Comparación de Puntos de Acceso Basados en Controlador vs. Gestionados en la Nube
Esta guía de referencia técnica compara las arquitecturas de Puntos de Acceso basados en controlador y gestionados en la nube para entornos empresariales. Proporciona a los líderes de TI un marco neutral para evaluar modelos de implementación, el costo total de propiedad y las capacidades de integración con plataformas de inteligencia de invitados como Purple.
Escucha esta guía
Ver transcripción del podcast
- Resumen Ejecutivo
- Análisis Técnico Detallado: Arquitectura y Planos de Control
- Arquitectura Basada en Controlador
- Arquitectura Gestionada en la Nube
- Implicaciones de Seguridad y Cumplimiento
- Guía de Implementación: Despliegue e Integración
- Aprovisionamiento sin Contacto (Zero-Touch) vs. Despliegue por Etapas
- Integración de Inteligencia y Analítica de Huéspedes
- Mejores Prácticas y Mitigación de Riesgos
- ROI e Impacto Comercial

Resumen Ejecutivo
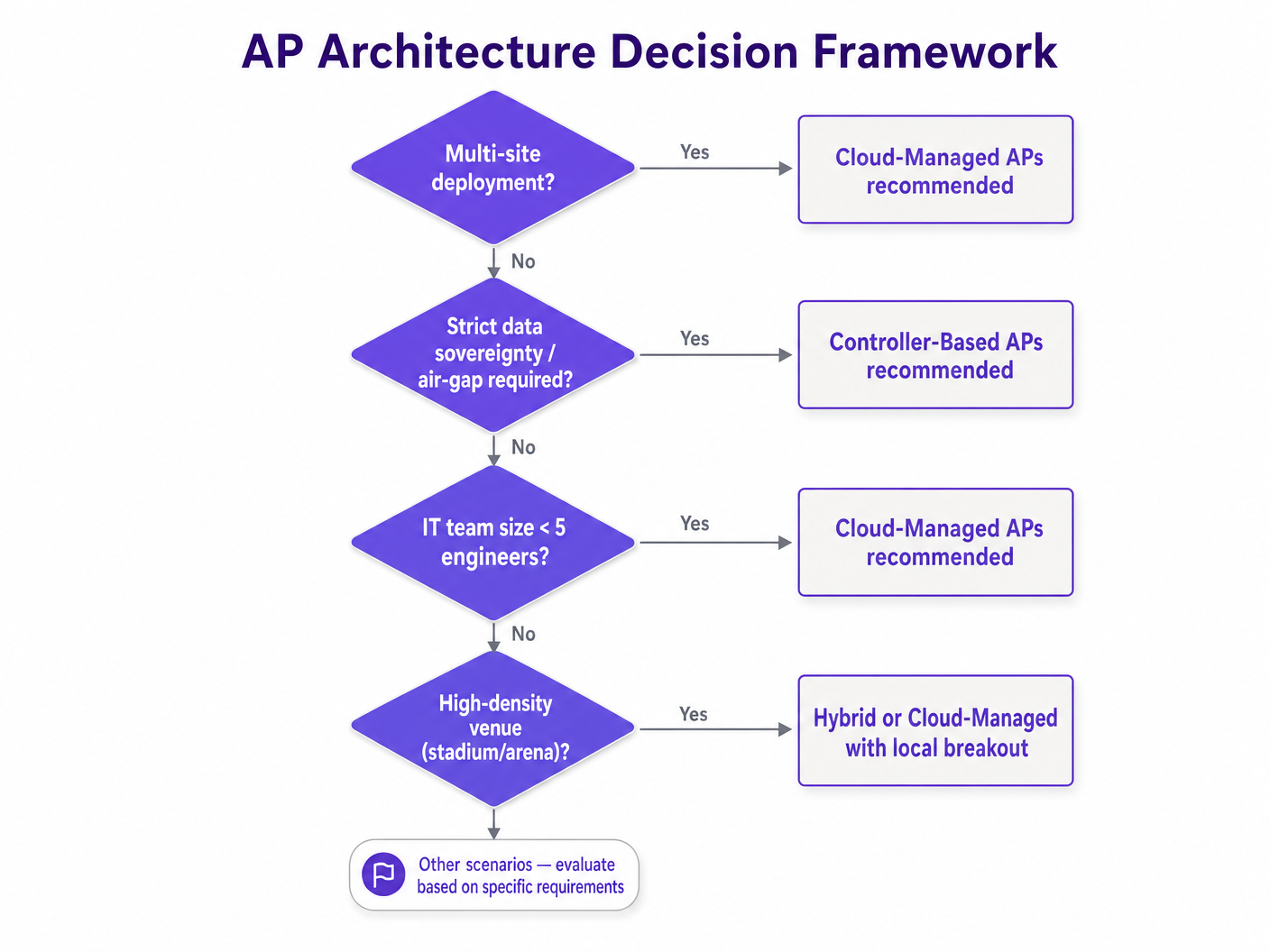
Para los operadores de recintos empresariales, la decisión arquitectónica entre Puntos de Acceso (APs) basados en controlador y gestionados en la nube define la agilidad operativa, la postura de seguridad y el costo total de propiedad (TCO) de su red para los próximos cinco a siete años. A medida que los recintos de Hospitalidad , Comercio Minorista y Transporte digitalizan sus espacios físicos, el WiFi ya no es meramente una comodidad; es la capa de transporte crítica para sensores IoT, sistemas de Punto de Venta (POS) y plataformas de inteligencia de invitados.
Históricamente, las demandas de alta densidad de estadios y grandes centros de conferencias requerían Controladores de LAN Inalámbrica (WLCs) en las instalaciones para manejar la coordinación compleja de RF y el roaming sin interrupciones. Sin embargo, las arquitecturas modernas gestionadas en la nube, aumentadas por la gestión de recursos de radio (RRM) impulsada por IA, han cerrado significativamente esta brecha de rendimiento al tiempo que eliminan la sobrecarga operativa de gestionar dispositivos controladores físicos.
Esta guía de referencia técnica proporciona a arquitectos de red y directores de TI un marco neutral para evaluar arquitecturas de AP. Detalla las distinciones técnicas en la gestión del plano de control, examina escenarios de implementación en el mundo real y describe cómo estas arquitecturas se integran con plataformas empresariales de Guest WiFi y WiFi Analytics para impulsar resultados de negocio medibles.
Análisis Técnico Detallado: Arquitectura y Planos de Control
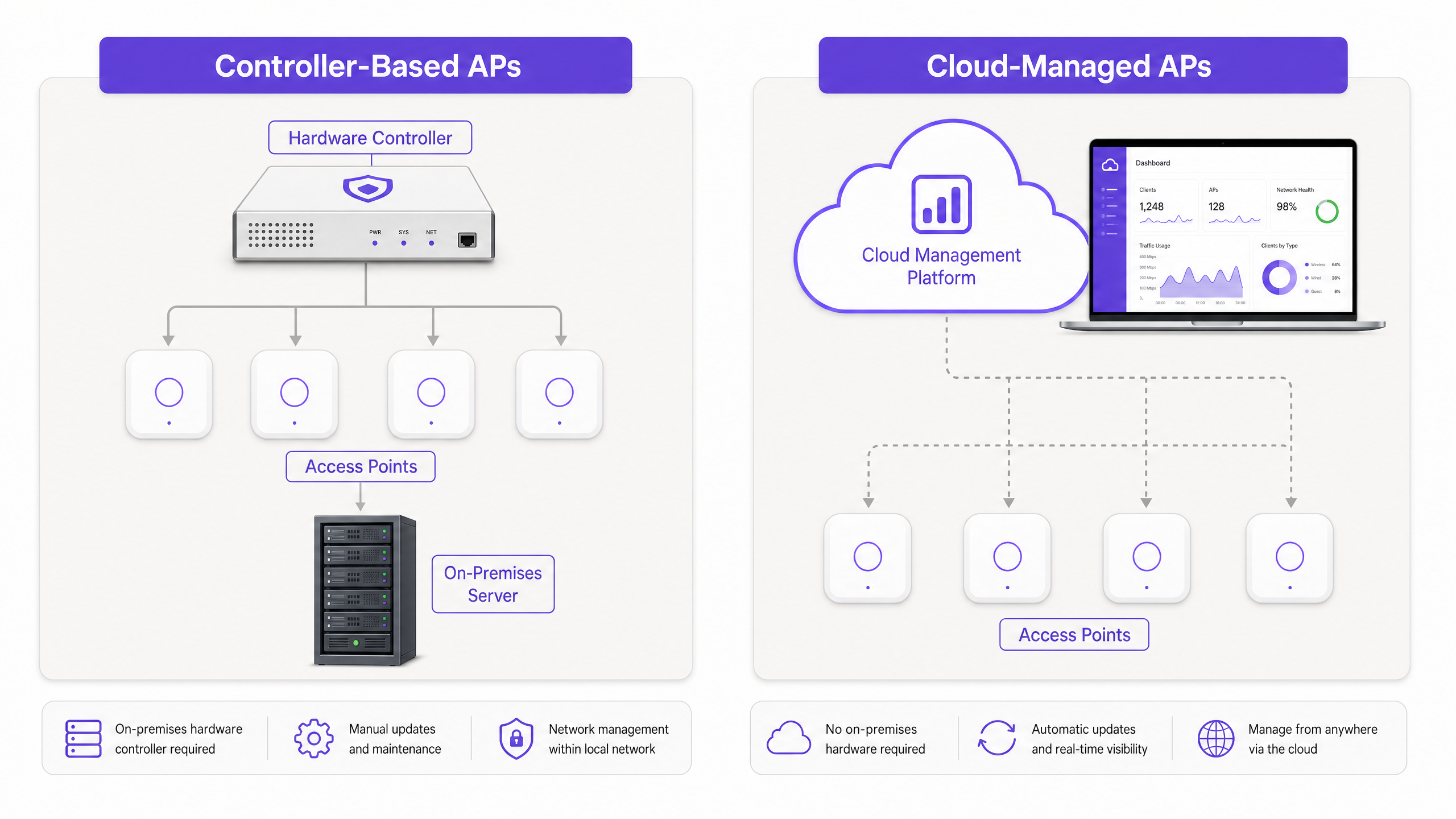
La distinción fundamental entre los APs basados en controlador y los gestionados en la nube radica en dónde residen los planos de gestión y control, y cómo los APs interactúan con el resto de la infraestructura de red.
Arquitectura Basada en Controlador
En un modelo tradicional basado en controlador, los APs "ligeros" terminan su gestión y a menudo su tráfico de datos en un dispositivo de hardware o virtual centralizado: el Controlador de LAN Inalámbrica (WLC). Los APs manejan las funciones físicas de radiofrecuencia (RF) de Capa 1 y Capa 2, pero la inteligencia está centralizada.
- Dependencia del Protocolo: Los APs se comunican con el WLC utilizando el protocolo Control and Provisioning of Wireless Access Points (CAPWAP) (RFC 5415).
- Procesamiento Centralizado: Las decisiones de roaming, los intercambios de autenticación (como 802.1X/EAP) y las asignaciones dinámicas de canales de RF son procesados por el controlador.
- Tunelización del Plano de Datos: En muchas implementaciones, el tráfico de datos del cliente se tuneliza de vuelta al WLC antes de salir a la red cableada. Esto permite la aplicación centralizada de políticas y una gestión simplificada de VLAN en un campus grande, pero crea un posible cuello de botella.
Ventajas para Entornos de Alta Densidad: Los sistemas basados en controlador sobresalen en entornos de ultra alta densidad (por ejemplo, estadios, grandes auditorios). Debido a que el WLC tiene una vista holística en tiempo real del entorno de RF en cientos de APs, puede coordinar la mitigación de interferencias de co-canal y gestionar el roaming 802.11r Fast BSS Transition (FT) con precisión de milisegundos.
Arquitectura Gestionada en la Nube
Las arquitecturas gestionadas en la nube descentralizan el plano de control. Los propios APs son "completos" o autónomos en términos de gestión local de RF y reenvío de datos, pero son orquestados centralmente a través de una plataforma de gestión alojada en la nube.
- Gestión Fuera de Banda: El AP establece un túnel de gestión seguro (típicamente HTTPS/TLS) a la nube del proveedor. La configuración, la telemetría y las actualizaciones de firmware fluyen a través de esta conexión.
- Salida Local: El tráfico de datos del cliente no se tuneliza a la nube. Sale localmente en el puerto del switch al que está conectado el AP.
- Supervivencia Local: Si la conexión a internet a la nube se cae, el AP continúa sirviendo a los clientes existentes, autenticando a nuevos clientes (si se utiliza RADIUS local o PSK) y enrutando el tráfico. Sin embargo, el equipo de TI pierde visibilidad en tiempo real y la capacidad de aplicar cambios de configuración hasta que se restablezca la conexión.
Implicaciones de Seguridad y Cumplimiento
Ambas arquitecturas soportan estándares de seguridad de nivel empresarial, incluyendo WPA3-Enterprise, autenticación 802.1X y detección de APs no autorizados. Sin embargo, la carga de cumplimiento difiere.
Con los sistemas gestionados en la nube, los equipos de TI deben asegurarse de que la plataforma en la nube del proveedor cumpla con los requisitos regulatorios relevantes (por ejemplo, SOC 2 Tipo II, ISO 27001) y que la residencia de datos se alinee con GDPR o las leyes de privacidad locales. Para entornos altamente sensibles que requieren un estricto aislamiento (air-gapping), como ciertas instalaciones gubernamentales o de defensa, un sistema basado en controlador que opere completamente dentro de la LAN local sigue siendo el estándar.
Para entornos que manejan datos de pago, ambas arquitecturas pueden lograr el cumplimiento de PCI DSS. Sin embargo, la segmentación de la red es crítica. La red de invitados, los dispositivos corporativos y los terminales POS deben aislarse en VLANs separadas, independientemente de la arquitectura del AP.
Guía de Implementación: Despliegue e Integración
El impacto operativo de la arquitectura elegida se hace más evidente durante el despliegue y la gestión continua, particularmente en escenarios multi-sitio.
Aprovisionamiento sin Contacto (Zero-Touch) vs. Despliegue por Etapas
Gestionado en la Nube: La principal ventaja operativa de los APs gestionados en la nube es el Aprovisionamiento sin Contacto (ZTP). Un AP puede enviarse directamente a una tienda minorista o un hotel remoto. Al conectarse, adquiere una dirección IP vía DHCP, se conecta a la nube, descarga su perfil preconfigurado y comienza a transmitir. Esto elimina la necesidad de costosas "visitas técnicas" o de desplegar ingenieros de red altamente cualificados a sitios remotos.
Basado en Controlador: La implementación de APs basados en controlador suele requerir más preparación. El AP debe ser capaz de descubrir el WLC (a menudo a través de la Opción 43 de DHCP o resolución DNS). El firmware a menudo debe alinearse manualmente entre el WLC y los APs. Para un despliegue en múltiples sitios, esto a menudo requiere preparar el hardware de forma centralizada antes del envío, o desplegar ingenieros en cada sitio.
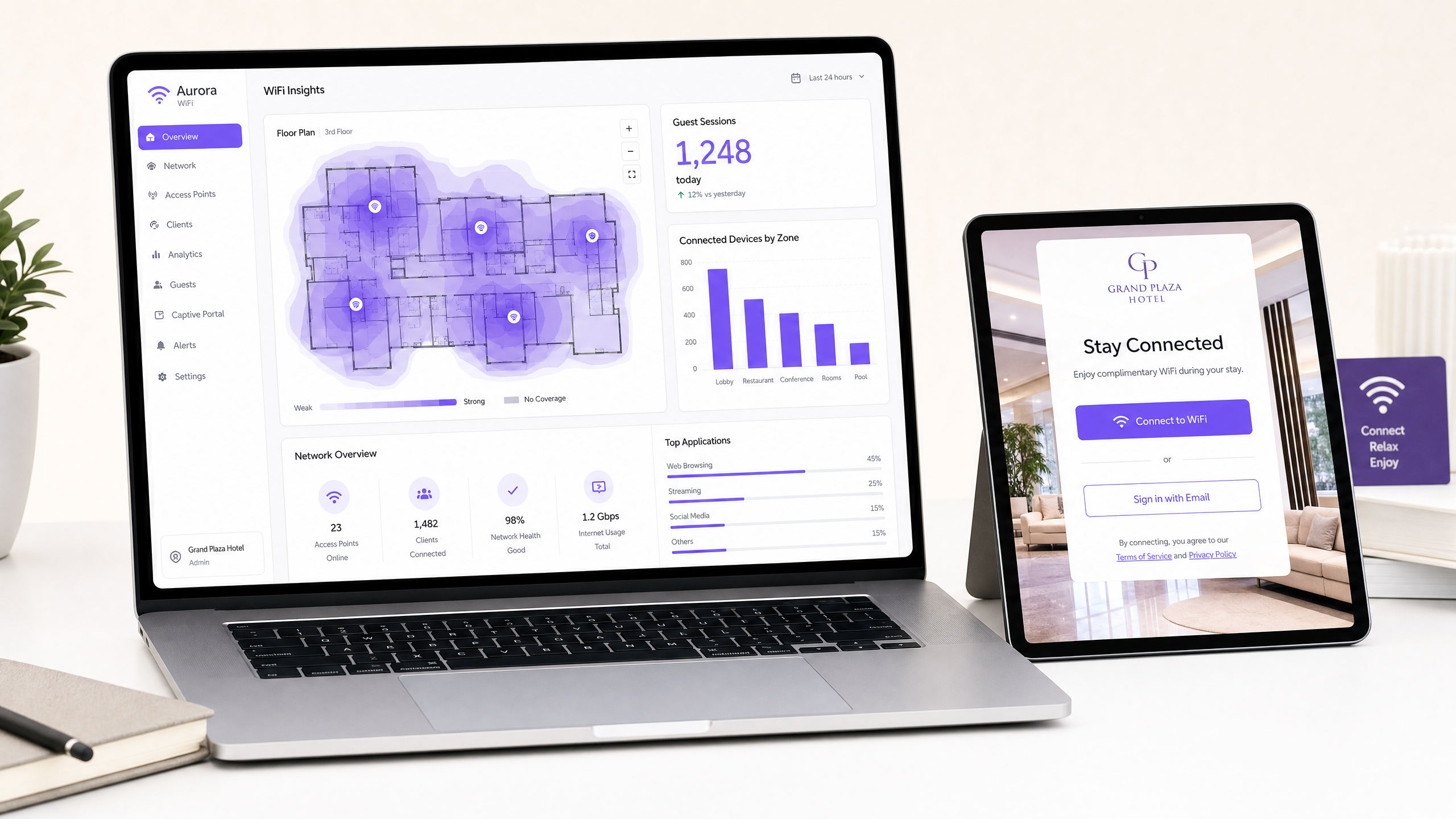
Integración de Inteligencia y Analítica de Huéspedes
La implementación de los APs físicos es solo la base. Para extraer valor comercial de la red, los establecimientos deben integrar su hardware con plataformas de inteligencia de huéspedes como Purple.
Purple opera como una capa superpuesta agnóstica al hardware, integrándose sin problemas con sistemas basados en controlador y gestionados en la nube de los principales proveedores (Cisco, Meraki, Aruba, Ruckus, Extreme).
- Autenticación y Onboarding: Purple gestiona la presentación del Captive Portal y la autenticación (a través de inicio de sesión social, formulario o Cómo un Wi-Fi assistant habilita el acceso sin contraseña en 2026 ). La arquitectura del AP simplemente necesita soportar la autenticación y contabilidad RADIUS, redirigiendo a los usuarios no autenticados al portal de Purple.
- Datos Analíticos: Purple ingiere datos de presencia y ubicación de los APs para alimentar su panel de analíticas. Ya sea que los datos se envíen a través de API desde un panel en la nube o directamente desde un WLC local, los conocimientos resultantes —tiempos de permanencia, tasas de retorno y afluencia— son idénticos. Para una inmersión más profunda en cómo se generan estos datos, consulte nuestra guía sobre Heatmapping vs. Análisis de Presencia: Diferencias Técnicas .
Mejores Prácticas y Mitigación de Riesgos
Independientemente de la arquitectura seleccionada, ciertas mejores prácticas fundamentales mitigan los riesgos de implementación y aseguran la estabilidad a largo plazo.
- Priorizar el Tráfico de Gestión: Para implementaciones gestionadas en la nube, la conexión de los APs a la nube es crítica. Asegúrese de que el tráfico de gestión tenga prioridad QoS en el circuito WAN. Si el establecimiento comparte una conexión a internet tanto para el tráfico de huéspedes como para la gestión, un enlace saturado durante las horas pico puede hacer que los APs aparezcan desconectados en el panel de la nube.
- Actualizaciones de Firmware por Etapas: Las plataformas en la nube a menudo envían actualizaciones de firmware automáticamente. Si bien esto asegura que los parches de seguridad se apliquen rápidamente, introduce el riesgo de errores inesperados. Configure su panel en la nube para realizar actualizaciones por etapas, probando el nuevo firmware en un pequeño subconjunto de APs (por ejemplo, la oficina de TI) antes de implementarlo en toda la infraestructura.
- Diseñar para la Densidad, No Solo para la Cobertura: Las implementaciones modernas rara vez fallan por falta de señal; fallan por agotamiento de capacidad o interferencia de co-canal. Realice encuestas de RF predictivas y activas adecuadas, asegurando una superposición de canales y configuraciones de potencia de transmisión apropiadas, particularmente en zonas de alta densidad como vestíbulos o salas de conferencias. Para obtener información sobre cómo mejorar la experiencia general, revise Cómo Mejorar la Satisfacción del Huésped: El Manual Definitivo .
- Estandarizar la Arquitectura VLAN: Implemente un esquema VLAN consistente en todos los sitios. Aísle las interfaces de gestión, los dispositivos corporativos, los sensores IoT y el tráfico de huéspedes.
ROI e Impacto Comercial
La decisión entre APs basados en controlador y gestionados en la nube debe basarse en un análisis del Costo Total de Propiedad (TCO) durante un ciclo de vida de 5 a 7 años.
- Gasto de Capital (CapEx): Los sistemas basados en controlador a menudo tienen un CapEx inicial más alto debido al costo de los dispositivos WLC y los requisitos de redundancia asociados. Los APs gestionados en la nube suelen tener costos de hardware más bajos, pero requieren licencias de suscripción continuas.
- Gasto Operativo (OpEx): Los sistemas gestionados en la nube demuestran consistentemente un OpEx más bajo en implementaciones multisitio. Los ahorros generados por el Aprovisionamiento Sin Contacto (Zero-Touch Provisioning), la resolución de problemas centralizada y la gestión automatizada del firmware a menudo compensan los costos de licencia recurrentes.
- Agilidad Comercial: La capacidad de implementar nuevos sitios rápidamente, aplicar cambios de política en toda la red al instante e integrarse sin problemas con plataformas de análisis proporciona una ventaja comercial tangible, particularmente en sectores de rápido movimiento como el comercio minorista y la hostelería.
Al seleccionar la arquitectura que se alinee con sus capacidades operativas y topología de sitio, y al superponer una plataforma de inteligencia agnóstica al hardware como Purple, los equipos de TI empresariales pueden transformar su red WiFi de un centro de costos necesario en un activo estratégico que genera ingresos.
Definiciones clave
WLC (Wireless LAN Controller)
A centralised hardware or virtual appliance that manages configuration, RF coordination, and security policies for multiple 'lightweight' access points.
The core component of a controller-based architecture, representing both a powerful management tool and a potential single point of failure.
CAPWAP
Control and Provisioning of Wireless Access Points. A standard protocol (RFC 5415) used by WLCs to manage a collection of APs.
The tunnel through which controller-based APs receive instructions and often route client data traffic.
Zero-Touch Provisioning (ZTP)
The ability to deploy network hardware at a remote site without manual configuration; the device automatically connects to a cloud platform to download its profile.
The primary driver for operational expenditure (OpEx) savings in multi-site cloud-managed deployments.
Local Survivability
The ability of a cloud-managed AP to continue routing local traffic and authenticating users even if the WAN connection to the cloud dashboard is lost.
A critical evaluation metric for cloud platforms, ensuring that a WAN outage does not result in a complete LAN failure.
Out-of-Band Management
An architecture where management traffic (telemetry, configuration) is separated from user data traffic.
The foundational security principle of cloud-managed APs, ensuring user data remains on the local network.
802.11r (Fast BSS Transition)
An IEEE standard that permits continuous connectivity aboard wireless devices in motion, with fast and secure handoffs from one AP to another.
Crucial for seamless roaming in high-density environments; historically handled better by centralised controllers.
Data Sovereignty
The concept that digital data is subject to the laws of the country in which it is located.
A key consideration when evaluating cloud-managed platforms to ensure compliance with regulations like GDPR.
Air-Gapped Network
A network security measure employed to ensure that a secure computer network is physically isolated from unsecured networks, such as the public Internet.
Environments requiring true air-gapping mandate the use of on-premises controller-based architectures.
Ejemplos resueltos
A national retail chain is deploying guest WiFi across 300 mid-sized stores. They have a lean central IT team of four engineers and no on-site technical staff. They require analytics to track dwell time and footfall.
Deploy cloud-managed APs across all locations. Utilise Zero-Touch Provisioning (ZTP) to ship APs directly to store managers, who simply plug them into the PoE switch. Configure the cloud dashboard to push a standardised SSIDs and VLAN configuration. Integrate the cloud controller with Purple via API/RADIUS for captive portal and analytics.
A newly constructed 60,000-seat sports stadium requires pervasive WiFi for fan engagement, ticketing, and POS systems. The environment will experience massive, simultaneous client onboarding and requires seamless roaming as crowds move through concourses.
Deploy a controller-based architecture with redundant high-availability WLC appliances in the on-site data centre. Utilise high-density directional antennas. Configure the WLC for aggressive load balancing, band steering, and 802.11r Fast BSS Transition.
Preguntas de práctica
Q1. A boutique hotel chain is upgrading its WiFi across 15 properties. The IT Director wants to move to cloud-managed APs but the Compliance Officer is concerned about PCI DSS compliance for the point-of-sale (POS) terminals in the restaurants. What is the correct architectural approach?
Sugerencia: Consider how data plane traffic is handled in cloud-managed deployments and the requirements of network segmentation.
Ver respuesta modelo
Cloud-managed APs are fully suitable, provided proper network segmentation is implemented. The IT team must configure separate VLANs for guest WiFi and the POS network. Because cloud-managed APs utilise out-of-band management, the POS data traffic will break out locally and will not traverse the vendor's cloud, satisfying PCI DSS requirements for the data plane. The vendor's cloud platform must hold appropriate security attestations (e.g., SOC 2) for the management plane.
Q2. During a peak trading event, the primary WAN link at a retail store fails. The store falls back to a low-bandwidth 4G connection. The cloud-managed APs remain online, but the IT team reports they cannot push configuration changes to the store via the dashboard. Why is this happening, and how should the network have been designed to prevent it?
Sugerencia: Consider the relationship between management traffic, data traffic, and QoS on constrained links.
Ver respuesta modelo
The APs are operating in 'local survivability' mode. The low-bandwidth 4G connection is likely saturated by essential POS or guest traffic, causing the management tunnels (HTTPS/TLS) to the cloud controller to drop or time out. To prevent this, the network architect should have implemented Quality of Service (QoS) rules on the edge router/firewall to guarantee a minimum bandwidth allocation and prioritise the AP management traffic over the failover link.
Q3. A university campus with an existing controller-based architecture wants to deploy Purple for guest analytics. The network team states they cannot integrate because they do not use cloud-managed APs. Is this correct?
Sugerencia: Consider Purple's integration methodology and hardware dependencies.
Ver respuesta modelo
No, this is incorrect. Purple is hardware-agnostic and does not require a cloud-managed architecture. The university's existing Wireless LAN Controllers (WLCs) can be configured to integrate with Purple using standard RADIUS authentication and accounting protocols, redirecting guest traffic to the Purple captive portal. The analytics data will be generated identically to a cloud-managed deployment.