Casos de uso de WiFi para invitados: Cómo diferentes industrias están utilizando el WiFi gratuito
Una referencia técnica exhaustiva para líderes de TI sobre la implementación de WiFi para invitados como una plataforma estratégica de adquisición de datos y análisis. Esta guía cubre la arquitectura, los casos de uso específicos de la industria y las mejores prácticas para transformar la conectividad en valor empresarial medible.
🎧 Escuchar esta guía
Ver transcripción
- Resumen Ejecutivo
- Análisis Técnico en Profundidad
- Arquitectura de Red y Estándares de Seguridad
- La Capa de Identidad y Análisis
- Guía de Implementación: Casos de Uso por Industria
- Comercio Minorista: Análisis de Tráfico Peatonal y Tiempo de Permanencia
- Hostelería: Conectividad Fluida y Engagement Contextual
- Recintos y Eventos: Alta Densidad "Análisis de multitudes
- Sanidad: Segmentación de Grado de Cumplimiento
- Transporte: Experiencia del Pasajero y Mapeo de Trayectos
- Mejores Prácticas
- Resolución de Problemas y Mitigación de Riesgos
- ROI e Impacto Empresarial

Resumen Ejecutivo
Para las empresas modernas, proporcionar WiFi gratuito para invitados ya no es un centro de costes, es un canal crítico de adquisición de datos. Esta guía examina cómo los gerentes de TI, arquitectos de red y CTOs de los sectores minorista, hotelero, sanitario, de recintos y transporte están transformando la conectividad estándar en inteligencia empresarial accionable. Al implementar mecanismos de autenticación avanzados, una segmentación de red robusta y plataformas de análisis integradas, las organizaciones pueden capturar datos de primera parte con consentimiento, medir el tráfico peatonal físico e impulsar los ingresos a través de la reinteracción dirigida.
Este documento de referencia proporciona un análisis técnico en profundidad de la arquitectura necesaria para soportar estos casos de uso, desde los estándares 802.1X y WPA3 hasta el diseño de Captive Portal y el cumplimiento de GDPR. Describe estrategias de implementación neutrales respecto al proveedor y destaca cómo plataformas como Guest WiFi y WiFi Analytics de Purple se alinean directamente con los resultados comerciales. Ya sea que esté gestionando una implementación en un estadio de alta densidad o una red minorista distribuida, esta guía ofrece la orientación práctica y arquitectónica necesaria para optimizar su infraestructura inalámbrica.
Análisis Técnico en Profundidad
La brecha entre una implementación básica de WiFi gratuito y una plataforma de inteligencia de invitados completamente instrumentada es significativa. Una arquitectura robusta requiere una orquestación cuidadosa a través de tres capas principales: la capa de red, la capa de identidad y la capa de análisis.
Arquitectura de Red y Estándares de Seguridad
En la base, la capa de red debe proporcionar un rendimiento fiable manteniendo un aislamiento estricto. Las redes de invitados empresariales deben aprovechar WPA3-SAE (Simultaneous Authentication of Equals) para una mayor fortaleza criptográfica contra ataques de diccionario offline. Para entornos que requieren la aplicación de políticas por usuario, IEEE 802.1X con autenticación basada en RADIUS es el estándar. Sin embargo, para implementaciones orientadas al consumidor donde el aprovisionamiento de dispositivos es poco práctico, el Captive Portal sigue siendo el mecanismo principal para la captura de identidad y la aceptación de políticas.
La segmentación estricta de la red es innegociable. El tráfico de invitados debe aislarse en VLANs dedicadas, con políticas de enrutamiento entre VLANs aplicadas por firewalls con estado para evitar el movimiento lateral hacia entornos corporativos o de punto de venta (POS). Esto es particularmente crítico en el comercio minorista y la atención médica, donde el cumplimiento de PCI DSS y HIPAA/GDPR exige la protección de los datos de los titulares de tarjetas y de los pacientes.
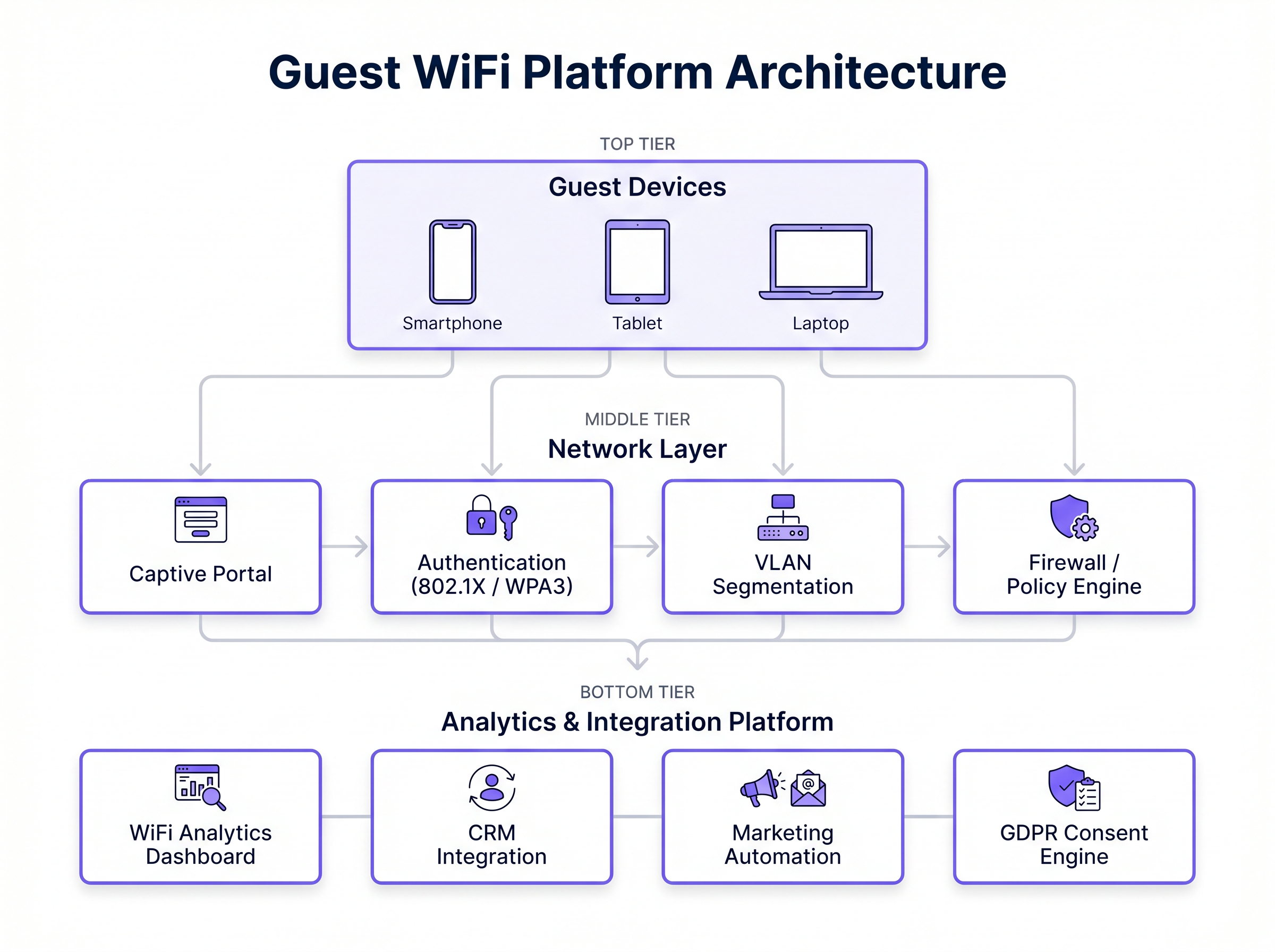
La Capa de Identidad y Análisis
El valor comercial de una red WiFi para invitados se captura en la capa de identidad. Un Captive Portal bien diseñado actúa como un motor de adquisición de datos, capturando identidades autenticadas (a través de correo electrónico, SMS o OAuth social) y registrando el consentimiento explícito para comunicaciones de marketing. Estos datos deben fluir sin problemas a la capa de análisis.
Plataformas como WiFi Analytics de Purple agregan eventos de conexión, datos de sondeo RSSI (Received Signal Strength Indicator) y perfiles autenticados. Esto permite la resolución de identidad entre recintos —permitiendo a un minorista reconocer a un cliente recurrente en diferentes ubicaciones de tiendas— y proporciona la base de datos para integraciones CRM automatizadas y campañas de marketing dirigidas. Además, Purple actúa como un proveedor de identidad gratuito para servicios como OpenRoaming bajo la licencia Connect, agilizando el proceso de autenticación para usuarios recurrentes.
Guía de Implementación: Casos de Uso por Industria
Diferentes verticales tienen requisitos y restricciones arquitectónicas distintas al implementar WiFi para invitados. A continuación, se presenta un análisis de cómo industrias específicas están aprovechando la infraestructura inalámbrica para impulsar el valor empresarial.
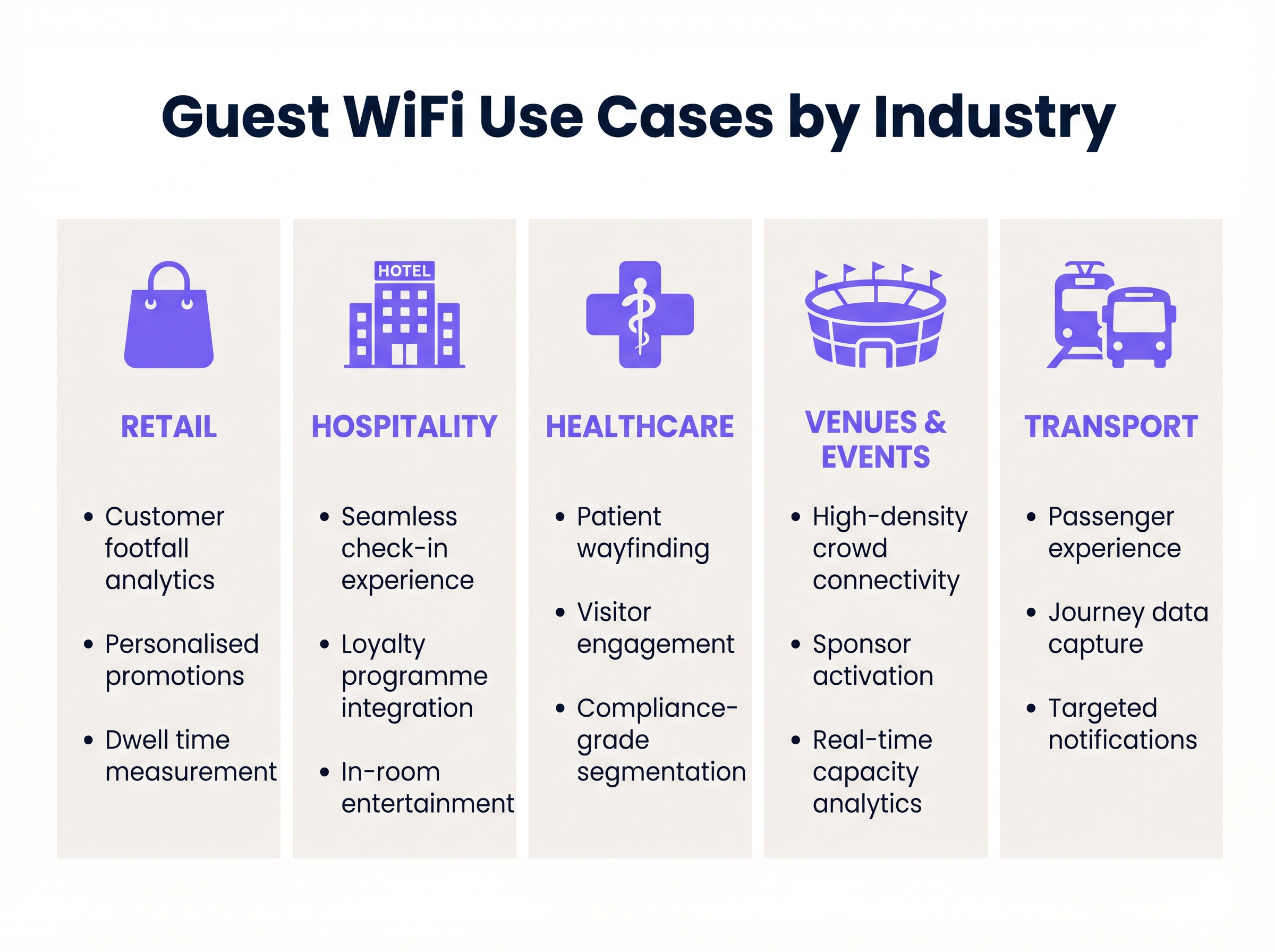
Comercio Minorista: Análisis de Tráfico Peatonal y Tiempo de Permanencia
En el sector minorista , el objetivo principal es comprender el comportamiento físico del cliente. Al capturar solicitudes de sondeo no autenticadas y datos de sesión autenticados, los minoristas pueden medir el tráfico peatonal, rastrear el tiempo de permanencia en zonas específicas de la tienda y analizar las tasas de conversión.
Estrategia de Implementación: Implementar puntos de acceso con radios de escaneo dedicadas para capturar solicitudes de sondeo pasivas. Integrar el Captive Portal con el CRM central para permitir la elaboración de perfiles progresiva. Cuando un cliente se autentica, el sistema debe activar un webhook a la plataforma de automatización de marketing, permitiendo campañas de reinteracción personalizadas basadas en su comportamiento en la tienda.
Hostelería: Conectividad Fluida y Engagement Contextual
Para entornos de hostelería , la conectividad fiable es la base. El caso de uso avanzado implica integrar el flujo de autenticación WiFi con el Sistema de Gestión de Propiedades (PMS).
Estrategia de Implementación: Configurar el Captive Portal para consultar el PMS a través de API. Cuando un huésped introduce su número de habitación y apellido, el sistema valida las credenciales y proporciona acceso durante la duración de su estancia. En un entorno de resort con WiFi, el análisis basado en la ubicación puede activar ofertas contextuales —por ejemplo, enviar una promoción de spa a un huésped que ha estado en la zona de la piscina durante un período prolongado.
Recintos y Eventos: Alta Densidad "Análisis de multitudes
Los estadios y centros de conferencias se enfrentan al desafío de una densidad de clientes extrema. Un despliegue de WiFi en un zoológico o parque temático comparte características similares, requiriendo una planificación RF cuidadosa para manejar conexiones concurrentes masivas.
Estrategia de Implementación: Utilice antenas direccionales y un balanceo de carga agresivo para gestionar la distribución de clientes entre los puntos de acceso. Implemente captive portals con la marca del patrocinador para generar ingresos publicitarios inmediatos. Después del evento, los datos de primera mano capturados (direcciones de correo electrónico y datos demográficos) se convierten en un activo crítico para futuras ventas de entradas y promociones de mercancía.
Sanidad: Segmentación de Grado de Cumplimiento
En Sanidad , el enfoque está en la eficiencia operativa y el estricto cumplimiento normativo. Las redes de invitados deben estar completamente segregadas de los sistemas clínicos.
Estrategia de Implementación: Implemente un estricto aislamiento de VLAN y filtrado de contenido web. El captive portal debe incluir flujos de consentimiento GDPR robustos, separando claramente la aceptación de los términos de servicio de las suscripciones de marketing, según lo exige el Data Security and Protection Toolkit. Los casos de uso incluyen la orientación de pacientes mediante mapas interiores y el acceso a recursos de salud digitales.
Transporte: Experiencia del Pasajero y Mapeo de Trayectos
Para el sector Transporte , el WiFi para invitados mejora la experiencia del pasajero al tiempo que genera valiosos datos de trayecto.
Estrategia de Implementación: Despliegue puntos de acceso móviles con backhaul celular (por ejemplo, routers SD-WAN) en trenes o autobuses. Para comprender la arquitectura de red necesaria para entornos distribuidos, revise Los beneficios clave de SD-WAN para empresas modernas . La plataforma de análisis puede correlacionar los datos de conexión con los sistemas de venta de billetes para mapear los flujos de pasajeros y optimizar la planificación de rutas.
Mejores Prácticas
Al diseñar y desplegar una solución de WiFi para invitados, los equipos de TI deben adherirse a los siguientes principios:
- Priorice la Experiencia de Usuario (UX) en el Portal: El captive portal es la puerta de entrada digital. Asegúrese de que sea responsivo, cargue rápidamente y funcione sin problemas en dispositivos iOS, Android y Windows. Para obtener orientación sobre el diseño del portal, consulte Cómo crear una página de inicio de sesión WiFi para invitados .
- Diseñe para la Escalabilidad: Diseñe la red para la capacidad máxima (el percentil 95), no para la carga promedio. Esto requiere estudios de sitio RF exhaustivos y planificación de capacidad, particularmente en entornos de alta densidad.
- Implemente una Gobernanza de Datos Robusta: Trate los datos de los invitados como un activo altamente sensible. Implemente políticas automatizadas de retención de datos, asegure mecanismos de consentimiento claros e integre una Plataforma de Gestión de Consentimientos (CMP) para manejar las solicitudes de acceso de los interesados (DSARs).
- Automatice las Integraciones: No deje los datos aislados en el controlador WiFi. Utilice APIs y webhooks para transmitir eventos de autenticación y datos de ubicación directamente a sus plataformas CRM y de marketing en tiempo real.
Resolución de Problemas y Mitigación de Riesgos
El despliegue de WiFi para invitados empresarial implica riesgos inherentes. Los modos de fallo más comunes y sus mitigaciones incluyen:
- No Aparición del Captive Portal: Esto a menudo ocurre debido a una interceptación DNS agresiva o políticas estrictas de inspección HTTPS. Mitigación: Asegúrese de que la configuración de Walled Garden permita el acceso a los proveedores de identidad necesarios (por ejemplo, Google, Facebook) y al dominio de alojamiento del portal antes de que se complete la autenticación.
- Fuga de VLAN: Los puertos de switch mal configurados pueden permitir que el tráfico de invitados atraviese las redes corporativas. Mitigación: Realice pruebas de penetración regulares y auditorías de configuración automatizadas para verificar el aislamiento de VLAN.
- Aleatorización de MAC: Los sistemas operativos móviles modernos emplean la aleatorización de direcciones MAC para proteger la privacidad del usuario, lo que complica el seguimiento entre visitas. Mitigación: Cambie la dependencia de los identificadores a nivel de dispositivo (direcciones MAC) a identidades de usuario autenticadas capturadas a través del captive portal.
ROI e Impacto Empresarial
El retorno de la inversión (ROI) para un despliegue de WiFi para invitados debe medirse en dos ejes: ahorros operativos y generación de ingresos.
Operativamente, la autenticación automatizada (por ejemplo, la integración de PMS en hoteles) reduce los tickets de soporte relacionados con el acceso WiFi. Comercialmente, la plataforma actúa como una herramienta de generación de leads de alto volumen. Al calcular el Coste por Adquisición (CPA) de una dirección de correo electrónico a través de canales de marketing digital tradicionales frente al coste de capturarla a través del portal WiFi para invitados, las organizaciones suelen demostrar un ROI positivo en un plazo de 6 a 12 meses. Además, los conocimientos derivados del análisis de afluencia permiten tomar decisiones basadas en datos sobre los niveles de personal, la distribución de las tiendas y las negociaciones de arrendamiento, amplificando el impacto empresarial general.
Términos clave y definiciones
Captive Portal
A web page that a user of a public access network is obliged to view and interact with before access is granted. It is the primary mechanism for authentication and terms acceptance.
Critical for capturing first-party data and ensuring users agree to terms of service before consuming bandwidth.
WPA3-SAE
Wi-Fi Protected Access 3 with Simultaneous Authentication of Equals. A security standard that provides robust protection against offline dictionary attacks.
The recommended security standard for modern enterprise guest networks to ensure cryptographic integrity.
MAC Randomisation
A privacy feature in modern mobile operating systems that generates a temporary MAC address for each network connection.
Complicates tracking users based solely on device hardware identifiers, making authenticated captive portal logins essential for persistent tracking.
RSSI (Received Signal Strength Indicator)
A measurement of the power present in a received radio signal.
Used in WiFi analytics to estimate the distance of a device from an access point, enabling location-based services and dwell time calculations.
Walled Garden
A limited environment that controls the user's access to web content and services before they have fully authenticated.
Must be carefully configured to allow access to necessary identity providers (like Google or Facebook for social login) before the user is granted full internet access.
VLAN Segmentation
The practice of dividing a physical network into multiple logical networks to isolate traffic.
Essential for security and compliance, ensuring guest traffic cannot route to corporate or POS systems.
Cross-Venue Identity Resolution
The ability to recognise a returning user across different physical locations within the same brand or estate.
Enables retailers and hospitality groups to build a unified customer profile and trigger consistent marketing campaigns regardless of which location the guest visits.
Progressive Profiling
A method of gradually gathering information about a user across multiple interactions rather than asking for all data upfront.
Used in captive portals to improve conversion rates; a user might provide just an email on their first visit, and a phone number on their second.
Casos de éxito
A 200-room hotel needs to implement a guest WiFi solution that provides seamless connectivity while capturing first-party data for the marketing team, without increasing the burden on the front desk.
Deploy a WPA3-enabled network with a captive portal integrated directly into the hotel's Property Management System (PMS) via API. Configure the Walled Garden to allow access to the PMS authentication endpoint. When a guest connects, they enter their room number and surname. The portal queries the PMS; upon validation, the device's MAC address is whitelisted for the duration of the stay. Simultaneously, the portal presents a GDPR-compliant opt-in for marketing communications, syncing consented profiles directly to the hotel's CRM.
A national retail chain requires visibility into store conversion rates (footfall vs. transactions) and wants to trigger personalised offers to returning customers based on their previous visits.
Implement access points with dedicated scanning radios to capture passive probe requests for baseline footfall metrics. Deploy a centralised captive portal with social login (OAuth) to capture authenticated identities. Configure cross-venue identity resolution in the central analytics platform. Set up webhooks to trigger an event in the marketing automation platform whenever a known device connects, allowing for real-time, personalised email or SMS offers based on the customer's purchase history.
Análisis de escenarios
Q1. A hospital IT director wants to provide free WiFi to patients and visitors but is concerned about HIPAA/GDPR compliance and the security of clinical systems. What is the most critical architectural requirement?
💡 Sugerencia:Consider how network traffic is isolated at Layer 2 and Layer 3.
Mostrar enfoque recomendado
The most critical requirement is strict network segmentation. Guest traffic must be placed on a dedicated VLAN that is completely isolated from clinical networks. Inter-VLAN routing must be blocked by stateful firewall policies, ensuring that a compromised guest device cannot access patient records or medical equipment.
Q2. A retail marketing team complains that their WiFi analytics dashboard shows a high number of 'visitors' but very few actionable customer profiles. What technical limitation is likely causing this, and how should the IT team resolve it?
💡 Sugerencia:Think about how modern smartphones handle their hardware identifiers when scanning for networks.
Mostrar enfoque recomendado
The dashboard is likely relying on passive probe requests, which are subject to MAC address randomisation by modern mobile operating systems (iOS/Android). This inflates visitor counts with temporary MACs and prevents profile building. The IT team must implement a captive portal to force authentication, capturing a persistent identity (like an email address) rather than relying on hardware MAC addresses.
Q3. During a major sporting event, the stadium's guest WiFi network becomes unresponsive. The access points are online, but users cannot reach the captive portal to log in. What is the most likely configuration issue?
💡 Sugerencia:Consider the dependencies required for a device to resolve and load an external web page before authentication.
Mostrar enfoque recomendado
The most likely issue is an incorrectly configured Walled Garden or DNS interception failure. If the Walled Garden does not permit access to the DNS servers, the captive portal hosting domain, or the required external Identity Providers (e.g., Google/Facebook for social login), the device cannot load the portal page, resulting in a denial of service for new connections.



