ISO 27001 Guest WiFi: Una Guida alla Conformità
Questo autorevole riferimento tecnico collega direttamente le implementazioni di guest WiFi ai controlli ISO 27001:2022, dettagliando i requisiti di segregazione della rete, logging e trattamento del rischio. Fornisce indicazioni operative per i responsabili IT e gli architetti di rete sulla generazione di prove pronte per l'audit e sull'utilizzo delle attestazioni SOC 2 dei fornitori per soddisfare i mandati di garanzia dei fornitori ISMS.
Ascolta questa guida
Visualizza trascrizione del podcast
- Riepilogo Esecutivo
- Approfondimento Tecnico: Mappatura dei Controlli ISO 27001 all'Architettura WiFi
- Segregazione e Sicurezza della Rete (Controlli A.8.20 e A.8.22)
- Garanzia del Fornitore e Piattaforme Cloud (Controllo A.8.21)
- Logging, Filtraggio e Trasferimento delle Informazioni (Controlli A.8.15, A.8.23, A.5.14)
- Guida all'Implementazione: Costruire il Pacchetto di Prove per l'Audit
- Fase 1: Formalizzare la Valutazione del Rischio
- Fase 2: Esportare le Configurazioni come Prova
- Fase 3: Stabilire la Cadenza di Revisione dei Fornitori
- Migliori Pratiche per Sedi Aziendali
- Risoluzione dei Problemi e Mitigazione del Rischio
- ROI e Impatto sul Business
- Briefing Audio

Riepilogo Esecutivo
Per le sedi aziendali — che si tratti di un hotel da 500 camere, di una catena di negozi multi-sede o di uno stadio da 50.000 posti — il guest WiFi è raramente trattato con lo stesso rigore di governance della LAN aziendale. Tuttavia, secondo la ISO 27001:2022, una rete wireless pubblica è un asset informativo vivo che interseca il confine della rete, le relazioni con i fornitori e gli obblighi legali. Questa guida traduce i requisiti teorici di un Sistema di Gestione della Sicurezza delle Informazioni (ISMS) in risultati pratici di ingegneria e conformità per le implementazioni di Guest WiFi .
Trattando la rete guest non come un servizio di commodity ma come un segmento sottoposto ad audit, i responsabili IT possono mitigare i rischi di movimento laterale, garantire la conformità normativa e produrre prove definitive per gli auditor principali. Questa guida illustra i controlli specifici dell'Allegato A applicabili alle implementazioni wireless, delinea la metodologia di valutazione del rischio richiesta e spiega come costruire un pacchetto di prove di audit difendibile, risparmiando centinaia di ore durante i cicli di certificazione.
Approfondimento Tecnico: Mappatura dei Controlli ISO 27001 all'Architettura WiFi
La ISO 27001:2022 ha ristrutturato i suoi controlli dell'Allegato A in quattro temi. Per le reti wireless guest, i requisiti critici risiedono principalmente nei domini Tecnologici e Organizzativi. Comprendere come questi controlli si traducano in configurazioni di rete è il fondamento della conformità.
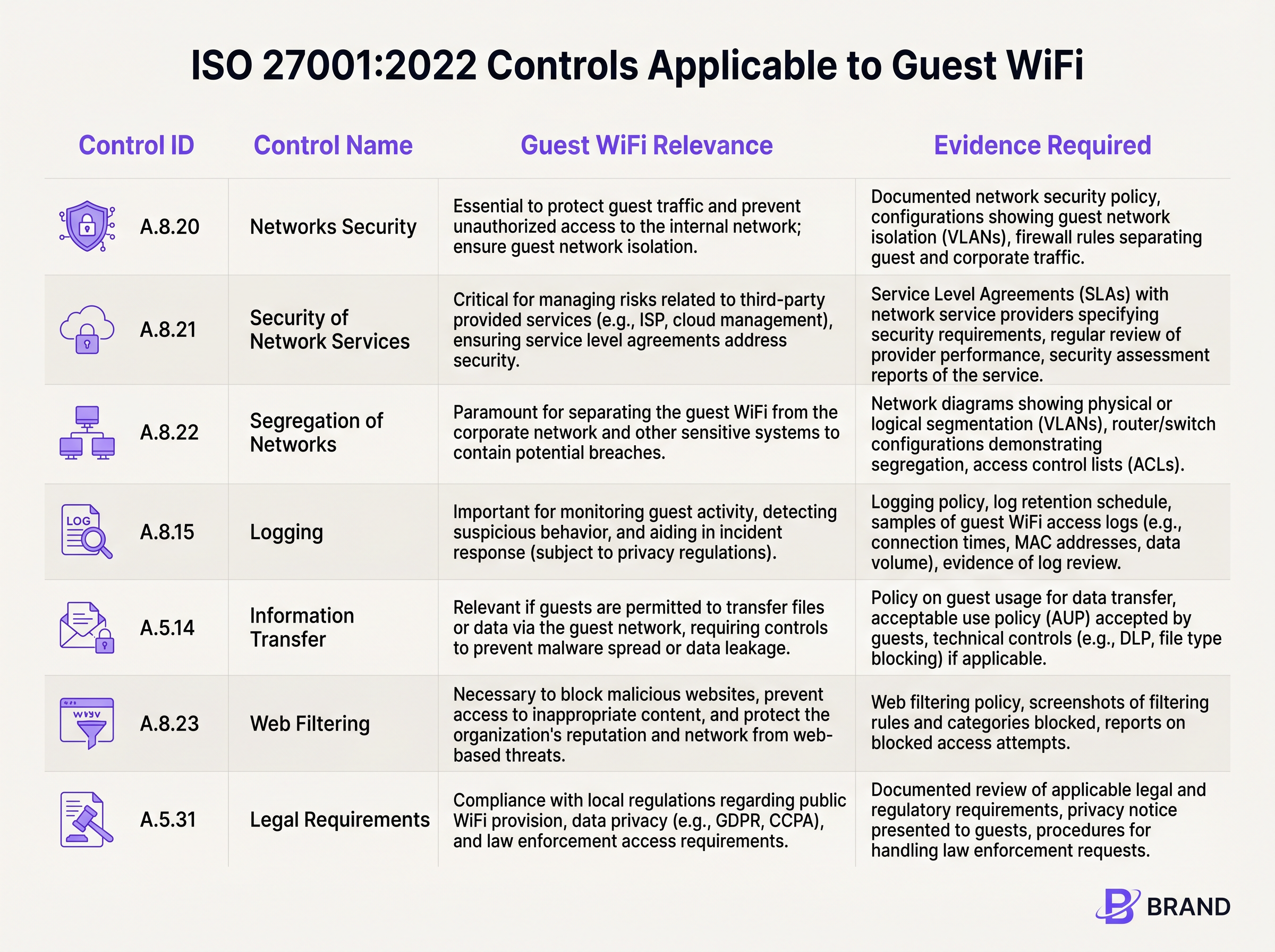
Segregazione e Sicurezza della Rete (Controlli A.8.20 e A.8.22)
Il requisito fondamentale per qualsiasi rete guest è l'isolamento rigoroso. Controllo A.8.22 (Segregazione delle Reti) impone che i gruppi di servizi informativi siano segregati. In termini pratici, ciò richiede l'implementazione di VLAN dedicate per il traffico guest che siano logicamente (e, ove necessario, fisicamente) separate dalle sottoreti aziendali, dai sistemi point-of-sale (POS) e dai dispositivi IoT di gestione degli edifici.
Insieme al Controllo A.8.20 (Sicurezza delle Reti), questo isolamento deve essere applicato tramite robusti set di regole firewall e Access Control Lists (ACL). Un auditor si aspetterà di vedere configurazioni che neghino esplicitamente il routing dalla VLAN guest a qualsiasi spazio IP interno RFC 1918. Se un penetration tester sulla guest SSID può raggiungere l'interfaccia di gestione di un gateway Sensors o una condivisione di file aziendale, ciò costituisce una non conformità maggiore.
Garanzia del Fornitore e Piattaforme Cloud (Controllo A.8.21)
Il moderno guest WiFi si basa fortemente su fornitori di servizi gestiti e captive portals ospitati nel cloud. Controllo A.8.21 (Sicurezza dei Servizi di Rete) stabilisce che queste relazioni con i fornitori devono essere governate da requisiti di sicurezza. È qui che le attestazioni dei fornitori diventano cruciali. Invece di condurre un audit su misura di una piattaforma WiFi cloud, le organizzazioni dovrebbero fare affidamento sul report SOC 2 Tipo II del fornitore. Piattaforme come Purple sono conformi a SOC 2, fornendo una garanzia indipendente sui loro controlli di sicurezza, disponibilità e privacy. Questa documentazione confluisce direttamente nel file di garanzia del fornitore del vostro ISMS.
Logging, Filtraggio e Trasferimento delle Informazioni (Controlli A.8.15, A.8.23, A.5.14)
La visibilità e il controllo sul traffico guest sono imposti da diversi controlli sovrapposti. Controllo A.8.15 (Logging) richiede la conservazione degli eventi di connessione e dei log di autenticazione. Tuttavia, ciò deve essere bilanciato con i principi di minimizzazione dei dati. Il captive portal funge da meccanismo primario per il Controllo A.5.14 (Trasferimento delle Informazioni), dove gli ospiti devono accettare una Politica di Utilizzo Accettabile (AUP) prima che l'accesso sia concesso.
Inoltre, il Controllo A.8.23 (Filtraggio Web) rende necessario l'implementazione di filtri basati su DNS o proxy cloud per bloccare domini dannosi e infrastrutture di comando e controllo, proteggendo sia la reputazione della rete che i dispositivi ad essa collegati.
Guida all'Implementazione: Costruire il Pacchetto di Prove per l'Audit
Implementare la tecnologia è solo metà della battaglia; dimostrarla a un auditor è l'altra metà. I seguenti passaggi descrivono come tradurre le configurazioni tecniche in un pacchetto di prove ISO 27001 difendibile.
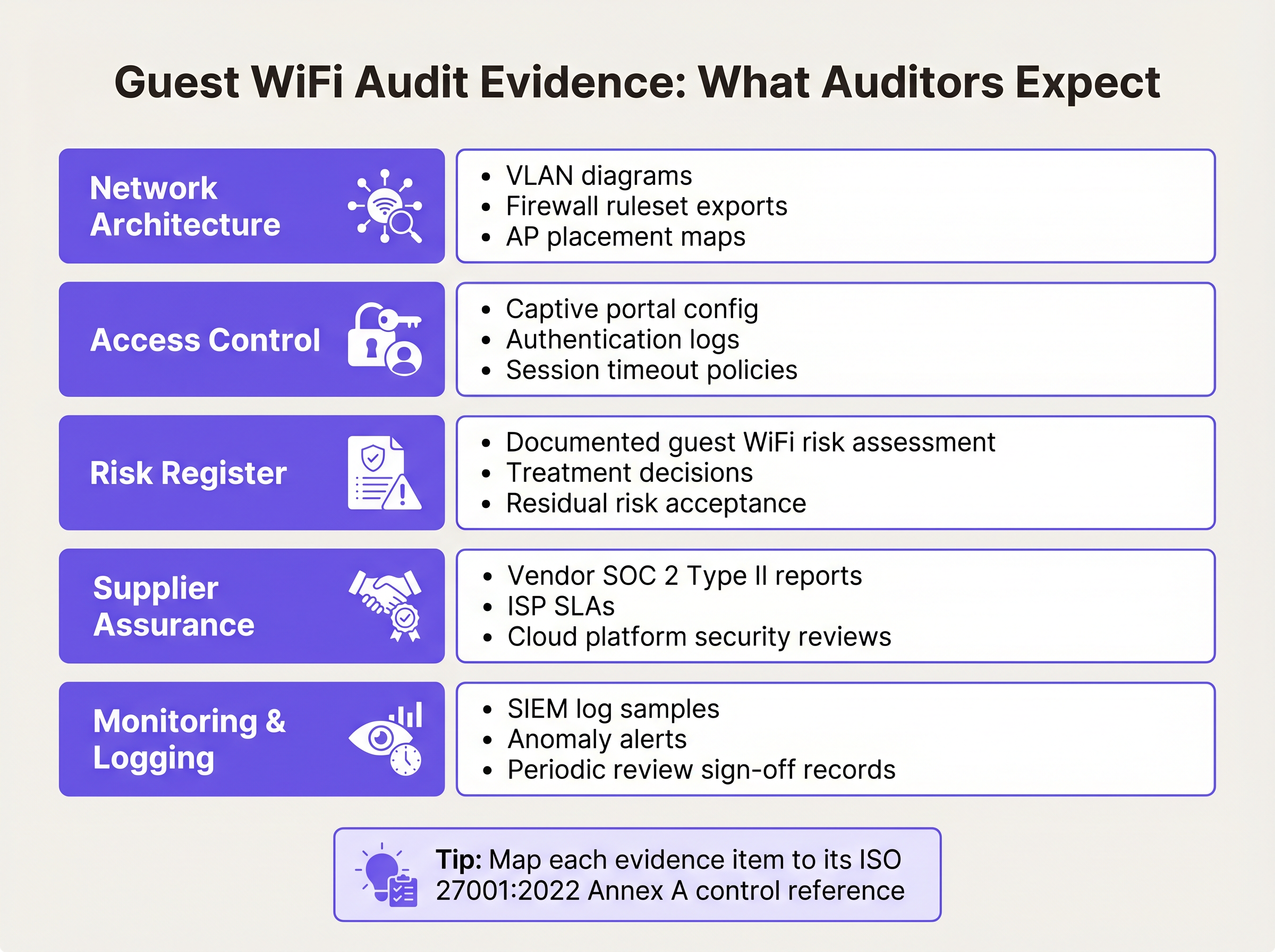
Fase 1: Formalizzare la Valutazione del Rischio
L'ISMS deve includere una valutazione formale del rischio specificamente per l'asset guest WiFi. Questa dovrebbe documentare minacce come il movimento laterale non autorizzato, la propagazione di malware e l'esaurimento della larghezza di banda. Per ogni minaccia, documentare la probabilità, l'impatto e il trattamento del rischio scelto (ad esempio, mitigare tramite isolamento VLAN e isolamento client). La Dichiarazione di Applicabilità (SoA) deve fare riferimento a questa valutazione come giustificazione per la selezione di controlli come A.8.22 e A.8.23.
Fase 2: Esportare le Configurazioni come Prova
Gli auditor richiedono prove puntuali delle configurazioni. Generare un diagramma di rete completo che etichetti chiaramente la VLAN guest e i suoi confini. Esportare il set di regole del firewall che dimostra le regole di negazione esplicita per il routing interno. Se si utilizza una piattaforma cloud, esportare la configurazione del captive portal che mostra il checkpoint obbligatorio di accettazione dell'AUP. Per indicazioni su come bilanciare l'esperienza utente con questi checkpoint di sicurezza, consultare la nostra guida su Guest WiFi Timeout delle sessioni: Bilanciare UX e Sicurezza .
Fase 3: Stabilire la Cadenza di Revisione dei Fornitori
La garanzia del fornitore non è un'attività una tantum. Stabilire un calendario per le revisioni annuali dei vostri ISP e fornitori di cloud portal. Richiedere i loro report SOC 2 Tipo II aggiornati e documentare una revisione formale da parte della direzione di questi report. Se il fornitoreL'audit evidenzia eventuali eccezioni; documenta come tali eccezioni influiscono sulla tua postura di rischio.
Migliori Pratiche per Sedi Aziendali
L'implementazione di un WiFi guest conforme in ambienti complessi come hub Ospitalità o Trasporto richiede l'adesione a migliori pratiche indipendenti dal fornitore che soddisfino sia le esigenze di sicurezza che quelle operative.
- Applica l'isolamento del client: A livello di punto di accesso, abilita l'isolamento del client (a volte chiamato isolamento AP o modalità guest). Ciò impedisce ai dispositivi connessi allo stesso SSID di comunicare direttamente tra loro, mitigando gli attacchi peer-to-peer e la propagazione di malware.
- Implementa una gestione robusta delle sessioni: Configura timeout di sessione forzati che richiedono la riautenticazione. Per un ambiente di vendita al dettaglio, un timeout di 12 ore potrebbe essere appropriato; per un aeroporto, un timeout di 4 ore garantisce che le sessioni abbandonate vengano terminate. Ciò limita la finestra di opportunità per gli indirizzi MAC dirottati.
- Allineati con le normative sulla privacy dei dati: Assicurati che la raccolta dati del tuo captive portal sia conforme alle leggi locali sulla privacy (es. GDPR). Raccogli solo i dati necessari per il servizio o per i quali hai un consenso esplicito e documentato. Questo supporta direttamente il Controllo A.5.31 (Requisiti Legali).
Risoluzione dei Problemi e Mitigazione del Rischio
Anche con un'architettura robusta, può verificarsi una deriva della conformità. La modalità di errore più comune è lo 'scope creep' (espansione incontrollata dell'ambito), in cui la rete guest è completamente esclusa dall'ambito ISMS (portando a fallimenti dell'audit) o sovra-dimensionata (applicando controlli interni non necessari ai dispositivi guest).
Un altro problema frequente è il degrado della segmentazione della rete. Gli aggiornamenti del firmware o le modifiche di rete di emergenza possono alterare inavvertitamente il routing VLAN. Per mitigare ciò, implementa il monitoraggio automatico della configurazione o pianifica revisioni manuali trimestrali del set di regole del firewall che governa il segmento guest. Se gestisci più siti distribuiti, considera i vantaggi di conformità del moderno networking wide-area; la nostra panoramica su I Vantaggi Chiave del SD WAN per le Aziende Moderne esplora come l'applicazione centralizzata delle policy riduca la complessità dell'audit.
ROI e Impatto sul Business
Investire nella conformità ISO 27001 per il WiFi guest offre un valore aziendale misurabile che va oltre il semplice superamento di un audit. Un'infrastruttura wireless sicura e conforme protegge la reputazione del marchio della sede impedendo che la rete venga utilizzata come terreno di preparazione per la criminalità informatica.
Inoltre, sfruttando una piattaforma allineata a SOC 2 che integra WiFi Analytics , le sedi possono estrarre in sicurezza valore commerciale dai dati di affluenza mantenendo una rigorosa aderenza ai controlli di privacy e sicurezza dei dati. La riduzione del tempo di preparazione dell'audit — spesso risparmiando decine di ore di ingegneria all'anno affidandosi a prove di piattaforma esportabili — fornisce un ROI operativo diretto.
Briefing Audio
Per una panoramica dettagliata di questi concetti, ascolta il nostro podcast di briefing tecnico di 10 minuti:
Definizioni chiave
VLAN Segregation
The logical separation of a physical network into distinct broadcast domains, preventing traffic from one segment from reaching another without passing through a routed firewall.
Critical for satisfying ISO 27001 Control A.8.22, ensuring guest devices cannot access corporate or operational technology systems.
Client Isolation
A wireless network setting that prevents devices connected to the same Access Point or SSID from communicating directly with one another.
Used to mitigate peer-to-peer attacks and malware spread on public networks, supporting Control A.8.20.
SOC 2 Type II
An independent audit report that evaluates a service organisation's controls related to security, availability, and privacy over a specified period (usually 6-12 months).
The primary evidence used by IT teams to satisfy Control A.8.21 (Security of Network Services) for cloud-hosted WiFi platforms.
Statement of Applicability (SoA)
A mandatory ISO 27001 document that lists all Annex A controls, stating whether each is applied or excluded, along with the justification.
The SoA must explicitly reference the guest WiFi risk assessment to justify the inclusion of network segregation and filtering controls.
Captive Portal
A web page that a user of a public access network is obliged to view and interact with before access is granted.
Serves as the technical enforcement point for Acceptable Use Policies and privacy consent, generating the logs required for Control A.8.15.
Acceptable Use Policy (AUP)
A set of rules applied by the owner of a network that restrict the ways in which the network may be used.
Required evidence for Control A.5.14, demonstrating that guests have been informed of their obligations before transferring data.
WPA3-Personal (SAE)
The modern wireless security protocol that uses Simultaneous Authentication of Equals to provide forward secrecy, protecting session traffic even if the shared password is known.
The recommended security standard for shared-passphrase guest networks to ensure baseline encryption of the wireless medium.
Risk Treatment
The process of selecting and implementing measures to modify risk, typically categorised as mitigate, accept, transfer, or avoid.
IT managers must document how they treat the risks associated with guest WiFi (e.g., mitigating lateral movement via firewalls) within the ISMS.
Esempi pratici
A 400-room hotel group needs to deploy guest WiFi across three properties. The IT Director wants to keep the guest network out of the ISO 27001 ISMS scope to save time. Is this permissible, and what are the architectural requirements if it is included?
Excluding the guest network from the ISMS scope is highly risky if the physical infrastructure (switches, APs, internet circuits) is shared with the corporate network, or if guest authentication captures personal data (bringing it under A.5.31 Legal Requirements). The correct approach is to include it in scope but apply proportionate controls. Architecturally, the hotel must implement strict VLAN segregation (Control A.8.22), apply client isolation at the AP level, and route guest traffic directly to the internet via a firewall that explicitly denies access to the hotel's property management system (PMS) and corporate subnets.
During an internal audit of a retail chain's WiFi, the auditor notes that the cloud-based captive portal provider has not been assessed for security in over two years. How should the network architect remediate this nonconformity against Control A.8.21?
The architect must immediately request the latest SOC 2 Type II report from the captive portal provider. Upon receipt, the architect should formally review the report, noting the auditor's opinion and any exceptions listed in the Trust Services Criteria. This review must be documented, signed off by management, and filed in the ISMS supplier assurance repository. A recurring calendar event should be established to request this report annually.
Domande di esercitazione
Q1. You are preparing for an ISO 27001 surveillance audit. The auditor asks for evidence that the guest WiFi network is secure from internal threats. What three specific artifacts should you provide?
Suggerimento: Think about architecture, policy enforcement, and supplier management.
Visualizza risposta modello
- A network diagram and firewall ruleset proving VLAN segregation (Control A.8.22). 2) Captive portal logs showing guests accepting the Acceptable Use Policy (Control A.5.14). 3) The latest SOC 2 Type II report from your cloud WiFi platform provider (Control A.8.21).
Q2. A stadium operations director wants to disable the captive portal to 'speed up entry' and just use an open network with no terms of service. As the Information Security Manager, how do you respond using ISO 27001 principles?
Suggerimento: Consider the legal and logging implications of an unmanaged open network.
Visualizza risposta modello
You must advise against this, as it violates Control A.5.14 (Information Transfer) by removing the Acceptable Use Policy checkpoint, and compromises Control A.8.15 (Logging) by removing the ability to tie sessions to an authentication event. Furthermore, it increases the venue's legal exposure under Control A.5.31 if the network is used for illicit purposes without a documented terms of service.
Q3. Your guest WiFi risk assessment identifies 'Access to malicious websites' as a high risk. You decide to implement DNS filtering. How do you document this in the ISMS?
Suggerimento: Link the threat to the specific Annex A control and the SoA.
Visualizza risposta modello
Update the Risk Register to show the threat is treated by implementing DNS filtering. In the Statement of Applicability (SoA), mark Control A.8.23 (Web Filtering) as 'Applicable', citing the risk assessment as the justification, and reference the DNS filtering configuration as the implementation evidence.
Continua a leggere questa serie
Il Futuro della Sicurezza Wi-Fi: NAC basato su AI e Rilevamento delle Minacce
Questa guida autorevole esplora l'evoluzione della sicurezza Wi-Fi aziendale, dal WPA2 tradizionale al Network Access Control (NAC) basato su AI e al rilevamento delle minacce. Progettata per i leader IT, fornisce strategie di implementazione attuabili per la messa in sicurezza di ambienti ad alta densità come negozi al dettaglio, strutture ricettive e stadi, utilizzando le reti basate sull'identità di Purple.
Gestire la sicurezza dei dispositivi IoT con NAC e MPSK
Questa guida tecnica illustra come le aziende possano proteggere i dispositivi IoT headless utilizzando l'architettura Multiple Pre-Shared Key (MPSK) e il Network Access Control (NAC). Fornisce passaggi di implementazione pratici per ottenere la micro-segmentazione, contenere i raggi di esplosione della sicurezza e mantenere la conformità senza sacrificare la scalabilità.
RadSec: Come RADIUS su TLS migliora la sicurezza dell'autenticazione WiFi
Questo riferimento tecnico autorevole spiega come RadSec (RFC 6614) protegge l'autenticazione WiFi aziendale incapsulando il traffico RADIUS tradizionale nella crittografia TLS. Progettato per manager IT e architetti di rete, copre architettura, strategie di implementazione e passaggi pratici per mitigare i rischi del traffico RADIUS UDP non crittografato attraverso reti aziendali e guest.