Aruba ClearPass vs Cisco ISE: Comparativa de Plataformas NAC
Esta guía de referencia técnica ofrece una comparación detallada y neutral de Aruba ClearPass y Cisco ISE. Proporciona a arquitectos de red y gerentes de TI información práctica sobre arquitectura, complejidad de implementación, licencias y ecosistemas de integración para tomar decisiones informadas sobre plataformas NAC.
Escuchar esta guía
Ver transcripción del podcast

Resumen Ejecutivo
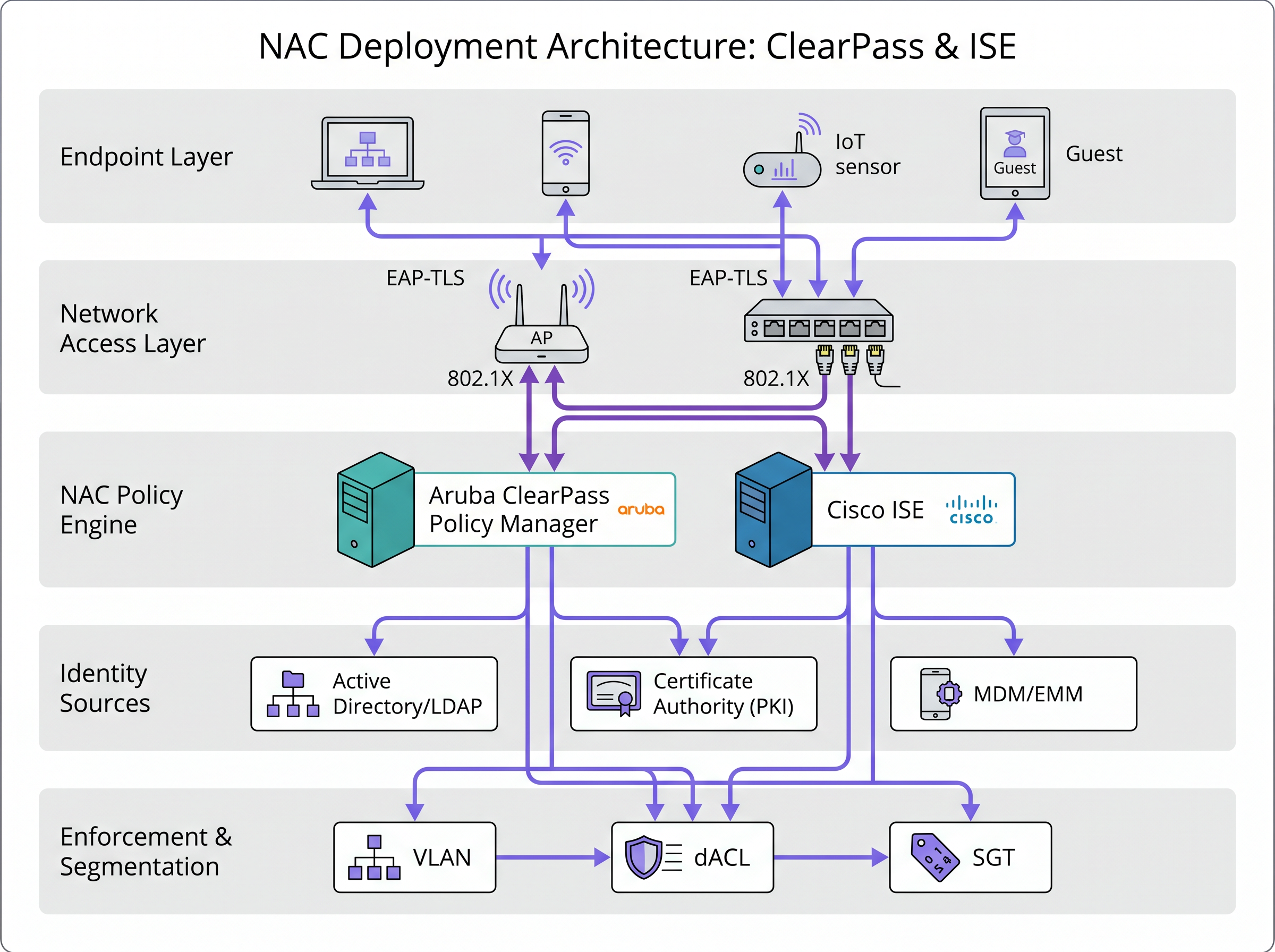
Para arquitectos de red empresariales y CTOs que evalúan plataformas de Control de Acceso a la Red (NAC), la elección a menudo se reduce a dos fuerzas dominantes: Aruba ClearPass y Cisco Identity Services Engine (ISE). Ambas plataformas ofrecen sólidas capacidades de autenticación, autorización y contabilidad (AAA), asegurando que cada punto final —desde portátiles corporativos hasta sensores IoT sin interfaz— sea perfilado y segmentado de forma segura antes de obtener acceso a la red. Sin embargo, sus filosofías arquitectónicas difieren significativamente. Cisco ISE está profundamente integrado en el ecosistema Cisco, aprovechando protocolos propietarios como pxGrid y TrustSec para ofrecer una microsegmentación sin igual en entornos homogéneos. Por el contrario, Aruba ClearPass está diseñado desde cero como un motor de políticas independiente del proveedor, utilizando estándares abiertos como RADIUS y REST APIs para integrarse sin problemas en redes de múltiples proveedores. Esta guía ofrece una comparación pragmática y en profundidad de ambas plataformas, explorando sus características, complejidades de implementación y modelos de licencia para ayudarle a alinear su estrategia NAC con las realidades operativas y los requisitos de cumplimiento de su organización.
Análisis Técnico Detallado
Arquitectura e Integración del Ecosistema
La divergencia fundamental entre ClearPass e ISE radica en su enfoque de integración del ecosistema. Cisco ISE prospera en un entorno centrado en Cisco. Utiliza Security Group Tags (SGTs) dentro del marco Cisco TrustSec para aplicar un control de acceso granular y escalable en switches Catalyst, puntos de acceso Meraki y firewalls Firepower sin depender únicamente de las Listas de Control de Acceso (ACLs) tradicionales basadas en IP. El protocolo pxGrid (Platform Exchange Grid) mejora aún más esto al permitir que ISE comparta datos contextuales enriquecidos con soluciones de seguridad de terceros, creando un ecosistema de respuesta a amenazas cohesivo y automatizado.
Aruba ClearPass, por el contrario, adopta una filosofía de red heterogénea. Actúa como un traductor universal, aplicando políticas consistentes en hardware de Aruba, Cisco, Juniper y Palo Alto utilizando protocolos estándar RADIUS y TACACS+. Su robusta REST API y su amplio ecosistema de integración le permiten ingerir contexto de plataformas de Mobile Device Management (MDM), firewalls y agentes de seguridad de endpoints sin esfuerzo. Para entornos con implementaciones de hardware mixtas, ClearPass a menudo presenta una barrera de entrada más baja para la aplicación unificada de políticas.
Motor de Políticas e Interfaz de Gestión
La creación de políticas en ClearPass es altamente visual y orientada a servicios. Los administradores definen un 'Servicio' (por ejemplo, 'Corporate 802.1X') y apilan secuencialmente métodos de autenticación, fuentes de autorización y perfiles de aplicación. Este enfoque modular y de arriba hacia abajo es intuitivo y simplifica la resolución de problemas.
Cisco ISE utiliza una matriz basada en reglas, similar a la configuración de un firewall sofisticado. Las políticas se construyen utilizando reglas complejas y de múltiples condiciones que evalúan la identidad, la postura y el contexto simultáneamente. Si bien esto ofrece una inmensa flexibilidad y potencia para escenarios empresariales complejos, exige una curva de aprendizaje más pronunciada y una gestión de configuración meticulosa para evitar consecuencias no deseadas.
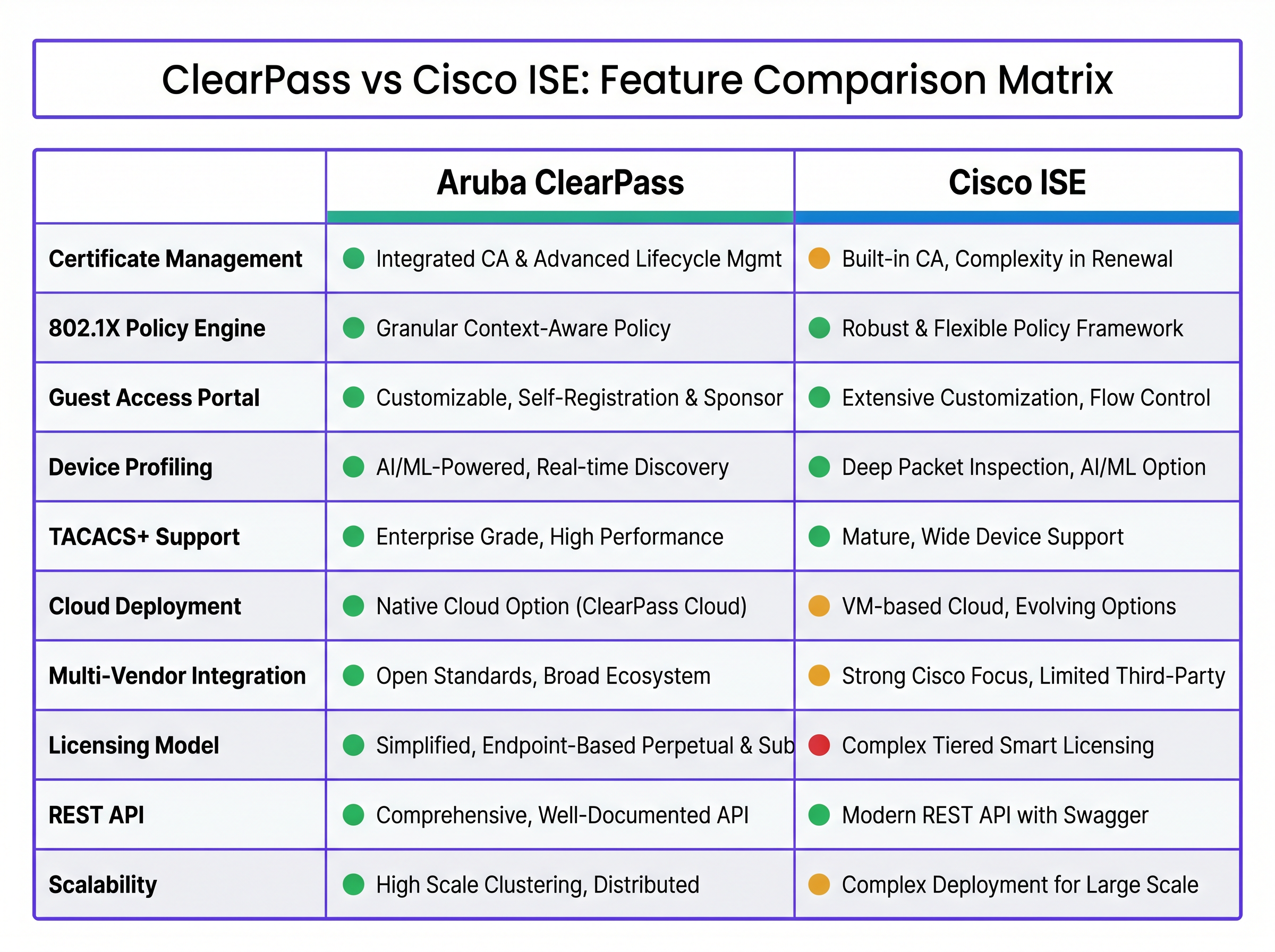
Perfilado y Visibilidad de Dispositivos
El perfilado preciso de dispositivos es fundamental para el NAC moderno, especialmente con la proliferación de dispositivos IoT. Ambas plataformas sobresalen en este aspecto, utilizando datos DHCP, HTTP, MAC OUI y SNMP. ISE tiene una ventaja en entornos Cisco a través de Device Sensor, que alimenta datos de inspección profunda de paquetes directamente desde los switches Cisco al nodo ISE. ClearPass contrarresta esto con ClearPass Device Insight, una solución basada en la nube y con IA que aprovecha el aprendizaje automático para identificar dispositivos oscuros o falsificados que eluden las firmas de perfilado estándar.
Guía de Implementación
Desplegar una plataforma NAC es una operación de alto riesgo. Una configuración incorrecta puede bloquear a usuarios legítimos fuera de la red, paralizando las operaciones comerciales.
- Comience con la Visibilidad (Modo Monitor): Nunca implemente la aplicación de políticas el primer día. Configure el NAC para perfilar dispositivos y registrar solicitudes de autenticación sin bloquear el tráfico. Esto proporciona una imagen clara de lo que realmente hay en su red y ayuda a identificar los dispositivos que fallarán la autenticación 802.1X.
- Aplique primero en la red Wireless: Las redes Wireless son generalmente más fáciles de asegurar porque los dispositivos están acostumbrados a autenticarse (por ejemplo, WPA3-Enterprise). Comience con los portátiles corporativos gestionados por Active Directory o un MDM, ya que estos pueden recibir fácilmente los certificados necesarios.
- Aborde la Red Cableada: El 802.1X cableado es notoriamente difícil debido a impresoras antiguas, dispositivos IoT no gestionados y switches 'tontos'. Utilice MAC Authentication Bypass (MAB) para dispositivos que no pueden soportar 802.1X, pero limite estrictamente su acceso a la red utilizando asignación dinámica de VLAN o dACLs.
- Implemente el Acceso de Invitados: Para entornos de hostelería y retail, el acceso de invitados es una preocupación principal. ClearPass Guest ofrece un portal altamente personalizable con auto-registro y aprobación de patrocinadores, integrándose sin problemas con plataformas como Guest WiFi para análisis avanzados. ISE también proporciona sólidas capacidades para invitados, pero puede requerir más esfuerzo para lograr una experiencia de marca altamente personalizada.
Mejores Prácticas
- Mantenga la Higiene del Directorio: Un NAC es tan efectivo como el almacén de identidades que consulta. Asegúrese de que su Active Directory o LDAP esté limpio, preciso y actualizado.
- Aproveche los Certificados: Evite la autenticación basada en contraseña (PEAP-MSCHAPv2) siempre que sea posible. DeDespliegue EAP-TLS utilizando certificados emitidos por una Autoridad de Certificación (CA) de confianza para una seguridad superior y una experiencia de usuario fluida.
- Planificación de Alta Disponibilidad: NAC es un componente crítico de la infraestructura. Despliegue nodos redundantes en una arquitectura distribuida para asegurar un acceso continuo a la red durante el mantenimiento o fallos.
Resolución de Problemas y Mitigación de Riesgos
Los modos de fallo comunes a menudo giran en torno a la caducidad de los certificados, el orden incorrecto de las políticas o los puertos de switch mal configurados.
- Caducidad de Certificados: Implemente procesos automatizados de renovación de certificados (por ejemplo, SCEP/EST) para prevenir fallos de autenticación repentinos y generalizados.
- Orden de las Políticas: Tanto en ClearPass como en ISE, las políticas se evalúan de arriba a abajo. Asegúrese de que las reglas más específicas se coloquen por encima de las reglas generales para evitar accesos no deseados.
- Puntos de Acceso Maliciosos (Rogue APs): Asegúrese de que su sistema de prevención de intrusiones inalámbricas (WIPS) esté monitorizando activamente los ataques de suplantación de identidad. Consulte nuestra guía sobre Detección de Puntos de Acceso Maliciosos: Protegiendo el WiFi del Recinto de Ataques de Suplantación de Identidad para estrategias detalladas.
ROI e Impacto Empresarial
El impacto financiero de una implementación de NAC se extiende más allá de los costes iniciales de software y hardware.
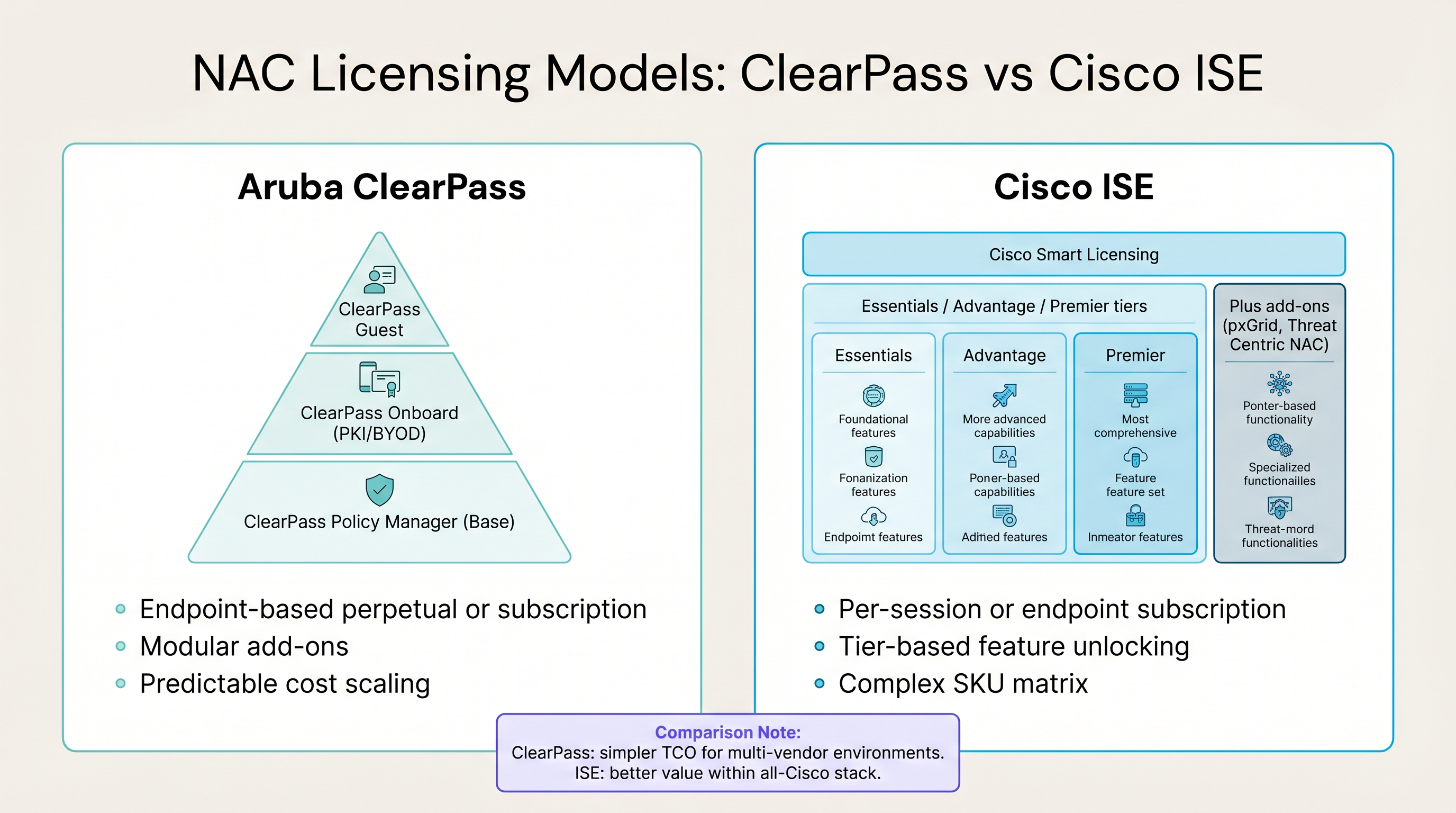
- Aruba ClearPass: Ofrece un modelo de licencia predecible basado en puntos finales (perpetuo o por suscripción) con complementos modulares para Invitados y Onboard. Esta simplicidad a menudo se traduce en un menor Coste Total de Propiedad (TCO) en entornos de múltiples proveedores.
- Cisco ISE: Utiliza un complejo modelo de Smart Licensing con niveles Essentials, Advantage y Premier. Aunque potencialmente más caro, ofrece un ROI excepcional si se aprovechan al máximo las capacidades avanzadas de una arquitectura de seguridad unificada de Cisco.
En última instancia, una implementación exitosa de NAC mitiga el riesgo de costosas filtraciones de datos, asegura el cumplimiento de estándares como PCI DSS y GDPR, y reduce la sobrecarga operativa del aprovisionamiento manual de la red.
Definiciones clave
802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol for secure enterprise network access, preventing unauthorized devices from communicating on the network.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The primary protocol used by both ClearPass and ISE to communicate with network switches and access points.
TACACS+ (Terminal Access Controller Access-Control System Plus)
A Cisco-developed protocol that provides access control for routers, network access servers, and other networked computing devices via one or more centralized servers.
Used primarily for device administration (authenticating IT staff logging into switches and routers), separating authentication from authorization.
MAC Authentication Bypass (MAB)
A method of authenticating devices that do not support 802.1X (like printers or legacy IoT devices) by using their MAC address as the identity credential.
A necessary workaround for headless devices, though inherently less secure than 802.1X as MAC addresses can be spoofed.
EAP-TLS (Extensible Authentication Protocol-Transport Layer Security)
An EAP method that relies on client and server certificates for mutual authentication.
Considered the gold standard for wireless and wired security, providing robust protection against credential theft.
TrustSec
A Cisco security architecture that uses Security Group Tags (SGTs) to enforce access control policies based on endpoint identity and context, rather than IP addresses.
A key differentiator for Cisco ISE in homogeneous Cisco environments, enabling scalable micro-segmentation.
pxGrid (Platform Exchange Grid)
A Cisco protocol that enables security platforms to share context and automate threat responses across the network infrastructure.
Allows ISE to act as a central intelligence hub, sharing user and device context with firewalls and endpoint security tools.
Device Profiling
The process of identifying the type, operating system, and capabilities of a device connecting to the network using various data sources (DHCP, HTTP, SNMP).
Essential for applying appropriate security policies to IoT and unmanaged devices that cannot authenticate via 802.1X.
Ejemplos prácticos
A large university campus with a mix of Aruba wireless controllers and legacy Juniper access switches needs to implement role-based access control for students, faculty, and IoT devices (projectors, smart locks). They currently use Active Directory for identity.
Given the multi-vendor environment, Aruba ClearPass is the recommended solution. The deployment would begin in monitor mode to profile the diverse range of IoT devices. Faculty and student laptops would be onboarded using ClearPass Onboard to provision EAP-TLS certificates, ensuring secure, password-less authentication. The legacy Juniper switches would be configured to use RADIUS for 802.1X authentication, with MAC Authentication Bypass (MAB) configured for the IoT devices. ClearPass policies would dynamically assign VLANs based on the user's AD group (Student vs. Faculty) or the device profile (IoT).
A global retail chain is standardizing its entire network infrastructure on Cisco Meraki (APs, switches, and MX security appliances). They need to enforce strict micro-segmentation to isolate point-of-sale (POS) terminals from the guest WiFi network and corporate devices to maintain PCI DSS compliance.
Cisco ISE is the optimal choice for this homogeneous Cisco environment. The deployment would leverage Cisco TrustSec to assign Security Group Tags (SGTs) to different endpoints. POS terminals would receive a specific SGT upon authentication (via MAB or 802.1X). ISE would then push Security Group Access Control Lists (SGACLs) to the Meraki switches and MX appliances, explicitly denying traffic between the POS SGT and the Guest or Corporate SGTs, regardless of the underlying IP addressing or VLAN structure.
Preguntas de práctica
Q1. A hospital network requires strict isolation between medical devices (infusion pumps, patient monitors) and the guest WiFi network. The infrastructure consists of Aruba wireless access points and Cisco Catalyst switches. Which NAC platform is best suited for this environment and why?
Sugerencia: Consider the multi-vendor nature of the network infrastructure.
Ver respuesta modelo
Aruba ClearPass is the recommended platform. While Cisco ISE is powerful, its advanced segmentation features (TrustSec/SGTs) require end-to-end Cisco hardware to function optimally. ClearPass can effectively manage policies across both Aruba APs and Cisco switches using standard RADIUS attributes to dynamically assign VLANs or dACLs, ensuring the medical devices are securely isolated from guest traffic.
Q2. Your organization is migrating from a password-based PEAP-MSCHAPv2 wireless network to a certificate-based EAP-TLS deployment to improve security. You have a large BYOD (Bring Your Own Device) population. What is a critical feature you need from your NAC platform to support this transition?
Sugerencia: Think about how certificates will be delivered to unmanaged personal devices.
Ver respuesta modelo
You need a robust onboarding and certificate provisioning portal. In the Aruba ecosystem, this is ClearPass Onboard; in Cisco, it's the ISE BYOD portal. This feature allows users to self-provision their personal devices by connecting to an open provisioning network, authenticating with their corporate credentials, and automatically downloading and installing the required EAP-TLS certificate and network profile, minimizing helpdesk overhead.
Q3. During a phased NAC rollout, you configure a switch port for 802.1X enforcement. A user connects a legacy printer that does not support 802.1X. What mechanism should the NAC platform use to authenticate this device, and what is the primary security risk associated with it?
Sugerencia: How do you identify a device that cannot provide a username or certificate?
Ver respuesta modelo
The NAC platform should use MAC Authentication Bypass (MAB). The switch sends the printer's MAC address to the NAC server as the username and password. The primary security risk is MAC spoofing; an attacker can easily discover the printer's MAC address, clone it to their laptop, and gain unauthorized access to the network segment assigned to the printer. Therefore, MAB must be combined with strict profiling and network segmentation (e.g., placing printers in a highly restricted VLAN).
Continúe leyendo esta serie
Términos y condiciones de la WiFi para empleados: Aspectos legales y de cumplimiento esenciales
Esta guía aborda los aspectos legales y técnicos esenciales para redactar y aplicar los términos y condiciones de la WiFi para empleados en establecimientos corporativos. Detalla qué incluir en una Política de Uso Aceptable (AUP), cómo cumplir con los requisitos de GDPR y PCI DSS, y cómo implementar la autenticación basada en la identidad y la segmentación de red para proteger los activos corporativos. Los responsables de TI, equipos de RR. HH. y directores de operaciones de hoteles, cadenas de retail, estadios y organizaciones del sector público encontrarán pautas prácticas que podrán implementar este trimestre.
Políticas de WiFi para el personal en el sector minorista: protección de las redes back-of-house
Esta guía cubre los requisitos técnicos y de políticas críticos para proteger las redes WiFi back-of-house en el sector minorista, desde la segmentación de VLAN y el cumplimiento de PCI DSS 4.0 hasta la gestión del BYOD de los empleados en la tienda. Ofrece a los responsables de TI, arquitectos de red y directores de operaciones un plan práctico y neutral respecto al proveedor que pueden poner en marcha este trimestre.
El Futuro de la Seguridad Wi-Fi: NAC Impulsado por IA y Detección de Amenazas
Esta guía autorizada explora la evolución de la seguridad Wi-Fi empresarial, desde el WPA2 heredado hasta el Control de Acceso a la Red (NAC) impulsado por IA y la detección de amenazas. Diseñada para líderes de TI, proporciona estrategias de implementación prácticas para asegurar entornos de alta densidad como comercios minoristas, hostelería y estadios utilizando las redes basadas en identidad de Purple.