How to Create a Guest WiFi Login Page
This authoritative guide details the technical architecture, UX best practices, and CRM integration strategies for deploying a branded guest WiFi login page (captive portal) in enterprise venues. Designed for IT managers, network architects, and venue operations directors, it provides actionable frameworks for balancing data capture requirements with user friction, ensuring GDPR compliance, and maximising ROI from guest WiFi infrastructure.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- Captive Portal Architecture and Routing
- Authentication Methodologies and Data Capture
- Network Segmentation and Security Architecture
- Implementation Guide
- Step 1: Infrastructure Preparation
- Step 2: Portal Design and Responsive UX
- Step 3: Data Capture Field Strategy
- Step 4: CRM and Analytics Integration
- Best Practices
- Troubleshooting & Risk Mitigation
- Captive Portal Fails to Invoke
- MAC Address Randomisation
- Dirty Data and Invalid Submissions
- SSL Certificate Warnings
- ROI & Business Impact

Executive Summary
For enterprise venues — from international hotel chains to expansive retail environments — the guest WiFi login page is no longer merely a network access gateway; it is a critical first-party data acquisition asset. As third-party cookies deprecate and privacy regulations tighten, the captive portal represents one of the most reliable mechanisms for building a robust, compliant customer database.
This guide provides a comprehensive technical reference for designing, deploying, and optimising a guest wifi login page . We explore the architectural considerations of captive portal routing, evaluate authentication methodologies against industry standards including IEEE 802.1X and WPA3, and detail the integration patterns required to flow authenticated user data securely into central CRM and marketing platforms. Organisations that implement the frameworks detailed below consistently transform their Guest WiFi infrastructure from a pure cost centre into a measurable driver of customer lifetime value — with database growth rates of 300–500% and demonstrably higher average transaction values in retail and hospitality environments.
Technical Deep-Dive
Captive Portal Architecture and Routing
The fundamental mechanism of a guest WiFi login page relies on captive portal technology. When a client device associates with the wireless local area network (WLAN), the network access controller (NAC) or the wireless access point (AP) intercepts the initial HTTP/HTTPS requests. Instead of routing this traffic to the intended destination, the infrastructure redirects the client to a walled garden environment — specifically, the captive portal splash page.
This redirection is typically achieved through DNS hijacking or HTTP redirection at the gateway level. The controller responds to DNS queries with its own IP address, serving the portal page regardless of the original destination. For HTTPS destinations, the controller issues a TCP redirect to port 80 before the TLS handshake completes, which is why the initial portal trigger relies on HTTP traffic.
It is critical to ensure that the walled garden configuration permits access to essential resources before authentication. If utilising social login mechanisms, the walled garden must whitelist the IP ranges or domains associated with Facebook, Google, or other OAuth identity provider APIs. Failure to do so is the single most common cause of portal load failures in new deployments.
Authentication Methodologies and Data Capture
The design of the authentication flow directly dictates the volume and quality of data captured. The architectural decision must align with the venue's broader digital strategy.
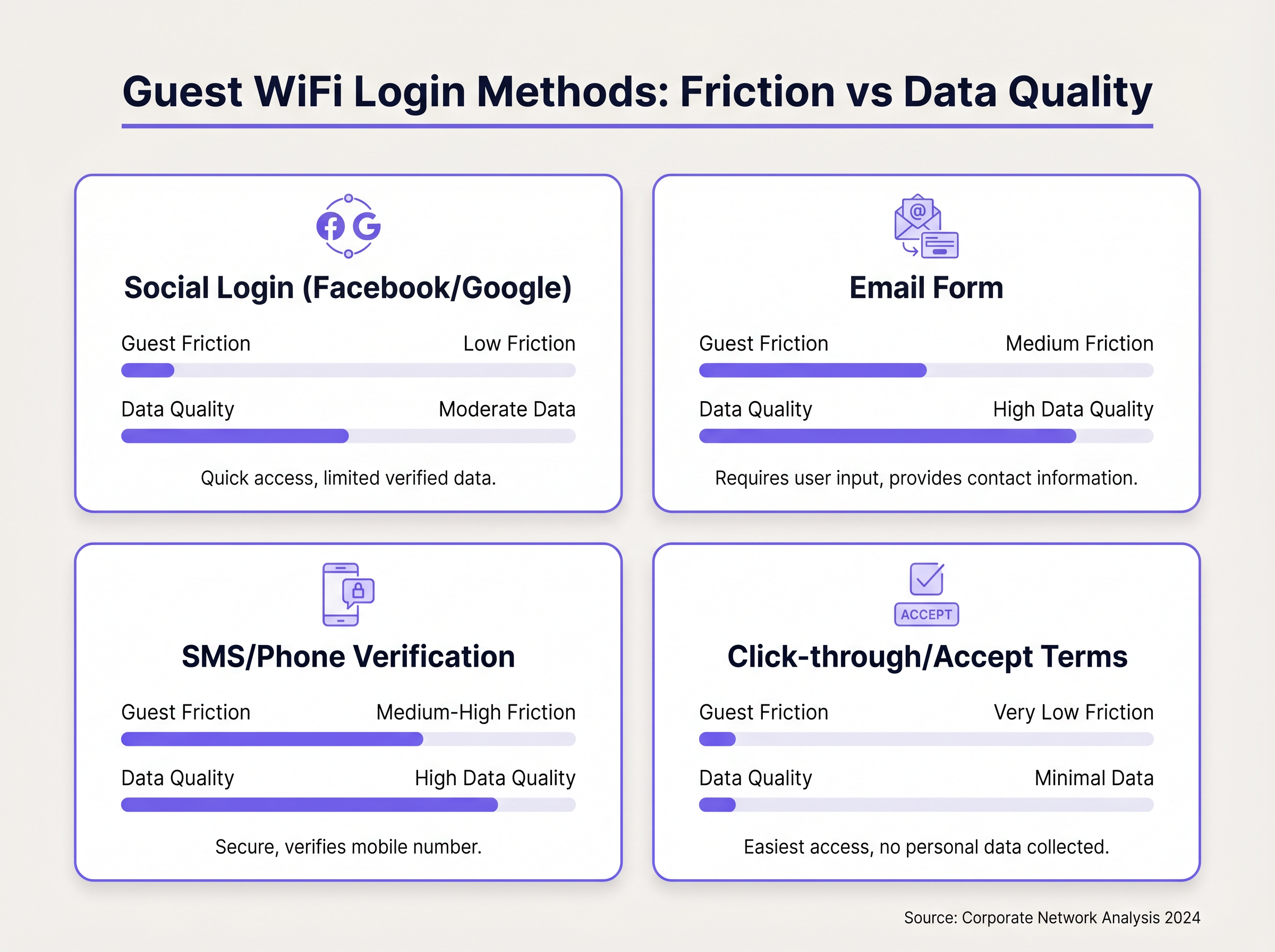
Form-Based Authentication requires users to input specific data fields such as email address, name, and postal code. While this yields high-fidelity CRM data, it introduces the highest user friction. Implementing robust validation — including regex for email formats and real-time MX record verification — at the edge is essential to maintain database hygiene and prevent dirty data from propagating into the CRM.
Social Authentication via OAuth 2.0 allows users to authenticate using existing credentials from platforms like Google or Facebook. This significantly reduces friction while securely retrieving verified demographic data points. The technical overhead involves managing API keys, secret tokens, and ensuring the portal's callback URLs are correctly registered with the identity providers. The data quality is substantially higher than form-based input because the identity provider has already verified the user's credentials.
Seamless Authentication via Passpoint (Hotspot 2.0) enables returning visitors to reconnect without presenting the captive portal. The device uses 802.1X/EAP authentication with WPA3-Enterprise security, providing a seamless and highly secure experience. Purple operates as a free identity provider for services like OpenRoaming under the Connect licence, enabling frictionless access while maintaining the user profile association across visits.
| Authentication Method | User Friction | Data Quality | Technical Complexity | Best Suited For |
|---|---|---|---|---|
| Form-Based | High | High | Low | Hotels, conference centres |
| Social Login (OAuth) | Low | Medium-High | Medium | Retail, F&B, events |
| SMS Verification | Medium | High | Medium | High-security environments |
| Click-Through / AUP | Very Low | Minimal | Low | Healthcare, public sector |
| Passpoint / OpenRoaming | None (returning) | Profile-based | High | Airports, transport hubs |
Network Segmentation and Security Architecture
Guest traffic must be logically isolated from corporate infrastructure. This is a non-negotiable security requirement, not an optional configuration. The recommended architecture deploys a dedicated VLAN for guest access with strict Access Control Lists (ACLs) preventing lateral movement into internal subnets. For a detailed breakdown of why this separation matters, see What Is the Difference Between a Guest WiFi Network and Your Main Network? .
The guest VLAN should provide direct internet breakout — ideally via a separate physical or logical WAN interface — with a stateful firewall inspecting outbound traffic. DNS filtering at the gateway level can enforce content policies and prevent the guest network from being used as a vector for malicious activity.
Implementation Guide
Step 1: Infrastructure Preparation
Before configuring the portal, provision the dedicated guest VLAN and verify that the NAC or controller supports captive portal redirection. Confirm that the walled garden configuration is correctly scoped — it should include the portal hosting domain, any CDN endpoints serving portal assets, and the OAuth API domains for any social login providers you intend to support.
Step 2: Portal Design and Responsive UX
The captive portal must be designed with a mobile-first philosophy, as over 85% of guest WiFi authentications occur on mobile devices.
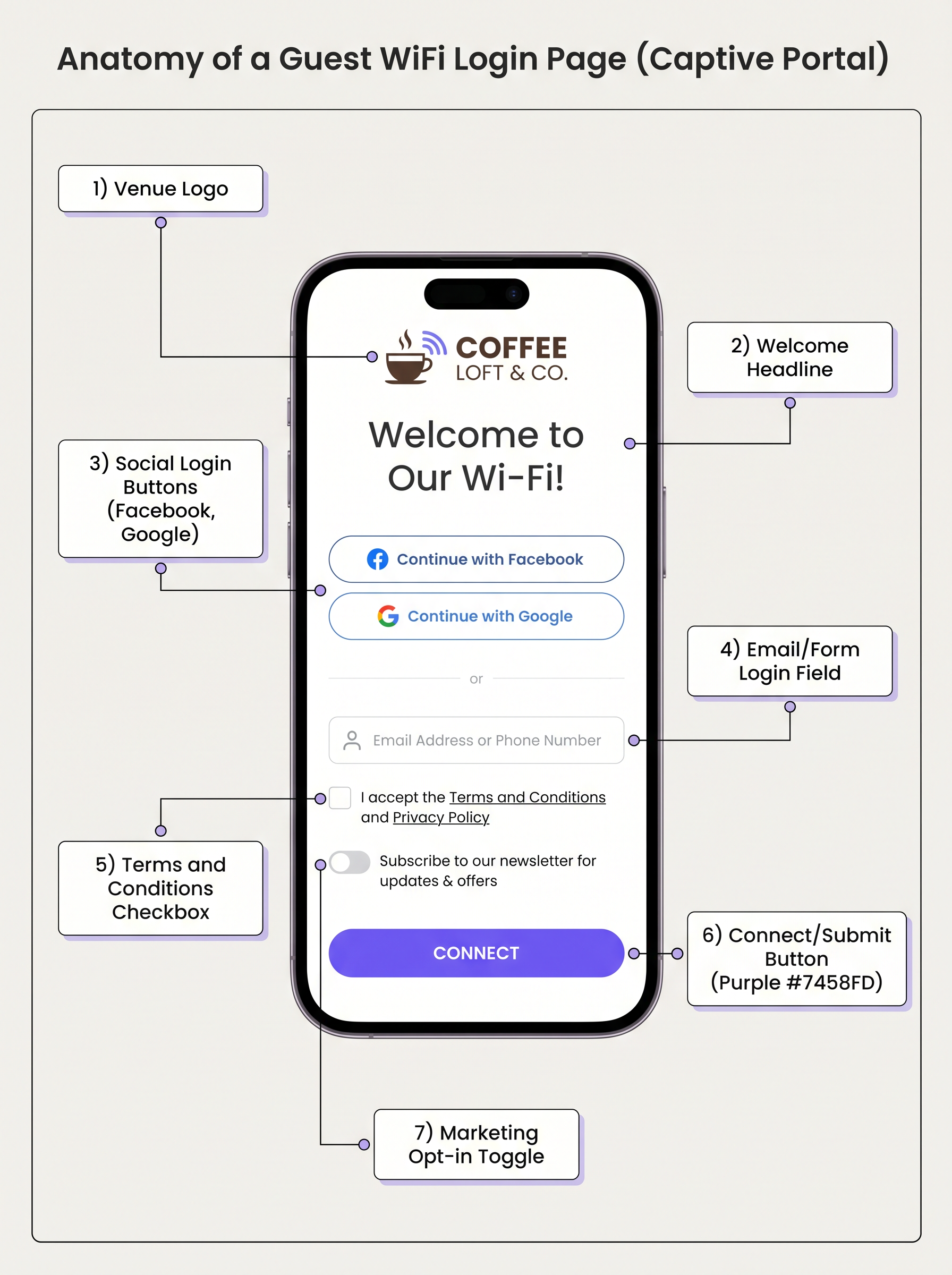
The portal should load within two seconds. Minimise payload sizes by compressing images, inlining critical CSS, and avoiding heavy JavaScript frameworks. A key constraint that many teams overlook: Apple's Captive Network Assistant (CNA) — the mini-browser that automatically invokes on iOS and macOS — has restricted capabilities. It does not support persistent cookies in the same way a full browser does, and it has limited JavaScript execution. Build the initial authentication flow to function without reliance on advanced browser features.
From a UX perspective, the portal should present a clear hierarchy: venue branding at the top, a concise value proposition ("Free WiFi — connect in seconds"), the authentication options, and a minimal legal footer. Avoid presenting the full terms and conditions inline; link to them within the walled garden.
Step 3: Data Capture Field Strategy
Apply the principle of progressive profiling. On the first visit, ask only for an email address and explicit marketing consent. On the second visit, prompt for a first name. On the third, a date of birth or postal code. This approach maintains low friction on the critical first interaction while building a comprehensive CRM profile over time.
For GDPR compliance, the consent mechanism must be explicit, unbundled, and granular. The marketing opt-in must be a separate, unchecked checkbox — it cannot be bundled with the terms of service acceptance. Record the consent timestamp, the portal version, and the specific consent language presented, as this constitutes the audit trail required under Article 7 of the GDPR.
Step 4: CRM and Analytics Integration
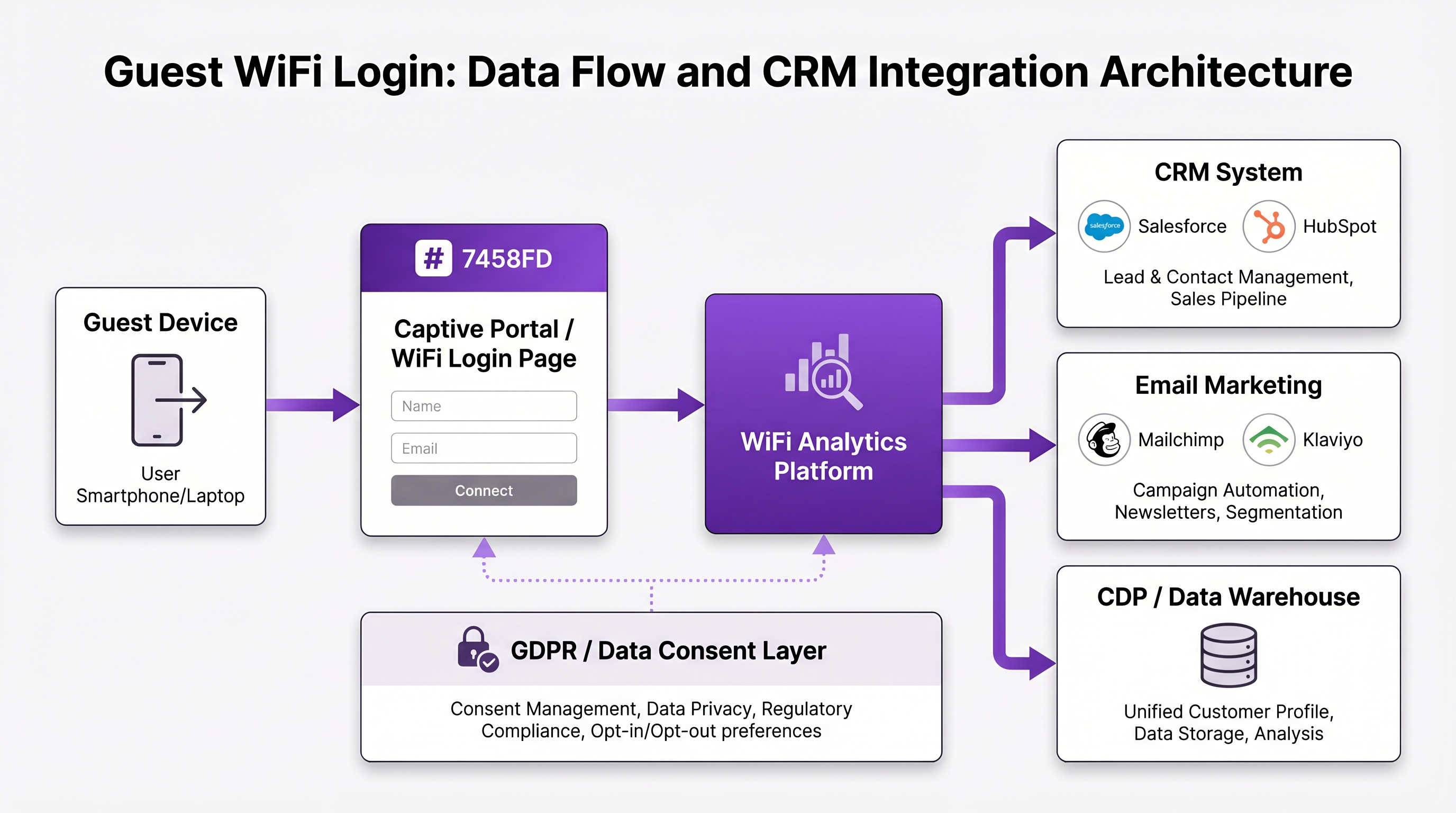
Post-authentication, the WiFi Analytics platform should immediately parse the authentication payload and transmit the data to the central CRM or Customer Data Platform (CDP) via a secure webhook or REST API call. This integration enables automated marketing workflows: a welcome email triggered within seconds of connection, a post-visit survey dispatched 24 hours after departure, or a loyalty reward notification on the third visit.
For distributed enterprise deployments — such as retail chains across Retail environments — centralising the authentication layer is critical. Rather than configuring complex walled gardens on every local controller, the local hardware is configured to redirect all unauthenticated traffic to the central cloud portal via RADIUS. The central platform manages the OAuth integrations and handles the API callbacks, abstracting the complexity away from the edge hardware and ensuring a consistent brand experience across all locations.
Best Practices
Progressive Profiling Over Comprehensive Forms. Do not attempt to capture every data point on the first interaction. A single email address with consent is worth more than a complete profile with a 60% abandonment rate. Build the profile incrementally across multiple visits.
Compliance by Design. The login page is the primary interface for regulatory compliance. GDPR Article 7 requires that consent be freely given, specific, informed, and unambiguous. The terms of service and privacy policy must be easily accessible within the walled garden, and the consent record must be stored with sufficient metadata to demonstrate compliance in the event of a regulatory audit.
Brand Consistency. The portal should feel like a seamless extension of the venue's physical and digital brand. Consistent typography, colour palette, and imagery reinforce trust and reduce abandonment. A portal that looks generic or mismatched with the venue brand signals to users that they may be on a rogue network.
Performance Optimisation. In high-density environments such as stadiums or conference centres, the portal infrastructure must be designed for concurrent load. Cloud-hosted portal solutions with global CDN distribution are significantly more resilient than on-premise portal servers under peak load conditions.
For venues operating across multiple sites, exploring The Core SD WAN Benefits for Modern Businesses is relevant — SD-WAN can ensure consistent, high-availability WAN connectivity for cloud-hosted portal services across distributed locations.
Troubleshooting & Risk Mitigation
Captive Portal Fails to Invoke
The most common failure mode is the captive portal not automatically presenting on the client device. This is almost always a walled garden or DNS configuration issue. Ensure the controller is correctly intercepting HTTP requests to captive portal detection URLs: captive.apple.com for Apple devices and connectivitycheck.gstatic.com for Android. If these domains are inadvertently whitelisted in the walled garden, the device assumes it has full internet access and bypasses the portal trigger entirely.
MAC Address Randomisation
Modern operating systems — iOS 14 and later, Android 10 and later — employ MAC address randomisation, generating a unique random MAC address for each SSID association. This disrupts legacy analytics platforms that rely on the MAC address as a persistent unique identifier for returning visitor tracking. The mitigation is to shift reliance from hardware identifiers to authenticated user profiles. By driving users toward login (and utilising seamless reconnection technologies like Passpoint for returning visitors), the network identifies the user based on their authenticated profile rather than their ephemeral hardware address.
Dirty Data and Invalid Submissions
Form-based portals are susceptible to users entering invalid or deliberately false data. Implement real-time edge validation: regex checking for email syntax, MX record verification for the email domain, and rate limiting to prevent automated submissions. Alternatively, shift the primary authentication method to Social Login, which provides inherently verified email addresses from the identity provider.
SSL Certificate Warnings
If the portal is served over HTTPS with a self-signed certificate, users will encounter browser security warnings that significantly increase abandonment. Ensure the portal domain has a valid, CA-signed TLS certificate. For cloud-hosted portal solutions, this is typically managed automatically.
ROI & Business Impact
Deploying a strategic guest WiFi login page transforms network infrastructure from a sunk cost into a measurable revenue driver. The ROI calculation spans three primary vectors.
Database Growth and CPA. Calculate the cost per acquisition of an email address via traditional digital marketing channels versus the captive portal. Venues consistently report a 300–500% increase in database growth rates post-deployment, at a fraction of the CPA of paid digital acquisition.
Dwell Time and Revenue Correlation. By analysing presence data from the WiFi Analytics platform, operators can correlate WiFi usage patterns with dwell time and transaction data. In Retail environments, increased dwell time directly correlates with higher average transaction values. In Hospitality environments, connected guests demonstrate higher F&B spend and ancillary service uptake.
Operational Efficiency. Implementing self-serve, automated onboarding reduces the burden on front-line staff — hotel receptionists no longer distribute paper slips with passwords, and retail associates are not interrupted to assist with WiFi access. This operational saving, combined with the data asset created, delivers a compelling business case for investment.
For Transport and Healthcare operators, the ROI calculation also incorporates risk mitigation: a properly deployed captive portal with documented consent and network segmentation significantly reduces the organisation's exposure to data protection regulatory risk.
Key Terms & Definitions
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before full internet access is granted. Implemented via DNS hijacking or HTTP redirection at the gateway.
The technical foundation of the guest WiFi login experience. Every guest WiFi login page is, architecturally, a captive portal.
Walled Garden
A restricted network environment that controls which web resources a client device can access prior to completing authentication on the captive portal.
Must be correctly scoped to allow devices to load portal assets and reach OAuth identity provider APIs before authentication. Misconfigured walled gardens are the primary cause of portal load failures.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol providing centralised Authentication, Authorization, and Accounting (AAA) management for network access. Operates on UDP ports 1812 (authentication) and 1813 (accounting).
The protocol used by the access point or controller to communicate with the central authentication server, verify credentials, and enforce bandwidth or VLAN policies post-authentication.
MAC Address Randomisation
A privacy feature in modern operating systems (iOS 14+, Android 10+) where the device generates a random MAC address per SSID, preventing persistent hardware-level tracking across sessions.
Disrupts legacy analytics platforms that rely on MAC addresses as persistent identifiers. Requires venues to implement authenticated login pages to maintain returning-visitor recognition.
Progressive Profiling
The practice of collecting user data incrementally across multiple interactions rather than demanding a complete profile at the first touchpoint.
Applied to login page design to minimise first-visit friction while building a comprehensive CRM profile over time. Typically: email on visit 1, name on visit 2, phone/postcode on visit 3.
Passpoint / Hotspot 2.0
A Wi-Fi Alliance certification standard (based on IEEE 802.11u) that enables mobile devices to automatically discover and connect to Wi-Fi networks using 802.1X/EAP authentication, without manual credential entry.
Enables seamless, secure WPA3-Enterprise reconnection for returning visitors, bypassing the captive portal while maintaining authenticated user profile association.
Captive Network Assistant (CNA)
The restricted pseudo-browser that automatically invokes on Apple iOS and macOS devices upon detecting a captive portal, presenting the login page within a sandboxed WebKit view.
Has significant limitations compared to a full browser: restricted cookie support, no tab navigation, limited JavaScript execution. Login pages must be designed to function correctly within the CNA environment.
First-Party Data
Customer data collected directly by the organisation from its own interactions with customers, owned entirely by the collecting organisation.
The primary commercial driver for deploying a guest WiFi login page. As third-party cookies are deprecated and privacy regulations tighten, first-party data collected via authenticated WiFi login is increasingly valuable.
OAuth 2.0
An open authorisation framework that enables applications to obtain limited access to user accounts on a third-party service (e.g., Google, Facebook) without exposing the user's credentials.
The protocol underpinning Social Login on captive portals. Allows the portal to retrieve verified user profile data (email, name) from the identity provider upon successful authentication.
VLAN (Virtual Local Area Network)
A logical subdivision of a physical network that isolates traffic between different groups of devices, enforced at the switch or controller level.
Guest WiFi traffic must be segregated onto a dedicated VLAN with strict ACLs to prevent lateral movement into corporate infrastructure — a fundamental security requirement for any guest network deployment.
Case Studies
A 400-room luxury hotel is experiencing a 40% drop-off rate on their current guest WiFi login page. They currently require guests to enter their room number, last name, email address, and accept a 5-page terms of service document before connecting. The IT Director needs to redesign this flow without losing the PMS integration that enables room-based billing.
Implement a tiered authentication model. For basic internet access (Tier 1), offer a Social Login (OAuth via Google or Facebook) option as the primary path — this reduces friction to a single tap and captures a verified email address. For premium, high-speed access (Tier 2), retain the PMS integration: the guest provides their Room Number and Last Name, the portal queries the PMS API, and upon successful match, the user is granted premium bandwidth with room-charge capability enabled. Replace the inline 5-page terms document with a concise, plain-language summary (3–4 sentences) with a required checkbox, linking to the full document hosted within the walled garden. Implement progressive profiling: capture the email on Tier 1 login, and prompt for loyalty programme enrolment on the post-authentication splash page rather than during the login flow itself.
A national retail chain with 150 locations wants to deploy a guest WiFi login page to build their marketing database. Their network estate is heterogeneous — a mix of Cisco, Aruba, and Meraki access points deployed across different store generations. The Head of IT is concerned about the technical overhead of managing OAuth walled garden configurations across three different hardware platforms.
Deploy a centralised, vendor-agnostic cloud captive portal solution. Rather than configuring OAuth walled gardens on each local controller — which would require platform-specific configuration across three different management interfaces — each local AP or controller is configured to redirect all unauthenticated guest traffic to the central cloud portal via a simple RADIUS or URL redirect rule. The central platform manages all OAuth API integrations (Facebook, Google), handles the callback URLs, and processes the authentication. The local hardware simply enforces the RADIUS Access-Accept or Access-Reject response. This architecture abstracts the complexity away from the edge hardware entirely. All 150 locations present an identical, centrally managed brand experience, and all data flows into a single CRM integration point.
Scenario Analysis
Q1. A stadium IT director needs to onboard 50,000 fans onto guest WiFi during a 90-minute pre-match window. The current form-based login page is generating RADIUS server timeouts under peak load and a 35% abandonment rate. What architectural changes should be prioritised?
💡 Hint:Consider the impact of high-density concurrent authentication requests on RADIUS server capacity, and the relationship between form complexity and abandonment rate in time-pressured environments.
Show Recommended Approach
Switch the primary authentication method to Social Login (OAuth) or a 1-click 'Accept Terms' flow. Social login offloads authentication processing to Google/Facebook infrastructure, eliminating the RADIUS bottleneck for the initial credential verification step. The RADIUS server only processes the final Access-Accept/Reject decision. Reduce form fields to zero on first connection — capture email via the OAuth payload rather than a form. Deploy a cloud-hosted portal with CDN distribution to handle the concurrent load spike. Implement progressive profiling post-connection via a lightweight survey on the post-authentication redirect page.
Q2. A hospital network needs to provide guest WiFi for patients and visitors. Legal counsel has confirmed they are prohibited from collecting any personally identifiable information on the portal due to healthcare data regulations. However, the network team must ensure all users have accepted an Acceptable Use Policy before connecting. How should the portal be configured?
💡 Hint:Focus on the compliance requirement: AUP acceptance without PII collection. Consider what session data is necessary for network management versus what constitutes PII.
Show Recommended Approach
Deploy a Click-Through / Accept Terms Only captive portal. The user is presented with the AUP and a single 'Accept & Connect' button — no form fields, no social login. The RADIUS server assigns a session token based on the randomised MAC address (for session management and bandwidth policy enforcement only) without storing any PII. The session record retains the timestamp, MAC address, and AUP version accepted — sufficient for network audit purposes without constituting PII under most healthcare data frameworks. Ensure the AUP is clearly written and accessible within the walled garden.
Q3. After deploying a new email form-based login page across a 30-location restaurant chain, the marketing team reports that 55% of captured email addresses are invalid or clearly fake (e.g., a@a.com, test@test.com). The CRM is being polluted with unusable records. How should the IT team resolve this without introducing significant additional friction for genuine users?
💡 Hint:Consider both technical validation approaches and alternative authentication methods that inherently provide verified data.
Show Recommended Approach
Implement two complementary mitigations. First, add real-time edge validation on the email field: regex checking for syntactically valid email format, combined with MX record DNS lookup to verify the domain actually accepts email. This silently rejects obviously fake entries without adding user-visible friction. Second, introduce Social Login (Google/Facebook OAuth) as an alternative or primary authentication path. Social login provides inherently verified email addresses from the identity provider, reducing the fake data rate to near zero for that authentication path. Over time, as Social Login adoption increases, the proportion of verified records in the CRM will improve significantly.



