ISO 27001 Guest WiFi : Un précis de conformité
Cette référence technique faisant autorité met en correspondance les déploiements de Guest WiFi directement avec les contrôles ISO 27001:2022, détaillant les exigences en matière de segmentation réseau, de journalisation et de traitement des risques. Elle fournit des orientations concrètes aux responsables informatiques et aux architectes réseau sur la manière de générer des preuves prêtes pour l'audit et de tirer parti des attestations SOC 2 des fournisseurs pour satisfaire aux exigences d'assurance des fournisseurs de l'ISMS.
Écouter ce guide
Voir la transcription du podcast
- Résumé Exécutif
- Approfondissement technique : Cartographie des contrôles ISO 27001 à l'architecture WiFi
- Segmentation et sécurité du réseau (Contrôles A.8.20 et A.8.22)
- Assurance des fournisseurs et plateformes cloud (Contrôle A.8.21)
- Journalisation, filtrage et transfert d'informations (Contrôles A.8.15, A.8.23, A.5.14)
- Guide d'implémentation : Constitution du dossier de preuves d'audit
- Étape 1 : Formaliser l'évaluation des risques
- Étape 2 : Exporter les configurations comme preuves
- Étape 3 : Établir la cadence de révision des fournisseurs
- Bonnes pratiques pour les sites d'entreprise
- Dépannage et atténuation des risques
- ROI et impact commercial
- Briefing audio

Résumé Exécutif
Pour les entreprises – qu'il s'agisse d'un hôtel de 500 chambres, d'une chaîne de magasins multi-sites ou d'un stade de 50 000 places – le Guest WiFi est rarement traité avec la même rigueur de gouvernance que le LAN d'entreprise. Cependant, selon la norme ISO 27001:2022, un réseau sans fil public est un actif informationnel vivant qui recoupe la limite de votre réseau, les relations avec les fournisseurs et les obligations légales. Ce précis traduit les exigences théoriques d'un Système de Management de la Sécurité de l'Information (SMSI) en résultats pratiques d'ingénierie et de conformité pour les déploiements de Guest WiFi .
En traitant le réseau invité non pas comme un service de base mais comme un segment audité, les responsables informatiques peuvent atténuer les risques de mouvement latéral, assurer la conformité réglementaire et produire des preuves définitives pour les auditeurs principaux. Ce guide détaille les contrôles spécifiques de l'Annexe A applicables aux déploiements sans fil, décrit la méthodologie d'évaluation des risques requise et explique comment constituer un dossier de preuves d'audit défendable, permettant d'économiser des centaines d'heures pendant les cycles de certification.
Approfondissement technique : Cartographie des contrôles ISO 27001 à l'architecture WiFi
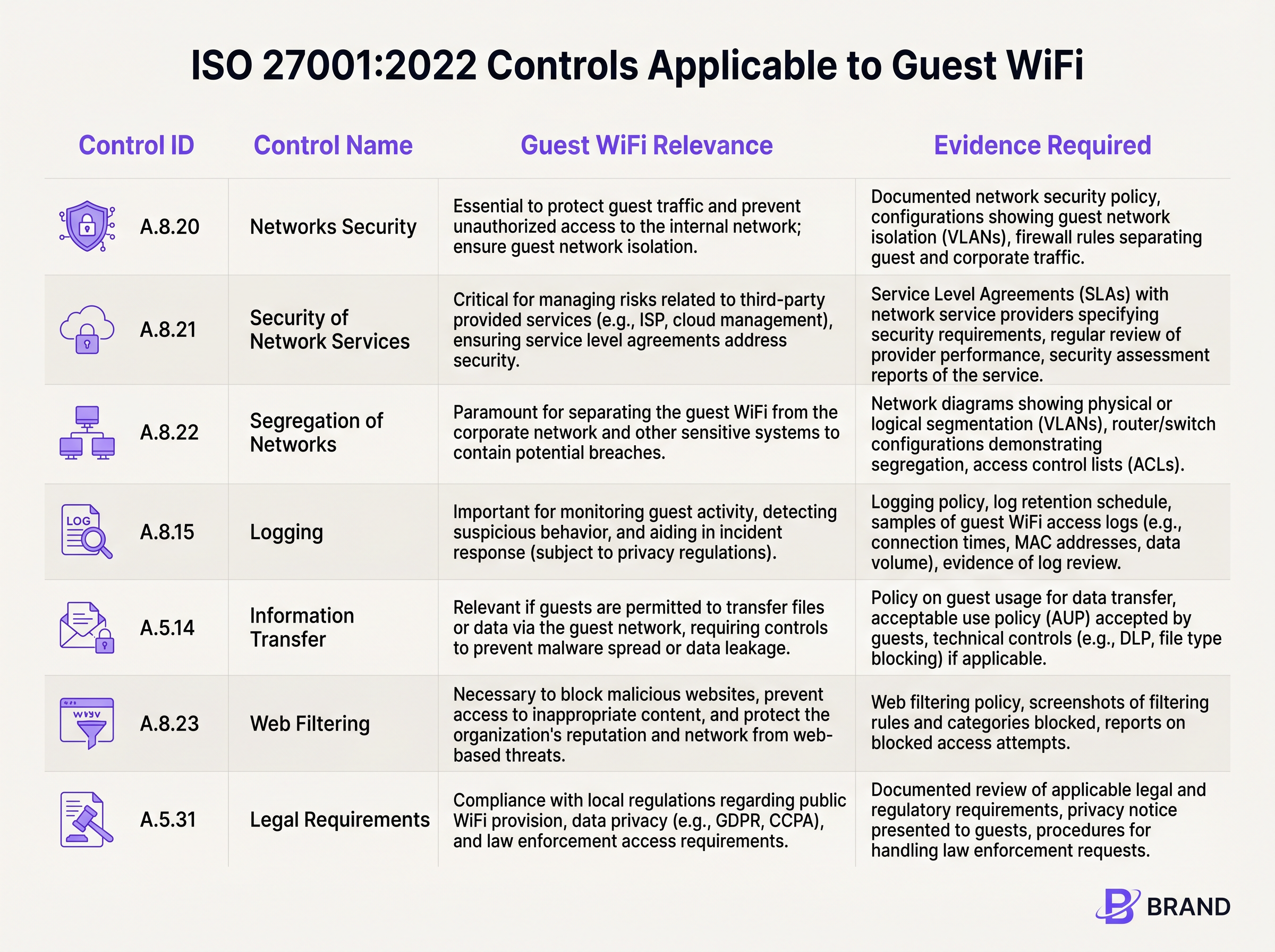
L'ISO 27001:2022 a restructuré ses contrôles de l'Annexe A en quatre thèmes. Pour les réseaux sans fil invités, les exigences critiques résident principalement dans les domaines technologique et organisationnel. Comprendre comment ces contrôles se traduisent en configurations réseau est le fondement de la conformité.
Segmentation et sécurité du réseau (Contrôles A.8.20 et A.8.22)
L'exigence fondamentale pour tout réseau invité est une isolation stricte. Le Contrôle A.8.22 (Ségrégation des réseaux) exige que les groupes de services d'information soient ségrégués. En termes pratiques, cela nécessite le déploiement de VLAN dédiés pour le trafic invité, logiquement (et si nécessaire, physiquement) séparés des sous-réseaux d'entreprise, des systèmes de point de vente (POS) et des dispositifs IoT de gestion des bâtiments.
Associée au Contrôle A.8.20 (Sécurité des réseaux), cette isolation doit être appliquée via des ensembles de règles de pare-feu robustes et des listes de contrôle d'accès (ACL). Un auditeur s'attendra à voir des configurations qui refusent explicitement le routage du VLAN invité vers tout espace IP interne RFC 1918. Si un testeur d'intrusion sur le SSID invité peut atteindre l'interface de gestion d'une passerelle Sensors ou un partage de fichiers d'entreprise, cela constitue une non-conformité majeure.
Assurance des fournisseurs et plateformes cloud (Contrôle A.8.21)
Le Guest WiFi moderne repose fortement sur les fournisseurs de services gérés et les portails captifs hébergés dans le cloud. Le Contrôle A.8.21 (Sécurité des services réseau) stipule que ces relations avec les fournisseurs doivent être régies par des exigences de sécurité. C'est là que les attestations des fournisseurs deviennent critiques. Au lieu de mener un audit sur mesure d'une plateforme WiFi cloud, les organisations devraient s'appuyer sur le rapport SOC 2 Type II du fournisseur. Des plateformes comme Purple sont alignées SOC 2, offrant une assurance indépendante sur leurs contrôles de sécurité, de disponibilité et de confidentialité. Cette documentation alimente directement votre dossier d'assurance des fournisseurs de l'ISMS.
Journalisation, filtrage et transfert d'informations (Contrôles A.8.15, A.8.23, A.5.14)
La visibilité et le contrôle du trafic invité sont imposés par plusieurs contrôles qui se chevauchent. Le Contrôle A.8.15 (Journalisation) exige la conservation des événements de connexion et des journaux d'authentification. Cependant, cela doit être équilibré avec les principes de minimisation des données. Le portail captif sert de mécanisme principal pour le Contrôle A.5.14 (Transfert d'informations), où les invités doivent accepter une Politique d'Utilisation Acceptable (PUA) avant que l'accès ne soit accordé.
De plus, le Contrôle A.8.23 (Filtrage Web) nécessite le déploiement d'un filtrage basé sur DNS ou de proxys cloud pour bloquer les domaines malveillants et l'infrastructure de commande et de contrôle, protégeant ainsi la réputation du réseau et les appareils qui y sont connectés.
Guide d'implémentation : Constitution du dossier de preuves d'audit
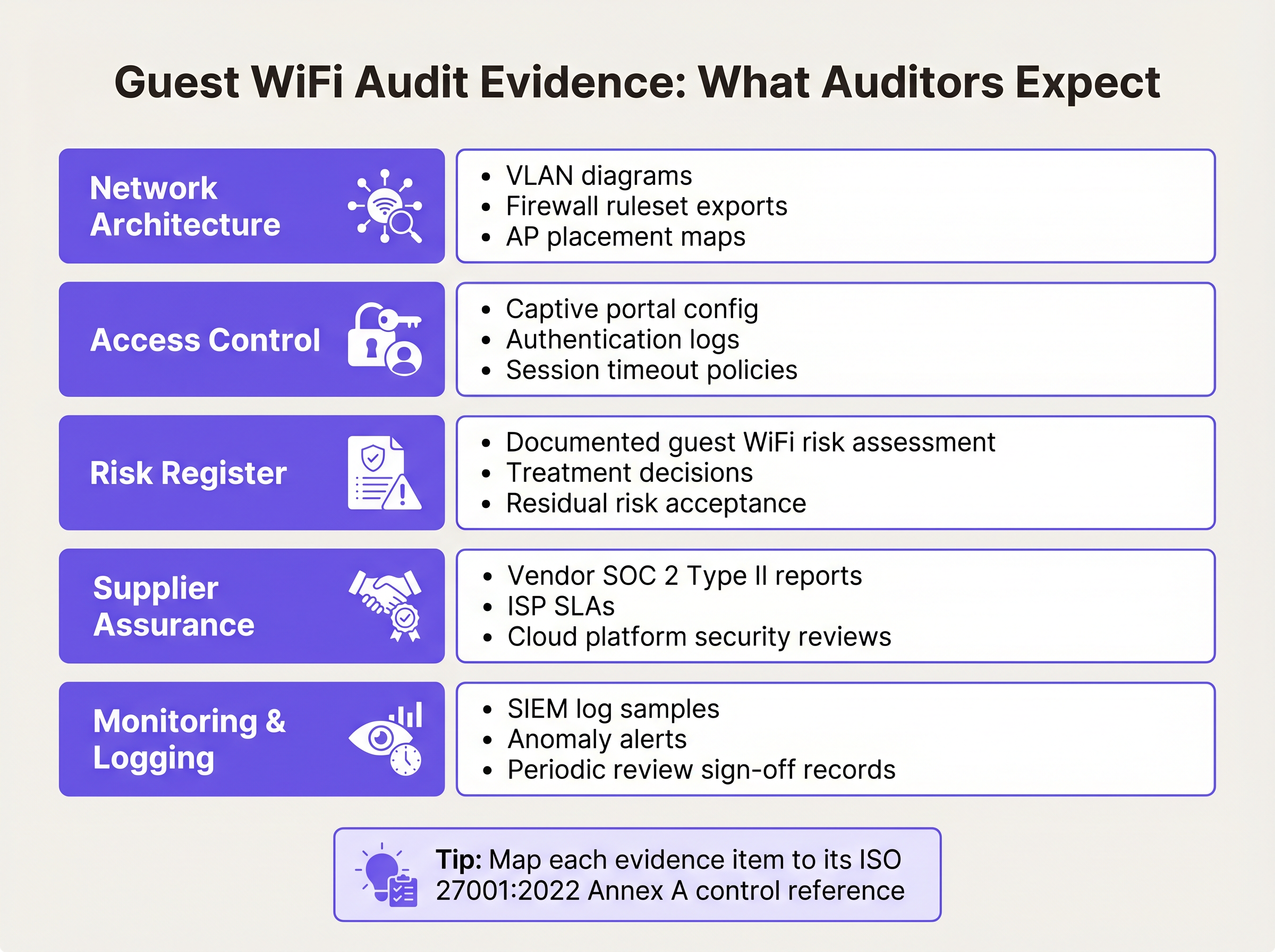
Mettre en œuvre la technologie n'est que la moitié de la bataille ; le prouver à un auditeur est l'autre moitié. Les étapes suivantes décrivent comment traduire les configurations techniques en un dossier de preuves ISO 27001 défendable.
Étape 1 : Formaliser l'évaluation des risques
Le SMSI doit inclure une évaluation formelle des risques spécifiquement pour l'actif Guest WiFi. Celle-ci doit documenter les menaces telles que le mouvement latéral non autorisé, la propagation de logiciels malveillants et l'épuisement de la bande passante. Pour chaque menace, documentez la probabilité, l'impact et le traitement des risques choisi (par exemple, atténuer via l'isolation VLAN et l'isolation client). La Déclaration d'Applicabilité (SoA) doit faire référence à cette évaluation comme justification de la sélection de contrôles tels que A.8.22 et A.8.23.
Étape 2 : Exporter les configurations comme preuves
Les auditeurs exigent des preuves ponctuelles des configurations. Générez un diagramme réseau complet étiquetant clairement le VLAN invité et ses limites. Exportez l'ensemble de règles du pare-feu démontrant les règles de refus explicites pour le routage interne. Si vous utilisez une plateforme cloud, exportez la configuration du portail captif montrant le point de contrôle obligatoire d'acceptation de la PUA. Pour des conseils sur l'équilibre entre l'expérience utilisateur et ces points de contrôle de sécurité, consultez notre guide sur Guest WiFi Session Timeouts : Équilibrer l'UX et la sécurité .
Étape 3 : Établir la cadence de révision des fournisseurs
L'assurance des fournisseurs n'est pas une activité ponctuelle. Établissez un calendrier pour les examens annuels de votre FAI et de vos fournisseurs de portails cloud. Demandez leurs rapports SOC 2 Type II mis à jour et documentez un examen formel de ces rapports par la direction. Si le fournisseurL'audit met en évidence toute exception, documentez comment ces exceptions impactent votre propre posture de risque.
Bonnes pratiques pour les sites d'entreprise
Le déploiement d'un WiFi invité conforme dans des environnements complexes tels que les pôles Hôtellerie ou Transport exige le respect de bonnes pratiques indépendantes des fournisseurs qui satisfont à la fois les exigences de sécurité et opérationnelles.
- Appliquer l'isolation des clients : Au niveau du point d'accès, activez l'isolation des clients (parfois appelée isolation AP ou mode invité). Cela empêche les appareils connectés au même SSID de communiquer directement entre eux, atténuant ainsi les attaques peer-to-peer et la propagation de logiciels malveillants.
- Mettre en œuvre une gestion robuste des sessions : Configurez des délais d'expiration de session forcés qui nécessitent une réauthentification. Pour un environnement de vente au détail, un délai d'expiration de 12 heures peut être approprié ; pour un aéroport, un délai d'expiration de 4 heures garantit la fin des sessions abandonnées. Cela limite la fenêtre d'opportunité pour les adresses MAC détournées.
- S'aligner sur les réglementations en matière de confidentialité des données : Assurez-vous que la collecte de données de votre Captive Portal est conforme aux lois locales sur la confidentialité (par exemple, GDPR). Ne collectez que les données nécessaires au service ou pour lesquelles vous avez un consentement explicite et documenté. Cela soutient directement le Contrôle A.5.31 (Exigences légales).
Dépannage et atténuation des risques
Même avec une architecture robuste, des écarts de conformité peuvent survenir. Le mode de défaillance le plus courant est le « glissement de périmètre » (scope creep) — où le réseau invité est soit entièrement exclu du périmètre de l'ISMS (entraînant des échecs d'audit), soit sur-périmétré (appliquant des contrôles internes inutiles aux appareils invités).
Un autre problème fréquent est la dégradation de la segmentation du réseau. Les mises à jour de firmware ou les modifications de réseau d'urgence peuvent modifier par inadvertance le routage VLAN. Pour atténuer cela, mettez en œuvre une surveillance automatisée de la configuration ou planifiez des examens manuels trimestriels de l'ensemble des règles de pare-feu régissant le segment invité. Si vous gérez plusieurs sites distribués, considérez les avantages en matière de conformité des réseaux étendus modernes ; notre aperçu des Avantages clés du SD WAN pour les entreprises modernes explore comment l'application centralisée des politiques réduit la complexité de l'audit.
ROI et impact commercial
Investir dans la conformité ISO 27001 pour le WiFi invité offre une valeur commerciale mesurable au-delà du simple fait de réussir un audit. Une infrastructure sans fil sécurisée et conforme protège la réputation de la marque du site en empêchant l'utilisation du réseau comme terrain d'action pour la cybercriminalité.
De plus, en tirant parti d'une plateforme alignée sur SOC 2 qui intègre WiFi Analytics , les sites peuvent extraire en toute sécurité de la valeur commerciale des données de fréquentation tout en maintenant une stricte adhésion aux contrôles de confidentialité et de sécurité des données. La réduction du temps de préparation à l'audit — économisant souvent des dizaines d'heures d'ingénierie par an en s'appuyant sur des preuves de plateforme exportables — offre un ROI opérationnel direct.
Briefing audio
Pour une présentation détaillée de ces concepts, écoutez notre podcast de briefing technique de 10 minutes :
Définitions clés
VLAN Segregation
The logical separation of a physical network into distinct broadcast domains, preventing traffic from one segment from reaching another without passing through a routed firewall.
Critical for satisfying ISO 27001 Control A.8.22, ensuring guest devices cannot access corporate or operational technology systems.
Client Isolation
A wireless network setting that prevents devices connected to the same Access Point or SSID from communicating directly with one another.
Used to mitigate peer-to-peer attacks and malware spread on public networks, supporting Control A.8.20.
SOC 2 Type II
An independent audit report that evaluates a service organisation's controls related to security, availability, and privacy over a specified period (usually 6-12 months).
The primary evidence used by IT teams to satisfy Control A.8.21 (Security of Network Services) for cloud-hosted WiFi platforms.
Statement of Applicability (SoA)
A mandatory ISO 27001 document that lists all Annex A controls, stating whether each is applied or excluded, along with the justification.
The SoA must explicitly reference the guest WiFi risk assessment to justify the inclusion of network segregation and filtering controls.
Captive Portal
A web page that a user of a public access network is obliged to view and interact with before access is granted.
Serves as the technical enforcement point for Acceptable Use Policies and privacy consent, generating the logs required for Control A.8.15.
Acceptable Use Policy (AUP)
A set of rules applied by the owner of a network that restrict the ways in which the network may be used.
Required evidence for Control A.5.14, demonstrating that guests have been informed of their obligations before transferring data.
WPA3-Personal (SAE)
The modern wireless security protocol that uses Simultaneous Authentication of Equals to provide forward secrecy, protecting session traffic even if the shared password is known.
The recommended security standard for shared-passphrase guest networks to ensure baseline encryption of the wireless medium.
Risk Treatment
The process of selecting and implementing measures to modify risk, typically categorised as mitigate, accept, transfer, or avoid.
IT managers must document how they treat the risks associated with guest WiFi (e.g., mitigating lateral movement via firewalls) within the ISMS.
Exemples concrets
A 400-room hotel group needs to deploy guest WiFi across three properties. The IT Director wants to keep the guest network out of the ISO 27001 ISMS scope to save time. Is this permissible, and what are the architectural requirements if it is included?
Excluding the guest network from the ISMS scope is highly risky if the physical infrastructure (switches, APs, internet circuits) is shared with the corporate network, or if guest authentication captures personal data (bringing it under A.5.31 Legal Requirements). The correct approach is to include it in scope but apply proportionate controls. Architecturally, the hotel must implement strict VLAN segregation (Control A.8.22), apply client isolation at the AP level, and route guest traffic directly to the internet via a firewall that explicitly denies access to the hotel's property management system (PMS) and corporate subnets.
During an internal audit of a retail chain's WiFi, the auditor notes that the cloud-based captive portal provider has not been assessed for security in over two years. How should the network architect remediate this nonconformity against Control A.8.21?
The architect must immediately request the latest SOC 2 Type II report from the captive portal provider. Upon receipt, the architect should formally review the report, noting the auditor's opinion and any exceptions listed in the Trust Services Criteria. This review must be documented, signed off by management, and filed in the ISMS supplier assurance repository. A recurring calendar event should be established to request this report annually.
Questions d'entraînement
Q1. You are preparing for an ISO 27001 surveillance audit. The auditor asks for evidence that the guest WiFi network is secure from internal threats. What three specific artifacts should you provide?
Conseil : Think about architecture, policy enforcement, and supplier management.
Voir la réponse type
- A network diagram and firewall ruleset proving VLAN segregation (Control A.8.22). 2) Captive portal logs showing guests accepting the Acceptable Use Policy (Control A.5.14). 3) The latest SOC 2 Type II report from your cloud WiFi platform provider (Control A.8.21).
Q2. A stadium operations director wants to disable the captive portal to 'speed up entry' and just use an open network with no terms of service. As the Information Security Manager, how do you respond using ISO 27001 principles?
Conseil : Consider the legal and logging implications of an unmanaged open network.
Voir la réponse type
You must advise against this, as it violates Control A.5.14 (Information Transfer) by removing the Acceptable Use Policy checkpoint, and compromises Control A.8.15 (Logging) by removing the ability to tie sessions to an authentication event. Furthermore, it increases the venue's legal exposure under Control A.5.31 if the network is used for illicit purposes without a documented terms of service.
Q3. Your guest WiFi risk assessment identifies 'Access to malicious websites' as a high risk. You decide to implement DNS filtering. How do you document this in the ISMS?
Conseil : Link the threat to the specific Annex A control and the SoA.
Voir la réponse type
Update the Risk Register to show the threat is treated by implementing DNS filtering. In the Statement of Applicability (SoA), mark Control A.8.23 (Web Filtering) as 'Applicable', citing the risk assessment as the justification, and reference the DNS filtering configuration as the implementation evidence.
Continuer la lecture de cette série
Conditions d'utilisation du WiFi pour le personnel : Essentiels juridiques et de conformité
Ce guide présente les aspects juridiques et techniques essentiels pour rédiger et appliquer les conditions d'utilisation du WiFi pour le personnel dans les établissements d'entreprise. Il détaille les éléments à inclure dans une charte d'utilisation acceptable (AUP), comment respecter les exigences du GDPR et de la norme PCI DSS, et comment déployer l'authentification basée sur l'identité et la segmentation du réseau pour protéger les actifs de l'entreprise. Les responsables informatiques, les équipes RH et les directeurs des opérations des hôtels, des chaînes de magasins, des stades et des organisations du secteur public y trouveront des conseils pratiques à mettre en œuvre dès ce trimestre.
L'avenir de la sécurité Wi-Fi : NAC et détection des menaces basés sur l'IA
Ce guide faisant autorité explore l'évolution de la sécurité Wi-Fi d'entreprise, du WPA2 hérité au contrôle d'accès réseau (NAC) basé sur l'IA et à la détection des menaces. Conçu pour les leaders informatiques, il fournit des stratégies de déploiement exploitables pour sécuriser les environnements à haute densité comme le commerce de détail, l'hôtellerie et les stades, en utilisant les réseaux basés sur l'identité de Purple.
Gestion de la sécurité des appareils IoT avec NAC et MPSK
Ce guide technique détaille comment les entreprises peuvent sécuriser les appareils IoT sans interface utilisateur en utilisant une architecture de clés pré-partagées multiples (MPSK) et le contrôle d'accès réseau (NAC). Il fournit des étapes de mise en œuvre concrètes pour réaliser la micro-segmentation, contenir les rayons d'explosion de sécurité et maintenir la conformité sans sacrifier l'évolutivité.