ISO 27001 Guest WiFi: Una guía de cumplimiento
Esta referencia técnica autorizada relaciona directamente las implementaciones de Guest WiFi con los controles de ISO 27001:2022, detallando los requisitos de segregación de red, registro y tratamiento de riesgos. Ofrece orientación práctica para gerentes de TI y arquitectos de red sobre cómo generar evidencia lista para auditorías y aprovechar las certificaciones SOC 2 de los proveedores para cumplir con los mandatos de aseguramiento de proveedores del SGSI.
Escuchar esta guía
Ver transcripción del podcast
- Resumen Ejecutivo
- Análisis Técnico Detallado: Mapeo de los Controles ISO 27001 a la Arquitectura WiFi
- Segregación y Seguridad de la Red (Controles A.8.20 y A.8.22)
- Aseguramiento de Proveedores y Plataformas en la Nube (Control A.8.21)
- Registro, Filtrado y Transferencia de Información (Controles A.8.15, A.8.23, A.5.14)
- Guía de Implementación: Construyendo el Paquete de Evidencia de Auditoría
- Paso 1: Formalizar la Evaluación de Riesgos
- Paso 2: Exportar Configuraciones como Evidencia
- Paso 3: Establecer la Cadencia de Revisión de Proveedores
- Mejores prácticas para recintos empresariales
- Resolución de problemas y mitigación de riesgos
- ROI e impacto empresarial
- Informe de audio

Resumen Ejecutivo
Para recintos empresariales —ya sea un hotel de 500 habitaciones, una cadena minorista multisitio o un estadio de 50.000 asientos—, el Guest WiFi rara vez se trata con el mismo rigor de gobernanza que la LAN corporativa. Sin embargo, bajo la ISO 27001:2022, una red inalámbrica de cara al público es un activo de información vivo que se cruza con el límite de su red, las relaciones con los proveedores y las obligaciones legales. Esta guía traduce los requisitos teóricos de un Sistema de Gestión de Seguridad de la Información (SGSI) en resultados prácticos de ingeniería y cumplimiento para las implementaciones de Guest WiFi .
Al tratar la red de invitados no como un servicio básico, sino como un segmento auditado, los líderes de TI pueden mitigar los riesgos de movimiento lateral, garantizar el cumplimiento normativo y producir evidencia definitiva para los auditores principales. Esta guía detalla los controles específicos del Anexo A aplicables a las implementaciones inalámbricas, describe la metodología de evaluación de riesgos requerida y explica cómo construir un paquete de evidencia de auditoría defendible, ahorrando cientos de horas durante los ciclos de certificación.
Análisis Técnico Detallado: Mapeo de los Controles ISO 27001 a la Arquitectura WiFi
ISO 27001:2022 reestructuró sus controles del Anexo A en cuatro temas. Para las redes inalámbricas de invitados, los requisitos críticos residen principalmente en los dominios Tecnológico y Organizacional. Comprender cómo estos controles se traducen en configuraciones de red es la base del cumplimiento.
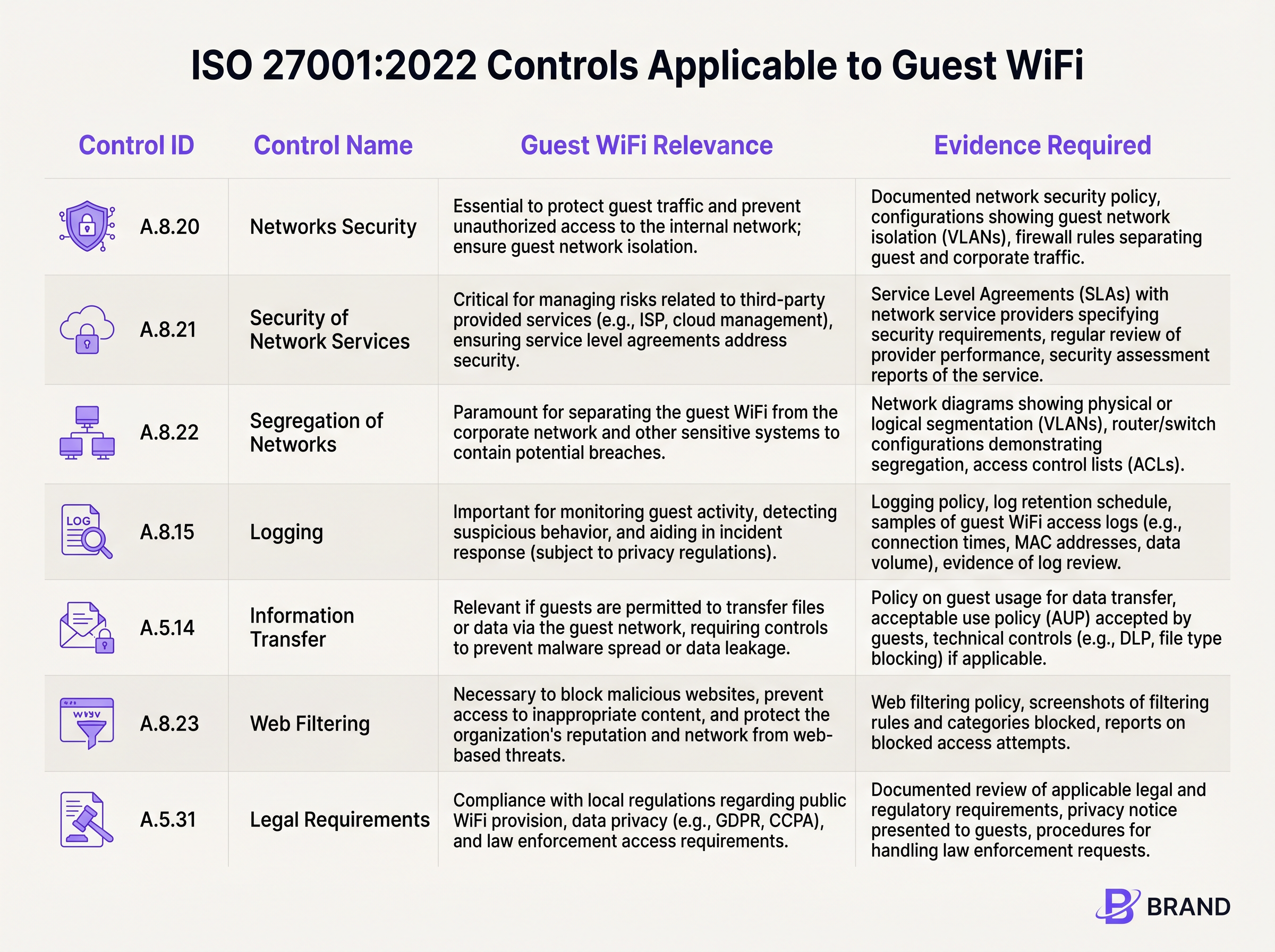
Segregación y Seguridad de la Red (Controles A.8.20 y A.8.22)
El requisito fundamental para cualquier red de invitados es un aislamiento estricto. El Control A.8.22 (Segregación de Redes) exige que los grupos de servicios de información estén segregados. En términos prácticos, esto requiere implementar VLANs dedicadas para el tráfico de invitados que estén lógica (y cuando sea necesario, físicamente) separadas de las subredes corporativas, los sistemas de punto de venta (POS) y los dispositivos IoT de gestión de edificios.
Junto con el Control A.8.20 (Seguridad de Redes), este aislamiento debe aplicarse mediante reglas de firewall robustas y Listas de Control de Acceso (ACLs). Un auditor esperará ver configuraciones que denieguen explícitamente el enrutamiento desde la VLAN de invitados a cualquier espacio IP interno RFC 1918. Si un probador de penetración en el SSID de invitados puede acceder a la interfaz de gestión de una pasarela de Sensores o a un recurso compartido de archivos corporativo, constituye una no conformidad importante.
Aseguramiento de Proveedores y Plataformas en la Nube (Control A.8.21)
El Guest WiFi moderno depende en gran medida de los proveedores de servicios gestionados y de los Captive Portal alojados en la nube. El Control A.8.21 (Seguridad de los Servicios de Red) establece que estas relaciones con los proveedores deben regirse por requisitos de seguridad. Aquí es donde las certificaciones de los proveedores se vuelven críticas. En lugar de realizar una auditoría a medida de una plataforma WiFi en la nube, las organizaciones deben confiar en el informe SOC 2 Tipo II del proveedor. Plataformas como Purple cumplen con SOC 2, proporcionando una garantía independiente sobre sus controles de seguridad, disponibilidad y privacidad. Esta documentación se incorpora directamente a su archivo de aseguramiento de proveedores del SGSI.
Registro, Filtrado y Transferencia de Información (Controles A.8.15, A.8.23, A.5.14)
La visibilidad y el control sobre el tráfico de invitados están exigidos por varios controles superpuestos. El Control A.8.15 (Registro) requiere la retención de eventos de conexión y registros de autenticación. Sin embargo, esto debe equilibrarse con los principios de minimización de datos. El Captive Portal sirve como mecanismo principal para el Control A.5.14 (Transferencia de Información), donde los invitados deben aceptar una Política de Uso Aceptable (AUP) antes de que se les conceda el acceso.
Además, el Control A.8.23 (Filtrado Web) requiere la implementación de filtrado basado en DNS o proxies en la nube para bloquear dominios maliciosos e infraestructura de comando y control, protegiendo tanto la reputación de la red como los dispositivos conectados a ella.
Guía de Implementación: Construyendo el Paquete de Evidencia de Auditoría
Implementar la tecnología es solo la mitad de la batalla; demostrarlo a un auditor es la otra. Los siguientes pasos describen cómo traducir las configuraciones técnicas en un paquete de evidencia ISO 27001 defendible.
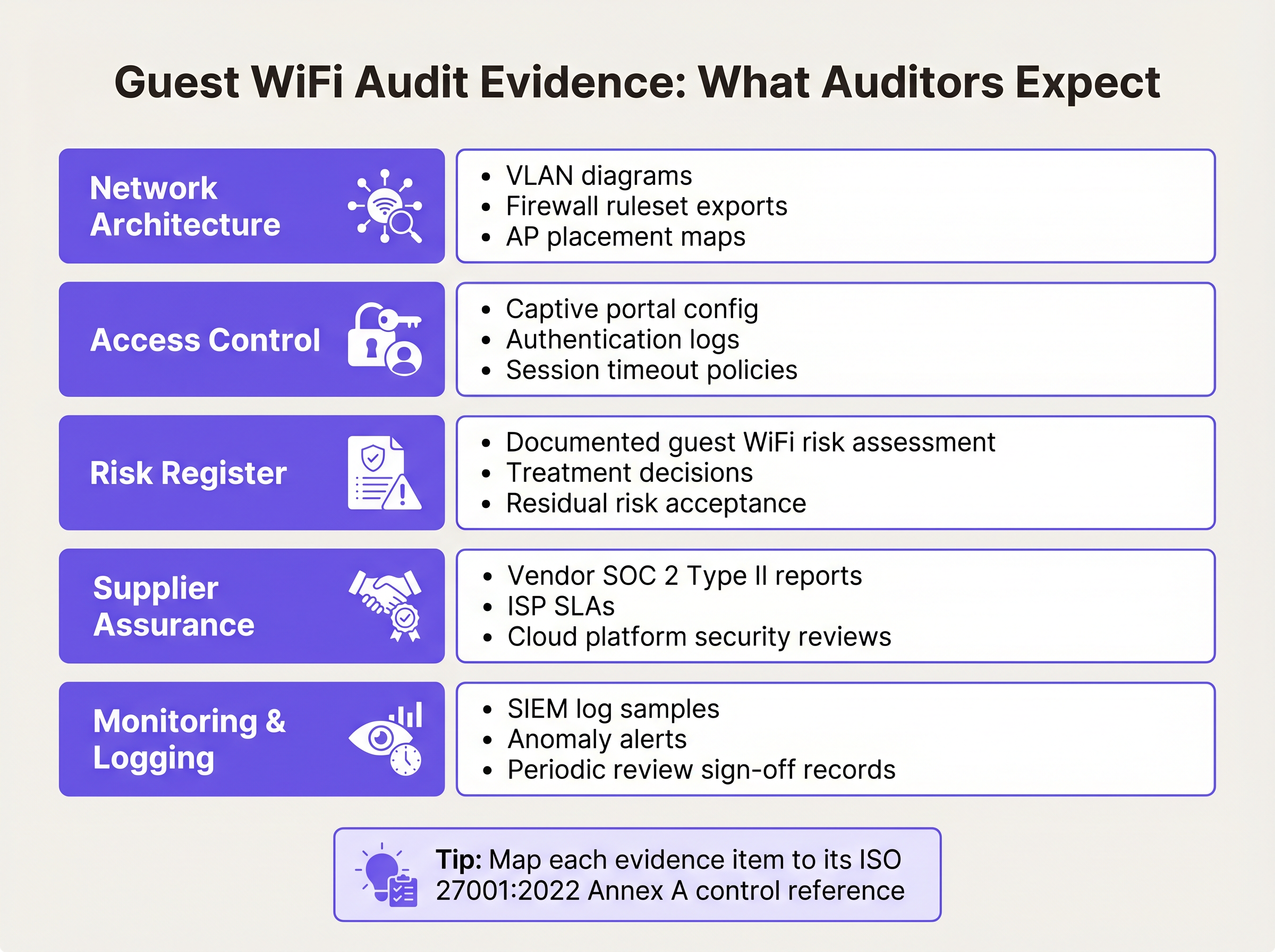
Paso 1: Formalizar la Evaluación de Riesgos
El SGSI debe incluir una evaluación formal de riesgos específicamente para el activo de Guest WiFi. Esto debe documentar amenazas como el movimiento lateral no autorizado, la propagación de malware y el agotamiento del ancho de banda. Para cada amenaza, documente la probabilidad, el impacto y el tratamiento de riesgo elegido (por ejemplo, mitigar mediante aislamiento de VLAN y aislamiento de cliente). La Declaración de Aplicabilidad (SoA) debe hacer referencia a esta evaluación como justificación para seleccionar controles como A.8.22 y A.8.23.
Paso 2: Exportar Configuraciones como Evidencia
Los auditores requieren evidencia puntual de las configuraciones. Genere un diagrama de red completo que etiquete claramente la VLAN de invitados y sus límites. Exporte el conjunto de reglas del firewall que demuestre las reglas de denegación explícita para el enrutamiento interno. Si utiliza una plataforma en la nube, exporte la configuración del Captive Portal mostrando el punto de control de aceptación obligatoria de la AUP. Para obtener orientación sobre cómo equilibrar la experiencia del usuario con estos puntos de control de seguridad, revise nuestra guía sobre Tiempos de espera de sesión de Guest WiFi: Equilibrando UX y Seguridad .
Paso 3: Establecer la Cadencia de Revisión de Proveedores
El aseguramiento de proveedores no es una actividad única. Establezca un calendario para revisiones anuales de su ISP y proveedores de portal en la nube. Solicite sus informes SOC 2 Tipo II actualizados y documente una revisión formal de estos informes por parte de la dirección. Si el proveedorLa auditoría destaca cualquier excepción; documente cómo esas excepciones impactan su propia postura de riesgo.
Mejores prácticas para recintos empresariales
La implementación de WiFi para invitados conforme en entornos complejos como Hostelería o centros de Transporte requiere la adhesión a las mejores prácticas neutrales del proveedor que satisfagan tanto las demandas de seguridad como las operativas.
- Aplicar el aislamiento de clientes: A nivel del punto de acceso, habilite el aislamiento de clientes (a veces llamado aislamiento de AP o modo invitado). Esto evita que los dispositivos conectados al mismo SSID se comuniquen directamente entre sí, mitigando los ataques peer-to-peer y la propagación de malware.
- Implementar una gestión de sesiones robusta: Configure tiempos de espera de sesión forzados que requieran reautenticación. Para un entorno minorista, un tiempo de espera de 12 horas puede ser apropiado; para un aeropuerto, un tiempo de espera de 4 horas asegura que las sesiones abandonadas se terminen. Esto limita la ventana de oportunidad para direcciones MAC secuestradas.
- Alinear con las regulaciones de privacidad de datos: Asegúrese de que la recopilación de datos de su captive portal se alinee con las leyes de privacidad locales (p. ej., GDPR). Solo recopile los datos necesarios para el servicio o para los cuales tenga un consentimiento explícito y documentado. Esto apoya directamente el Control A.5.31 (Requisitos Legales).
Resolución de problemas y mitigación de riesgos
Incluso con una arquitectura robusta, puede producirse una desviación del cumplimiento. El modo de fallo más común es la 'expansión del alcance' (scope creep), donde la red de invitados se excluye por completo del alcance del SGSI (lo que lleva a fallos en la auditoría) o se sobredimensiona (aplicando controles internos innecesarios a los dispositivos de los invitados).
Otro problema frecuente es la degradación de la segmentación de la red. Las actualizaciones de firmware o los cambios de red de emergencia pueden alterar inadvertidamente el enrutamiento de VLAN. Para mitigar esto, implemente la monitorización automatizada de la configuración o programe revisiones manuales trimestrales del conjunto de reglas del firewall que rige el segmento de invitados. Si gestiona múltiples sitios distribuidos, considere las ventajas de cumplimiento de las redes de área amplia modernas; nuestra visión general de Los beneficios clave de SD WAN para empresas modernas explora cómo la aplicación centralizada de políticas reduce la complejidad de la auditoría.
ROI e impacto empresarial
Invertir en el cumplimiento de ISO 27001 para el WiFi de invitados ofrece un valor empresarial medible más allá de simplemente pasar una auditoría. Una infraestructura inalámbrica segura y conforme protege la reputación de la marca del recinto al evitar que la red sea utilizada como base para la ciberdelincuencia.
Además, al aprovechar una plataforma alineada con SOC 2 que integra WiFi Analytics , los recintos pueden extraer de forma segura valor comercial de los datos de afluencia de público, manteniendo una estricta adhesión a los controles de privacidad y seguridad de los datos. La reducción en el tiempo de preparación de auditorías —a menudo ahorrando docenas de horas de ingeniería anualmente al confiar en la evidencia exportable de la plataforma— proporciona un ROI operativo directo.
Informe de audio
Para una explicación detallada de estos conceptos, escuche nuestro podcast de informe técnico de 10 minutos:
Definiciones clave
VLAN Segregation
The logical separation of a physical network into distinct broadcast domains, preventing traffic from one segment from reaching another without passing through a routed firewall.
Critical for satisfying ISO 27001 Control A.8.22, ensuring guest devices cannot access corporate or operational technology systems.
Client Isolation
A wireless network setting that prevents devices connected to the same Access Point or SSID from communicating directly with one another.
Used to mitigate peer-to-peer attacks and malware spread on public networks, supporting Control A.8.20.
SOC 2 Type II
An independent audit report that evaluates a service organisation's controls related to security, availability, and privacy over a specified period (usually 6-12 months).
The primary evidence used by IT teams to satisfy Control A.8.21 (Security of Network Services) for cloud-hosted WiFi platforms.
Statement of Applicability (SoA)
A mandatory ISO 27001 document that lists all Annex A controls, stating whether each is applied or excluded, along with the justification.
The SoA must explicitly reference the guest WiFi risk assessment to justify the inclusion of network segregation and filtering controls.
Captive Portal
A web page that a user of a public access network is obliged to view and interact with before access is granted.
Serves as the technical enforcement point for Acceptable Use Policies and privacy consent, generating the logs required for Control A.8.15.
Acceptable Use Policy (AUP)
A set of rules applied by the owner of a network that restrict the ways in which the network may be used.
Required evidence for Control A.5.14, demonstrating that guests have been informed of their obligations before transferring data.
WPA3-Personal (SAE)
The modern wireless security protocol that uses Simultaneous Authentication of Equals to provide forward secrecy, protecting session traffic even if the shared password is known.
The recommended security standard for shared-passphrase guest networks to ensure baseline encryption of the wireless medium.
Risk Treatment
The process of selecting and implementing measures to modify risk, typically categorised as mitigate, accept, transfer, or avoid.
IT managers must document how they treat the risks associated with guest WiFi (e.g., mitigating lateral movement via firewalls) within the ISMS.
Ejemplos prácticos
A 400-room hotel group needs to deploy guest WiFi across three properties. The IT Director wants to keep the guest network out of the ISO 27001 ISMS scope to save time. Is this permissible, and what are the architectural requirements if it is included?
Excluding the guest network from the ISMS scope is highly risky if the physical infrastructure (switches, APs, internet circuits) is shared with the corporate network, or if guest authentication captures personal data (bringing it under A.5.31 Legal Requirements). The correct approach is to include it in scope but apply proportionate controls. Architecturally, the hotel must implement strict VLAN segregation (Control A.8.22), apply client isolation at the AP level, and route guest traffic directly to the internet via a firewall that explicitly denies access to the hotel's property management system (PMS) and corporate subnets.
During an internal audit of a retail chain's WiFi, the auditor notes that the cloud-based captive portal provider has not been assessed for security in over two years. How should the network architect remediate this nonconformity against Control A.8.21?
The architect must immediately request the latest SOC 2 Type II report from the captive portal provider. Upon receipt, the architect should formally review the report, noting the auditor's opinion and any exceptions listed in the Trust Services Criteria. This review must be documented, signed off by management, and filed in the ISMS supplier assurance repository. A recurring calendar event should be established to request this report annually.
Preguntas de práctica
Q1. You are preparing for an ISO 27001 surveillance audit. The auditor asks for evidence that the guest WiFi network is secure from internal threats. What three specific artifacts should you provide?
Sugerencia: Think about architecture, policy enforcement, and supplier management.
Ver respuesta modelo
- A network diagram and firewall ruleset proving VLAN segregation (Control A.8.22). 2) Captive portal logs showing guests accepting the Acceptable Use Policy (Control A.5.14). 3) The latest SOC 2 Type II report from your cloud WiFi platform provider (Control A.8.21).
Q2. A stadium operations director wants to disable the captive portal to 'speed up entry' and just use an open network with no terms of service. As the Information Security Manager, how do you respond using ISO 27001 principles?
Sugerencia: Consider the legal and logging implications of an unmanaged open network.
Ver respuesta modelo
You must advise against this, as it violates Control A.5.14 (Information Transfer) by removing the Acceptable Use Policy checkpoint, and compromises Control A.8.15 (Logging) by removing the ability to tie sessions to an authentication event. Furthermore, it increases the venue's legal exposure under Control A.5.31 if the network is used for illicit purposes without a documented terms of service.
Q3. Your guest WiFi risk assessment identifies 'Access to malicious websites' as a high risk. You decide to implement DNS filtering. How do you document this in the ISMS?
Sugerencia: Link the threat to the specific Annex A control and the SoA.
Ver respuesta modelo
Update the Risk Register to show the threat is treated by implementing DNS filtering. In the Statement of Applicability (SoA), mark Control A.8.23 (Web Filtering) as 'Applicable', citing the risk assessment as the justification, and reference the DNS filtering configuration as the implementation evidence.
Continúe leyendo esta serie
Términos y condiciones de la WiFi para empleados: Aspectos legales y de cumplimiento esenciales
Esta guía aborda los aspectos legales y técnicos esenciales para redactar y aplicar los términos y condiciones de la WiFi para empleados en establecimientos corporativos. Detalla qué incluir en una Política de Uso Aceptable (AUP), cómo cumplir con los requisitos de GDPR y PCI DSS, y cómo implementar la autenticación basada en la identidad y la segmentación de red para proteger los activos corporativos. Los responsables de TI, equipos de RR. HH. y directores de operaciones de hoteles, cadenas de retail, estadios y organizaciones del sector público encontrarán pautas prácticas que podrán implementar este trimestre.
Políticas de WiFi para el personal en el sector minorista: protección de las redes back-of-house
Esta guía cubre los requisitos técnicos y de políticas críticos para proteger las redes WiFi back-of-house en el sector minorista, desde la segmentación de VLAN y el cumplimiento de PCI DSS 4.0 hasta la gestión del BYOD de los empleados en la tienda. Ofrece a los responsables de TI, arquitectos de red y directores de operaciones un plan práctico y neutral respecto al proveedor que pueden poner en marcha este trimestre.
El Futuro de la Seguridad Wi-Fi: NAC Impulsado por IA y Detección de Amenazas
Esta guía autorizada explora la evolución de la seguridad Wi-Fi empresarial, desde el WPA2 heredado hasta el Control de Acceso a la Red (NAC) impulsado por IA y la detección de amenazas. Diseñada para líderes de TI, proporciona estrategias de implementación prácticas para asegurar entornos de alta densidad como comercios minoristas, hostelería y estadios utilizando las redes basadas en identidad de Purple.