ISO 27001 Guest WiFi: Um Guia de Conformidade
Esta referência técnica autoritária mapeia as implementações de Guest WiFi diretamente aos controles da ISO 27001:2022, detalhando os requisitos de segregação de rede, registro de eventos (logging) e tratamento de riscos. Ela fornece orientação prática para gerentes de TI e arquitetos de rede sobre como gerar evidências prontas para auditoria e aproveitar as atestações SOC 2 de fornecedores para satisfazer os mandatos de garantia de fornecedores do ISMS.
Ouça este guia
Ver transcrição do podcast
- Resumo Executivo
- Análise Técnica Aprofundada: Mapeando Controles ISO 27001 para a Arquitetura WiFi
- Segregação e Segurança de Rede (Controles A.8.20 e A.8.22)
- Garantia de Fornecedores e Plataformas em Nuvem (Controle A.8.21)
- Registro de Eventos (Logging), Filtragem e Transferência de Informações (Controles A.8.15, A.8.23, A.5.14)
- Guia de Implementação: Construindo o Pacote de Evidências de Auditoria
- Etapa 1: Formalizar a Avaliação de Risco
- Etapa 2: Exportar Configurações como Evidência
- Etapa 3: Estabelecer a Cadência de Revisão de Fornecedores
- Melhores Práticas para Locais Corporativos
- Solução de Problemas e Mitigação de Riscos
- ROI e Impacto nos Negócios
- Resumo em Áudio

Resumo Executivo
Para locais corporativos — seja um hotel de 500 quartos, uma rede de varejo multi-site ou um estádio com 50.000 lugares — o Guest WiFi raramente é tratado com o mesmo rigor de governança que a LAN corporativa. No entanto, sob a ISO 27001:2022, uma rede sem fio pública é um ativo de informação ativo que se cruza com o limite da sua rede, relacionamentos com fornecedores e obrigações legais. Este guia traduz os requisitos teóricos de um Sistema de Gestão de Segurança da Informação (ISMS) em resultados práticos de engenharia e conformidade para implementações de Guest WiFi .
Ao tratar a rede de convidados não como um serviço de commodity, mas como um segmento auditado, os líderes de TI podem mitigar riscos de movimento lateral, garantir a conformidade regulatória e produzir evidências definitivas para os auditores líderes. Este guia detalha os controles específicos do Anexo A aplicáveis a implementações sem fio, descreve a metodologia de avaliação de risco necessária e explica como construir um pacote de evidências de auditoria defensável — economizando centenas de horas durante os ciclos de certificação.
Análise Técnica Aprofundada: Mapeando Controles ISO 27001 para a Arquitetura WiFi
A ISO 27001:2022 reestruturou seus controles do Anexo A em quatro temas. Para redes sem fio de convidados, os requisitos críticos residem principalmente nos domínios Tecnológico e Organizacional. Compreender como esses controles se traduzem em configurações de rede é a base da conformidade.
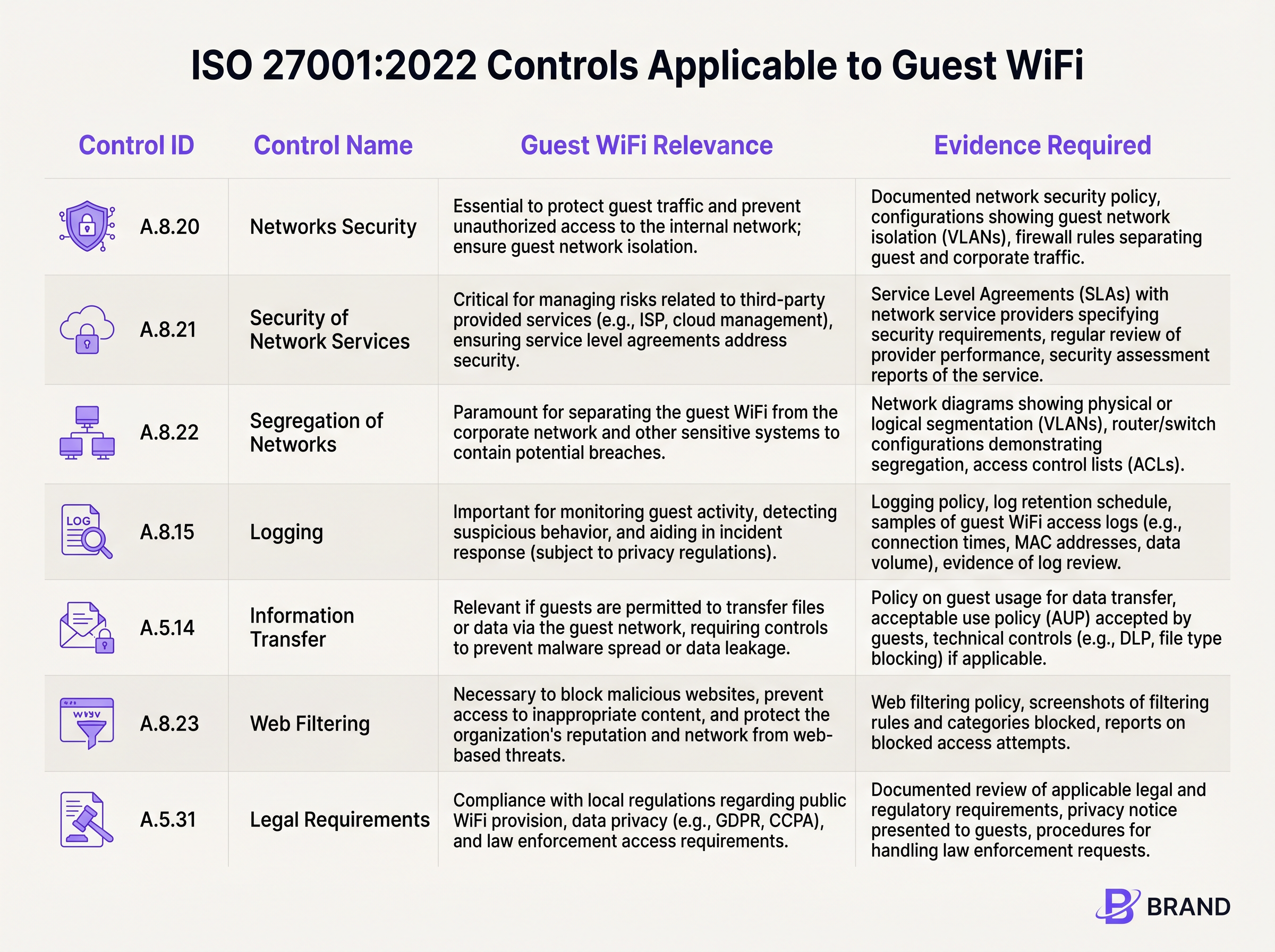
Segregação e Segurança de Rede (Controles A.8.20 e A.8.22)
O requisito fundamental para qualquer rede de convidados é o isolamento rigoroso. O Controle A.8.22 (Segregação de Redes) exige que grupos de serviços de informação sejam segregados. Em termos práticos, isso exige a implantação de VLANs dedicadas para o tráfego de convidados que sejam lógica (e, quando necessário, fisicamente) separadas das sub-redes corporativas, sistemas de ponto de venda (POS) e dispositivos IoT de gerenciamento de edifícios.
Juntamente com o Controle A.8.20 (Segurança de Redes), esse isolamento deve ser imposto por meio de conjuntos de regras de firewall robustos e Listas de Controle de Acesso (ACLs). Um auditor esperará ver configurações que neguem explicitamente o roteamento da VLAN de convidados para qualquer espaço IP interno RFC 1918. Se um testador de penetração no SSID de convidados puder alcançar a interface de gerenciamento de um gateway de Sensors ou um compartilhamento de arquivos corporativo, isso constitui uma não conformidade grave.
Garantia de Fornecedores e Plataformas em Nuvem (Controle A.8.21)
O Guest WiFi moderno depende fortemente de provedores de serviços gerenciados e portais cativos hospedados em nuvem. O Controle A.8.21 (Segurança de Serviços de Rede) dita que esses relacionamentos com fornecedores devem ser governados por requisitos de segurança. É aqui que as atestações de fornecedores se tornam críticas. Em vez de conduzir uma auditoria personalizada de uma plataforma WiFi em nuvem, as organizações devem confiar no relatório SOC 2 Tipo II do fornecedor. Plataformas como a Purple possuem alinhamento SOC 2, fornecendo garantia independente sobre seus controles de segurança, disponibilidade e privacidade. Esta documentação alimenta diretamente o seu arquivo de garantia de fornecedores do ISMS.
Registro de Eventos (Logging), Filtragem e Transferência de Informações (Controles A.8.15, A.8.23, A.5.14)
A visibilidade e o controle sobre o tráfego de convidados são exigidos por vários controles sobrepostos. O Controle A.8.15 (Registro de Eventos) exige a retenção de eventos de conexão e logs de autenticação. No entanto, isso deve ser equilibrado com os princípios de minimização de dados. O Captive Portal serve como o mecanismo principal para o Controle A.5.14 (Transferência de Informações), onde os convidados devem aceitar uma Política de Uso Aceitável (AUP) antes que o acesso seja concedido.
Além disso, o Controle A.8.23 (Filtragem Web) exige a implantação de filtragem baseada em DNS ou proxies em nuvem para bloquear domínios maliciosos e infraestrutura de comando e controle, protegendo tanto a reputação da rede quanto os dispositivos a ela conectados.
Guia de Implementação: Construindo o Pacote de Evidências de Auditoria
Implementar a tecnologia é apenas metade da batalha; prová-la a um auditor é a outra. As etapas a seguir descrevem como traduzir configurações técnicas em um pacote de evidências ISO 27001 defensável.
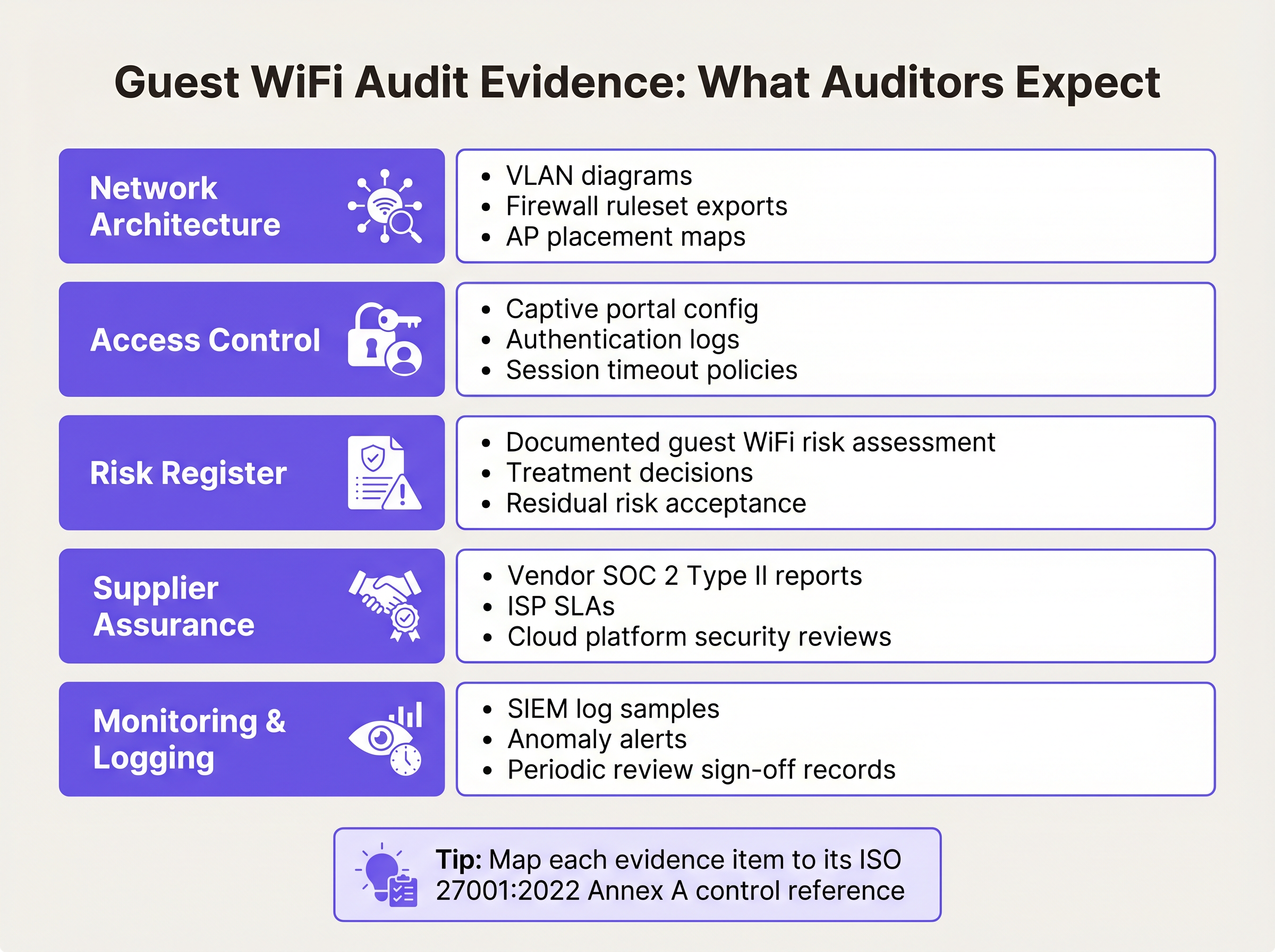
Etapa 1: Formalizar a Avaliação de Risco
O ISMS deve incluir uma avaliação de risco formal especificamente para o ativo Guest WiFi. Isso deve documentar ameaças como movimento lateral não autorizado, propagação de malware e exaustão de largura de banda. Para cada ameaça, documente a probabilidade, o impacto e o tratamento de risco escolhido (por exemplo, mitigar via isolamento de VLAN e isolamento de cliente). A Declaração de Aplicabilidade (SoA) deve referenciar esta avaliação como a justificativa para a seleção de controles como A.8.22 e A.8.23.
Etapa 2: Exportar Configurações como Evidência
Auditores exigem evidências pontuais das configurações. Gere um diagrama de rede abrangente rotulando claramente a VLAN de convidados e seus limites. Exporte o conjunto de regras do firewall demonstrando as regras de negação explícita para roteamento interno. Se você estiver usando uma plataforma em nuvem, exporte a configuração do Captive Portal mostrando o ponto de verificação obrigatório de aceitação da AUP. Para orientação sobre como equilibrar a experiência do usuário com esses pontos de verificação de segurança, revise nosso guia sobre Guest WiFi Session Timeouts: Equilibrando UX e Segurança .
Etapa 3: Estabelecer a Cadência de Revisão de Fornecedores
A garantia de fornecedores não é uma atividade única. Estabeleça um calendário para revisões anuais de seus provedores de ISP e portal em nuvem. Solicite seus relatórios SOC 2 Tipo II atualizados e documente uma revisão formal da gerência desses relatórios. Se o fornecedorSe a auditoria destacar quaisquer exceções, documente como essas exceções impactam sua própria postura de risco.
Melhores Práticas para Locais Corporativos
A implantação de WiFi para convidados em conformidade em ambientes complexos como Hospitalidade ou centros de Transporte exige a adesão a melhores práticas neutras em relação a fornecedores que satisfaçam tanto as demandas de segurança quanto as operacionais.
- Impor Isolamento de Cliente: No nível do ponto de acesso, habilite o isolamento de cliente (às vezes chamado de isolamento de AP ou modo convidado). Isso impede que dispositivos conectados ao mesmo SSID se comuniquem diretamente entre si, mitigando ataques peer-to-peer e a propagação de malware.
- Implementar Gerenciamento Robusto de Sessões: Configure tempos limite de sessão forçados que exijam reautenticação. Para um ambiente de varejo, um tempo limite de 12 horas pode ser apropriado; para um aeroporto, um tempo limite de 4 horas garante que as sessões abandonadas sejam encerradas. Isso limita a janela de oportunidade para endereços MAC sequestrados.
- Alinhar com as Regulamentações de Privacidade de Dados: Garanta que a coleta de dados do seu Captive Portal esteja alinhada com as leis de privacidade locais (por exemplo, GDPR). Colete apenas os dados necessários para o serviço ou para os quais você tenha consentimento explícito e documentado. Isso apoia diretamente o Controle A.5.31 (Requisitos Legais).
Solução de Problemas e Mitigação de Riscos
Mesmo com uma arquitetura robusta, pode ocorrer desvio de conformidade. O modo de falha mais comum é o 'scope creep' (expansão do escopo) — onde a rede de convidados é totalmente excluída do escopo do ISMS (levando a falhas de auditoria) ou tem seu escopo excessivamente ampliado (aplicando controles internos desnecessários a dispositivos de convidados).
Outro problema frequente é a degradação da segmentação de rede. Atualizações de firmware ou alterações de rede de emergência podem inadvertidamente alterar o roteamento de VLAN. Para mitigar isso, implemente monitoramento automatizado de configuração ou agende revisões manuais trimestrais do conjunto de regras do firewall que governa o segmento de convidados. Se você estiver gerenciando vários sites distribuídos, considere as vantagens de conformidade das redes de longa distância modernas; nossa visão geral de Os Principais Benefícios da SD WAN para Empresas Modernas explora como a aplicação centralizada de políticas reduz a complexidade da auditoria.
ROI e Impacto nos Negócios
Investir na conformidade ISO 27001 para WiFi de convidados oferece valor de negócio mensurável além de simplesmente passar em uma auditoria. Uma infraestrutura sem fio segura e em conformidade protege a reputação da marca do local, impedindo que a rede seja usada como base para crimes cibernéticos.
Além disso, ao aproveitar uma plataforma alinhada com SOC 2 que integra WiFi Analytics , os locais podem extrair com segurança valor comercial dos dados de fluxo de pessoas, mantendo estrita adesão aos controles de privacidade e segurança de dados. A redução no tempo de preparação da auditoria — muitas vezes economizando dezenas de horas de engenharia anualmente ao depender de evidências de plataforma exportáveis — proporciona um ROI operacional direto.
Resumo em Áudio
Para uma análise detalhada desses conceitos, ouça nosso podcast de briefing técnico de 10 minutos:
Definições principais
VLAN Segregation
The logical separation of a physical network into distinct broadcast domains, preventing traffic from one segment from reaching another without passing through a routed firewall.
Critical for satisfying ISO 27001 Control A.8.22, ensuring guest devices cannot access corporate or operational technology systems.
Client Isolation
A wireless network setting that prevents devices connected to the same Access Point or SSID from communicating directly with one another.
Used to mitigate peer-to-peer attacks and malware spread on public networks, supporting Control A.8.20.
SOC 2 Type II
An independent audit report that evaluates a service organisation's controls related to security, availability, and privacy over a specified period (usually 6-12 months).
The primary evidence used by IT teams to satisfy Control A.8.21 (Security of Network Services) for cloud-hosted WiFi platforms.
Statement of Applicability (SoA)
A mandatory ISO 27001 document that lists all Annex A controls, stating whether each is applied or excluded, along with the justification.
The SoA must explicitly reference the guest WiFi risk assessment to justify the inclusion of network segregation and filtering controls.
Captive Portal
A web page that a user of a public access network is obliged to view and interact with before access is granted.
Serves as the technical enforcement point for Acceptable Use Policies and privacy consent, generating the logs required for Control A.8.15.
Acceptable Use Policy (AUP)
A set of rules applied by the owner of a network that restrict the ways in which the network may be used.
Required evidence for Control A.5.14, demonstrating that guests have been informed of their obligations before transferring data.
WPA3-Personal (SAE)
The modern wireless security protocol that uses Simultaneous Authentication of Equals to provide forward secrecy, protecting session traffic even if the shared password is known.
The recommended security standard for shared-passphrase guest networks to ensure baseline encryption of the wireless medium.
Risk Treatment
The process of selecting and implementing measures to modify risk, typically categorised as mitigate, accept, transfer, or avoid.
IT managers must document how they treat the risks associated with guest WiFi (e.g., mitigating lateral movement via firewalls) within the ISMS.
Exemplos práticos
A 400-room hotel group needs to deploy guest WiFi across three properties. The IT Director wants to keep the guest network out of the ISO 27001 ISMS scope to save time. Is this permissible, and what are the architectural requirements if it is included?
Excluding the guest network from the ISMS scope is highly risky if the physical infrastructure (switches, APs, internet circuits) is shared with the corporate network, or if guest authentication captures personal data (bringing it under A.5.31 Legal Requirements). The correct approach is to include it in scope but apply proportionate controls. Architecturally, the hotel must implement strict VLAN segregation (Control A.8.22), apply client isolation at the AP level, and route guest traffic directly to the internet via a firewall that explicitly denies access to the hotel's property management system (PMS) and corporate subnets.
During an internal audit of a retail chain's WiFi, the auditor notes that the cloud-based captive portal provider has not been assessed for security in over two years. How should the network architect remediate this nonconformity against Control A.8.21?
The architect must immediately request the latest SOC 2 Type II report from the captive portal provider. Upon receipt, the architect should formally review the report, noting the auditor's opinion and any exceptions listed in the Trust Services Criteria. This review must be documented, signed off by management, and filed in the ISMS supplier assurance repository. A recurring calendar event should be established to request this report annually.
Questões práticas
Q1. You are preparing for an ISO 27001 surveillance audit. The auditor asks for evidence that the guest WiFi network is secure from internal threats. What three specific artifacts should you provide?
Dica: Think about architecture, policy enforcement, and supplier management.
Ver resposta modelo
- A network diagram and firewall ruleset proving VLAN segregation (Control A.8.22). 2) Captive portal logs showing guests accepting the Acceptable Use Policy (Control A.5.14). 3) The latest SOC 2 Type II report from your cloud WiFi platform provider (Control A.8.21).
Q2. A stadium operations director wants to disable the captive portal to 'speed up entry' and just use an open network with no terms of service. As the Information Security Manager, how do you respond using ISO 27001 principles?
Dica: Consider the legal and logging implications of an unmanaged open network.
Ver resposta modelo
You must advise against this, as it violates Control A.5.14 (Information Transfer) by removing the Acceptable Use Policy checkpoint, and compromises Control A.8.15 (Logging) by removing the ability to tie sessions to an authentication event. Furthermore, it increases the venue's legal exposure under Control A.5.31 if the network is used for illicit purposes without a documented terms of service.
Q3. Your guest WiFi risk assessment identifies 'Access to malicious websites' as a high risk. You decide to implement DNS filtering. How do you document this in the ISMS?
Dica: Link the threat to the specific Annex A control and the SoA.
Ver resposta modelo
Update the Risk Register to show the threat is treated by implementing DNS filtering. In the Statement of Applicability (SoA), mark Control A.8.23 (Web Filtering) as 'Applicable', citing the risk assessment as the justification, and reference the DNS filtering configuration as the implementation evidence.
Continue a ler esta série
O Futuro da Segurança Wi-Fi: NAC Orientado por IA e Detecção de Ameaças
Este guia abrangente explora a evolução da segurança Wi-Fi empresarial, desde o WPA2 legado até o Network Access Control (NAC) orientado por IA e a detecção de ameaças. Projetado para líderes de TI, ele oferece estratégias de implantação acionáveis para proteger ambientes de alta densidade, como varejo, hotelaria e estádios, usando as redes baseadas em identidade da Purple.
Gerenciando a Segurança de Dispositivos IoT com NAC e MPSK
Este guia técnico detalha como ambientes corporativos podem proteger dispositivos IoT sem interface de usuário (headless) usando a arquitetura Multiple Pre-Shared Key (MPSK) e Network Access Control (NAC). Ele fornece etapas de implementação acionáveis para alcançar micro-segmentação, conter raios de explosão de segurança e manter a conformidade sem sacrificar a escalabilidade.
RadSec: Como o RADIUS sobre TLS Melhora a Segurança da Autenticação WiFi
Esta referência técnica autoritária explica como o RadSec (RFC 6614) protege a autenticação WiFi empresarial ao encapsular o tráfego RADIUS tradicional em criptografia TLS. Projetado para gerentes de TI e arquitetos de rede, ele aborda arquitetura, estratégias de implantação e etapas práticas para mitigar os riscos do tráfego RADIUS UDP não criptografado em redes corporativas e de convidados.