¿Qué es WiFi Analytics? Una Guía Completa
Esta guía técnica completa explica cómo WiFi analytics transforma la infraestructura de red estándar en un motor de inteligencia de negocios, cubriendo mecanismos de captura de datos (afluencia, tiempo de permanencia, tipo de dispositivo, visitas repetidas), consideraciones arquitectónicas y ROI medible. Está diseñada para gerentes de TI, arquitectos de red y directores de operaciones de recintos que necesitan evaluar e implementar WiFi analytics en entornos empresariales.
🎧 Escucha esta guía
Ver transcripción
Resumen Ejecutivo
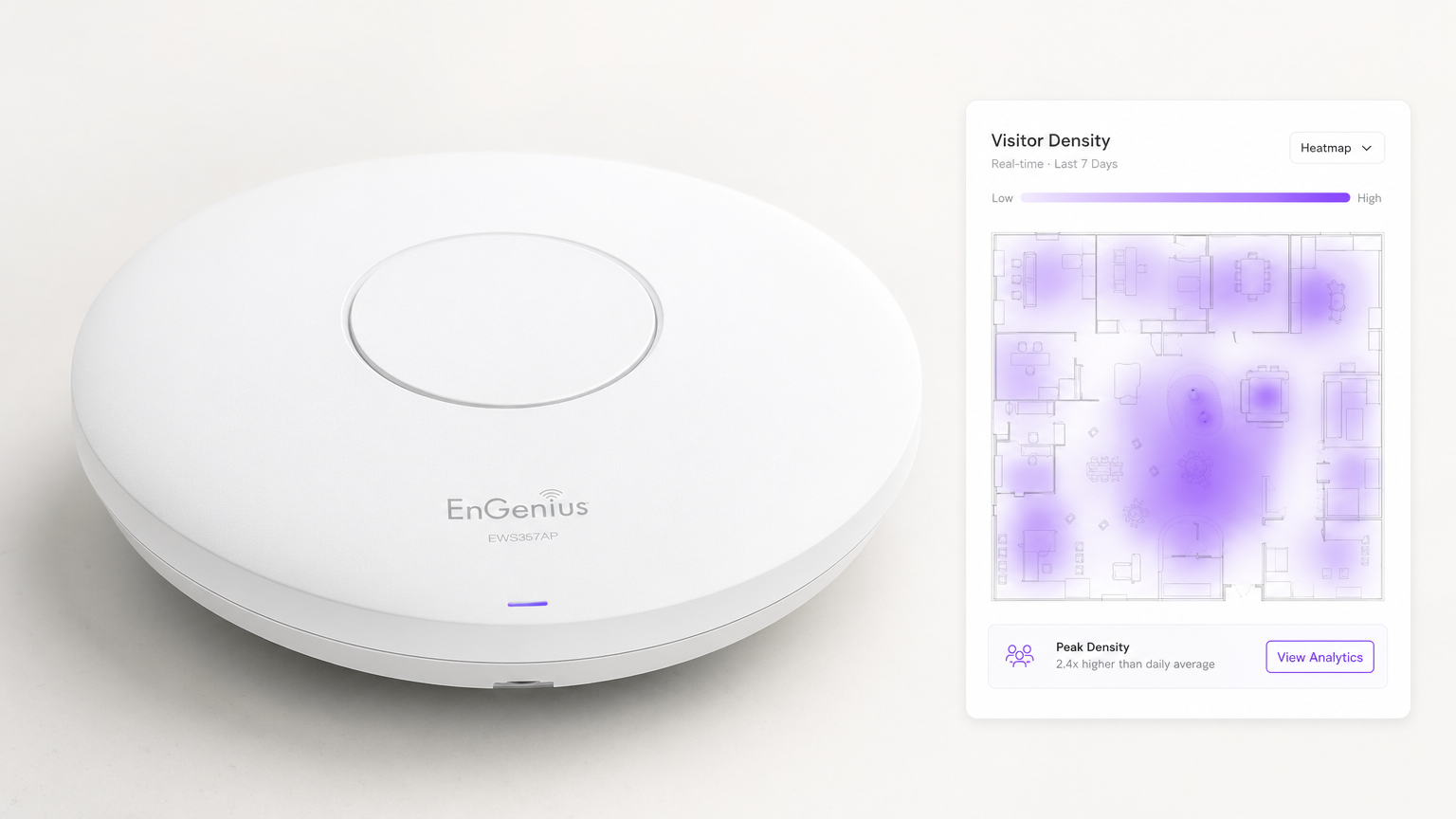
Para los recintos empresariales modernos, proporcionar Guest WiFi ya no es simplemente un centro de costos o una utilidad esperada, es una capa de infraestructura crítica para la inteligencia de negocios. WiFi Analytics es el proceso de capturar, procesar y visualizar datos generados por dispositivos que se conectan o sondean una red inalámbrica. Para los gerentes de TI, arquitectos de red y directores de operaciones de recintos, implementar una solución de analytics robusta cierra la brecha entre el gasto de TI y el valor comercial medible.
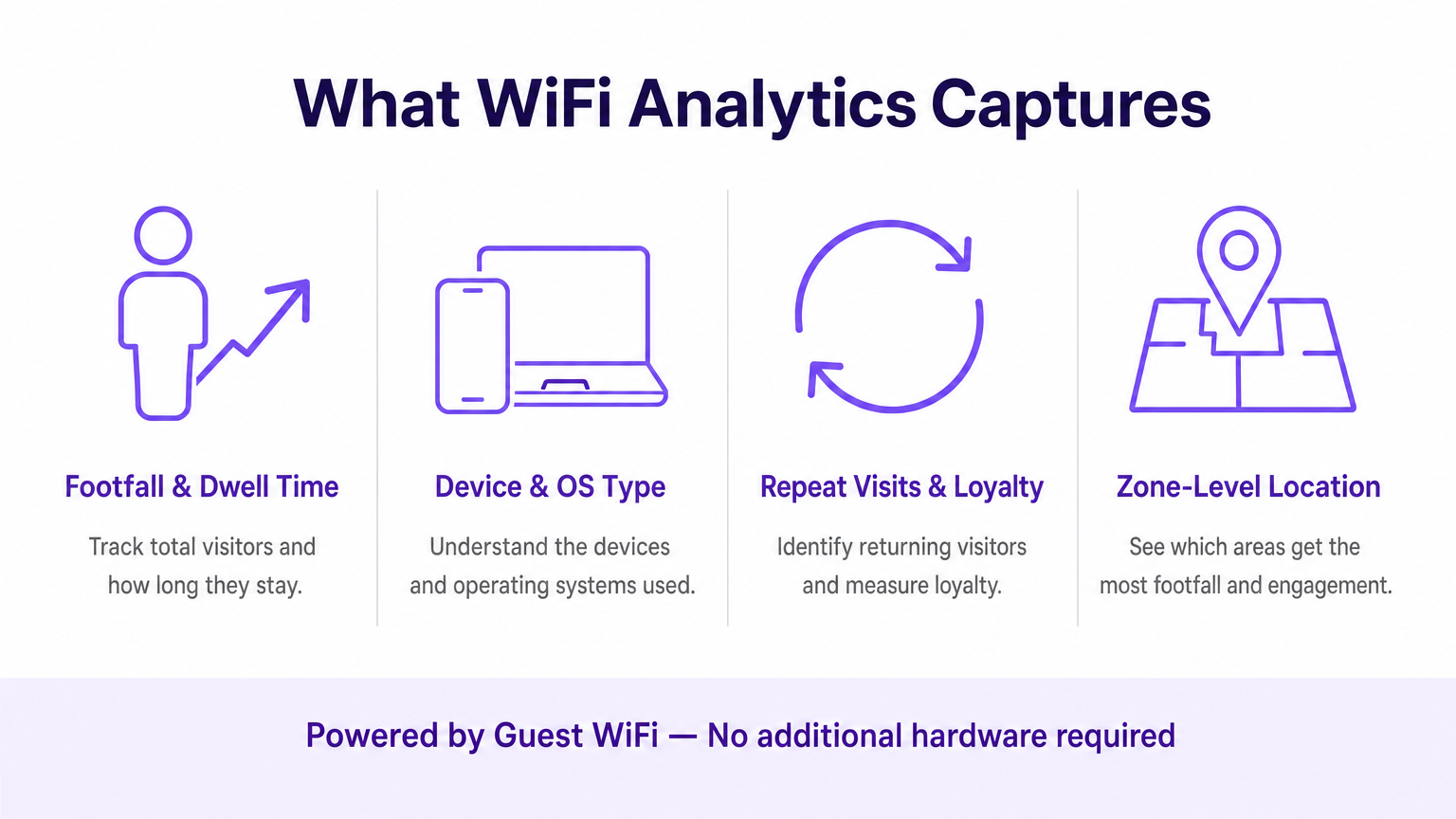
Esta guía detalla la arquitectura técnica de la recopilación de datos de WiFi, las métricas específicas capturadas —incluyendo afluencia, tiempo de permanencia, tipo de dispositivo y visitas repetidas— y los puntos de integración necesarios para transformar la telemetría de red en bruto en información procesable. Al aprovechar la infraestructura existente, ya sea implementando en Retail , Healthcare , Hospitality o Transport , las organizaciones pueden lograr una visibilidad profunda de los espacios físicos sin implementar costosas redes de sensores superpuestas.
Análisis Técnico Detallado: Cómo Funciona WiFi Analytics
En su esencia, WiFi analytics se basa en el comportamiento fundamental de los dispositivos cliente 802.11. Incluso antes de que un usuario se autentique en una red, su dispositivo transmite solicitudes de sondeo para descubrir puntos de acceso (APs) disponibles. Estos marcos de gestión, combinados con los datos generados durante las sesiones autenticadas, forman los dos flujos de datos principales que procesa una plataforma de WiFi analytics.
Los Mecanismos de Captura de Datos
Análisis de Presencia (No Autenticado): Cuando un smartphone tiene WiFi habilitado, envía periódicamente solicitudes de sondeo que contienen su dirección MAC y la intensidad de la señal (RSSI). Los puntos de acceso detectan estas sondas. Al triangular el RSSI a través de múltiples APs, el sistema calcula la ubicación aproximada del dispositivo dentro de un recinto. Esto proporciona métricas básicas de afluencia y conversión — transeúntes versus visitantes activos — sin requerir ninguna interacción del usuario.
Analytics Autenticado: Cuando un usuario se conecta activamente al Captive Portal, el motor de analytics captura datos propios enriquecidos. Esto típicamente incluye información demográfica, detalles de contacto e identificadores de CRM, cerrando la brecha entre una dirección MAC anónima y un perfil de cliente conocido y persistente. Esta es la capa de datos que permite el marketing personalizado y los programas de lealtad.
Servicios de Ubicación (RTLS): Las implementaciones avanzadas utilizan técnicas como la Diferencia de Tiempo de Llegada (TDOA) o la Medición de Tiempo Fino (802.11mc/802.11az) para proporcionar un posicionamiento interior de alta precisión, a menudo aumentado por balizas Bluetooth Low Energy (BLE). Para un desglose detallado de estas tecnologías de posicionamiento, consulte nuestra Guía de Sistemas de Posicionamiento Interior: UWB, BLE y WiFi .
Arquitectura e Integración
La arquitectura típicamente involucra hardware de borde —controladores de LAN inalámbrica y APs— que reenvían datos de telemetría vía API o syslog a un motor de analytics basado en la nube. La plataforma ingiere este flujo de datos de alta velocidad, lo normaliza y aplica algoritmos de mapeo espacial contra planos de planta cargados para producir analytics a nivel de zona.
Crucialmente, el sistema debe integrarse sin problemas con la pila de proveedores de red existente. Ya sea que esté evaluando Purple vs Cisco Spaces (DNA Spaces): Cuándo Elegir Cada Uno o implementando en Aruba, Ruckus o Meraki, la plataforma de analytics actúa como una superposición — extrayendo valor sin requerir el reemplazo de hardware. Esta es una distinción fundamental de las soluciones propietarias basadas en sensores.
El pipeline de datos sigue este flujo: los APs capturan solicitudes de sondeo y eventos de conexión → el controlador WLAN agrega y reenvía la telemetría → el motor de analytics normaliza y mapea los datos → el panel de control muestra insights a los equipos de operaciones y marketing → los webhooks de la API envían perfiles de usuario autenticados a plataformas de CRM y automatización de marketing.
Consideraciones de Estándares y Cumplimiento
Las implementaciones deben tener en cuenta varios estándares regulatorios y técnicos:
| Estándar | Relevancia |
|---|---|
| IEEE 802.11ax (Wi-Fi 6/6E) | Proporciona las características OFDMA y BSS Colouring que mejoran la densidad de AP y la precisión de la ubicación |
| IEEE 802.11mc / 802.11az | La Medición de Tiempo Fino (FTM) permite una precisión de alcance sub-métrica para implementaciones RTLS |
| WPA3-Enterprise | Obligatorio para implementaciones que manejan datos sensibles; proporciona modo de seguridad de 192 bits |
| GDPR / UK GDPR | Requiere consentimiento explícito y auditable antes de capturar datos personales a través del Captive Portal |
| PCI DSS | El tráfico de Guest WiFi debe aislarse de las redes de tarjetas de pago mediante VLANs dedicadas |
| CCPA | Aplica a implementaciones que atienden a residentes de California; requiere mecanismos de exclusión voluntaria |
Guía de Implementación
La implementación de una solución de WiFi analytics requiere una cuidadosa coordinación entre la ingeniería de red y los interesados del negocio. Los siguientes pasos representan un marco de implementación neutral al proveedor.
Paso 1 — Evaluación de la Preparación de la Red: Evalúe la densidad y ubicación actuales de los APs en función de los requisitos de analytics de ubicación. El diseño de cobertura estándar (APs centrados en las habitaciones) es insuficiente para una triangulación precisa. La ubicación perimetral de los APs es esencial. Realice un estudio de sitio activo utilizando herramientas como Ekahau o iBwave para identificar zonas muertas de RF y fuentes de interferencia.
Paso 2 — Mapeo de Planos: Cargue planos precisos y escalados a la plataforma de análisis. Defina zonas que se alineen con los objetivos comerciales — por ejemplo, 'Área de Caja', 'Zona de Cabecera Promocional' o 'Lobby'. Una escala imprecisa del plano es una de las causas más comunes de la mala calidad de los datos de ubicación.
Paso 3 — Configuración del Captive Portal: Diseñe el flujo de autenticación para equilibrar la experiencia del usuario con la adquisición de datos. Implemente opciones de inicio de sesión social (Google, Apple ID) para reducir la fricción. Asegúrese de que el portal sea totalmente responsivo en todos los tipos de dispositivos. Purple puede actuar como proveedor de identidad para OpenRoaming bajo la licencia Connect, permitiendo una incorporación fluida para usuarios recurrentes sin interacciones repetidas con el portal.
Paso 4 — Marco de Consentimiento y Privacidad: Implemente la captura de consentimiento compatible con GDPR. El consentimiento debe ser granular (opt-ins separados para análisis, marketing y uso compartido con terceros), explícito (sin casillas premarcadas) y auditable (registros con marca de tiempo almacenados por perfil de usuario).
Paso 5 — Integración de Datos: Configure webhooks e integraciones de REST API para enviar datos de usuarios autenticados a plataformas CRM (Salesforce, HubSpot) y herramientas de automatización de marketing (Marketo, Klaviyo). Este paso es donde la implementación de TI habilita directamente el ROI de marketing y con frecuencia se le resta prioridad — no permita que esto suceda.
Paso 6 — Alertas e Informes: Configure alertas operativas (por ejemplo, umbrales de tiempo de permanencia que activan notificaciones al personal) e informes automatizados para las partes interesadas no técnicas. Los datos que permanecen en un panel de TI no generan valor comercial.
Mejores Prácticas
Mitigación de la Aleatorización de MAC: Los sistemas operativos modernos (iOS 14+, Android 10+) utilizan direcciones MAC aleatorizadas por red. Las plataformas de análisis deben depender de sesiones autenticadas y algoritmos de unión de comportamiento en lugar de direcciones de hardware persistentes para el seguimiento de visitantes recurrentes. Priorice las tasas de autenticación del captive portal como un KPI.
Densidad de AP para Precisión de Ubicación: Se requiere un mínimo de tres AP con cobertura superpuesta para una triangulación básica. Para una precisión inferior a 3 metros, implemente APs a intervalos de 8 a 10 metros en zonas de alto valor. Para RTLS de sub-metro, complemente con balizas BLE o implemente hardware compatible con 802.11az.
Segmentación de Red: Aísle el tráfico de Guest WiFi de las redes corporativas y de pago utilizando VLANs dedicadas, ACLs de firewall y filtrado DNS. Esto es innegociable para el cumplimiento de PCI DSS y reduce significativamente la superficie de ataque.
Gobernanza de Datos: Establezca una política clara de retención de datos. La mayoría de los casos de uso de análisis se benefician de 13 meses de datos (lo que permite la comparación año tras año). Períodos de retención más largos aumentan el riesgo de cumplimiento y los costos de almacenamiento sin un beneficio analítico proporcional.
Solución de Problemas y Mitigación de Riesgos
Datos de Ubicación Imprecisos: Causados más comúnmente por una densidad insuficiente de AP, una escala incorrecta del plano o interferencia de RF de redes adyacentes. Valide la ubicación de los APs con el estudio del sitio, verifique la escala del plano en la plataforma de análisis y utilice las herramientas de análisis de espectro en su controlador WLAN para identificar fuentes de interferencia.
Bajas Tasas de Autenticación: Si los visitantes no completan el captive portal, audite el recorrido del usuario. Mida la tasa de abandono en cada paso. Las causas comunes incluyen tiempos de carga lentos del portal (optimice para dispositivos móviles en conexiones de respaldo 3G/4G), campos de datos excesivos y propuestas de valor poco claras. Realice pruebas A/B del diseño del portal.
Silos de Datos: El modo de falla más perjudicial comercialmente. Cree proactivamente informes automatizados para los equipos de operaciones y marketing. Establezca un grupo de trabajo interfuncional de 'Datos WiFi' con representantes de TI, marketing y operaciones para revisar los conocimientos mensualmente.
Dependencia del Proveedor (Vendor Lock-In): Evite las plataformas de análisis que requieren hardware propietario. Asegúrese de que la plataforma sea compatible con su proveedor de AP existente a través de APIs estándar y pueda exportar datos en formatos abiertos (CSV, JSON) para evitar la dependencia del ecosistema de un solo proveedor.
ROI e Impacto Comercial
La medida definitiva de una implementación de análisis de WiFi es su contribución a los resultados comerciales. El siguiente marco mapea las capacidades de análisis a KPIs medibles.
| Capacidad de Análisis | KPI Comercial | Mejora Típica |
|---|---|---|
| Conteo de afluencia | Seguimiento del volumen de visitantes | Reemplaza el conteo manual; precisión del 99%+ |
| Tiempo de permanencia por zona | Gestión de colas, asignación de personal | Reducción del 15–25% en tiempos de espera pico |
| Tasa de visitas repetidas | Medición de la lealtad del cliente | Base para el ROI del programa de lealtad |
| Tasa de conversión espacial | Conversión de escaparate a entrada | Informa la inversión en exhibiciones exteriores |
| Perfiles autenticados | Enriquecimiento de CRM, segmentación de campañas | Mejora de 3 a 5 veces en la relevancia de las campañas de email |
| Análisis de flujo de zona | Optimización de diseño | Aumento medible en el gasto secundario |
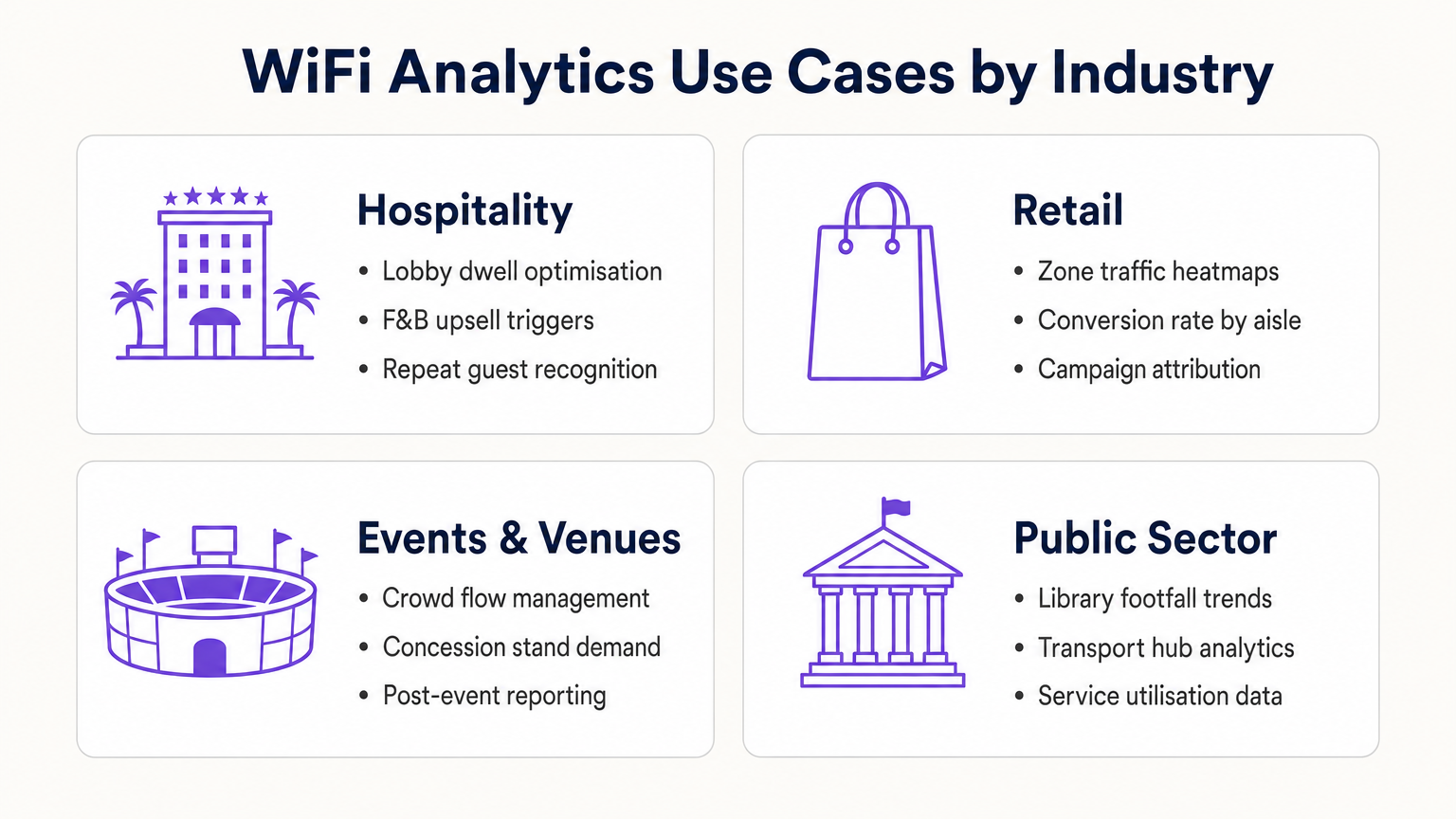
Para operadores de Hospitalidad , el análisis de WiFi permite el reconocimiento de huéspedes recurrentes, la gestión de la congestión del lobby y los disparadores de venta adicional de alimentos y bebidas. Para cadenas de Retail , proporciona optimización de diseño basada en mapas de calor y atribución de campañas. Para centros de transporte y lugares del sector público, ofrece datos de utilización de servicios y gestión del flujo de multitudes. Para una mirada detallada a las aplicaciones de lugares conectados, consulte nuestra Arquitectura del Internet de las Cosas: Una Guía Completa .
Al tratar la red WiFi como un activo de datos estratégico en lugar de una utilidad, los líderes de TI transitan de gerentes de centro de costos a habilitadores de negocios — entregando un ROI concreto a través de una mayor eficiencia operativa, una mejor interacción con el cliente y una toma de decisiones basada en evidencia.
Términos clave y definiciones
Probe Request
An 802.11 management frame broadcast by a client device to discover available wireless networks in its vicinity, containing the device's MAC address and supported data rates.
The foundational mechanism for unauthenticated presence analytics. Access points capture these frames to detect and locate devices before any user interaction occurs.
RSSI (Received Signal Strength Indicator)
A measurement of the power level of a received radio signal, expressed in dBm (typically ranging from 0 to -100 dBm).
Analytics platforms use RSSI readings from multiple APs simultaneously to triangulate a device's physical location. Lower (more negative) values indicate greater distance from the AP.
MAC Address Randomisation
A privacy feature in modern operating systems (iOS 14+, Android 10+) that assigns a randomised hardware address to a device on a per-network basis, replacing the device's permanent MAC address.
Significantly limits the reliability of unauthenticated presence analytics for repeat visitor tracking, making captive portal authentication essential for building persistent customer profiles.
Captive Portal
A web-based authentication interface that intercepts a user's HTTP/HTTPS traffic and redirects them to a login or registration page before granting network access.
The primary mechanism for capturing first-party customer data and securing GDPR-compliant consent. Portal design and friction level directly determine data capture rates.
Dwell Time
The duration a specific authenticated or detected device remains within a defined physical zone, measured from first detection to last detection within that zone.
A critical operational metric used to identify queue congestion, measure engagement with promotional displays, and trigger time-based marketing automations.
Footfall
The total count of unique devices detected within a defined venue or zone over a specified time period.
Provides the baseline traffic metric analogous to website sessions. Used to measure overall venue performance, compare locations, and calculate spatial conversion rates.
Spatial Conversion Rate
The percentage of devices detected in an outer zone (e.g., a street or main walkway) that subsequently enter an inner zone (e.g., a store or aisle).
Used by retail operators to evaluate the effectiveness of exterior displays and entrance signage. A low conversion rate despite high footfall indicates an attraction problem at the threshold.
OpenRoaming
A Wireless Broadband Alliance (WBA) federation standard that enables seamless, secure Wi-Fi onboarding across participating networks without requiring repeated captive portal interactions.
Purple can act as an identity provider for OpenRoaming under the Connect licence, enabling venues to offer seamless connectivity while retaining the ability to capture analytics data from returning users.
RTLS (Real-Time Location System)
A system that uses radio frequency technologies (WiFi, BLE, UWB, or RFID) to determine and track the real-time location of objects or people within a defined space.
Relevant when sub-3-metre location accuracy is required — for example, asset tracking in healthcare or turn-by-turn indoor navigation in large venues. Standard WiFi RSSI triangulation is typically insufficient for these use cases.
TDOA (Time Difference of Arrival)
A location technique that calculates position by measuring the difference in the time a signal arrives at multiple reference points (APs or anchors).
Provides significantly higher location accuracy than RSSI-based triangulation, but requires hardware support and precise clock synchronisation across APs.
Casos de éxito
A 400-room resort hotel wants to reduce congestion at check-in desks during peak hours (15:00–17:00) and increase revenue at the lobby bar. The IT team has a Cisco Meraki deployment with 24 APs across the ground floor.
- Map the lobby floor plan in the analytics platform with three distinct zones: 'Check-In Queue', 'Lobby Seating', and 'Bar Area'. Verify that at least three APs provide overlapping coverage in each zone for accurate triangulation.
- Configure a real-time operational alert: if the device count in the 'Check-In Queue' zone exceeds 20 simultaneously AND average dwell time exceeds 15 minutes, trigger an automated SMS to the Duty Manager via the platform's webhook integration.
- Configure a marketing trigger: if a device dwells in the 'Lobby Seating' zone for more than 10 minutes, push a personalised notification (via the captive portal session or email if authenticated) offering a 10% discount at the bar, valid for 30 minutes.
- Integrate the authenticated user profiles with the hotel PMS (Property Management System) to automatically recognise returning guests and suppress the captive portal for them, surfacing a personalised welcome message instead.
- Review weekly dwell time reports to identify whether the check-in queue alert is triggering at consistent times, enabling proactive staffing adjustments rather than reactive responses.
A 50-store retail chain has deployed WiFi analytics across all locations. The Head of Merchandising reports that a specific promotional aisle in their flagship Manchester store generates high footfall but below-average sales per square foot. They want to understand why before rolling out the same layout to 15 other stores.
- Define two zones in the analytics platform for the Manchester store: 'Main Walkway' (the primary traffic artery adjacent to the aisle) and 'Promotional Aisle' (the target zone).
- Pull a 30-day report comparing: (a) the spatial conversion rate — the percentage of devices in the Main Walkway that subsequently enter the Promotional Aisle — and (b) the average dwell time within the Promotional Aisle for devices that do enter.
- Scenario A — High conversion, low dwell time: Visitors are entering the aisle but leaving quickly. This indicates the product placement or signage within the aisle is confusing or unappealing once inside. Recommendation: redesign the aisle layout and test with a 14-day A/B comparison.
- Scenario B — Low conversion despite high walkway traffic: Visitors are not being drawn into the aisle from the walkway. This indicates the end-cap display or entrance signage is ineffective. Recommendation: redesign the entrance display and measure conversion rate change over the following 14 days.
- Correlate the WiFi analytics data with POS transaction data by time-of-day to identify whether dwell time correlates with purchase probability, establishing a venue-specific 'engagement threshold' for future campaign design.
Análisis de escenarios
Q1. A retail client reports that their 'Repeat Visitor' metric has dropped by 40% over the past eight months, despite sales remaining steady and no significant change in marketing activity. Their analytics deployment relies entirely on unauthenticated presence tracking. What is the most likely technical cause, and what is the recommended remediation?
💡 Sugerencia:Consider the timeline of major mobile OS updates and their privacy features.
Mostrar enfoque recomendado
The most likely cause is the progressive adoption of MAC address randomisation across the client's customer base. iOS 14 (released September 2020) and Android 10+ introduced per-network MAC randomisation, causing returning devices to appear as new, unique visitors to presence analytics engines. As the proportion of customers running these OS versions has increased, the repeat visitor metric has degraded. The remediation is to implement a captive portal authentication layer. When users authenticate with a persistent identifier (email address, social login), the analytics platform can build a customer profile tied to that identifier rather than the rotating MAC address. This restores repeat visitor tracking accuracy and simultaneously generates first-party marketing data.
Q2. You are the network architect for a new 80,000-seat stadium. The venue operations team wants WiFi analytics to manage crowd flow through concourse areas and identify concession stand congestion in real time. The IT budget allows for 400 APs. How should you prioritise AP placement to maximise analytics accuracy, and what accuracy level can you realistically expect?
💡 Sugerencia:Think about the geometric requirements of triangulation and the difference between coverage and analytics design principles.
Mostrar enfoque recomendado
Prioritise perimeter placement over central coverage. For each concourse zone, ensure APs are placed at the zone boundaries rather than the centre. This enables the analytics engine to accurately determine when a device crosses from one zone to another. Aim for a minimum of three APs with overlapping coverage in each defined zone, with AP spacing of 8–10 metres in high-priority areas (concession stands, entry/exit gates). With standard RSSI triangulation on 802.11ax hardware, expect 3–5 metre location accuracy in open concourse areas. For sub-3-metre accuracy at specific chokepoints (e.g., individual concession windows), supplement with BLE beacons or deploy 802.11az-capable APs at those locations.
Q3. A hospital IT director wants to use the existing WiFi network to track the location of 200 high-value mobile medical assets (infusion pumps, portable ECG monitors). They do not want to deploy any additional hardware. The analytics platform currently provides 5-metre RSSI triangulation accuracy. Is this deployment viable, and what are the key risks?
💡 Sugerencia:Consider both the technical accuracy requirements and the behaviour of the devices being tracked.
Mostrar enfoque recomendado
This deployment is not reliably viable for two reasons. First, medical equipment frequently enters low-power or sleep states, causing the device to stop broadcasting WiFi probe requests. When a device is not actively probing, it is invisible to the presence analytics engine. This creates gaps in tracking that are unacceptable for asset management. Second, 5-metre RSSI accuracy is insufficient to determine whether an asset is in Room 4A or Room 4B in a typical hospital ward layout. The recommended alternative is a dedicated RTLS solution using active RFID tags or BLE beacons attached to the assets, which actively broadcast at regular intervals regardless of the asset's power state, and which can achieve sub-2-metre accuracy. The existing WiFi infrastructure can serve as the receiver network for BLE beacons, avoiding the need for a completely separate sensor network.



