WPA-PSK Explained: What It Is, How It Works, and Its Security Risks
This authoritative technical reference breaks down the mechanics of WPA-PSK — its 4-way handshake, cryptographic architecture, and inherent security vulnerabilities — and explains precisely why enterprise networks must transition to robust 802.1X or managed captive portal architectures. It provides actionable deployment guidance for IT leaders managing complex venue environments across hospitality, retail, events, and public-sector organisations.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive: How WPA-PSK Works
- The Cryptographic Foundation
- The 4-Way Handshake
- Where the Security Model Breaks Down
- Implementation Guide: Transitioning to Enterprise Security
- Step 1: Audit Your Current Network Estate
- Step 2: Separate Guest and Corporate Traffic
- Step 3: Deploy Managed Guest WiFi
- Step 4: Contain Legacy PSK Devices
- Step 5: Integrate with Modern Network Architecture
- Best Practices & Risk Mitigation
- ROI & Business Impact

Executive Summary
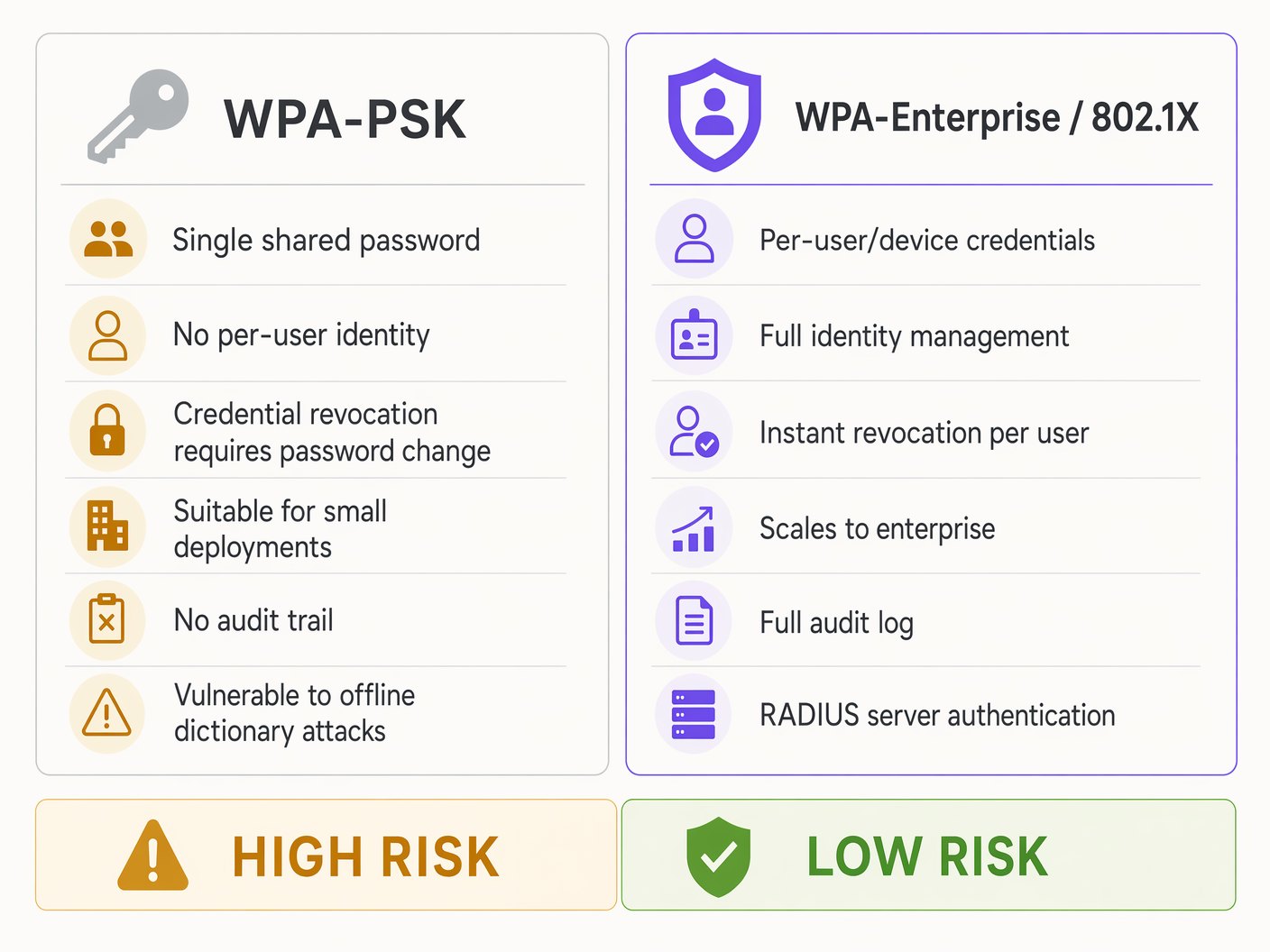
For IT managers and network architects operating at scale — whether across retail chains, hospitality venues, or large public-sector facilities — WiFi security cannot rely on consumer-grade mechanisms. WPA-PSK (WiFi Protected Access Pre-Shared Key) remains the default standard for home networks and small businesses, but its architectural limitations introduce unacceptable risks in enterprise environments.
While WPA-PSK is simple to deploy, relying on a single shared passphrase creates severe operational bottlenecks: credential revocation is impossible without network-wide disruption, user identity remains opaque, and the fundamental cryptography is vulnerable to offline dictionary attacks. This guide dissects the technical mechanics of WPA-PSK, explains exactly where its security model breaks down for business applications, and outlines the imperative shift towards WPA-Enterprise (802.1X) and robust Guest WiFi solutions.
By understanding these limitations, CTOs and venue operations directors can mitigate risk, ensure compliance with standards like PCI DSS and GDPR, and leverage platforms like Purple to transform a security liability into a managed, analytics-driven asset.
Technical Deep-Dive: How WPA-PSK Works
WPA-PSK was designed to provide strong encryption without the overhead of an authentication server. It relies on a Pre-Shared Key (PSK) — a password ranging from 8 to 63 characters — which is known to both the client device (supplicant) and the Access Point (authenticator).
The Cryptographic Foundation
The PSK is not used directly to encrypt data traffic. Instead, it serves as the seed material to generate a Pairwise Master Key (PMK). The PMK is calculated using the PBKDF2 (Password-Based Key Derivation Function 2) algorithm, hashing the passphrase along with the network's SSID 4,096 times. This computationally intensive process was designed to slow down brute-force attacks. However, modern GPU rigs can perform billions of hash operations per second, rendering this protection inadequate against a determined attacker with a captured handshake.
The 4-Way Handshake
Once the PMK is established, the client and the AP must prove they both know the PMK without ever transmitting it over the air. This is achieved through the 4-Way Handshake, which derives the Pairwise Transient Key (PTK) used for actual session encryption.
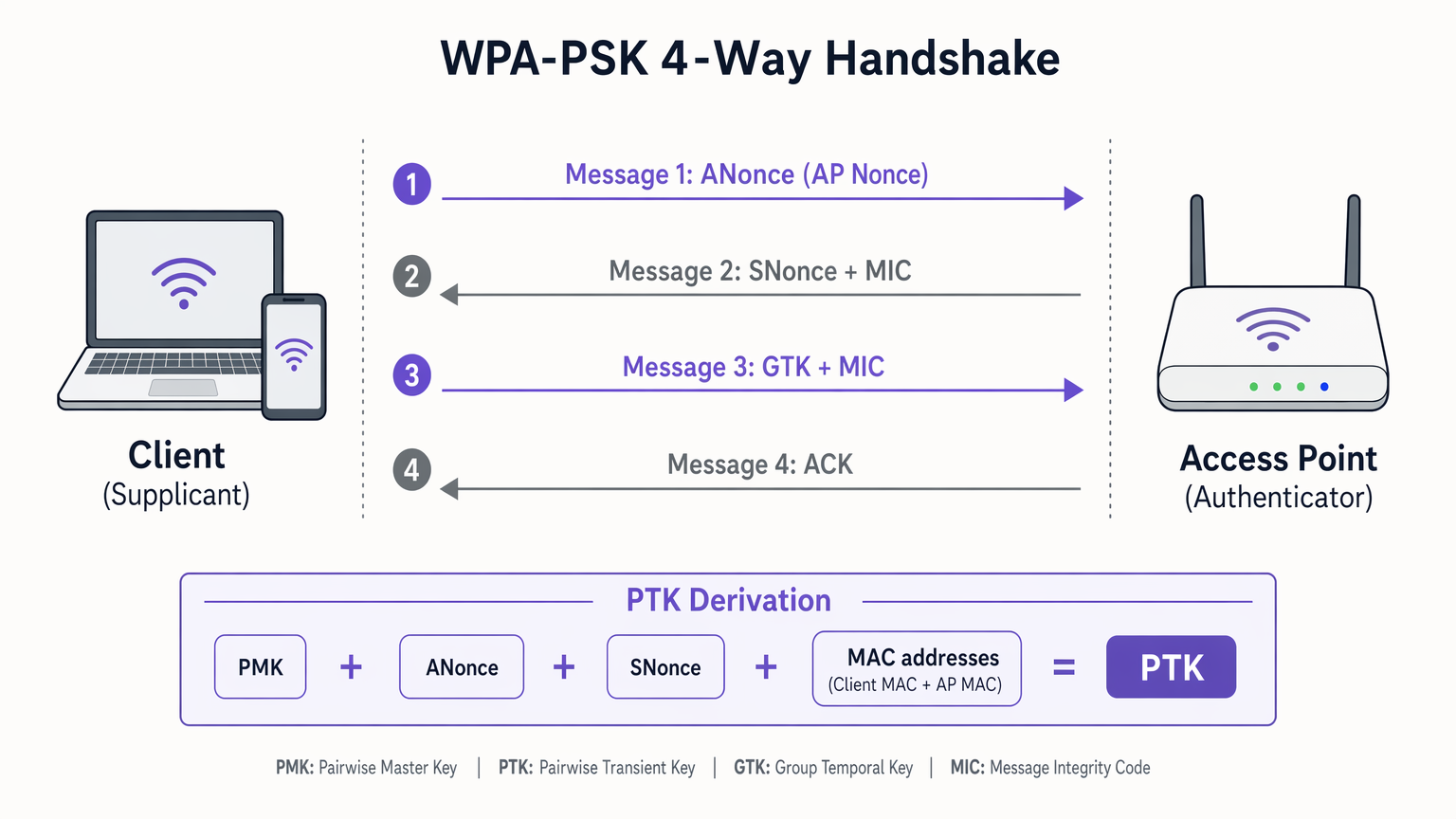
The handshake proceeds as follows. In Message 1, the AP sends a cryptographic nonce (ANonce) to the client. The client now has all the inputs needed — PMK, ANonce, its own SNonce, and both MAC addresses — to calculate the PTK. In Message 2, the client sends its own nonce (SNonce) to the AP, along with a Message Integrity Code (MIC) to prove it successfully generated the PTK. In Message 3, the AP verifies the MIC, generates the PTK, and sends the Group Temporal Key (GTK) — used for broadcast and multicast traffic — encrypted under the PTK. In Message 4, the client acknowledges receipt, and encrypted data transmission begins.
Where the Security Model Breaks Down
The fundamental flaw of WPA-PSK in an enterprise setting is not the encryption algorithm — AES-CCMP is highly secure — but the key management architecture.
First, offline dictionary attacks represent the primary cryptographic risk. If an attacker captures the 4-way handshake (which is transmitted in the clear), they can run offline brute-force attacks against the captured MIC. Since many venues use weak or predictable passwords, this is a trivial exercise for modern GPU rigs capable of billions of hash operations per second.
Second, the lack of user identity is a critical operational failure. WPA-PSK authenticates the device, not the user. An IP address and MAC address provide no verifiable identity, severely limiting WiFi Analytics and making incident response nearly impossible. Modern mobile operating systems (iOS 14+, Android 10+) also randomise MAC addresses by default, making even device-level tracking unreliable.
Third, the revocation problem creates an ongoing operational burden. When an employee leaves or a device is compromised, the only way to revoke access is to change the PSK on the AP and manually update every single legitimate client device. In a Retail environment with hundreds of locations and thousands of devices, this is operationally unfeasible — and in practice, passwords are rarely changed.
Implementation Guide: Transitioning to Enterprise Security
For enterprise environments, the migration from WPA-PSK to WPA-Enterprise (802.1X) is a critical security mandate. The following framework applies across Hospitality , Healthcare , Retail , and Transport deployments.
Step 1: Audit Your Current Network Estate
Begin with a comprehensive inventory. Identify every SSID, every authentication method, and every device type connecting to your network. Categorise devices into three groups: corporate managed assets, guest or visitor devices, and legacy or IoT devices. This segmentation drives every subsequent decision.
Step 2: Separate Guest and Corporate Traffic
Never use a PSK for corporate assets. Corporate devices must authenticate via 802.1X using RADIUS servers and EAP methods. EAP-TLS (certificate-based) is the gold standard for headless devices such as POS terminals, while PEAP-MSCHAPv2 is appropriate for user-facing devices tied to Active Directory accounts. For a detailed comparison of these protocols, refer to EAP-TLS vs. PEAP: ¿Qué protocolo de autenticación es el adecuado para su red? .
Step 3: Deploy Managed Guest WiFi
For public-facing networks, providing a static PSK is both a security and a marketing failure. Deploy an open SSID that redirects to a captive portal. Platforms like Purple integrate seamlessly with existing hardware to provide secure, identity-based access. Users authenticate via social login, email, or SMS, generating a unique session with a full audit trail — satisfying GDPR Article 32 requirements for appropriate technical security measures.
Step 4: Contain Legacy PSK Devices
For IoT devices or legacy hardware that cannot support 802.1X, containment is the strategy. Place all PSK devices on a dedicated, heavily restricted VLAN with no access to the corporate subnet. Enable client isolation to prevent lateral movement between devices. Use a complex, randomly generated passphrase of 20 or more characters, and establish a rotation schedule.
Step 5: Integrate with Modern Network Architecture
Modern network deployments must support dynamic security policies across distributed locations. Integrating robust WiFi security with SD-WAN ensures consistent policy enforcement from the edge to the core. Learn more about The Core SD WAN Benefits for Modern Businesses .
Best Practices & Risk Mitigation
The following table summarises the key risk mitigation controls for each network segment.
| Network Segment | Authentication Method | Key Controls | Compliance Relevance |
|---|---|---|---|
| Corporate Staff | WPA-Enterprise / 802.1X | RADIUS, EAP-TLS or PEAP, per-user revocation | PCI DSS Req. 8.2, ISO 27001 |
| Guest / Visitor | Open SSID + Captive Portal | Identity capture, bandwidth throttling, session logging | GDPR Art. 32, PCI DSS Req. 1.3 |
| IoT / Legacy | WPA-PSK (contained) | Isolated VLAN, client isolation, complex passphrase, rotation | PCI DSS Req. 1.3, network segmentation |
Beyond architecture, operational controls are equally important. Configure your Wireless Intrusion Detection System (WIDS) to alert on excessive deauthentication frames — a strong indicator of an active handshake-capture attack. If your hardware supports WPA3, enable Simultaneous Authentication of Equals (SAE) on any remaining PSK networks, as SAE provides forward secrecy and resistance to offline dictionary attacks even in PSK mode.
ROI & Business Impact
Moving away from WPA-PSK is not just a security upgrade; it is a strategic business enabler with measurable outcomes.
Reduced Operational Overhead: Helpdesk tickets related to WiFi password updates drop significantly when identity is managed centrally. In a retail estate with 500 locations, eliminating manual PSK rotation across thousands of devices can save hundreds of IT hours annually.
Compliance & Risk Mitigation: 802.1X and managed captive portals provide the per-user audit trails required by PCI DSS and GDPR. The cost of a PCI DSS non-compliance fine or a GDPR data breach notification far exceeds the investment in a proper authentication infrastructure.
Data Monetisation: Transitioning from a static PSK to a Purple-managed captive portal transforms WiFi from a cost centre into a revenue generator. Venues using Purple's platform capture opt-in first-party data, enabling targeted marketing campaigns, loyalty programme integration, and deep venue analytics including dwell time, footfall patterns, and repeat visit rates.
Key Definitions
Pre-Shared Key (PSK)
A static passphrase of 8 to 63 characters shared between the access point and all client devices, used as the seed material for generating encryption keys.
The primary vulnerability in small business and consumer networks. When one person knows the PSK, the entire network is potentially compromised, and revocation requires a network-wide password change.
Pairwise Master Key (PMK)
A 256-bit key derived from the PSK and the network SSID using the PBKDF2 hashing algorithm, run 4,096 times.
The PMK is the top-level key in the WPA architecture. Because it incorporates the SSID, changing the network name requires recalculating the PMK on all devices.
4-Way Handshake
The cryptographic exchange where the AP and client swap nonces to independently calculate the session encryption key without transmitting the master key over the air.
The critical phase where offline dictionary attacks occur. If an attacker captures this handshake, they can attempt to crack the PSK entirely offline, with no network interaction required.
Pairwise Transient Key (PTK)
The temporary per-session encryption key generated during the 4-way handshake, used to encrypt unicast data traffic between a specific client and the AP.
Ensures that even though all users share the same PSK, they cannot easily decrypt each other's unicast traffic — though this protection is undermined if the PSK is cracked.
Message Integrity Code (MIC)
A cryptographic checksum transmitted during the handshake to prove that the sender possesses the correct PMK and has successfully calculated the PTK.
The MIC is the target of offline dictionary attacks. Attackers capture the MIC and use brute-force tools to generate matching MICs, thereby discovering the original PSK.
WPA-Enterprise / 802.1X
An IEEE standard for port-based network access control that provides an authentication mechanism requiring each user or device to authenticate individually against a RADIUS server using an EAP method.
The necessary upgrade path for enterprises moving away from WPA-PSK. Provides per-user identity, instant revocation, and a full audit trail.
Captive Portal
A web page that a user of a public-access network is required to interact with before network access is granted, typically used to capture identity, enforce terms of service, and apply access policies.
The modern alternative to providing a static PSK to guests. Enables identity capture, GDPR-compliant consent collection, bandwidth management, and marketing analytics integration.
Deauthentication Attack
A denial-of-service attack where forged 802.11 management frames are sent to force a client to disconnect from the AP, causing it to reconnect and perform a new 4-way handshake.
Used by attackers to actively generate handshake traffic for capture. Detection requires a Wireless Intrusion Detection System (WIDS) monitoring for abnormal deauthentication frame volumes.
RADIUS (Remote Authentication Dial-In User Service)
A networking protocol that provides centralised authentication, authorisation, and accounting (AAA) management for users connecting to a network service.
The core infrastructure component required for WPA-Enterprise deployments. Can be cloud-hosted or on-premises, and integrates with identity providers such as Active Directory, Azure AD, or Okta.
Worked Examples
A national retail chain with 500 locations currently uses a single WPA-PSK for all point-of-sale (POS) terminals and handheld inventory scanners. They have experienced high staff turnover and are preparing for a PCI DSS compliance audit. How should the network architecture be redesigned?
- Deploy a cloud-managed RADIUS server integrated with the corporate Identity Provider (IdP), such as Azure AD or Okta.
- Configure the APs to broadcast a dedicated corporate SSID using WPA-Enterprise (802.1X).
- Provision POS terminals with EAP-TLS (certificate-based authentication) to eliminate passwords entirely — certificates are provisioned via an MDM platform.
- Provision inventory scanners using PEAP-MSCHAPv2 tied to individual employee accounts in Active Directory.
- Retire the old WPA-PSK SSID for all corporate devices.
- If legacy scanners cannot support 802.1X, isolate them on a dedicated VLAN with MAC filtering and a highly complex, unique PSK per store — and document this as a compensating control in the PCI DSS audit.
- Deploy a separate guest SSID with a captive portal for customer-facing WiFi, ensuring complete network segmentation from the corporate environment.
A large conference centre provides WiFi to attendees by printing a WPA-PSK on the back of event badges. The IT team is dealing with bandwidth exhaustion, cannot identify malicious users, and is missing out on attendee engagement data. What is the recommended deployment?
- Remove the WPA-PSK requirement and transition to an Open SSID for all attendees.
- Implement a captive portal solution (such as Purple) for guest access, requiring authentication via email, social login, or SMS validation.
- Apply per-user bandwidth throttling policies through the portal to prevent any single user from exhausting available throughput.
- Configure content filtering to block known malicious domains and peer-to-peer traffic.
- Integrate the portal with the event's CRM or marketing automation platform to capture attendee demographics and consent.
- Enable Purple's analytics dashboard to monitor real-time footfall, dwell time by zone, and return visitor rates.
- Maintain the existing WPA-Enterprise SSID for event staff and AV equipment, ensuring complete separation from the attendee network.
Practice Questions
Q1. A stadium IT director proposes using a WPA-PSK network for the press box, changing the password before every match to maintain security. What is the primary operational risk of this approach, and what alternative architecture would you recommend?
Hint: Consider the workflow required when a journalist arrives late, needs to connect a secondary device mid-match, or when a credential is shared beyond the intended recipients.
View model answer
The primary operational risk is the support bottleneck and lack of identity it creates. Every journalist must manually enter the new password, leading to support calls and delays during a time-critical event. More critically, there is no audit trail to identify which specific individual is consuming excessive bandwidth or attempting malicious activity. The recommended architecture is a dedicated SSID for accredited press using a captive portal with pre-issued credentials tied to individual media accreditation IDs, or a WPA-Enterprise SSID using PEAP tied to a temporary RADIUS account provisioned for each accredited journalist. This provides individual accountability, instant revocation, and bandwidth management per user.
Q2. During a penetration test, a tester captures the 4-way handshake of your WPA-PSK network and cracks the password offline within four hours using a GPU rig. How does migrating to WPA-Enterprise (802.1X) using PEAP prevent this specific attack vector?
Hint: Consider how the authentication tunnel is established in PEAP before any user credentials are exchanged, and what an attacker would capture from the wireless frames.
View model answer
WPA-Enterprise using PEAP (Protected Extensible Authentication Protocol) establishes an encrypted TLS tunnel between the client and the RADIUS server before any user credentials are exchanged. The user authentication happens inside this secure tunnel. Therefore, even if an attacker captures all wireless frames during the association process, they cannot perform an offline dictionary attack against the credentials — the credentials are protected by the server's TLS certificate. The attacker would need to compromise the RADIUS server's private key to decrypt the tunnel, which is a fundamentally different and far more difficult attack surface.
Q3. A hotel chain wants to improve its guest WiFi analytics to understand dwell times and repeat visit rates, but currently uses a static WPA-PSK for all guest rooms. Why does the PSK model prevent effective analytics, and what specific data does a captive portal solution unlock?
Hint: Consider what data is visible to the network when a device connects using a shared key versus an individualised portal login, and how modern mobile OS privacy features affect MAC-based tracking.
View model answer
WPA-PSK only authenticates the device's MAC address, which is randomised by default on iOS 14+ and Android 10+ for privacy. Because all guests share the same key, the network has no way to link a specific device to a specific guest identity. Even if MAC randomisation were not a factor, a MAC address provides no demographic or identity data. Moving to a captive portal unlocks explicit first-party data: name, email address, loyalty programme ID, marketing consent, and demographic information provided at login. This ties every session to a known user profile, enabling accurate dwell time measurement, repeat visit identification, segmented marketing campaigns, and integration with the hotel's CRM and loyalty platform.
Continue reading in this series
Staff WiFi Terms and Conditions: Legal and Compliance Essentials
This guide covers the legal and technical essentials of drafting and enforcing staff WiFi terms and conditions for enterprise venues. It details what to include in an Acceptable Use Policy (AUP), how to meet GDPR and PCI DSS requirements, and how to deploy identity-based authentication and network segmentation to protect corporate assets. IT managers, HR teams, and operations directors at hotels, retail chains, stadiums, and public-sector organisations will find actionable guidance they can implement this quarter.
Staff WiFi Policies for Retail: Securing Back-of-House Networks
This guide covers the critical technical and policy requirements for securing retail back-of-house WiFi networks - from VLAN segmentation and PCI DSS 4.0 compliance to managing employee BYOD on the shop floor. It gives IT managers, network architects, and operations directors a practical, vendor-neutral blueprint they can act on this quarter.
The Future of Wi-Fi Security: AI-Driven NAC and Threat Detection
This authoritative guide explores the evolution of enterprise Wi-Fi security from legacy WPA2 to AI-driven Network Access Control (NAC) and threat detection. Designed for IT leaders, it provides actionable deployment strategies for securing high-density environments like retail, hospitality, and stadiums using Purple's identity-based networks.