¿Qué es la autenticación 802.1X? Cómo funciona y por qué es importante
Una guía de referencia técnica completa para gerentes de TI y arquitectos de red sobre la autenticación IEEE 802.1X. Esta guía cubre la arquitectura subyacente, las estrategias de implementación, los beneficios de seguridad sobre PSK y cómo implementar eficazmente el control de acceso de nivel empresarial junto con soluciones de guest WiFi.
🎧 Escucha esta guía
Ver transcripción
- Resumen Ejecutivo
- Análisis Técnico Detallado: Cómo Funciona 802.1X
- La Arquitectura de Tres Partes
- El Flujo de Autenticación
- Métodos EAP: Elegir el Protocolo Correcto
- Guía de Implementación
- Fase 1: Preparación de la Infraestructura
- Fase 2: Configuración del Solicitante
- Fase 3: Piloto y Despliegue
- Integración con el Acceso de Invitados
- Mejores Prácticas
- Solución de Problemas y Mitigación de Riesgos
- ROI e Impacto Empresarial
- Resumen de Audio

Resumen Ejecutivo
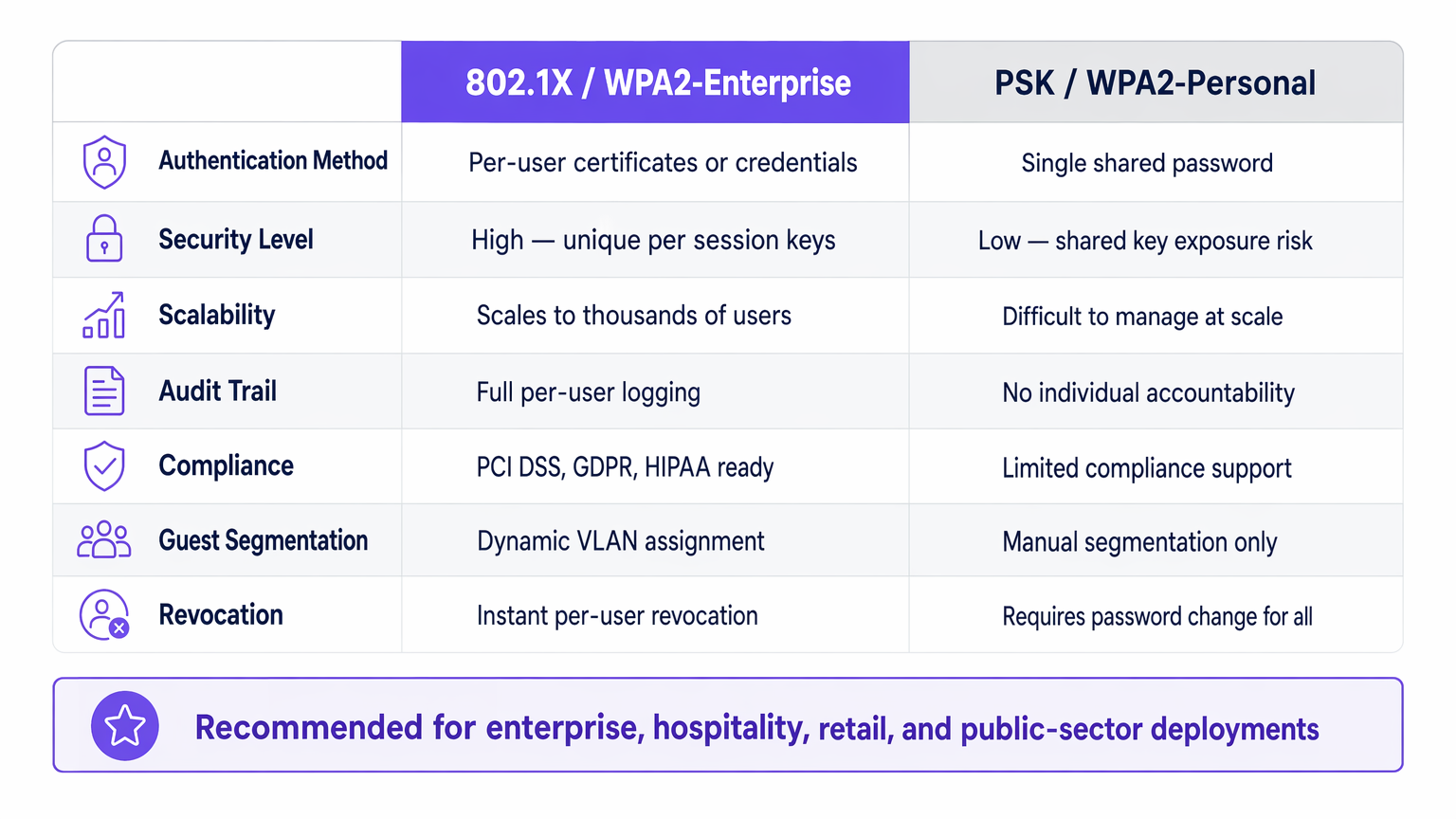
Para los líderes de TI empresariales que gestionan redes en entornos de Hospitalidad , Comercio Minorista , Salud o Transporte , asegurar el acceso a la red es un requisito fundamental. Confiar en Claves Precompartidas (PSK) para el acceso corporativo introduce riesgos inaceptables: falta de responsabilidad individual, procesos de revocación complejos y vulnerabilidades de cifrado compartido.
IEEE 802.1X es el marco estándar de la industria para el control de acceso a la red basado en puertos. Impone un proceso de autenticación riguroso antes de que un dispositivo pueda comunicarse en la red, lo que permite la verificación de identidad por usuario, la aplicación dinámica de políticas y el cumplimiento de marcos como PCI DSS y GDPR. Esta guía explora la mecánica de 802.1X, las diferencias entre los métodos EAP comunes y las estrategias prácticas de implementación para entornos empresariales, incluyendo cómo se integra con soluciones de Guest WiFi para proporcionar una estrategia de acceso holística.
Análisis Técnico Detallado: Cómo Funciona 802.1X
En su esencia, 802.1X opera sobre un modelo de tres partes diseñado para aislar los dispositivos no autenticados de la red interna.
La Arquitectura de Tres Partes
- Solicitante: El dispositivo del usuario final (laptop, smartphone, sensor IoT) que solicita acceso a la red. Debe ejecutar un cliente de software compatible con 802.1X.
- Autenticador: El dispositivo de red (punto de acceso inalámbrico o switch gestionado) que controla el puerto físico o lógico. Actúa como un guardián, bloqueando todo el tráfico excepto EAP (Extensible Authentication Protocol) hasta que la autenticación sea exitosa.
- Servidor de Autenticación: Típicamente un servidor RADIUS (Remote Authentication Dial-In User Service). Valida las credenciales del solicitante contra un almacén de identidades de backend (como Active Directory) y devuelve una decisión de política.
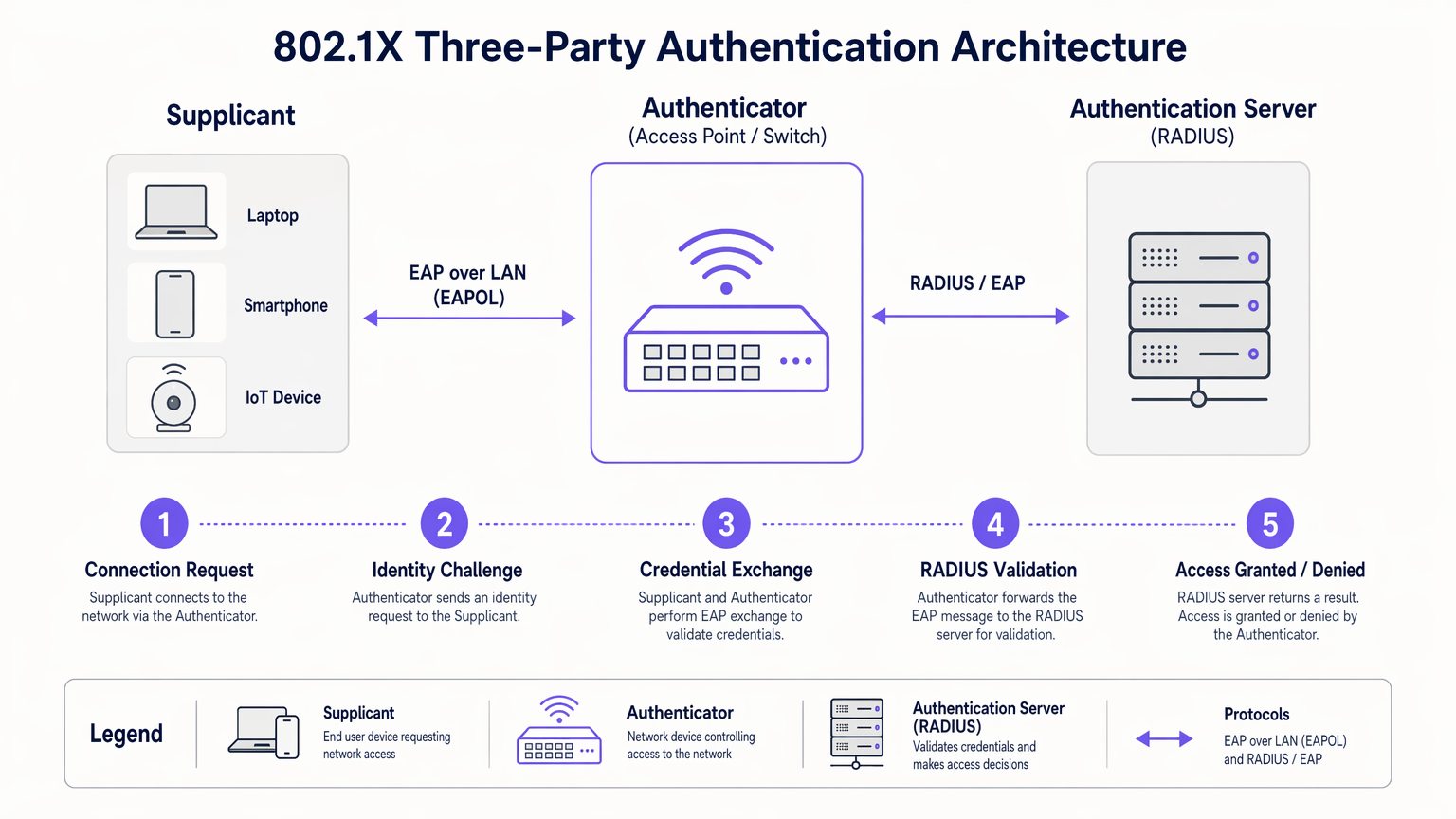
El Flujo de Autenticación
Cuando un solicitante se conecta a un puerto o SSID habilitado para 802.1X, el autenticador coloca el puerto en un estado no autorizado. El flujo procede de la siguiente manera:
- Inicio EAPOL: El solicitante envía una trama EAP over LAN (EAPOL) Start al autenticador.
- Solicitud de Identidad: El autenticador solicita la identidad del solicitante.
- Respuesta de Identidad: El solicitante proporciona su identidad, que el autenticador reenvía al servidor RADIUS a través de un paquete RADIUS Access-Request.
- Intercambio EAP: El servidor RADIUS y el solicitante negocian un método EAP e intercambian credenciales de forma segura a través del autenticador.
- Decisión de Acceso: Tras una validación exitosa, el servidor RADIUS envía un paquete RADIUS Access-Accept al autenticador. Este paquete a menudo incluye atributos específicos del proveedor (VSAs) para la asignación dinámica de VLAN o políticas de QoS.
- Puerto Autorizado: El autenticador transiciona el puerto a un estado autorizado, permitiendo el tráfico de red normal.
Métodos EAP: Elegir el Protocolo Correcto
El marco EAP es extensible. La elección del método EAP determina cómo se intercambian y verifican las credenciales:
- EAP-TLS (Transport Layer Security): El estándar de oro para la seguridad. Requiere autenticación mutua utilizando certificados digitales tanto en el cliente como en el servidor. Aunque es altamente seguro, requiere una Infraestructura de Clave Pública (PKI) robusta.
- PEAP-MSCHAPv2 (Protected EAP): La implementación más común en entornos empresariales. Utiliza un certificado del lado del servidor para establecer un túnel TLS seguro, dentro del cual el cliente se autentica utilizando un nombre de usuario y contraseña estándar (MSCHAPv2). Equilibra la seguridad con la simplicidad de implementación.
- EAP-TTLS (Tunneled TLS): Similar a PEAP, pero soporta una gama más amplia de protocolos de autenticación internos, incluyendo PAP o CHAP heredados, a menudo utilizados en entornos que no son de Windows.
Guía de Implementación
La implementación de 802.1X requiere una planificación cuidadosa para evitar interrupciones al usuario. Un enfoque por fases es fundamental para el éxito.
Fase 1: Preparación de la Infraestructura
Antes de habilitar 802.1X en el borde, asegúrese de que su infraestructura central esté preparada. Implemente un servidor RADIUS (como Microsoft NPS o FreeRADIUS) e intégrelo con su proveedor de identidad. Configure alta disponibilidad para la infraestructura RADIUS; si el servidor de autenticación falla, el acceso a la red se detiene.
Fase 2: Configuración del Solicitante
No confíe en que los usuarios configuren manualmente sus dispositivos. Para dispositivos corporativos gestionados, utilice Objetos de Política de Grupo (GPO) o plataformas de Gestión de Dispositivos Móviles (MDM) para enviar el perfil 802.1X correcto, incluyendo el método EAP requerido y el certificado raíz de confianza para el servidor RADIUS.
Fase 3: Piloto y Despliegue
Comience con un pequeño grupo piloto utilizando un SSID de prueba dedicado o un stack de switch específico. Monitoree los registros RADIUS en busca de fallos de autenticación, particularmente aquellos relacionados con problemas de confianza de certificados o credenciales incorrectas. Una vez que el piloto sea estable, proceda con un despliegue por fases en toda la organización.
Integración con el Acceso de Invitados
802.1X está diseñado para usuarios corporativos con credenciales conocidas. Para visitantes, contratistas y clientes, necesita una estrategia paralela. Aquí es donde una plataforma dedicada de Guest WiFi se vuelve esencial. Mientras los dispositivos corporativos se autentican sin problemas a través de 802.1X en VLANs seguras, los invitados se autentican a través de un captive portal, proporcionando valiosos datos de primera parte para WiFi Analytics mientras permanecen aislados de los recursos internos.
La plataforma de Purple también puede actuar como proveedor de identidad para servicios como OpenRoaming bajo la licencia Connect, cerrando la brecha entre el acceso público sin interrupciones y la autenticación segura.
Mejores Prácticas
- Aplicar Servidor "Validación de Certificados: Al usar PEAP o EAP-TTLS, debe configurar los suplicantes para validar el certificado del servidor RADIUS. No hacerlo deja la red vulnerable a ataques de puntos de acceso no autorizados (Evil Twin).
- Implementar Asignación Dinámica de VLAN: Aproveche los atributos RADIUS para asignar usuarios a VLAN específicas según su membresía en grupos de Active Directory. Esto reduce el número de SSIDs requeridos y simplifica la segmentación de la red.
- Abordar Dispositivos IoT con MAB: Muchos dispositivos IoT (impresoras, televisores inteligentes) no son compatibles con los suplicantes 802.1X. Utilice MAC Authentication Bypass (MAB) como alternativa. El autenticador usa la dirección MAC del dispositivo como nombre de usuario y contraseña. Dado que las direcciones MAC pueden ser suplantadas, limite estrictamente los privilegios de acceso de los dispositivos autenticados por MAB.
Solución de Problemas y Mitigación de Riesgos
Cuando 802.1X falla, los registros del servidor RADIUS son su herramienta de diagnóstico principal.
- Error: EAP Timeout: El autenticador no está recibiendo una respuesta del suplicante. Esto a menudo indica que el software del suplicante no se está ejecutando, o que el dispositivo no está configurado para 802.1X.
- Error: Usuario Desconocido o Contraseña Incorrecta: El usuario ingresó credenciales incorrectas, o el servidor RADIUS no puede comunicarse con el almacén de identidades de backend.
- Error: Falla de Confianza de Certificado: El suplicante rechazó el certificado del servidor RADIUS. Asegúrese de que el certificado de la CA raíz que emitió el certificado del servidor RADIUS esté instalado en el almacén raíz de confianza del suplicante.
Para una perspectiva más amplia sobre la optimización de la arquitectura de red, considere cómo la autenticación se integra con las estrategias WAN modernas, como se discute en Los Beneficios Clave de SD WAN para Empresas Modernas .
ROI e Impacto Empresarial
La implementación de 802.1X ofrece un valor empresarial medible más allá de la seguridad pura:
- Reducción de la Carga Operativa: Elimina la necesidad de rotar manualmente las PSK cuando los empleados se van o los contratistas terminan sus compromisos. El acceso se revoca instantáneamente deshabilitando la cuenta de directorio del usuario.
- Cumplimiento Simplificado: Proporciona los registros de auditoría por usuario y los controles de acceso robustos requeridos por PCI DSS, HIPAA y GDPR.
- Visibilidad de Red Mejorada: Integra la identidad con la actividad de la red, permitiendo a los equipos de TI rastrear eventos de seguridad o problemas de rendimiento hasta usuarios específicos en lugar de direcciones IP genéricas.
Al alejarse de las claves compartidas y adoptar el control de acceso basado en puertos, las redes empresariales logran la seguridad granular requerida para las demandas operativas modernas. Para una comparación detallada de los estándares de seguridad inalámbrica, revise nuestra guía sobre WPA, WPA2 y WPA3: ¿Cuál es la Diferencia y Cuál Debería Usar? .
Resumen de Audio
Escuche nuestro resumen técnico de 10 minutos sobre la autenticación 802.1X:
Términos clave y definiciones
802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism to devices wishing to attach to a LAN or WLAN.
The foundational standard replacing shared passwords with per-user authentication in enterprise networks.
Supplicant
The software client on an end-user device that requests network access and handles the EAP exchange.
Required on all laptops, phones, and tablets connecting to an 802.1X network.
Authenticator
The network edge device (switch or access point) that controls the physical or logical port, blocking traffic until authentication is complete.
The enforcement point in the network architecture.
RADIUS Server
Remote Authentication Dial-In User Service. The central server that validates credentials against a directory and returns policy decisions.
The brain of the 802.1X deployment, often implemented via Microsoft NPS or Cisco ISE.
EAP (Extensible Authentication Protocol)
An authentication framework frequently used in wireless networks and point-to-point connections, providing transport for various authentication methods.
The language spoken between the supplicant and the RADIUS server.
Dynamic VLAN Assignment
The process where a RADIUS server instructs the authenticator to place a user into a specific VLAN based on their identity or group membership.
Crucial for network segmentation and compliance without broadcasting dozens of SSIDs.
EAP-TLS
An EAP method requiring mutual certificate-based authentication between the client and the server.
The most secure method, ideal for highly regulated environments like healthcare or finance.
PEAP (Protected EAP)
An EAP method that establishes a secure TLS tunnel using a server certificate, protecting the inner credential exchange (usually a username/password).
The most common deployment method due to its balance of security and operational simplicity.
Casos de éxito
A 200-room hotel needs to secure its back-of-house operational network (staff tablets, VoIP phones, management laptops) while maintaining a separate, open guest network. They currently use a single PSK for staff.
- Deploy Microsoft NPS (RADIUS) integrated with the hotel's Active Directory.
- Configure the wireless controller to broadcast a new 'Staff_Secure' SSID using WPA2-Enterprise (802.1X).
- Push a PEAP-MSCHAPv2 profile to all managed staff laptops and tablets via MDM.
- For VoIP phones lacking 802.1X support, configure MAC Authentication Bypass (MAB) on the RADIUS server, assigning them to an isolated Voice VLAN.
- Retain the open guest network, securing it with Purple's captive portal for guest isolation and analytics.
A large retail chain is failing PCI DSS compliance because their Point of Sale (PoS) terminals are on the same logical network segment as store manager laptops, using a shared WPA2-Personal key.
- Implement 802.1X across all corporate access points.
- Configure dynamic VLAN assignment on the RADIUS server.
- Create a policy: If the authenticating device is a PoS terminal (authenticated via machine certificate using EAP-TLS), assign it to the highly restricted PCI-VLAN.
- Create a second policy: If the user is a Store Manager (authenticated via PEAP), assign them to the Corp-VLAN with standard internet and intranet access.
Análisis de escenarios
Q1. Your organization is migrating from WPA2-Personal to WPA2-Enterprise. You have a mix of corporate-owned Windows laptops and employee-owned BYOD smartphones. You do not have a PKI infrastructure. Which EAP method should you deploy?
💡 Sugerencia:Consider the requirement for client certificates versus server-only certificates.
Mostrar enfoque recomendado
PEAP-MSCHAPv2. Since you lack a PKI infrastructure, deploying client certificates for EAP-TLS is not feasible. PEAP only requires a server-side certificate on the RADIUS server, allowing users to authenticate with their standard Active Directory username and password.
Q2. After deploying 802.1X using PEAP, several users report they are prompted with a security warning asking them to 'Trust' a certificate when connecting to the network. What configuration step was missed?
💡 Sugerencia:Think about how the supplicant validates the identity of the RADIUS server.
Mostrar enfoque recomendado
The supplicant profile pushed to the devices was not configured to explicitly trust the Root CA that issued the RADIUS server's certificate. Without this configuration, the OS prompts the user to manually verify the server's identity, which is a security risk and poor user experience.
Q3. You need to connect 50 smart TVs in hotel conference rooms to the network. These devices do not support 802.1X supplicants. How can you provide them access while maintaining security?
💡 Sugerencia:Consider alternative authentication methods for headless devices and how to restrict their access.
Mostrar enfoque recomendado
Implement MAC Authentication Bypass (MAB). The authenticator will use the smart TV's MAC address to authenticate against the RADIUS server. Crucially, the RADIUS server must be configured to assign these devices to a heavily restricted VLAN (e.g., internet-only, no internal access) to mitigate the risk of MAC address spoofing.



