além disso, o portal é o principal mecanismo para capturar o consentimento do usuário sob estruturas como GDPR e CCPA. Ele deve suportar OAuth 2.0 para logins sociais e gerar registros de consentimento imutáveis e prontos para auditoria.
Camada 5: Análise e Plataforma de Dados
Esta camada transforma a telemetria da rede em inteligência acionável. A análise de presença rastreia o tempo de permanência e o fluxo de pessoas, mas o valor estratégico reside na resolução de identidade — vinculando um endereço MAC de dispositivo a um perfil de usuário autenticado.
Com o iOS 14 e o Android 10 implementando a randomização de endereços MAC por padrão, depender apenas de identificadores de dispositivo é obsoleto. A análise baseada em identidade fornece insights precisos e compatíveis. Para uma visão abrangente de como esses dados geram valor, explore nossas capacidades de Análise de WiFi e nosso guia específico sobre WiFi para Varejo: Da Análise de Tráfego às Experiências Personalizadas na Loja .
Camada 6: Integração de CRM e Marketing
A camada superior converte dados de rede em resultados de negócios por meio de integrações de API bidirecionais com plataformas como Salesforce, HubSpot ou Customer Data Platforms (CDPs) personalizadas. Webhooks em tempo real devem acionar fluxos de trabalho automatizados — como atualizações de pontos de fidelidade ou mensagens personalizadas — no momento em que um convidado conhecido se autentica na rede.
Guia de Implementação
Ao implantar uma pilha de WiFi para convidados multi-site, os líderes de TI enfrentam uma decisão arquitetônica fundamental: Construir, Comprar ou Integrar.
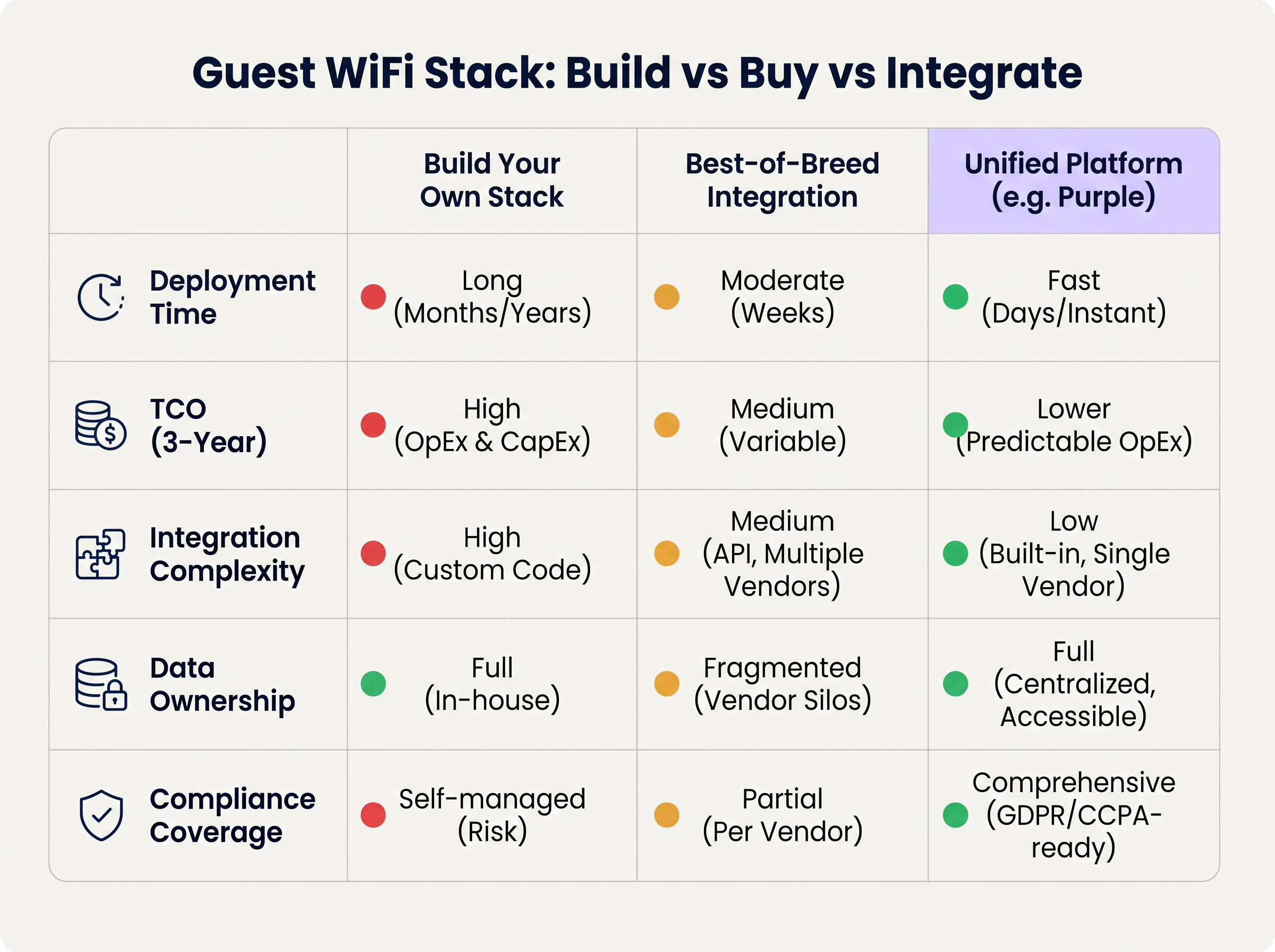
Abordagem 1: Construa Sua Própria Pilha
Unir um fornecedor de AP, um servidor RADIUS personalizado, um captive portal sob medida e um pipeline de análise interno oferece controle máximo, mas exige recursos de engenharia significativos. O Custo Total de Propriedade (TCO) é fortemente inclinado para manutenção contínua, gerenciamento de conformidade e atualizações de API.
Abordagem 2: Integração Best-of-Breed
A seleção do fornecedor ideal em cada camada e a integração via APIs é comum em organizações de TI maduras. No entanto, a complexidade da integração é alta. Atualizações de fornecedores podem quebrar conexões de API, modelos de dados frequentemente divergem, e a resolução de problemas em múltiplos balcões de suporte aumenta o Tempo Médio para Resolução (MTTR).
Abordagem 3: Plataforma Unificada (A Abordagem Purple)
Uma plataforma unificada se sobrepõe à infraestrutura existente de Camada 1 e Camada 2, consolidando autenticação, captive portal, análises e integração de CRM em uma única solução. Essa abordagem reduz drasticamente o tempo de implantação, diminui o TCO por meio de OpEx previsível e centraliza o gerenciamento de conformidade. A Purple, por exemplo, se integra perfeitamente com mais de 90 fornecedores de AP, evitando o bloqueio de hardware e fornecendo análises de nível empresarial.
Melhores Práticas
- Desacople o Portal do Hardware: Evite usar o captive portal nativo fornecido pelo seu fornecedor de AP. Separar a camada do portal garante que você mantenha seus dados de convidado e fluxos de trabalho personalizados, mesmo que migre para um fornecedor de hardware diferente no futuro.
- Implemente Segmentação de VLAN Estrita: Mantenha um mínimo de três SSIDs por local: Corporativo (802.1X), Convidado (Captive Portal) e IoT (VLAN Isolada). Garanta que a VLAN de convidado não tenha rota para a rede corporativa e restrinja o tráfego por meio de políticas de firewall rigorosas.
- Projete para Identidade, Não para Dispositivos: Arquiteture seu pipeline de análises em torno de perfis de usuário autenticados, em vez de endereços MAC, para se proteger contra as contínuas mudanças de privacidade em nível de sistema operacional.
Solução de Problemas e Mitigação de Riscos
- Falhas na Randomização de MAC: Se as análises mostrarem contagens de visitantes artificialmente inflacionadas com baixas taxas de repetição, a randomização de MAC provavelmente está distorcendo os dados. Mitigação: Imponha a autenticação via captive portal para ancorar as análises à identidade do usuário.
- Captive Portal Não Acionando: Frequentemente causado por imposição HTTPS estrita (HSTS) no dispositivo cliente ou manuseio inadequado do Assistente de Rede Captive do sistema operacional. Mitigação: Garanta que a infraestrutura do portal use certificados SSL válidos e intercepte corretamente as URLs específicas usadas pela Apple e Google para detectar redes captive.
- Auditorias de Conformidade: Pilhas fragmentadas frequentemente falham em auditorias de GDPR devido a políticas inconsistentes de retenção de dados entre fornecedores. Mitigação: Centralize o gerenciamento de consentimento e a retenção de dados em uma plataforma unificada que atue como a única fonte da verdade.
ROI e Impacto nos Negócios
O ROI de uma pilha moderna de WiFi para convidados é medido em dois vetores: eficiência de TI e valor comercial.
- Eficiência de TI: O gerenciamento centralizado e uma abordagem de plataforma unificada reduzem os tempos de implantação de meses para dias. O onboarding automatizado e o provisionamento zero-touch diminuem os tickets de suporte de Nível 1 relacionados ao acesso à rede em até 40%.
- Valor Comercial: Ao capturar dados primários e integrá-los com sistemas de CRM, os locais podem atribuir diretamente a receita a campanhas de marketing impulsionadas por WiFi. Em ambientes de varejo, a autenticação baseada em perfil e o engajamento direcionado podem aumentar significativamente o valor vitalício do cliente, transformando a rede de um centro de custo em um ativo gerador de receita.
Termos-Chave e Definições
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC) that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
Essential for securing corporate networks and advanced guest deployments, moving beyond simple shared passwords.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The backend engine that validates user credentials and tracks session data in a secure guest WiFi deployment.
Captive Network Assistant (CNA)
The pseudo-browser built into mobile operating systems (iOS, Android) that automatically detects a captive portal and prompts the user to log in.
If a WiFi platform does not interact correctly with the CNA, users will experience a broken login flow and assume the network is down.
MAC Randomisation
A privacy feature in modern mobile OSs where the device broadcasts a fake, rotating MAC address to public networks rather than its true hardware address.
This feature breaks legacy presence analytics systems that rely on MAC addresses to count unique visitors and track dwell time.
Identity Resolution
The process of matching a network connection event to a known, authenticated customer profile within a database.
The critical step that turns anonymous network traffic into actionable marketing intelligence.
Zero-Touch Provisioning (ZTP)
A deployment method where network devices (like APs) automatically download their configuration from a central controller the moment they are plugged in.
Crucial for multi-site operators to deploy infrastructure rapidly without requiring highly skilled engineers on-site.
WPA3
The latest generation of Wi-Fi security, providing enhanced cryptographic strength and better protection against brute-force attacks.
A mandatory requirement for any modern network deployment, especially those processing payments or handling sensitive data.
Webhook
A method for augmenting or altering the behaviour of a web page or web application with custom callbacks, triggered by specific events.
Used to push real-time data from the WiFi platform to a CRM (e.g., triggering a welcome email the moment a guest connects).
Estudos de Caso
A 200-site retail chain needs to upgrade its legacy guest WiFi. They currently use Cisco Meraki APs with the native Meraki splash page, but marketing cannot export the data easily, and IT is concerned about GDPR compliance regarding data retention.
The chain should retain their Meraki Layer 1/2 infrastructure to avoid massive CapEx. They must deploy a unified Layer 4-6 platform (like Purple) via API integration with the Meraki dashboard. The new architecture will use Meraki for RF delivery and SD-WAN routing, while the unified platform handles the captive portal, RADIUS authentication, and consent capture. The platform will automatically enforce a 12-month data retention policy to satisfy GDPR requirements and provide a bi-directional API sync to their central CRM.
A large stadium complex experiences severe captive portal timeouts and authentication failures during half-time when 15,000 users attempt to connect simultaneously.
The issue is a bottleneck at the Layer 3 (RADIUS) and Layer 4 (Portal) infrastructure, which cannot handle the concurrent connection spikes. The solution requires migrating from an on-premise RADIUS server to an auto-scaling cloud RADIUS service. Additionally, the AP configuration must be optimised to aggressively drop weak client connections (Minimum Bitrate requirements) to preserve airtime, and the captive portal must be served via a robust CDN to handle the burst in HTTP requests.
Análise de Cenário
Q1. You are the IT Director for a 50-site hospital trust. You need to deploy guest WiFi that captures user demographics, but you are subject to strict data sovereignty and compliance audits. A vendor proposes a solution where the APs handle authentication and send data directly to their proprietary cloud analytics tool. Do you accept?
💡 Dica:Consider the implications of hardware lock-in and audit requirements for data processing agreements.
Mostrar Abordagem Recomendada
Reject the proposal. Relying on the AP vendor's proprietary cloud tool creates hardware lock-in and fragments compliance management. Instead, implement a unified platform that overlays the AP infrastructure. This ensures you maintain ownership of the data, can enforce granular consent and retention policies centrally, and can switch AP hardware in the future without losing your compliance architecture or historical data.
Q2. A retail brand wants to trigger an immediate push notification via their mobile app when a high-tier loyalty member walks into a store. They currently rely on MAC address tracking from their APs to detect presence. Why will this fail, and how should it be architected?
💡 Dica:Think about modern mobile OS privacy features and the difference between presence and identity.
Mostrar Abordagem Recomendada
This will fail because iOS and Android use MAC randomisation, meaning the APs will see a different, fake MAC address each time the device connects, making it impossible to reliably identify the loyalty member passively. The architecture must shift to identity resolution via authentication. The user must authenticate via the captive portal (or via an integration like OpenRoaming/Passpoint), binding their session to their profile. Once authenticated, the WiFi platform can use a webhook to signal the CRM/App backend to trigger the notification.
Q3. During a network refresh, you are evaluating Wi-Fi 6 vs Wi-Fi 6E for a chain of small coffee shops (max capacity 40 people). The Wi-Fi 6E access points are 40% more expensive. Which do you choose?
💡 Dica:Consider the primary benefit of the 6 GHz band and the density of the environment.
Mostrar Abordagem Recomendada
Choose Wi-Fi 6. Wi-Fi 6E introduces the 6 GHz band, which is highly beneficial for relieving spectrum congestion in ultra-high-density environments like stadiums or large auditoriums. For a small coffee shop with a maximum capacity of 40 concurrent users, spectrum congestion is unlikely to be a critical issue. Wi-Fi 6 provides sufficient throughput and efficiency features (like OFDMA) at a lower CapEx, improving the overall ROI of the deployment.
Principais Conclusões
- ✓A modern guest WiFi stack consists of six layers: AP infrastructure, Network Controller, RADIUS, Captive Portal, Analytics, and CRM Integration.
- ✓Evaluating these layers in isolation leads to integration complexity, data silos, and compliance risks.
- ✓Mobile OS MAC randomisation means analytics must be anchored to authenticated user identities, not device MAC addresses.
- ✓Decoupling the captive portal and analytics platform from the physical access points prevents hardware lock-in and protects historical data.
- ✓For most multi-site operators, a Unified Platform approach delivers the fastest time-to-value and lowest TCO compared to building in-house or integrating multiple vendors.
- ✓Robust compliance architecture (GDPR/CCPA) requires centralised consent capture and automated data retention policies.



