CCPA vs GDPR: Global Privacy Compliance for Guest WiFi Data
This guide provides a comprehensive technical comparison of CCPA and GDPR requirements for guest WiFi deployments. It delivers actionable strategies for IT leaders and network architects to build a unified, dual-compliant consent framework that mitigates regulatory risk while preserving the commercial value of first-party data.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive: Architectural Tensions
- GDPR: The Opt-In Imperative
- CCPA/CPRA: The Opt-Out Mandate
- Regulated Data Categories in WiFi Deployments
- Implementation Guide: Building the Dual-Compliant Portal
- Step 1: Geo-Detection and Routing
- Step 2: The High-Water-Mark UI Design
- Step 3: Immutable Audit Logging
- Step 4: Unified Data Subject Request (DSR) Workflows
- Best Practices & Real-World Case Studies
- Case Study 1: Global Hospitality Brand
- Case Study 2: High-Density Stadium Deployment
- Troubleshooting & Risk Mitigation
- ROI & Business Impact
- References

Executive Summary
For enterprise IT leaders and venue operators, guest WiFi is no longer merely a connectivity amenity; it is a critical first-party data acquisition channel. However, capturing this data—ranging from MAC addresses and email identifiers to session dwell times—exposes organisations to significant regulatory liability under both the European Union's General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA), as amended by the California Privacy Rights Act (CPRA).
This guide cuts through the legal ambiguity to provide a technical, vendor-neutral roadmap for dual compliance. We explore the fundamental architectural tension between GDPR's opt-in mandate and CCPA's opt-out framework. More importantly, we outline how network architects and privacy officers can deploy a single, unified consent portal that satisfies both regimes without degrading the user experience or bifurcating the underlying data pipelines. By standardising on a high-water-mark compliance posture, global brands in Retail , Hospitality , and Transport can confidently scale their Guest WiFi deployments and WiFi Analytics initiatives.
Technical Deep-Dive: Architectural Tensions
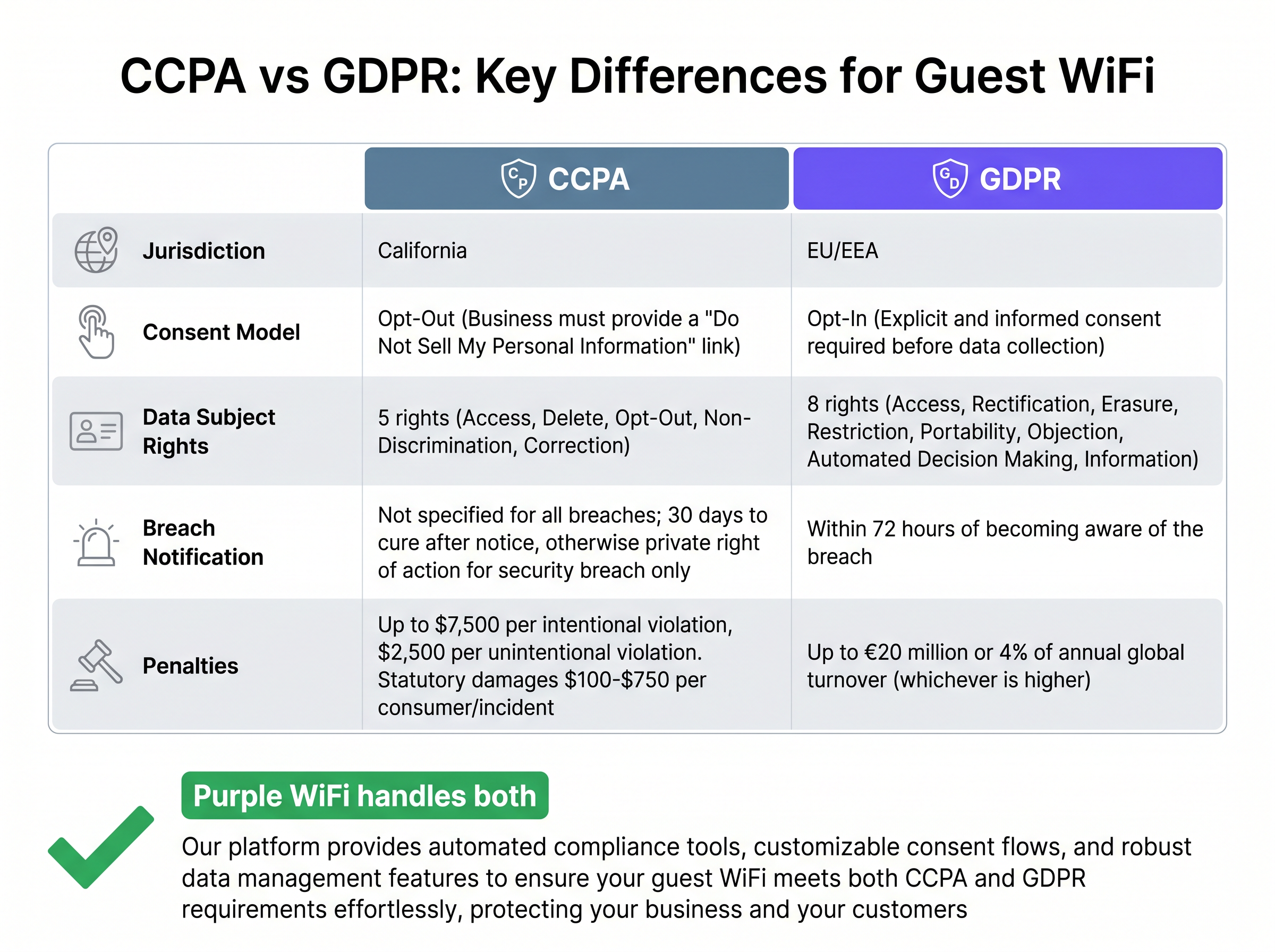
The core challenge in designing a globally compliant guest WiFi architecture lies in the conflicting consent models of the two primary regulatory frameworks.
GDPR: The Opt-In Imperative
Under GDPR, personal data collection requires a lawful basis. For marketing and analytics purposes, this basis is almost exclusively explicit, freely given, informed consent [1]. The technical implementation of this mandate is uncompromising:
- Active Affirmation: Users must actively tick an unchecked box to grant consent. Pre-ticked boxes are strictly prohibited.
- Granularity: Consent cannot be bundled. A user must be able to accept network terms and conditions without being forced to accept marketing communications.
- Auditability: The system must log an immutable record of the consent event, including the timestamp, user identifier, exact wording presented, and the specific version of the privacy notice in effect.
CCPA/CPRA: The Opt-Out Mandate
Conversely, CCPA operates on an opt-out model. Venues may collect data by default upon connection. However, if the venue "sells" or "shares" this data—which the statute defines broadly enough to include transferring data to advertising technology partners or cross-context behavioural advertising platforms—it must provide a clear mechanism to opt out [2].
- The "Do Not Sell" Link: The portal must prominently feature a "Do Not Sell or Share My Personal Information" link or toggle.
- Perpetual Honouring: Once a consumer opts out, the system must persistently honour that preference across all downstream systems.
Regulated Data Categories in WiFi Deployments
Both frameworks cast a wide net over what constitutes regulated data. In a typical enterprise deployment, the following data points fall under regulatory scrutiny:
- Identifiers: MAC addresses, IP addresses, email addresses, phone numbers, and social media handles used for authentication.
- Session Metrics: Connection timestamps, AP association logs, and bandwidth consumption.
- Location Data: RSSI-based trilateration data used for Wayfinding or heatmapping, particularly when correlated with a specific device identifier.
Because the overlap in regulated data is near-total, a bifurcated data architecture is rarely necessary. Instead, the focus must be on the intake mechanism—the captive portal.
Implementation Guide: Building the Dual-Compliant Portal
Deploying a dual-compliant architecture requires a systematic approach to user routing, UI design, and backend data management. The following steps outline a robust implementation strategy.
Step 1: Geo-Detection and Routing
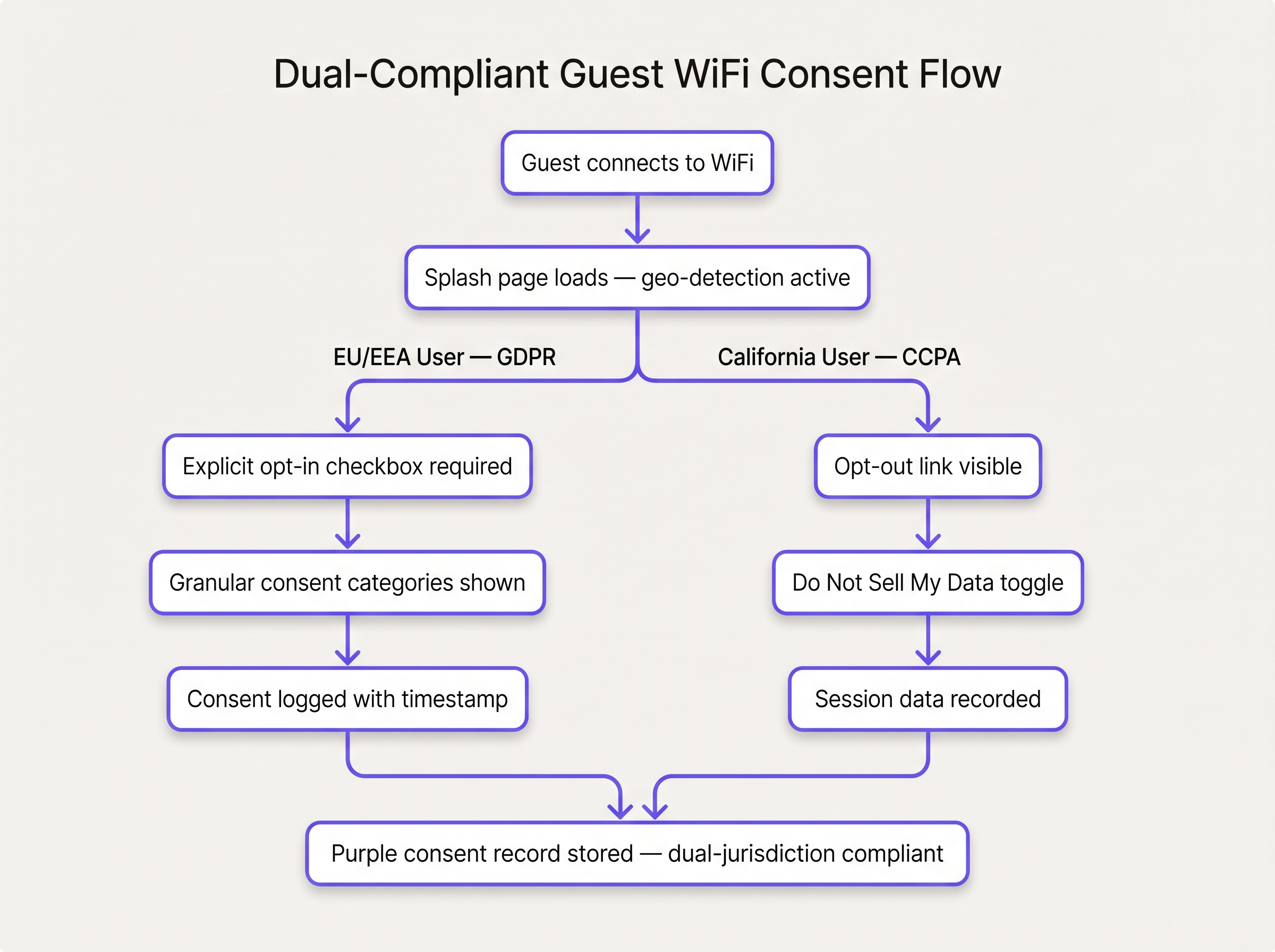
The first line of defence is identifying the user's regulatory jurisdiction. Your captive portal infrastructure must incorporate geo-IP lookup capabilities to detect whether the connecting device originates from an EU/EEA IP space or a Californian IP space.
While VPN usage can obfuscate true location, geo-IP routing satisfies the "reasonable technical measures" standard expected by regulators. Based on this detection, the portal dynamically serves the appropriate UI payload.
Step 2: The High-Water-Mark UI Design
The most defensible architectural choice is to design the global baseline to the GDPR standard, while layering CCPA requirements for applicable users.
- Global Baseline (GDPR Standard): Present an explicit, unchecked opt-in box for marketing and analytics data collection to all users. This ensures GDPR compliance for European users and establishes a highly defensible, privacy-first posture globally.
- CCPA Layering: For users detected in California, the UI must also prominently display the "Do Not Sell or Share My Personal Information" link, even if they have not opted in to marketing. This covers the scenario where operational data (e.g., session logs) might be shared with third parties in a manner that constitutes a "sale" under CCPA.
Step 3: Immutable Audit Logging
Consent is meaningless without proof. The authentication backend (typically a RADIUS server integrated with a consent management database) must write an immutable log for every session initiation. This log must capture:
- Device MAC address (hashed or encrypted at rest)
- Timestamp (UTC)
- Consent status (Opt-in: True/False)
- The specific privacy policy version ID presented
- Jurisdiction flag (e.g., EU, CA, ROW)
Step 4: Unified Data Subject Request (DSR) Workflows
Both regimes grant individuals the right to access, delete, and control their data. GDPR provides 30 days to respond; CCPA provides 45 days. IT teams must build a unified DSR pipeline.
When a request is received (via a web form or dedicated email), the system must query all data stores—the WiFi analytics database, CRM, marketing automation platforms, and any integrated Sensors databases—using the user's primary identifier (usually email or MAC address). The deletion or extraction script must execute across all systems simultaneously to ensure compliance within the stricter 30-day window.
Best Practices & Real-World Case Studies
Case Study 1: Global Hospitality Brand
Scenario: A 500-property hotel chain operating across the EU and the US needed to standardise its guest WiFi login. Historically, US properties collected email addresses silently via MAC caching, while EU properties used a clunky, multi-page GDPR form.
Implementation: The network architecture team deployed Purple's unified consent framework. They implemented a single-page splash portal globally. To access the network, guests provided an email address and accepted the terms of service. A separate, unchecked box was provided for marketing consent. For Californian IP addresses, a persistent "Privacy Choices" footer was injected into the portal.
Outcome: Marketing opt-in rates stabilised at 42% globally—lower than the previous US baseline, but representing a highly engaged, legally compliant database. More importantly, the IT team decommissioned three legacy portal servers, reducing maintenance overhead and standardising their DSR response time to under 72 hours.
Case Study 2: High-Density Stadium Deployment
Scenario: A major sports franchise in California required high-throughput onboarding for 60,000 fans simultaneously, while ensuring CCPA compliance and capturing data for retail sponsor attribution.
Implementation: To minimise onboarding friction (a critical factor in High-Density WiFi Design: Stadium and Arena Best Practices ), the IT team utilised profile-based authentication (similar to OpenRoaming). First-time visitors completed a rapid onboarding flow with a clear CCPA opt-out link. Returning devices were authenticated silently via MAC caching, but the backend system periodically triggered a re-authentication flow every 90 days to refresh consent and ensure the privacy notice remained current.
Outcome: The venue achieved a 68% attachment rate to the network while maintaining a fully auditable consent trail for their retail media monetisation strategy.
Troubleshooting & Risk Mitigation
Deploying a compliant architecture is not a set-and-forget exercise. IT teams must actively monitor for these common failure modes:
- The MAC Randomisation Problem: Modern mobile operating systems (iOS 14+, Android 10+) use randomised MAC addresses by default. This breaks legacy consent tracking that relies solely on the hardware MAC. Mitigation: Tie consent to a persistent user identifier (e.g., email or phone number) rather than the device MAC. Consider SMS vs Email Verification for Guest WiFi: Which to Choose to establish a verified identity.
- Stale Consent: Consent degrades over time. Relying on an opt-in from three years ago is risky, especially if your data processing purposes have evolved. Mitigation: Implement a forced re-authentication policy (e.g., every 12 months) requiring users to re-accept the current privacy terms.
- Third-Party Data Leakage: Pushing raw session logs to a third-party analytics vendor without a Data Processing Agreement (DPA) violates both GDPR and CCPA. Mitigation: Audit all API webhooks and data exports. Ensure all third-party vendors are contractually bound as processors or service providers.
ROI & Business Impact
Investing in a robust, dual-compliant guest WiFi architecture yields measurable returns beyond mere risk avoidance:
- Operational Efficiency: Maintaining a single, unified consent management platform reduces the engineering overhead associated with managing regional portal variants.
- Data Quality: An explicit opt-in database, while potentially smaller than an opt-out database, exhibits significantly higher engagement rates and lower bounce rates in downstream marketing campaigns.
- Strategic Agility: A high-water-mark compliance posture future-proofs the organisation against emerging state-level privacy laws in the US (e.g., VCDPA, CPA) and evolving international standards.
By treating privacy compliance as a core architectural requirement rather than a legal afterthought, IT leaders can transform guest WiFi from a regulatory liability into a secure, high-value asset.
Listen to the companion briefing:
References
[1] General Data Protection Regulation (GDPR), Article 4(11) and Article 7. https://gdpr-info.eu/ [2] California Consumer Privacy Act (CCPA), Civil Code Section 1798.120. https://oag.ca.gov/privacy/ccpa
Key Terms & Definitions
Lawful Basis
The legal justification required under GDPR to process personal data. For guest WiFi marketing, this is almost always 'Consent'.
Without a documented lawful basis, any data captured by the access point is toxic and must be purged.
Opt-In Framework
A regulatory model (like GDPR) where data collection is prohibited by default until the user explicitly grants permission.
Requires unchecked boxes on splash pages; pre-ticked boxes result in compliance failures.
Opt-Out Framework
A regulatory model (like CCPA) where data collection is permitted by default, but the user must be given a clear mechanism to stop the sharing or sale of that data.
Drives the requirement for 'Do Not Sell' links on California-facing portals.
MAC Randomisation
A privacy feature in modern mobile OSs that generates a temporary MAC address for each network, preventing long-term device tracking.
Forces IT teams to rely on authenticated user identities (email/SMS) rather than hardware addresses for analytics.
Data Subject Request (DSR)
A formal request from an individual to access, correct, or delete the data an organisation holds about them.
Requires IT to have unified querying capabilities across all databases to respond within statutory deadlines (30-45 days).
Immutable Audit Log
A database record of a consent event that cannot be altered or deleted, serving as cryptographic proof of compliance.
Essential for surviving regulatory audits; must include timestamp, identifier, and exact policy version.
Cross-Context Behavioural Advertising
Targeting advertising to a consumer based on their personal information obtained across different businesses or services.
Under CCPA, sharing WiFi data for this purpose constitutes a 'sale' and requires an opt-out mechanism.
Pseudonymisation
Replacing direct identifiers (like a name) with artificial identifiers (like a token), while retaining the ability to re-identify the data with a separate key.
Unlike true anonymisation, pseudonymised data is still regulated under GDPR and requires full compliance controls.
Case Studies
A global retail chain is deploying guest WiFi across 200 stores in the UK, Germany, and California. The marketing director wants to use MAC address tracking to measure store-to-store conversion rates. How should the network architect design the consent flow?
The architect must deploy a geo-aware captive portal. Upon connection, the portal identifies the user's region. For all regions, the portal presents the Terms of Service. Below this, an explicit, unchecked opt-in box is provided: 'I consent to the use of my device data to analyse visit patterns.' If the user does not check the box, MAC tracking must be disabled or heavily anonymised (hashed with a rotating salt) to prevent re-identification. For California users, a persistent 'Do Not Sell My Personal Information' link is added to the portal footer. The backend RADIUS server logs the MAC address against the consent timestamp and status.
A hotel guest submits a Data Subject Request (DSR) via email, stating: 'Delete all data you hold on me.' The guest frequently visits properties in both London and Los Angeles. What is the required technical response?
The IT team must treat this as a high-priority erasure request. The system must query the central consent database using the guest's email address. The query must identify all associated MAC addresses and session logs. An automated script must then execute a deletion command across the core WiFi database, the CRM, and any third-party marketing platforms integrated via API. The entire process must be completed, and confirmation sent to the user, within 30 days to satisfy the stricter GDPR timeline.
Scenario Analysis
Q1. Your marketing team wants to implement a 'seamless onboarding' experience where users agree to terms and marketing communications with a single click of a 'Connect' button. They argue this will increase the database size by 40%. As the network architect, how do you evaluate this request?
💡 Hint:Consider the GDPR requirement for granular and explicit consent.
Show Recommended Approach
The request must be rejected. Under GDPR, consent cannot be bundled. The 'Connect' button serves as agreement to the network Terms of Service (a contractual necessity for access). Marketing consent requires a separate, un-ticked checkbox. Implementing a single-click bundled consent would render the entire captured database legally invalid and expose the organisation to significant fines.
Q2. A venue in Los Angeles uses a third-party analytics vendor to generate footfall heatmaps. The vendor receives raw MAC addresses and RSSI data directly from the access points. The venue does not pay the vendor; instead, the vendor uses the data to improve its own algorithms. Does this require a CCPA 'Do Not Sell' link?
💡 Hint:Review the CCPA definition of 'Sale'.
Show Recommended Approach
Yes. Under CCPA, a 'sale' is not limited to monetary exchange; it includes sharing personal data for 'other valuable consideration'. Because the vendor uses the data for its own algorithmic improvement (valuable consideration), this constitutes a sale. The venue must provide a 'Do Not Sell' link on the splash page and ensure the vendor can process opt-out signals.
Q3. During an audit, you discover that your radius server logs consent (True/False) but does not record the specific version of the privacy policy that was active at the time of connection. Why is this a critical vulnerability?
💡 Hint:Think about the burden of proof required during a regulatory investigation.
Show Recommended Approach
Under GDPR, the data controller bears the burden of proof to demonstrate that consent was informed. If you cannot prove exactly what text the user agreed to (because the policy version was not logged), you cannot prove the consent was informed. This invalidates the consent log, meaning all data collected under that flawed process must be treated as non-compliant.
Key Takeaways
- ✓GDPR requires explicit, un-ticked opt-in for data collection; CCPA allows collection but mandates an opt-out mechanism for data sharing/selling.
- ✓Guest WiFi data, including MAC addresses, IP addresses, and session logs, is heavily regulated under both frameworks.
- ✓The most efficient global architecture applies the stricter GDPR opt-in standard universally, while layering CCPA opt-out links for Californian users.
- ✓Consent must be recorded in an immutable audit log containing the timestamp, user ID, and exact privacy policy version.
- ✓IT teams must build unified Data Subject Request (DSR) workflows capable of querying and deleting data across all integrated systems within 30 days.
- ✓Consent is not perpetual; venues should implement forced re-authentication cycles to refresh consent and maintain compliance.
- ✓Modern MAC randomisation requires venues to tie consent to verified identities (like email or SMS) rather than hardware addresses.



