eduroam y 802.1X: Autenticación WiFi Segura para la Educación Superior
Esta guía de referencia técnica autorizada explica la arquitectura, el despliegue y la seguridad de la autenticación eduroam y 802.1X. Diseñada para gerentes de TI y arquitectos de red, cubre pasos prácticos de implementación, selección de métodos EAP y cómo los operadores de recintos pueden soportar de forma segura el roaming académico.
GuidesSlugPage.podcastTitle
GuidesSlugPage.podcastTranscript
- Resumen Ejecutivo
- Análisis Técnico Detallado: 802.1X y la Arquitectura de eduroam
- El Triángulo 802.1X
- La Jerarquía de Proxy RADIUS de eduroam
- Métodos EAP: Seguridad vs. Desplegabilidad
- Guía de Implementación
- 1. Preparación de la Infraestructura
- 2. Gestión de Certificados
- 3. Configuración del Cliente (La Herramienta CAT)
- 4. Asignación y Segmentación de VLAN
- Mejores Prácticas y Recomendaciones Neutrales al Proveedor
- Solución de Problemas y Mitigación de Riesgos
- ROI e Impacto Comercial

Resumen Ejecutivo
Para las instituciones de educación superior y los recintos que acogen a sus estudiantes y personal, proporcionar conectividad inalámbrica segura y sin interrupciones ya no es un lujo, es un mandato operativo. El estándar para esta conectividad es eduroam, un servicio global de roaming construido sobre el marco IEEE 802.1X.
Esta guía proporciona a los gerentes de TI, arquitectos de red y directores de operaciones de recintos una referencia completa y neutral en cuanto a proveedores para comprender, desplegar y solucionar problemas de 802.1X y eduroam. Vamos más allá de los modelos teóricos básicos para abordar las realidades prácticas del WiFi de campus empresarial, incluyendo la gestión de certificados, la arquitectura de proxy RADIUS y la integración con estrategias más amplias de red de invitados.
Ya sea que esté actualizando una red universitaria antigua o configurando un centro de conferencias para apoyar a visitantes académicos, implementar 802.1X correctamente mitiga riesgos de seguridad significativos —particularmente el robo de credenciales— mientras reduce drásticamente los gastos generales de soporte. Para los recintos fuera de la educación superior tradicional, comprender estos estándares es fundamental para evaluar federaciones comerciales de roaming como OpenRoaming, que comparten la misma arquitectura subyacente.
Análisis Técnico Detallado: 802.1X y la Arquitectura de eduroam
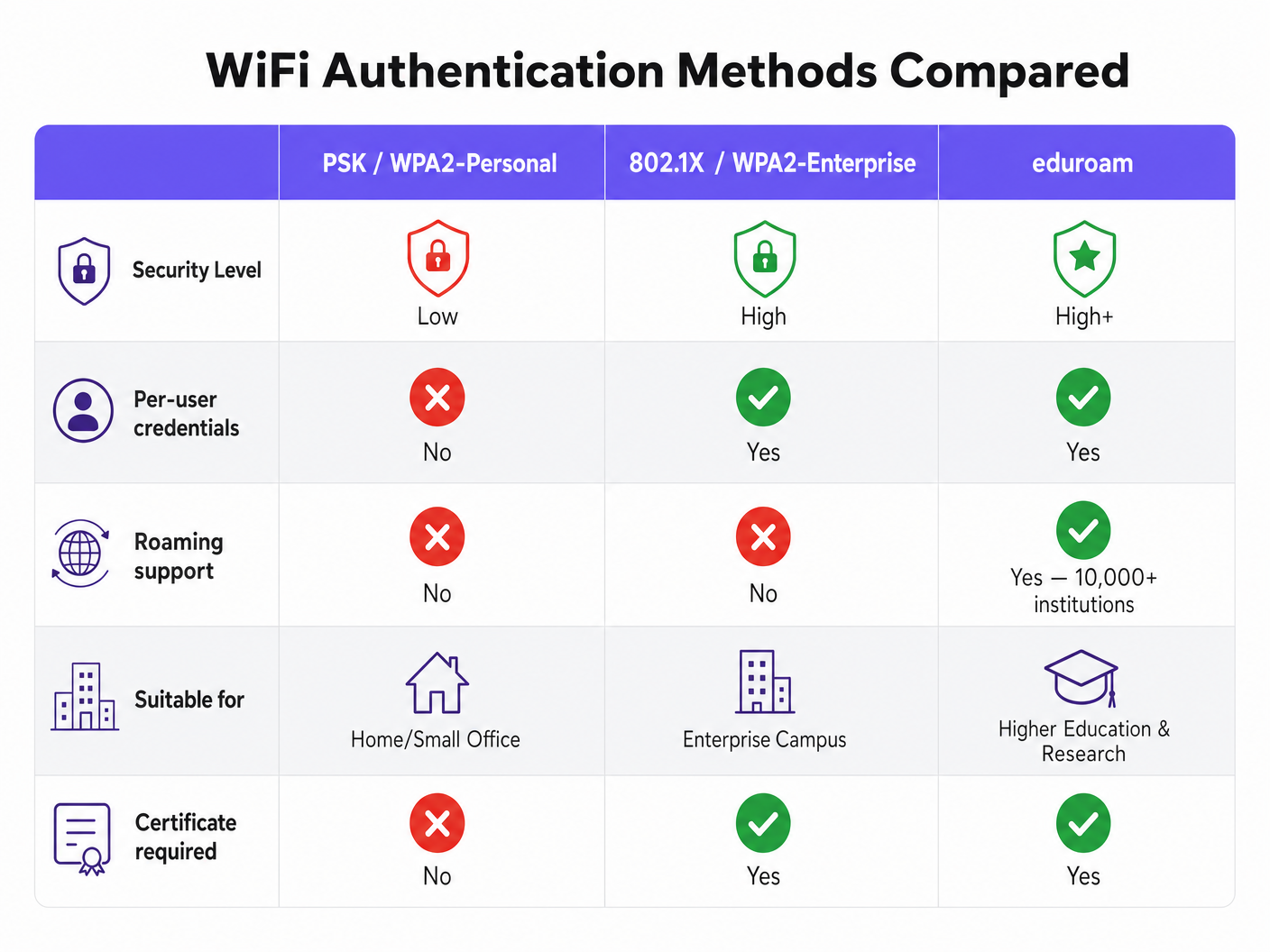
En su esencia, eduroam es una implementación de IEEE 802.1X, el estándar para el control de acceso a la red basado en puertos. Aunque originalmente diseñado para redes cableadas, 802.1X constituye la base de la seguridad WPA2-Enterprise y WPA3-Enterprise.
El Triángulo 802.1X
El marco 802.1X se basa en tres componentes distintos que interactúan para autorizar el acceso:
- Solicitante: El dispositivo cliente (por ejemplo, el portátil o smartphone de un estudiante) que solicita acceso a la red.
- Autenticador: El dispositivo de acceso a la red (por ejemplo, un punto de acceso inalámbrico o un switch gestionado). Actúa como un guardián, bloqueando todo el tráfico excepto los mensajes de autenticación hasta que el dispositivo es autorizado.
- Servidor de Autenticación: El sistema de backend que valida las credenciales, casi universalmente un servidor RADIUS (Remote Authentication Dial-In User Service).
Cuando un dispositivo se conecta, el Autenticador establece un puerto controlado. Pasa mensajes del Protocolo de Autenticación Extensible (EAP) entre el Solicitante y el Servidor de Autenticación. Si las credenciales son válidas, el servidor devuelve un mensaje RADIUS Access-Accept, y el Autenticador abre el puerto para el tráfico IP estándar.
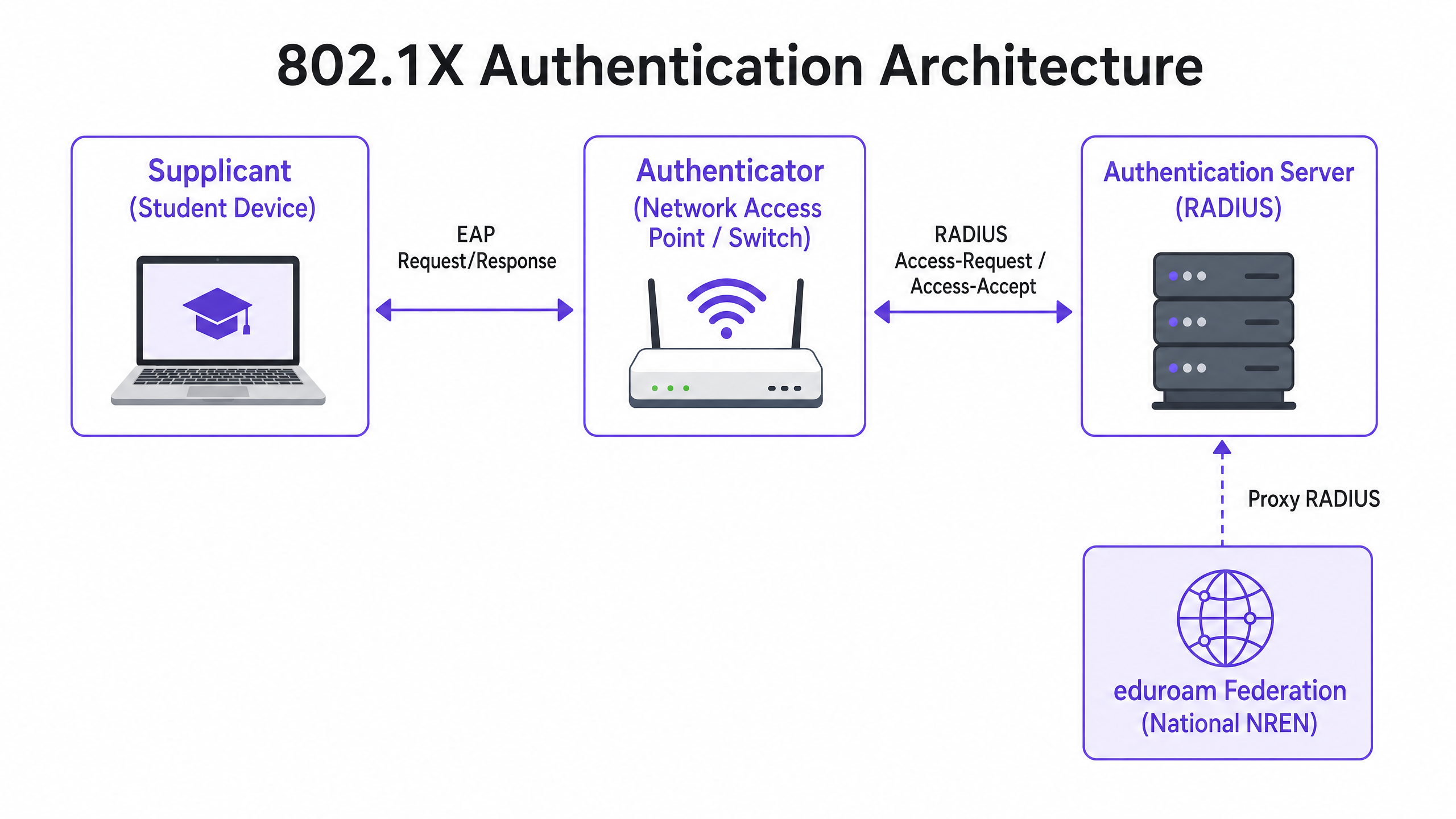
La Jerarquía de Proxy RADIUS de eduroam
Lo que hace único a eduroam es su arquitectura federada. Permite a los usuarios autenticarse en cualquier institución participante utilizando sus credenciales de origen, sin que la institución anfitriona necesite una copia de esas credenciales.
Esto se logra a través de una cadena jerárquica de proxy RADIUS. Cuando un usuario de username@university.ac.uk se conecta al SSID de eduroam en un recinto anfitrión:
- El dispositivo del usuario envía una solicitud de autenticación en el formato
username@university.ac.uk. - El servidor RADIUS del recinto anfitrión examina el reino (la porción después del
@). Reconociéndolo como un dominio externo, reenvía la solicitud al servidor RADIUS nacional de nivel superior (operado por la Red Nacional de Investigación y Educación, o NREN). - El servidor nacional enruta la solicitud al servidor RADIUS de la institución de origen (
university.ac.uk). - La institución de origen valida las credenciales y devuelve un mensaje
Access-AcceptoAccess-Rejecta lo largo de la cadena.
Todo este proceso se completa típicamente en menos de dos segundos. Fundamentalmente, la contraseña del usuario nunca se expone a la institución anfitriona ni a los proxies intermedios; está protegida dentro de un túnel EAP cifrado establecido directamente entre el solicitante y el servidor RADIUS de origen.
Métodos EAP: Seguridad vs. Desplegabilidad
La elección del método EAP dicta cómo se forma el túnel cifrado y cómo se intercambian las credenciales. La Definición del Servicio de Política de eduroam restringe fuertemente los métodos permitidos para garantizar la seguridad.
- PEAP (Protected EAP): El despliegue más común. Establece un túnel TLS utilizando un certificado del lado del servidor en el servidor RADIUS. El cliente luego se autentica dentro de este túnel, típicamente usando MSCHAPv2 (nombre de usuario y contraseña). Es relativamente fácil de desplegar pero vulnerable a ataques de puntos de acceso no autorizados si los clientes no están configurados para validar estrictamente el certificado del servidor.
- EAP-TLS: El estándar de oro para la seguridad. Requiere autenticación mutua, lo que significa que tanto el servidor RADIUS como el dispositivo cliente deben presentar certificados válidos. Aunque es inmune al phishing de credenciales, requiere una infraestructura de clave pública (PKI) robusta para emitir y gestionar certificados de cliente, lo que lo hace más complejo de desplegar a escala.
Guía de Implementación
El despliegue de 802.1X y eduroam requiere una cuidadosa coordinación entre la infraestructura de red, la gestión de identidades y la configuración del cliente.
1. Preparación de la Infraestructura
Asegúrese de que sus puntos de acceso inalámbricos y controladores soporten WPA2-Enterprise/WPA3-Enterprise y 802.1X. Cualquier hardware moderno de grado empresarial (Cisco, Aruba, Juniper, etc.) cumplirá con este requisito. También debe desplegar una infraestructura RADIUS robusta (por ejemplo, FreeRADIUS, Cisco ISE, Aruba ClearPass) capaz de manejar la carga de autenticación esperada y las solicitudes de proxy.
2. Gestión de Certificados
Para despliegues PEAP, su servidor RADIUS requiere un certificado TLS emitido por una Autoridad de Certificación (CA) de confianza para sus clientes. No utilicecertificados autofirmados para implementaciones de eduroam en producción. El certificado debe renovarse regularmente para evitar interrupciones en la autenticación.
3. Configuración del Cliente (La Herramienta CAT)
El punto de falla más común en las implementaciones de eduroam es la mala configuración del cliente. Los usuarios que se conectan manualmente a menudo no configuran la validación del certificado, lo que los deja vulnerables a la recolección de credenciales.
Para mitigar esto, las instituciones deben usar la Herramienta de Asistencia de Configuración de eduroam (CAT) o una solución MDM para distribuir perfiles preconfigurados. Estos perfiles configuran automáticamente el método EAP correcto, fijan el certificado del servidor RADIUS esperado y establecen los protocolos de autenticación internos apropiados.
4. Asignación y Segmentación de VLAN
Una implementación madura utiliza atributos RADIUS para asignar dinámicamente VLANs basándose en la identidad del usuario.
- Usuarios Locales: Asignados a VLANs internas con acceso apropiado a los recursos del campus.
- Usuarios Visitantes: Asignados a una VLAN de invitados restringida con acceso solo a internet.
Esta segmentación es vital para la seguridad y el cumplimiento, asegurando que los dispositivos visitantes no puedan acceder a redes internas sensibles.
Mejores Prácticas y Recomendaciones Neutrales al Proveedor
- Priorice WPA3: Para nuevas implementaciones, habilite WPA3-Enterprise para beneficiarse del cifrado obligatorio de 192 bits y una protección mejorada contra ataques de diccionario fuera de línea.
- Aplique la Validación de Certificados: Exija el uso de perfiles de configuración (a través de CAT o MDM) para asegurar que los solicitantes validen estrictamente el certificado del servidor RADIUS antes de transmitir las credenciales.
- Use RadSec: Al configurar conexiones de proxy RADIUS a la federación nacional, use RadSec (RADIUS over TLS) en lugar de UDP simple. Esto cifra el tráfico del proxy y mejora la fiabilidad en los enlaces WAN.
- Integre con Soluciones para Invitados: eduroam solo atiende a usuarios con credenciales académicas. Debe mantener una solución Guest WiFi separada y segura para contratistas, visitantes públicos y asistentes a eventos.
- Revise la Infraestructura Relacionada: Asegúrese de que su red subyacente sea segura. Lea nuestra guía Proteja su Red con DNS y Seguridad Robustos para más detalles. Si va a implementar infraestructura temporal para eventos universitarios, consulte Event WiFi: Planificación e Implementación de Redes Inalámbricas Temporales o la versión en portugués Event WiFi: Planeamento e Implementação de Redes Sem Fios Temporárias .
Solución de Problemas y Mitigación de Riesgos
Cuando la autenticación falla, la solución sistemática de problemas es esencial.
- Aísle el Dominio de Falla: Determine si la falla es local (afectando a sus propios usuarios en su propia red), remota (afectando a sus usuarios en otro lugar) o entrante (afectando a los visitantes en su red).
- Revise los Registros RADIUS: Los registros del servidor RADIUS son la fuente definitiva de la verdad. Busque mensajes de
Access-Reject(que indican credenciales incorrectas o violaciones de políticas) o tiempos de espera (que indican problemas de conectividad del proxy). - Verifique la Validez del Certificado: Asegúrese de que el certificado del servidor RADIUS no haya caducado y de que la cadena completa de certificados se presente al cliente.
- Monitoree la Latencia Ascendente: Una alta latencia en la conexión al proxy RADIUS nacional puede causar tiempos de espera en el cliente, lo que resulta en conexiones fallidas incluso con credenciales correctas.
ROI e Impacto Comercial
Para las instituciones de educación superior, el ROI de una implementación adecuada de eduroam se mide en una reducción drástica de los tickets de soporte. Al eliminar los captive portals y la entrada manual de contraseñas, los servicios de asistencia de TI observan una caída significativa en las llamadas relacionadas con la conectividad. (El compromiso de Purple con este sector es evidente; vea Purple Señala Ambiciones en Educación Superior con el Nombramiento del VP de Educación Tim Peers ).
Para los establecimientos comerciales —como los de Hostelería , Comercio Minorista , Salud o Transporte —, el soporte de eduroam Visitor Access (eVA) o federaciones similares como OpenRoaming proporciona una experiencia sin fricciones para datos demográficos de alto valor. Asegura que los visitantes académicos puedan conectarse de forma automática y segura, mejorando la satisfacción y permitiendo que el establecimiento mantenga una estricta segmentación de la red. Si su establecimiento requiere ancho de banda dedicado para soportar esto, considere leer ¿Qué es una Línea Dedicada? Internet Empresarial Dedicado .
Al planificar actualizaciones de red, la integración de capacidades 802.1X asegura que la infraestructura esté lista para redes modernas basadas en identidad, sentando las bases para WiFi Analytics avanzados y servicios basados en la ubicación.
GuidesSlugPage.keyDefinitionsTitle
802.1X
An IEEE standard for port-based Network Access Control (PNAC). It provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational protocol for enterprise-grade WiFi security, replacing shared passwords (PSKs) with individualised authentication.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised Authentication, Authorization, and Accounting (AAA) management for users who connect and use a network service.
The backend server in an 802.1X deployment that actually checks the user's credentials against a directory (like Active Directory).
EAP (Extensible Authentication Protocol)
An authentication framework frequently used in wireless networks and point-to-point connections. It provides for the transport and usage of various authentication mechanisms.
The language spoken between the client device and the RADIUS server during the 802.1X handshake.
Supplicant
The client device (e.g., laptop, smartphone) or the software on that device attempting to authenticate to a network using 802.1X.
The entity requesting access. Its configuration (especially regarding certificate validation) is critical for security.
Authenticator
The network device (e.g., wireless access point, Ethernet switch) that facilitates the 802.1X authentication process by passing messages between the Supplicant and the Authentication Server.
The gatekeeper that blocks network traffic until the RADIUS server gives the green light.
PEAP (Protected Extensible Authentication Protocol)
An EAP method that encapsulates the EAP transaction within a TLS tunnel established using a server-side certificate, protecting the inner authentication (usually a password).
The most common authentication method for eduroam, balancing security with ease of deployment.
RadSec
A protocol for transmitting RADIUS data over TCP and TLS, rather than the traditional UDP.
Recommended for securing the proxy connections between institutions and the national eduroam federation, preventing interception of authentication traffic.
Realm
The portion of a user's identity following the '@' symbol (e.g., 'university.ac.uk' in 'user@university.ac.uk').
Used by RADIUS proxy servers to determine where to route the authentication request in a federated environment like eduroam.
GuidesSlugPage.workedExamplesTitle
A 400-room conference hotel adjacent to a major university frequently hosts academic symposiums. The IT Director wants to allow visiting academics to connect automatically without using the hotel's standard captive portal, but must ensure these visitors cannot access the hotel's corporate network or the standard guest network VLAN.
The hotel should implement eduroam Visitor Access (eVA) or join a commercial federation like OpenRoaming.
- The hotel configures a new SSID ('eduroam' or 'OpenRoaming') on their enterprise access points.
- The APs are configured to use WPA2-Enterprise/802.1X.
- The hotel deploys a local RADIUS server configured to proxy authentication requests for external realms to the national federation (for eduroam) or the OpenRoaming hub.
- Crucially, the local RADIUS server is configured to return a specific VLAN ID attribute in the
Access-Acceptmessage for all proxied authentications. - The access points place these authenticated users onto an isolated, internet-only VLAN, completely segmented from the hotel's corporate and standard guest traffic.
A university IT team notices a spike in compromised student accounts. Investigation reveals that students are connecting to a rogue access point broadcasting the 'eduroam' SSID at a local coffee shop. The rogue AP is using a self-signed certificate to harvest credentials via PEAP.
The IT team must immediately enforce strict certificate validation on all client devices.
- They must stop advising students to manually connect to the SSID and 'accept the certificate warning'.
- They deploy the eduroam Configuration Assistant Tool (CAT) for BYOD devices and update MDM profiles for managed devices.
- These profiles configure the supplicant to only trust the specific Certificate Authority (CA) that issued the university's RADIUS server certificate, and to verify the server's Common Name (CN).
- Once configured, if a student's device encounters the rogue AP, the EAP tunnel establishment will fail because the rogue certificate does not match the pinned CA/CN, preventing the transmission of credentials.
A retail chain wants to offer OpenRoaming across 50 locations using their existing guest WiFi infrastructure, which currently relies on an open SSID with a captive portal.
The retail chain must upgrade their network to support 802.1X and RADIUS proxying.
- The network team enables a new SSID broadcasting the OpenRoaming Consortium OI (Organization Identifier).
- They configure the access points to authenticate via 802.1X.
- They configure their central RADIUS server to proxy requests to the OpenRoaming federation hub.
- They ensure their internet backhaul can support the expected increase in automated connections, potentially upgrading to dedicated leased lines if necessary.
GuidesSlugPage.practiceQuestionsTitle
Q1. Your university is deploying a new wireless network. The CISO mandates that credential phishing via rogue access points must be mathematically impossible. Which EAP method must you select?
GuidesSlugPage.hintPrefixConsider which method relies on passwords versus which relies entirely on cryptographic keys.
GuidesSlugPage.viewModelAnswer
You must select EAP-TLS. Unlike PEAP, which relies on a password inside a TLS tunnel, EAP-TLS requires mutual certificate authentication. Because the client device authenticates using a cryptographic certificate rather than a password, there are no credentials for a rogue access point to phish.
Q2. A visiting researcher from another university complains they cannot connect to your eduroam network. Your local users are connecting fine. You check your local RADIUS server logs and see the request arriving, but it times out before an Access-Accept is received. What is the most likely cause?
GuidesSlugPage.hintPrefixThink about the path the authentication request takes for a visiting user versus a local user.
GuidesSlugPage.viewModelAnswer
The most likely cause is a connectivity or latency issue between your local RADIUS server and the national NREN RADIUS proxy. Because local users authenticate directly against your server, they are unaffected. The visiting user's request must be proxied upstream, and a timeout indicates the response from the home institution is not returning in time.
Q3. You are a network architect for a retail chain located near a large university. You want to offer seamless WiFi to students using eduroam Visitor Access (eVA), but you must comply with PCI DSS for your point-of-sale terminals. How do you securely integrate eVA?
GuidesSlugPage.hintPrefixHow does 802.1X allow the network access point to differentiate traffic after authentication?
GuidesSlugPage.viewModelAnswer
You integrate eVA by configuring your RADIUS server to assign all successful eVA authentications to a dedicated, internet-only guest VLAN. The Access-Accept message from the RADIUS server must include the specific VLAN ID. This ensures student devices are completely segmented from the PCI-compliant VLAN used by the point-of-sale terminals, satisfying compliance requirements.



