La Guía Completa de WiFi para Invitados para Empresas
Esta guía técnica definitiva proporciona a los líderes de TI y arquitectos de red un plan integral para implementar, asegurar y monetizar el WiFi para invitados empresarial. Cierra la brecha entre la infraestructura de red física, los estándares de cumplimiento como GDPR y PCI DSS, y el valor comercial desbloqueado a través de la captura de datos de primera parte.
🎧 Escucha esta guía
Ver transcripción
- Resumen Ejecutivo
- Análisis Técnico Detallado: Arquitectura y Estándares
- Segmentación de Red y Etiquetado VLAN
- Estándares de Autenticación y Cifrado
- Planificación de Rendimiento y Capacidad
- Guía de Implementación: Del Hardware al Portal
- Fase 1: Planificación de RF y Estudio de Sitio
- Fase 2: Configuración de la Infraestructura
- Fase 3: Integración del Captive Portal
- Fase 4: Analítica y Automatización de Marketing
- Mejores Prácticas y Cumplimiento
- Solución de Problemas y Mitigación de Riesgos
- Agotamiento de DHCP
- Fallas de Intercepción del Captive Portal
- Puntos de Acceso Maliciosos
- ROI e Impacto Comercial

Resumen Ejecutivo
Para las empresas modernas, el WiFi para invitados ha evolucionado de un simple centro de costos a un activo de infraestructura crítico capaz de generar un retorno comercial significativo. Ya sea que operen en Retail , Hospitality o en grandes espacios públicos, los líderes de TI se enfrentan a un doble mandato: proporcionar conectividad fluida y de alto rendimiento, al mismo tiempo que capturan datos de primera parte de forma segura y conforme a las normativas.
Esta guía proporciona un plan arquitectónico definitivo para el WiFi para invitados empresarial. Detallamos los requisitos técnicos para la segmentación de red, los estándares criptográficos necesarios para una autenticación segura y las metodologías de implementación requeridas para prevenir la saturación de la red. Además, examinamos cómo plataformas como Purple cierran la brecha entre el hardware de red y la tecnología de marketing, transformando direcciones MAC anónimas en perfiles de clientes accionables a través de captive portals conformes. Al tratar el WiFi para invitados como una implementación estratégica en lugar de una utilidad, las organizaciones pueden lograr un ROI medible mientras mitigan los riesgos de seguridad inherentes a las redes de acceso público.
Escuche el podcast complementario de información técnica:
Análisis Técnico Detallado: Arquitectura y Estándares
La base de cualquier implementación de WiFi para invitados empresarial es una segmentación de red rigurosa y protocolos de autenticación robustos. Implementar un SSID abierto sin salvaguardas estructurales introduce un riesgo inaceptable para los datos corporativos y los sistemas de pago.
Segmentación de Red y Etiquetado VLAN
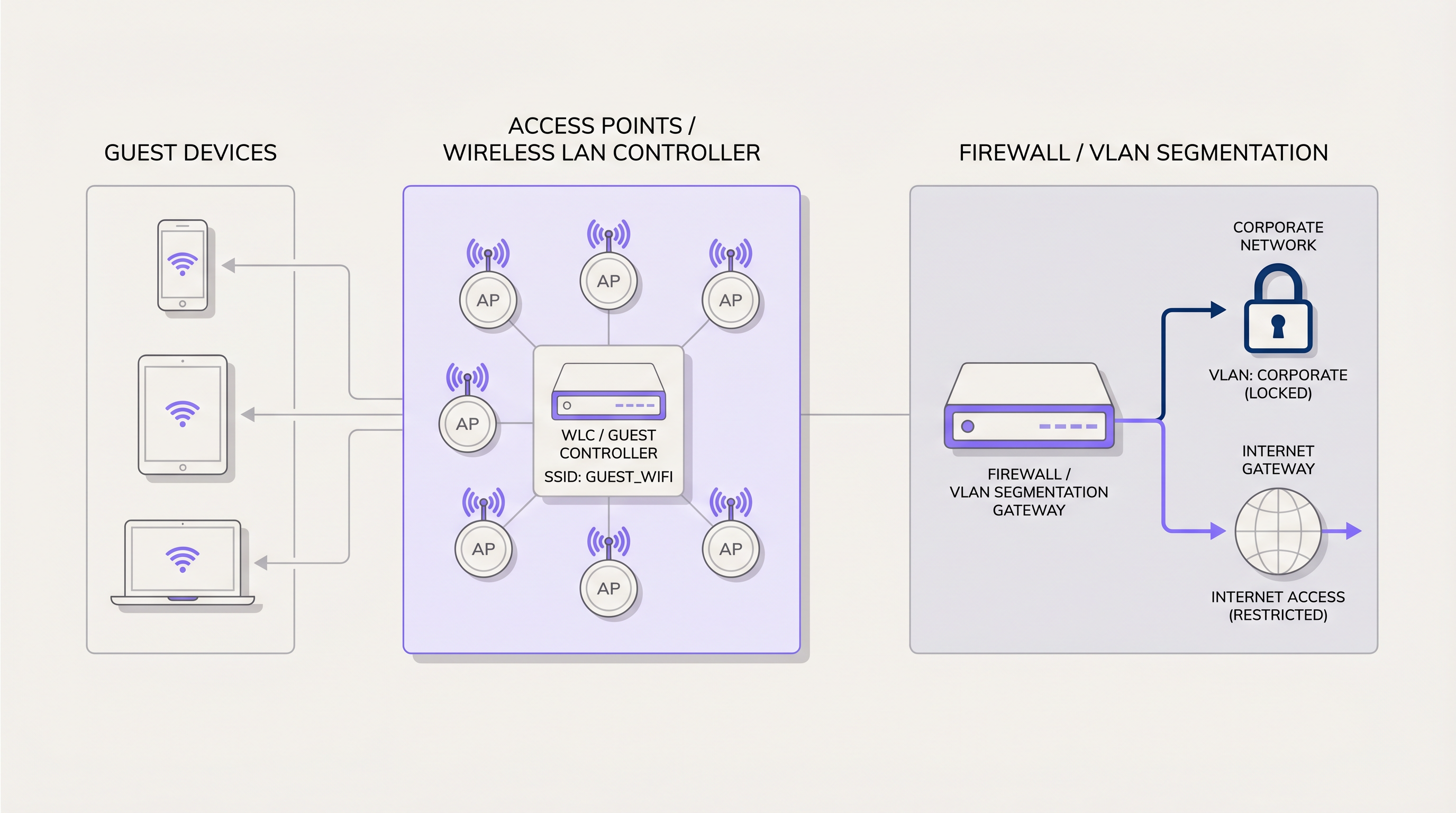
El tráfico de invitados debe aislarse en la Capa 2 y la Capa 3. El modelo de implementación estándar requiere mapear el SSID de invitados a una Red de Área Local Virtual (VLAN) dedicada en el Access Point (AP) o el Wireless LAN Controller (WLC). Esta VLAN debe ser troncalizada a través de la infraestructura de conmutación central directamente al firewall perimetral.
En el firewall, las Listas de Control de Acceso (ACLs) estrictas deben aplicar una política de "denegar todo" para el tráfico destinado a las subredes corporativas internas. El tráfico de invitados solo debe permitirse enrutar a la puerta de enlace de internet. Esta segmentación no es meramente una mejor práctica; es un requisito fundamental para marcos de cumplimiento como PCI DSS. Si un dispositivo de invitado comprometido puede enrutar paquetes a un terminal de punto de venta, toda la red deja de cumplir con las normativas.
Estándares de Autenticación y Cifrado
La era de las redes de invitados abiertas y sin cifrar está terminando. Para proteger los datos del usuario de la escucha pasiva y los ataques de intermediario (man-in-the-middle), las implementaciones deben aprovechar WPA3. Específicamente, WPA3-SAE (Simultaneous Authentication of Equals) proporciona secreto hacia adelante, asegurando que incluso si la frase de contraseña de la red es conocida, el tráfico de sesión individual permanece cifrado y no puede ser descifrado retrospectivamente.
Para entornos que requieren control de acceso granular, IEEE 802.1X con autenticación de backend RADIUS proporciona seguridad de nivel empresarial. Al transmitir solicitudes de autenticación a través de Wide Area Networks (WANs) a proveedores de identidad en la nube, asegurar el propio tráfico RADIUS es crítico. Los equipos de TI deben implementar RadSec: Asegurando el Tráfico de Autenticación RADIUS con TLS para prevenir la interceptación de credenciales. Purple actúa como un proveedor de identidad robusto en estas arquitecturas, integrándose sin problemas con la infraestructura RADIUS existente y soportando estándares de roaming modernos como OpenRoaming.
Planificación de Rendimiento y Capacidad
En entornos de alta densidad, el rendimiento no está limitado por el enlace ascendente de internet, sino por la equidad del tiempo de aire y la utilización del canal. Implementar APs que soporten Wi-Fi 6 (802.11ax) es esencial para mitigar estos cuellos de botella. Las capacidades de Acceso Múltiple por División de Frecuencia Ortogonal (OFDMA) de Wi-Fi 6 permiten que un solo AP se comunique con múltiples clientes simultáneamente, reduciendo drásticamente la latencia en áreas concurridas.
Además, los equipos de TI deben implementar la limitación de velocidad por usuario a nivel de controlador o firewall. Asignar un límite estricto de ancho de banda (por ejemplo, 10 Mbps de descarga / 2 Mbps de subida por usuario) evita que un solo cliente monopolice el enlace ascendente de internet con aplicaciones de alto ancho de banda, asegurando una experiencia base consistente para todos los invitados.
Guía de Implementación: Del Hardware al Portal
Implementar una red WiFi para invitados resiliente requiere un enfoque sistemático, integrando la planificación de RF física con plataformas de análisis basadas en la nube.
Fase 1: Planificación de RF y Estudio de Sitio
Antes de la adquisición de hardware, un estudio de sitio de RF predictivo es obligatorio. El uso de herramientas de software para modelar el entorno físico —teniendo en cuenta la atenuación de paredes, alturas de techo y densidad de usuarios— permite a los arquitectos de red determinar la ubicación óptima de los AP y la asignación de canales. Esto mitiga la interferencia de co-canal y asegura una relación señal/ruido (SNR) suficiente en todo el lugar.
Fase 2: Configuración de la Infraestructura
Una vez que el hardware está físicamente implementado, configure el WLC para transmitir el SSID de invitados dedicado. Asegúrese de que la VLAN correspondiente esté correctamente etiquetada en todos los puertos troncales del switch. En el borde del firewall, verifique que los alcances de DHCP tengan el tamaño adecuado para el número esperado de usuarios concurrentes; una subred /24 (254 direcciones) rara vez es suficiente para lugares empresariales. Implemente el filtrado DNS para bloquear dominios maliciosos y contenido para adultos a nivel de red.
Fase 3: Integración del Captive Portal
El Captive Portal es el punto de integración crítico entre la infraestructura de red y lel objetivo de negocio. En lugar de una página de bienvenida genérica, el WLC está configurado para redirigir el tráfico de invitados no autenticados a un Captive Portal externo alojado por una plataforma de Guest WiFi como Purple.
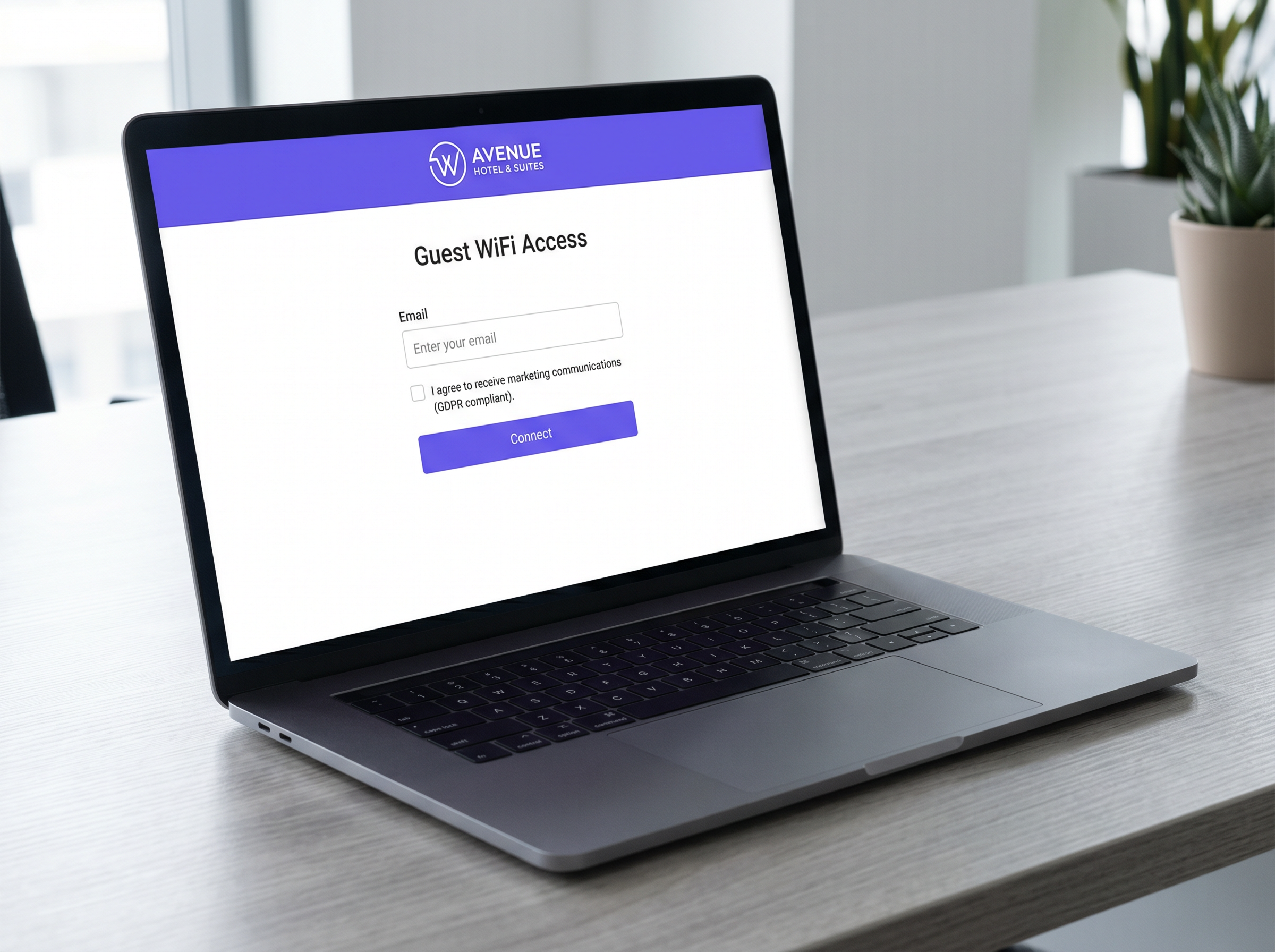
Este portal debe estar diseñado para autenticar a los usuarios a través de métodos estándar (correo electrónico, SMS, inicio de sesión social) mientras captura datos de primera parte. Fundamentalmente, el portal debe manejar los complejos requisitos de cumplimiento de GDPR, presentando opciones de consentimiento granular y registrando la marca de tiempo exacta y los términos acordados por el usuario.
Fase 4: Analítica y Automatización de Marketing
Una vez autenticada, la dirección MAC del dispositivo del usuario se asocia con su perfil demográfico. Estos datos fluyen a un panel de WiFi Analytics , proporcionando a TI visibilidad sobre los tiempos de permanencia y el flujo de visitantes, al tiempo que permite a los equipos de marketing activar campañas automatizadas basadas en la frecuencia de las visitas.
Mejores Prácticas y Cumplimiento
Adherirse a los estándares de la industria protege al negocio de multas regulatorias y daños a la reputación.
- Mecanismos de Consentimiento Explícito: Bajo GDPR y la Ley de Protección de Datos del Reino Unido, el consentimiento para las comunicaciones de marketing debe ser otorgado libremente, específico e inequívoco. Las casillas premarcadas en los Captive Portals están estrictamente prohibidas. La plataforma debe mantener un registro auditable de todas las transacciones de consentimiento.
- Políticas de Retención de Datos: Implemente políticas automatizadas de purga de datos. Los datos de los invitados no deben conservarse indefinidamente. Configure la plataforma de análisis para anonimizar o eliminar registros después de un período definido de inactividad (por ejemplo, 24 meses).
- Filtrado de Contenido: Las redes de cara al público deben implementar filtrado de contenido basado en DNS para prevenir el acceso a material ilegal o inapropiado, protegiendo el lugar de responsabilidad y asegurando un ambiente familiar.
Solución de Problemas y Mitigación de Riesgos
Incluso las redes bien diseñadas encuentran problemas. Comprender los modos de falla comunes acelera el tiempo de resolución.
Agotamiento de DHCP
Síntoma: Los invitados pueden asociarse con el AP pero reciben una dirección APIPA (169.254.x.x) y no pueden acceder al portal. Mitigación: Disminuya los tiempos de arrendamiento de DHCP (por ejemplo, a 2 horas en lugar de 24 horas) en entornos de alta rotación como tiendas minoristas. Asegúrese de que el tamaño de la subred coincida con las estimaciones de afluencia máxima.
Fallas de Intercepción del Captive Portal
Síntoma: Los invitados se conectan a la red pero el Captive Portal no aparece automáticamente (falla de CNA). Mitigación: Asegúrese de que el "Walled Garden" o las ACL de preautenticación en el WLC permitan el tráfico a las direcciones IP del Captive Portal y los dominios CDN necesarios. Si el sistema operativo no puede alcanzar su URL de detección de Captive Portal (por ejemplo, captive.apple.com), el portal no se activará.
Puntos de Acceso Maliciosos
Síntoma: APs no autorizados que transmiten SSIDs similares o están conectados a la LAN corporativa. Mitigación: Habilite los Sistemas de Detección de Intrusiones Inalámbricas (WIDS) en el WLC para detectar y contener automáticamente los APs maliciosos enviando tramas de desautenticación a los clientes conectados.
ROI e Impacto Comercial
La transición de una red estándar a una plataforma WiFi inteligente produce resultados comerciales medibles. Al aprovechar los datos capturados a través del Captive Portal, las empresas pueden generar ingresos tangibles.
Por ejemplo, en Atención Médica , la analítica puede optimizar el flujo de pacientes y reducir los tiempos de espera. En el comercio minorista, la integración de datos WiFi con sistemas CRM permite campañas de retargeting dirigidas, enviando una oferta promocional a un cliente que no ha visitado en 90 días. Además, la adopción de paradigmas de red modernos, como los discutidos en Los Beneficios Clave de SD WAN para Empresas Modernas , permite a los operadores multisitio gestionar centralmente estas políticas en cientos de ubicaciones, reduciendo significativamente los gastos operativos.
Términos clave y definiciones
VLAN (Virtual Local Area Network)
A logical grouping of network devices that acts as if they are on their own independent network, regardless of physical location.
Used to isolate guest WiFi traffic from corporate traffic on the same physical switches and access points.
Captive Portal
A web page that a user of a public-access network is obliged to view and interact with before access is granted.
The primary interface for authenticating users, capturing first-party marketing data, and securing GDPR consent.
Walled Garden
A limited environment that controls the user's access to web content and services before they have fully authenticated.
Essential for allowing devices to load the captive portal page and associated assets (like logos or social login APIs) before internet access is granted.
WPA3-SAE
Wi-Fi Protected Access 3 with Simultaneous Authentication of Equals. The modern standard for wireless encryption.
Replaces WPA2-PSK to provide forward secrecy, preventing attackers from decrypting captured traffic even if they later discover the network password.
OFDMA
Orthogonal Frequency Division Multiple Access. A feature of Wi-Fi 6 that allows an access point to divide a channel into smaller sub-channels.
Crucial for high-density venues (stadiums, conferences) as it allows simultaneous transmission to multiple clients, drastically reducing latency.
MAC Address
Media Access Control address. A unique identifier assigned to a network interface controller for use as a network address.
Used by analytics platforms to track unique device visits, dwell time, and return frequency, even before the user authenticates.
DHCP Exhaustion
A state where a network's DHCP server has no more IP addresses available to assign to new clients.
A common failure in retail environments where footfall is high but the IP subnet is too small or lease times are set too long.
PCI DSS
Payment Card Industry Data Security Standard. A set of security standards designed to ensure that all companies that accept, process, store or transmit credit card information maintain a secure environment.
The primary regulatory reason why guest WiFi must be strictly segmented from point-of-sale (POS) systems.
Casos de éxito
A 400-room luxury hotel is experiencing severe guest complaints regarding WiFi speeds during the evening hours (7 PM - 10 PM). The internet uplink is a dedicated 1 Gbps fibre circuit. Network monitoring shows the uplink is fully saturated during these times.
The IT team must implement per-device bandwidth rate limiting. On the Wireless LAN Controller or edge firewall, a QoS policy should be applied to the guest VLAN, capping individual client throughput to 15 Mbps download and 5 Mbps upload. Additionally, application-layer filtering should be enabled to throttle peer-to-peer (P2P) file sharing protocols.
A national retail chain wants to implement a captive portal to collect customer emails for marketing, but the legal team is concerned about GDPR compliance following recent ICO fines in the sector.
The deployment must utilize a dedicated Guest WiFi platform like Purple that handles consent natively. The captive portal must be configured with an unticked checkbox explicitly stating: 'I consent to receive marketing communications.' The platform must automatically record the user's MAC address, IP address, timestamp, and the exact text of the consent agreement. A secondary option to connect without providing marketing consent must be available.
Análisis de escenarios
Q1. A stadium IT director is planning a network upgrade for a 50,000-seat venue. The current Wi-Fi 5 (802.11ac) network collapses during half-time. They are considering deploying more APs of the same model to increase coverage. Do you agree with this approach?
💡 Sugerencia:Consider the difference between coverage and capacity, and how Wi-Fi 5 handles concurrent client transmissions.
Mostrar enfoque recomendado
No. Deploying more Wi-Fi 5 APs in a high-density environment will likely increase co-channel interference without solving the capacity issue. The venue requires an upgrade to Wi-Fi 6 (802.11ax) APs. The OFDMA technology in Wi-Fi 6 is specifically designed for high-density environments, allowing the AP to communicate with multiple clients simultaneously, rather than the sequential transmission limitation of Wi-Fi 5.
Q2. A retail client wants to use their guest WiFi to track how many people walk past their store versus how many enter, using MAC address probing. However, they are concerned about MAC randomization features in modern iOS and Android devices. How should you advise them?
💡 Sugerencia:Consider the limitations of passive tracking versus active authentication.
Mostrar enfoque recomendado
Advise the client that while passive MAC tracking (probing) can provide directional trends, MAC randomization significantly reduces its absolute accuracy for unique user counts. The architectural solution is to incentivize active connection to the captive portal. Once a user authenticates, the platform associates the current MAC address with a known identity (e.g., email), providing highly accurate analytics for that session.
Q3. During a network audit, you discover that the guest WiFi subnet (10.0.50.0/24) can ping the IP address of the venue's internal Active Directory server (10.0.10.5). What is the immediate architectural remediation?
💡 Sugerencia:Focus on Layer 3 routing and firewall policies.
Mostrar enfoque recomendado
Immediate remediation requires updating the Access Control Lists (ACLs) on the core firewall/router. A rule must be placed at the top of the ACL for the guest VLAN interface that explicitly denies all traffic destined for RFC 1918 private IP space (10.0.0.0/8, 172.16.0.0/12, 192.168.0.0/16), followed by a rule permitting traffic to the internet (0.0.0.0/0).



