Confronto tra Access Point basati su controller e gestiti tramite cloud
Questa guida tecnica di riferimento confronta le architetture di Access Point basate su controller e gestite tramite cloud per ambienti aziendali. Fornisce ai leader IT un framework neutrale rispetto al fornitore per la valutazione dei modelli di implementazione, del costo totale di proprietà e delle capacità di integrazione con piattaforme di guest intelligence come Purple.
Ascolta questa guida
Visualizza trascrizione del podcast
- Sintesi Esecutiva
- Approfondimento Tecnico: Architettura e Piani di Controllo
- Architettura basata su Controller
- Architettura gestita tramite Cloud
- Implicazioni per la Sicurezza e la Conformità
- Guida all'Implementazione: Distribuzione e Integrazione
- Provisioning Zero-Touch vs. Distribuzione a Fasi
- Integrazione di Guest Intelligence e Analytics
- Best Practice e Mitigazione del Rischio
- ROI e Impatto sul Business

Sintesi Esecutiva
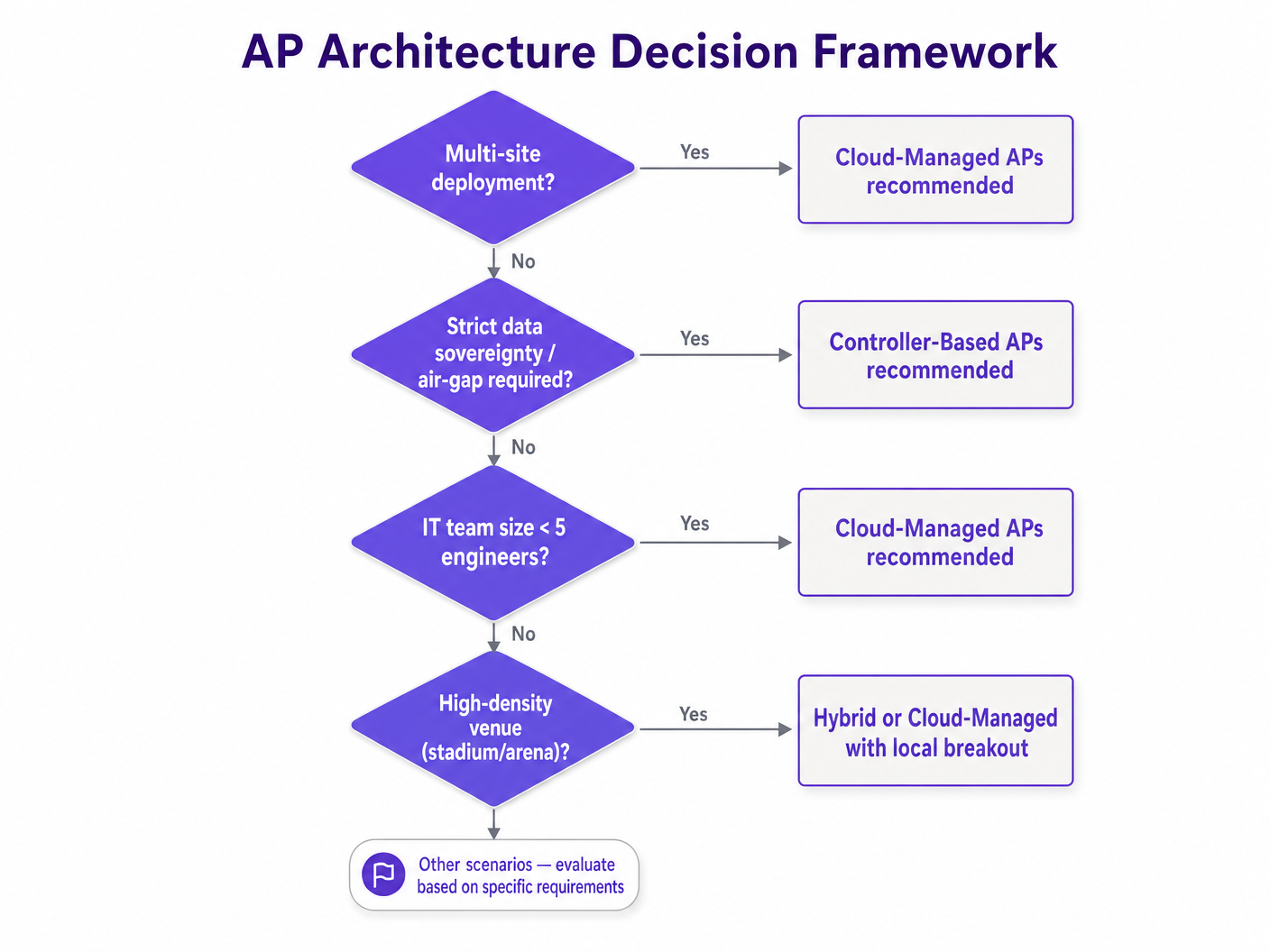
Per gli operatori di sedi aziendali, la decisione architetturale tra Access Point (APs) basati su controller e gestiti tramite cloud definisce l'agilità operativa, la postura di sicurezza e il costo totale di proprietà (TCO) della loro rete per i prossimi cinque-sette anni. Poiché le sedi nei settori Hospitality , Retail e Transport digitalizzano i loro spazi fisici, il WiFi non è più semplicemente un servizio; è lo strato di trasporto critico per sensori IoT, sistemi Point-of-Sale (POS) e piattaforme di guest intelligence.
Storicamente, le esigenze di alta densità di stadi e grandi centri congressi richiedevano Wireless LAN Controllers (WLCs) on-premises per gestire la complessa coordinazione RF e il roaming senza interruzioni. Tuttavia, le moderne architetture gestite tramite cloud, potenziate dalla gestione delle risorse radio (RRM) basata su AI, hanno ridotto significativamente questo divario di prestazioni, eliminando al contempo l'overhead operativo della gestione degli apparati controller fisici.
Questa guida tecnica di riferimento fornisce ad architetti di rete e direttori IT un framework neutrale rispetto al fornitore per la valutazione delle architetture AP. Dettaglia le distinzioni tecniche nella gestione del piano di controllo, esamina scenari di implementazione reali e delinea come queste architetture si integrano con le piattaforme aziendali di Guest WiFi e WiFi Analytics per generare risultati di business misurabili.
Approfondimento Tecnico: Architettura e Piani di Controllo
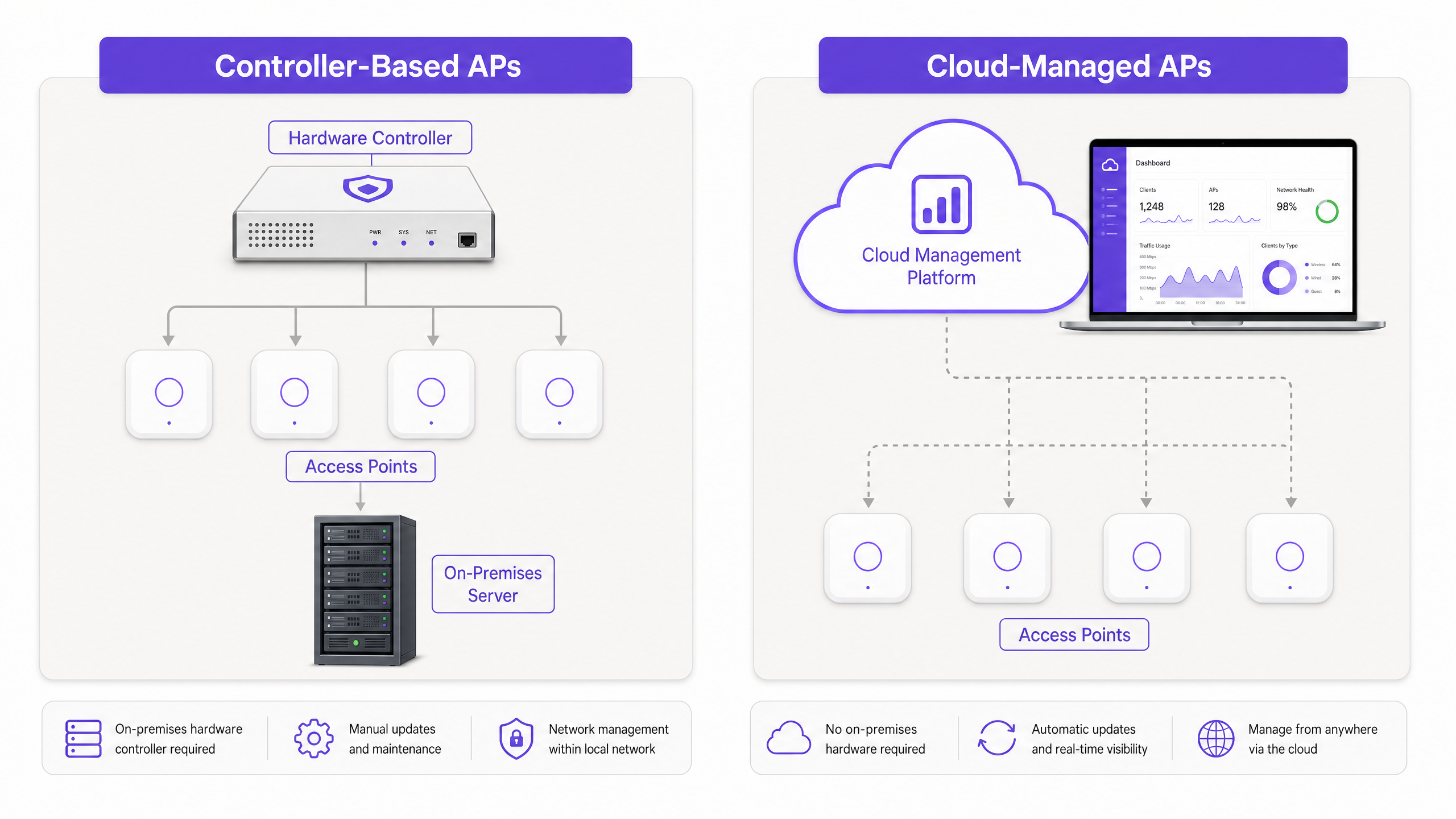
La distinzione fondamentale tra AP basati su controller e gestiti tramite cloud risiede nel luogo in cui risiedono i piani di gestione e controllo e nel modo in cui gli AP interagiscono con il resto dell'infrastruttura di rete.
Architettura basata su Controller
In un modello tradizionale basato su controller, gli AP "leggeri" terminano la loro gestione e spesso il loro traffico dati su un apparato hardware o virtuale centralizzato: il Wireless LAN Controller (WLC). Gli AP gestiscono le funzioni fisiche di radiofrequenza (RF) di Livello 1 e Livello 2, ma l'intelligenza è centralizzata.
- Dipendenza dal Protocollo: Gli AP comunicano con il WLC utilizzando il protocollo Control and Provisioning of Wireless Access Points (CAPWAP) (RFC 5415).
- Elaborazione Centralizzata: Le decisioni di roaming, gli handshake di autenticazione (come 802.1X/EAP) e le assegnazioni dinamiche dei canali RF sono elaborate dal controller.
- Tunneling del Piano Dati: In molte implementazioni, il traffico dati del client viene incanalato (tunnelled) verso il WLC prima di essere instradato sulla rete cablata. Ciò consente l'applicazione centralizzata delle policy e una gestione VLAN semplificata in un grande campus, ma crea un potenziale collo di bottiglia.
Vantaggi per Ambienti ad Alta Densità: I sistemi basati su controller eccellono in ambienti ad altissima densità (ad esempio, stadi, grandi auditorium). Poiché il WLC ha una visione olistica in tempo reale dell'ambiente RF su centinaia di AP, può coordinare la mitigazione delle interferenze co-canale e gestire il roaming 802.11r Fast BSS Transition (FT) con precisione al millisecondo.
Architettura gestita tramite Cloud
Le architetture gestite tramite cloud decentralizzano il piano di controllo. Gli AP stessi sono "fat" o autonomi in termini di gestione RF locale e inoltro dati, ma sono orchestrati centralmente tramite una piattaforma di gestione ospitata nel cloud.
- Gestione Out-of-Band: L'AP stabilisce un tunnel di gestione sicuro (tipicamente HTTPS/TLS) verso il cloud del fornitore. La configurazione, la telemetria e gli aggiornamenti del firmware fluiscono attraverso questa connessione.
- Local Breakout: Il traffico dati del client non viene incanalato verso il cloud. Viene instradato localmente sulla porta dello switch a cui è collegato l'AP.
- Sopravvivenza Locale: Se la connessione internet al cloud si interrompe, l'AP continua a servire i client esistenti, autentica i nuovi client (se viene utilizzato RADIUS locale o PSK) e instrada il traffico. Tuttavia, il team IT perde la visibilità in tempo reale e la capacità di inviare modifiche alla configurazione fino al ripristino della connessione.
Implicazioni per la Sicurezza e la Conformità
Entrambe le architetture supportano standard di sicurezza di livello enterprise, inclusi WPA3-Enterprise, autenticazione 802.1X e rilevamento di AP non autorizzati. Tuttavia, l'onere di conformità differisce.
Con i sistemi gestiti tramite cloud, i team IT devono assicurarsi che la piattaforma cloud del fornitore soddisfi i requisiti normativi pertinenti (ad esempio, SOC 2 Type II, ISO 27001) e che la residenza dei dati sia conforme al GDPR o alle leggi locali sulla privacy. Per ambienti altamente sensibili che richiedono una rigorosa separazione fisica (air-gapping), come alcune strutture governative o di difesa, un sistema basato su controller che opera interamente all'interno della LAN locale rimane lo standard.
Per ambienti che gestiscono dati di pagamento, entrambe le architetture possono raggiungere la conformità PCI DSS. Tuttavia, la segmentazione della rete è fondamentale. La rete guest, i dispositivi aziendali e i terminali POS devono essere isolati su VLAN separate, indipendentemente dall'architettura AP.
Guida all'Implementazione: Distribuzione e Integrazione
L'impatto operativo dell'architettura scelta diventa più evidente durante la distribuzione e la gestione continua, in particolare negli scenari multi-sito.
Provisioning Zero-Touch vs. Distribuzione a Fasi
Gestito tramite Cloud: Il principale vantaggio operativo degli AP gestiti tramite cloud è il Zero-Touch Provisioning (ZTP). Un AP può essere spedito direttamente a un negozio al dettaglio o a un hotel remoto. Una volta collegato, acquisisce un indirizzo IP via DHCP, si connette al cloud, scarica il suo profilo pre-configurato e inizia a trasmettere. Questo elimina la necessità di costosi "interventi in loco" o di dispiegare ingegneri di rete altamente qualificati in siti remoti.
Basati su Controller: Il deployment di AP basati su controller richiede tipicamente più preparazione. L'AP deve essere in grado di scoprire il WLC (spesso tramite DHCP Option 43 o risoluzione DNS). Il firmware deve spesso essere allineato manualmente tra il WLC e gli AP. Per un rollout multi-sito, questo richiede spesso la preparazione centralizzata dell'hardware prima della spedizione, o il dispiegamento di ingegneri in ogni sito.
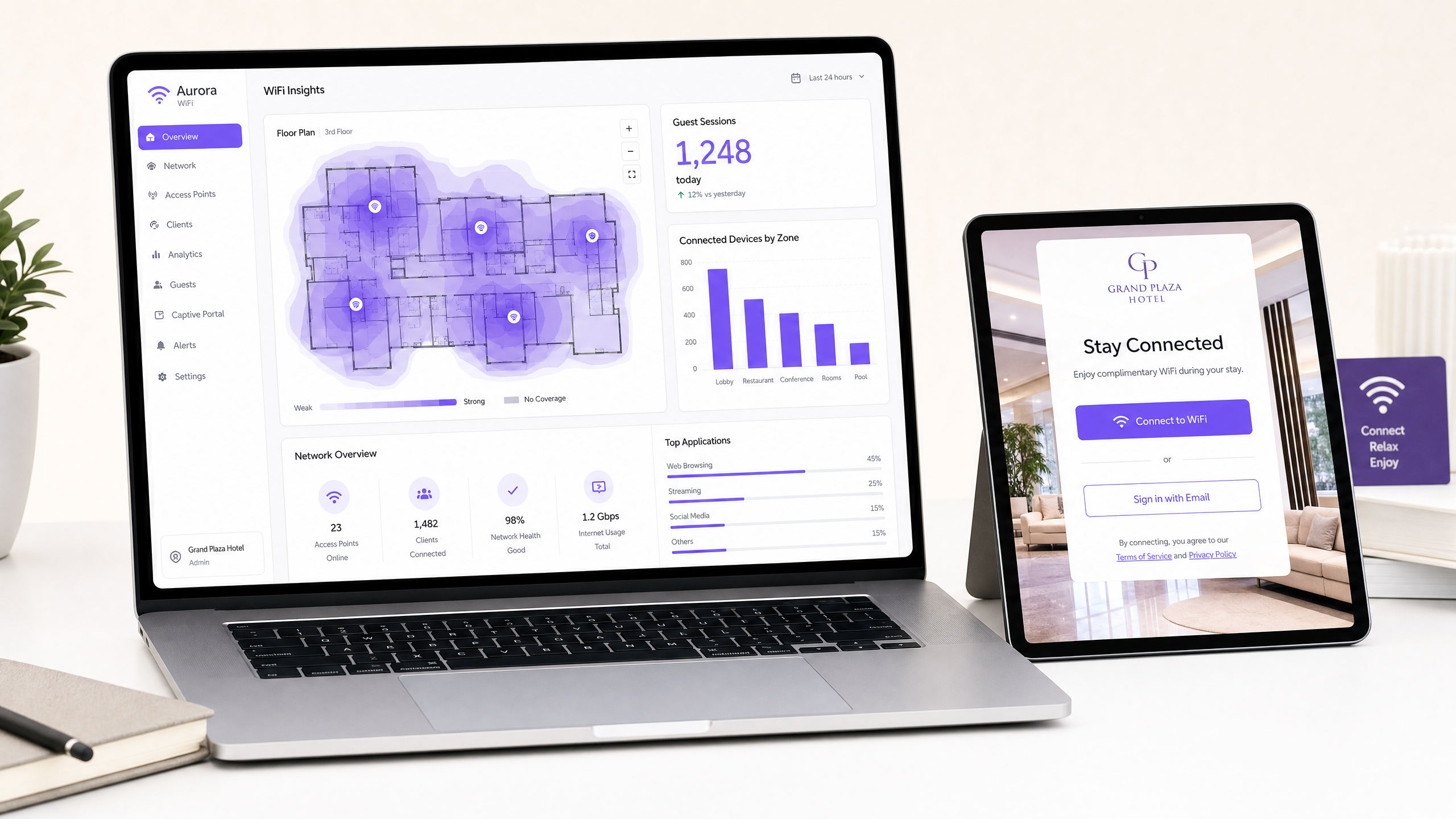
Integrazione di Guest Intelligence e Analytics
Il deployment degli AP fisici è solo la base. Per estrarre valore aziendale dalla rete, le strutture devono integrare il loro hardware con piattaforme di guest intelligence come Purple.
Purple opera come un overlay hardware-agnostic, integrandosi perfettamente con sistemi basati su controller e cloud-managed dei principali fornitori (Cisco, Meraki, Aruba, Ruckus, Extreme).
- Autenticazione e Onboarding: Purple gestisce la presentazione del Captive Portal e l'autenticazione (tramite social login, compilazione di moduli o How a wi fi assistant Enables Passwordless Access in 2026 ). L'architettura dell'AP deve semplicemente supportare l'autenticazione e la contabilità RADIUS, reindirizzando gli utenti non autenticati al portal Purple.
- Dati di Analytics: Purple acquisisce dati di presenza e posizione dagli AP per alimentare la sua dashboard di analytics. Sia che i dati vengano inviati via API da una dashboard cloud o direttamente da un WLC locale, le intuizioni risultanti—tempi di permanenza, tassi di ritorno e affluenza—sono identiche. Per un'analisi più approfondita su come vengono generati questi dati, consulta la nostra guida su Heatmapping vs Presence Analytics: Technical Differences .
Best Practice e Mitigazione del Rischio
Indipendentemente dall'architettura selezionata, alcune best practice fondamentali mitigano i rischi di deployment e garantiscono stabilità a lungo termine.
- Prioritizzare il Traffico di Gestione: Per i deployment cloud-managed, la connessione degli AP al cloud è critica. Assicurarsi che il traffico di gestione sia prioritizzato QoS sul circuito WAN. Se la struttura condivide una connessione internet sia per il traffico guest che per la gestione, un link saturo durante le ore di punta può far sì che gli AP appaiano offline alla dashboard cloud.
- Aggiornamenti Firmware a Fasi: Le piattaforme cloud spesso inviano aggiornamenti firmware automaticamente. Sebbene ciò garantisca che le patch di sicurezza vengano applicate tempestivamente, introduce il rischio di bug imprevisti. Configura la tua dashboard cloud per eseguire aggiornamenti a fasi—testando il nuovo firmware su un piccolo sottoinsieme di AP (ad esempio, l'ufficio IT) prima di distribuirlo all'intera infrastruttura.
- Progettare per la Densità, Non Solo per la Copertura: I deployment moderni raramente falliscono per mancanza di segnale; falliscono a causa dell'esaurimento della capacità o dell'interferenza co-canale. Conduci indagini RF predittive e attive appropriate, assicurando una sovrapposizione di canali e impostazioni di potenza di trasmissione adeguate, in particolare in zone ad alta densità come hall o sale conferenze. Per approfondimenti su come migliorare l'esperienza complessiva, consulta How To Improve Guest Satisfaction: The Ultimate Playbook .
- Standardizzare l'Architettura VLAN: Implementa uno schema VLAN coerente su tutti i siti. Isola le interfacce di gestione, i dispositivi aziendali, i sensori IoT e il traffico guest.
ROI e Impatto sul Business
La decisione tra AP basati su controller e cloud-managed dovrebbe essere guidata da un'analisi del Costo Totale di Proprietà (TCO) su un ciclo di vita di 5-7 anni.
- Spese in Conto Capitale (CapEx): I sistemi basati su controller spesso hanno un CapEx iniziale più elevato a causa del costo degli apparati WLC e dei requisiti di ridondanza associati. Gli AP cloud-managed hanno tipicamente costi hardware inferiori ma richiedono una licenza di abbonamento continua.
- Spese Operative (OpEx): I sistemi cloud-managed dimostrano costantemente un OpEx inferiore nei deployment multi-sito. I risparmi generati da Zero-Touch Provisioning, risoluzione dei problemi centralizzata e gestione automatizzata del firmware spesso compensano i costi di licenza ricorrenti.
- Agilità Aziendale: La capacità di implementare rapidamente nuovi siti, applicare istantaneamente modifiche alle policy di rete e integrarsi senza problemi con le piattaforme di analytics offre un vantaggio aziendale tangibile, in particolare in settori in rapida evoluzione come il retail e l'ospitalità.
Selezionando l'architettura che si allinea con le loro capacità operative e la topologia del sito, e sovrapponendo una piattaforma di intelligence hardware-agnostic come Purple, i team IT aziendali possono trasformare la loro rete WiFi da un centro di costo necessario a una risorsa strategica che genera entrate.
Definizioni chiave
WLC (Wireless LAN Controller)
A centralised hardware or virtual appliance that manages configuration, RF coordination, and security policies for multiple 'lightweight' access points.
The core component of a controller-based architecture, representing both a powerful management tool and a potential single point of failure.
CAPWAP
Control and Provisioning of Wireless Access Points. A standard protocol (RFC 5415) used by WLCs to manage a collection of APs.
The tunnel through which controller-based APs receive instructions and often route client data traffic.
Zero-Touch Provisioning (ZTP)
The ability to deploy network hardware at a remote site without manual configuration; the device automatically connects to a cloud platform to download its profile.
The primary driver for operational expenditure (OpEx) savings in multi-site cloud-managed deployments.
Local Survivability
The ability of a cloud-managed AP to continue routing local traffic and authenticating users even if the WAN connection to the cloud dashboard is lost.
A critical evaluation metric for cloud platforms, ensuring that a WAN outage does not result in a complete LAN failure.
Out-of-Band Management
An architecture where management traffic (telemetry, configuration) is separated from user data traffic.
The foundational security principle of cloud-managed APs, ensuring user data remains on the local network.
802.11r (Fast BSS Transition)
An IEEE standard that permits continuous connectivity aboard wireless devices in motion, with fast and secure handoffs from one AP to another.
Crucial for seamless roaming in high-density environments; historically handled better by centralised controllers.
Data Sovereignty
The concept that digital data is subject to the laws of the country in which it is located.
A key consideration when evaluating cloud-managed platforms to ensure compliance with regulations like GDPR.
Air-Gapped Network
A network security measure employed to ensure that a secure computer network is physically isolated from unsecured networks, such as the public Internet.
Environments requiring true air-gapping mandate the use of on-premises controller-based architectures.
Esempi pratici
A national retail chain is deploying guest WiFi across 300 mid-sized stores. They have a lean central IT team of four engineers and no on-site technical staff. They require analytics to track dwell time and footfall.
Deploy cloud-managed APs across all locations. Utilise Zero-Touch Provisioning (ZTP) to ship APs directly to store managers, who simply plug them into the PoE switch. Configure the cloud dashboard to push a standardised SSIDs and VLAN configuration. Integrate the cloud controller with Purple via API/RADIUS for captive portal and analytics.
A newly constructed 60,000-seat sports stadium requires pervasive WiFi for fan engagement, ticketing, and POS systems. The environment will experience massive, simultaneous client onboarding and requires seamless roaming as crowds move through concourses.
Deploy a controller-based architecture with redundant high-availability WLC appliances in the on-site data centre. Utilise high-density directional antennas. Configure the WLC for aggressive load balancing, band steering, and 802.11r Fast BSS Transition.
Domande di esercitazione
Q1. A boutique hotel chain is upgrading its WiFi across 15 properties. The IT Director wants to move to cloud-managed APs but the Compliance Officer is concerned about PCI DSS compliance for the point-of-sale (POS) terminals in the restaurants. What is the correct architectural approach?
Suggerimento: Consider how data plane traffic is handled in cloud-managed deployments and the requirements of network segmentation.
Visualizza risposta modello
Cloud-managed APs are fully suitable, provided proper network segmentation is implemented. The IT team must configure separate VLANs for guest WiFi and the POS network. Because cloud-managed APs utilise out-of-band management, the POS data traffic will break out locally and will not traverse the vendor's cloud, satisfying PCI DSS requirements for the data plane. The vendor's cloud platform must hold appropriate security attestations (e.g., SOC 2) for the management plane.
Q2. During a peak trading event, the primary WAN link at a retail store fails. The store falls back to a low-bandwidth 4G connection. The cloud-managed APs remain online, but the IT team reports they cannot push configuration changes to the store via the dashboard. Why is this happening, and how should the network have been designed to prevent it?
Suggerimento: Consider the relationship between management traffic, data traffic, and QoS on constrained links.
Visualizza risposta modello
The APs are operating in 'local survivability' mode. The low-bandwidth 4G connection is likely saturated by essential POS or guest traffic, causing the management tunnels (HTTPS/TLS) to the cloud controller to drop or time out. To prevent this, the network architect should have implemented Quality of Service (QoS) rules on the edge router/firewall to guarantee a minimum bandwidth allocation and prioritise the AP management traffic over the failover link.
Q3. A university campus with an existing controller-based architecture wants to deploy Purple for guest analytics. The network team states they cannot integrate because they do not use cloud-managed APs. Is this correct?
Suggerimento: Consider Purple's integration methodology and hardware dependencies.
Visualizza risposta modello
No, this is incorrect. Purple is hardware-agnostic and does not require a cloud-managed architecture. The university's existing Wireless LAN Controllers (WLCs) can be configured to integrate with Purple using standard RADIUS authentication and accounting protocols, redirecting guest traffic to the Purple captive portal. The analytics data will be generated identically to a cloud-managed deployment.