Guest WiFi Use Cases: How Different Industries Are Using Free WiFi
A comprehensive technical reference for IT leaders on deploying guest WiFi as a strategic data acquisition and analytics platform. This guide covers architecture, industry-specific use cases, and best practices for transforming connectivity into measurable business value.
🎧 Listen to this Guide
View Transcript
- Executive Summary
- Technical Deep-Dive
- Network Architecture and Security Standards
- The Identity and Analytics Layer
- Implementation Guide: Industry Use Cases
- Retail: Footfall Analytics and Dwell Time
- Hospitality: Seamless Connectivity and Contextual Engagement
- Venues and Events: High-Density Crowd Analytics
- Healthcare: Compliance-Grade Segmentation
- Transport: Passenger Experience and Journey Mapping
- Best Practices
- Troubleshooting & Risk Mitigation
- ROI & Business Impact

Executive Summary
For modern enterprises, providing free guest WiFi is no longer a cost centre—it is a critical data acquisition channel. This guide examines how IT managers, network architects, and CTOs across retail, hospitality, healthcare, venues, and transport are transforming standard connectivity into actionable business intelligence. By deploying advanced authentication mechanisms, robust network segmentation, and integrated analytics platforms, organisations can capture consented first-party data, measure physical footfall, and drive revenue through targeted re-engagement.
This reference document provides a technical deep-dive into the architecture required to support these use cases, from 802.1X and WPA3 standards to captive portal design and GDPR compliance. It outlines vendor-neutral implementation strategies and highlights how platforms like Purple's Guest WiFi and WiFi Analytics map directly to commercial outcomes. Whether you are managing a high-density stadium deployment or a distributed retail estate, this guide delivers the practical, architectural guidance needed to optimise your wireless infrastructure.
Technical Deep-Dive
The gap between a basic free WiFi deployment and a fully instrumented guest intelligence platform is significant. A robust architecture requires careful orchestration across three primary layers: the network layer, the identity layer, and the analytics layer.
Network Architecture and Security Standards
At the foundation, the network layer must provide reliable throughput while maintaining strict isolation. Enterprise guest networks should leverage WPA3-SAE (Simultaneous Authentication of Equals) for enhanced cryptographic strength against offline dictionary attacks. For environments requiring per-user policy enforcement, IEEE 802.1X with RADIUS-based authentication is the standard. However, for consumer-facing deployments where device provisioning is impractical, the captive portal remains the primary mechanism for identity capture and policy acceptance.
Strict network segmentation is non-negotiable. Guest traffic must be isolated into dedicated VLANs, with inter-VLAN routing policies enforced by stateful firewalls to prevent lateral movement into corporate or point-of-sale (POS) environments. This is particularly critical in retail and healthcare, where PCI DSS and HIPAA/GDPR compliance mandate the protection of cardholder and patient data.
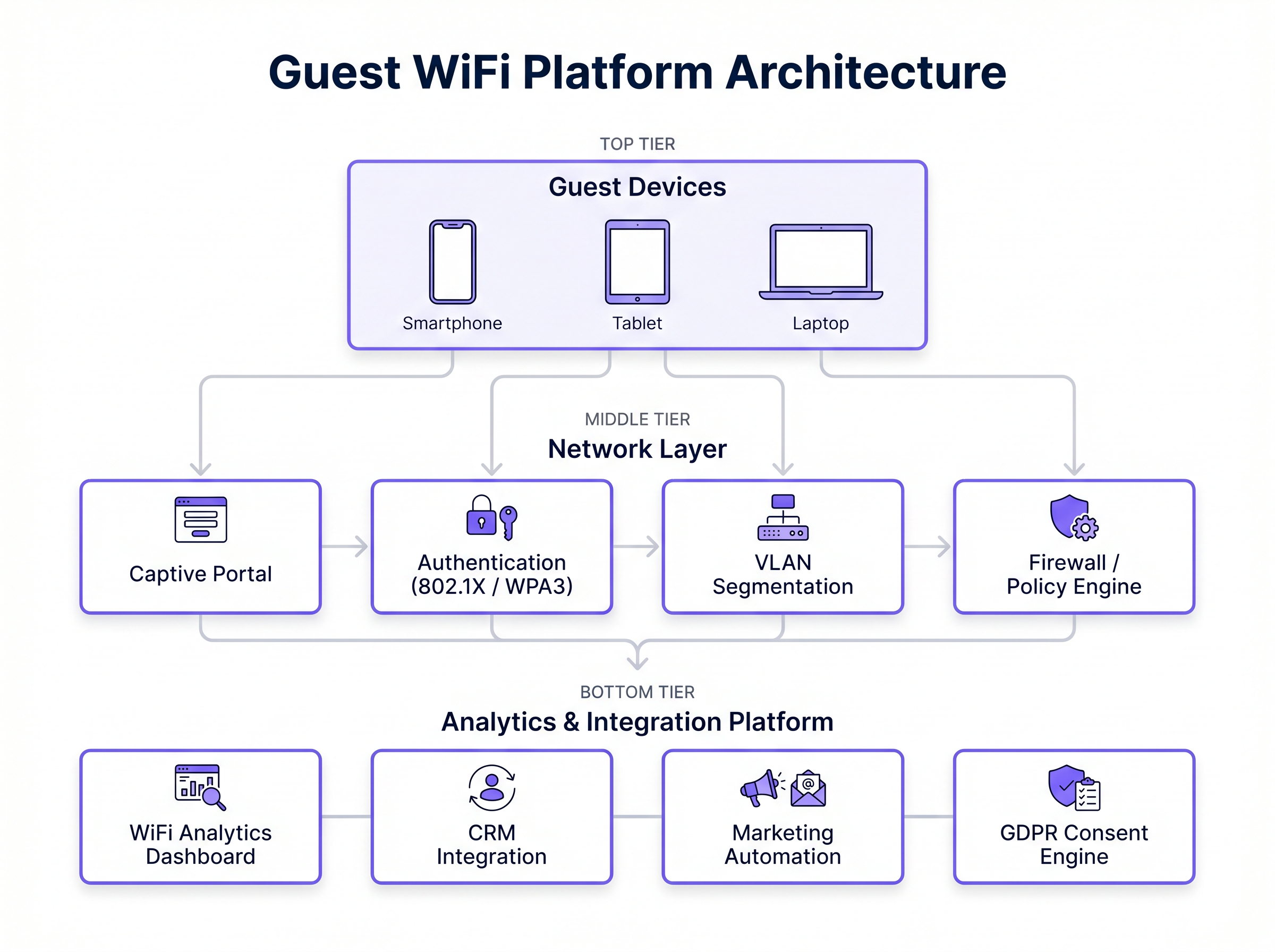
The Identity and Analytics Layer
The commercial value of a guest WiFi network is captured at the identity layer. A well-designed captive portal acts as a data acquisition engine, capturing authenticated identities (via email, SMS, or social OAuth) and recording explicit consent for marketing communications. This data must then flow seamlessly into the analytics layer.
Platforms like Purple's WiFi Analytics aggregate connection events, RSSI (Received Signal Strength Indicator) probe data, and authenticated profiles. This enables cross-venue identity resolution—allowing a retailer to recognise a returning customer across different store locations—and provides the data foundation for automated CRM integrations and targeted marketing campaigns. Furthermore, Purple acts as a free identity provider for services like OpenRoaming under the Connect license, streamlining the authentication process for returning users.
Implementation Guide: Industry Use Cases
Different verticals have distinct requirements and architectural constraints when deploying guest WiFi. Below is an analysis of how specific industries are leveraging wireless infrastructure to drive business value.
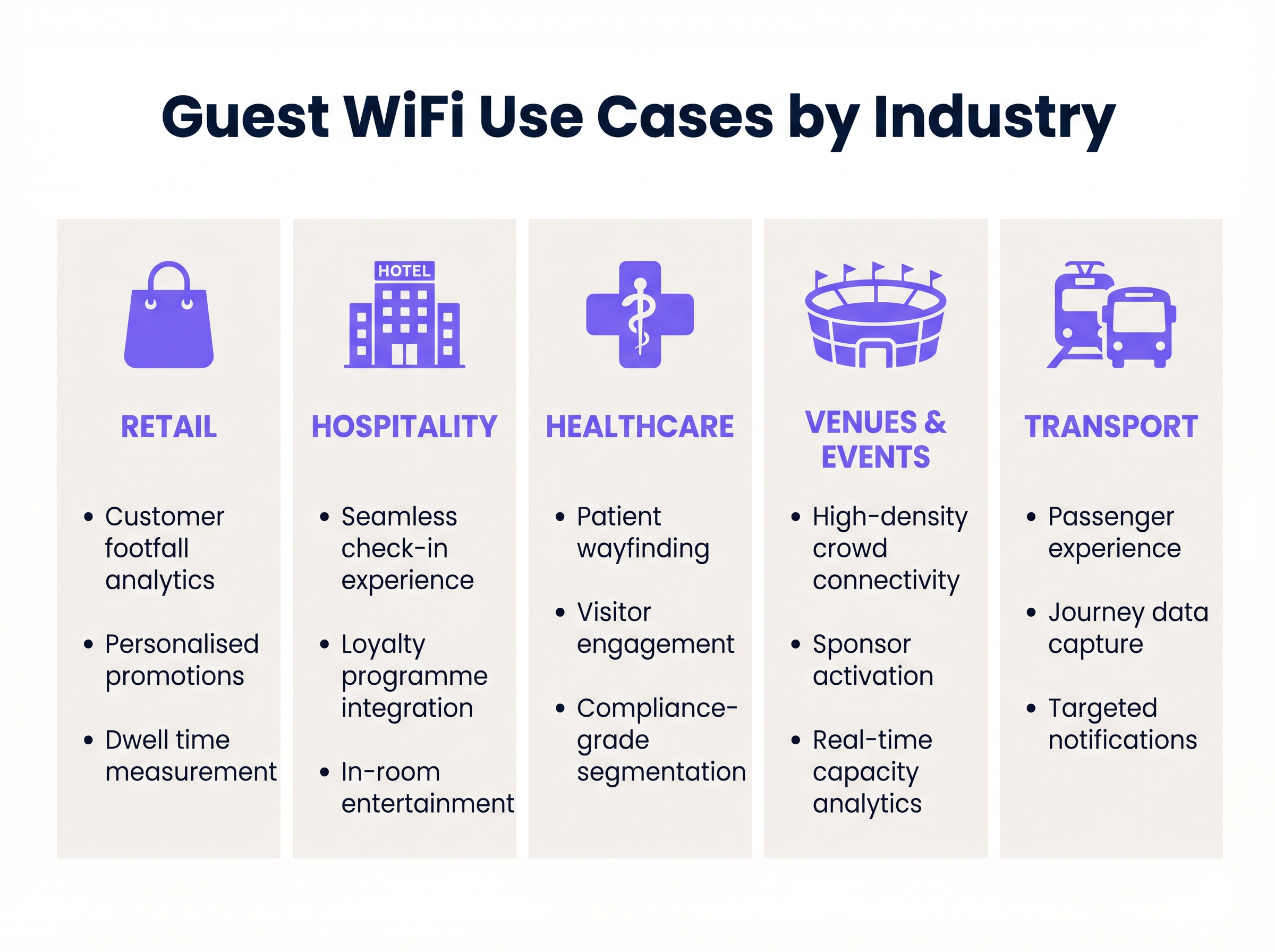
Retail: Footfall Analytics and Dwell Time
In the Retail sector, the primary objective is understanding physical customer behaviour. By capturing unauthenticated probe requests and authenticated session data, retailers can measure footfall, track dwell time in specific store zones, and analyse conversion rates.
Implementation Strategy: Deploy access points with dedicated scanning radios to capture passive probe requests. Integrate the captive portal with the central CRM to enable progressive profiling. When a customer authenticates, the system should trigger a webhook to the marketing automation platform, enabling personalised re-engagement campaigns based on their in-store behaviour.
Hospitality: Seamless Connectivity and Contextual Engagement
For Hospitality environments, reliable connectivity is the baseline. The advanced use case involves integrating the WiFi authentication flow with the Property Management System (PMS).
Implementation Strategy: Configure the captive portal to query the PMS via API. When a guest enters their room number and surname, the system validates the credentials and provisions access for the duration of their stay. In a wifi resort environment, location-based analytics can trigger contextual offers—for example, sending a spa promotion to a guest who has been dwelling near the pool area for an extended period.
Venues and Events: High-Density Crowd Analytics
Stadiums and conference centres face the challenge of extreme client density. A wifi zoo or theme park deployment shares similar characteristics, requiring careful RF planning to handle massive concurrent connections.
Implementation Strategy: Utilise directional antennas and aggressive load balancing to manage client distribution across access points. Implement captive portals with sponsor branding to generate immediate advertising revenue. Post-event, the captured first-party data (email addresses and demographics) becomes a critical asset for future ticket sales and merchandise promotions.
Healthcare: Compliance-Grade Segmentation
In Healthcare , the focus is on operational efficiency and strict regulatory compliance. Guest networks must be completely segregated from clinical systems.
Implementation Strategy: Implement strict VLAN isolation and web content filtering. The captive portal must feature robust GDPR consent flows, clearly separating terms of service acceptance from marketing opt-ins, as mandated by the Data Security and Protection Toolkit. Use cases include patient wayfinding via indoor mapping and providing access to digital health resources.
Transport: Passenger Experience and Journey Mapping
For the Transport sector, guest WiFi improves the passenger experience while generating valuable journey data.
Implementation Strategy: Deploy mobile access points with cellular backhaul (e.g., SD-WAN routers) on trains or buses. To understand the network architecture required for distributed environments, review The Core SD WAN Benefits for Modern Businesses . The analytics platform can correlate connection data with ticketing systems to map passenger flows and optimise route planning.
Best Practices
When designing and deploying a guest WiFi solution, IT teams should adhere to the following principles:
- Prioritise User Experience (UX) at the Portal: The captive portal is the digital front door. Ensure it is responsive, loads quickly, and functions seamlessly across iOS, Android, and Windows devices. For guidance on portal design, refer to Comment créer une page de connexion WiFi invité .
- Design for Scalability: Engineer the network for peak capacity (the 95th percentile), not average load. This requires comprehensive RF site surveys and capacity planning, particularly in high-density environments.
- Implement Robust Data Governance: Treat guest data as a highly sensitive asset. Implement automated data retention policies, ensure clear consent mechanisms, and integrate a Consent Management Platform (CMP) to handle data subject access requests (DSARs).
- Automate Integrations: Do not leave data siloed in the WiFi controller. Use APIs and webhooks to stream authentication events and location data directly into your CRM and marketing platforms in real-time.
Troubleshooting & Risk Mitigation
Deploying enterprise guest WiFi involves inherent risks. The most common failure modes and their mitigations include:
- Captive Portal Non-Appearance: This often occurs due to aggressive DNS interception or strict HTTPS inspection policies. Mitigation: Ensure the Walled Garden configuration allows access to the necessary identity providers (e.g., Google, Facebook) and the portal hosting domain before authentication is complete.
- VLAN Leakage: Misconfigured switch ports can allow guest traffic to traverse corporate networks. Mitigation: Conduct regular penetration testing and automated configuration audits to verify VLAN isolation.
- MAC Randomisation: Modern mobile operating systems employ MAC address randomisation to protect user privacy, complicating cross-visit tracking. Mitigation: Shift reliance from device-level identifiers (MAC addresses) to authenticated user identities captured via the captive portal.
ROI & Business Impact
The return on investment (ROI) for a guest WiFi deployment should be measured across two axes: operational savings and revenue generation.
Operationally, automated authentication (e.g., PMS integration in hotels) reduces helpdesk tickets related to WiFi access. Commercially, the platform acts as a high-volume lead generation tool. By calculating the Cost Per Acquisition (CPA) of an email address via traditional digital marketing channels versus the cost of capturing it via the guest WiFi portal, organisations typically demonstrate a positive ROI within 6 to 12 months. Furthermore, the insights derived from footfall analytics allow for data-driven decisions regarding staffing levels, store layouts, and lease negotiations, amplifying the overall business impact.
Key Terms & Definitions
Captive Portal
A web page that a user of a public access network is obliged to view and interact with before access is granted. It is the primary mechanism for authentication and terms acceptance.
Critical for capturing first-party data and ensuring users agree to terms of service before consuming bandwidth.
WPA3-SAE
Wi-Fi Protected Access 3 with Simultaneous Authentication of Equals. A security standard that provides robust protection against offline dictionary attacks.
The recommended security standard for modern enterprise guest networks to ensure cryptographic integrity.
MAC Randomisation
A privacy feature in modern mobile operating systems that generates a temporary MAC address for each network connection.
Complicates tracking users based solely on device hardware identifiers, making authenticated captive portal logins essential for persistent tracking.
RSSI (Received Signal Strength Indicator)
A measurement of the power present in a received radio signal.
Used in WiFi analytics to estimate the distance of a device from an access point, enabling location-based services and dwell time calculations.
Walled Garden
A limited environment that controls the user's access to web content and services before they have fully authenticated.
Must be carefully configured to allow access to necessary identity providers (like Google or Facebook for social login) before the user is granted full internet access.
VLAN Segmentation
The practice of dividing a physical network into multiple logical networks to isolate traffic.
Essential for security and compliance, ensuring guest traffic cannot route to corporate or POS systems.
Cross-Venue Identity Resolution
The ability to recognise a returning user across different physical locations within the same brand or estate.
Enables retailers and hospitality groups to build a unified customer profile and trigger consistent marketing campaigns regardless of which location the guest visits.
Progressive Profiling
A method of gradually gathering information about a user across multiple interactions rather than asking for all data upfront.
Used in captive portals to improve conversion rates; a user might provide just an email on their first visit, and a phone number on their second.
Case Studies
A 200-room hotel needs to implement a guest WiFi solution that provides seamless connectivity while capturing first-party data for the marketing team, without increasing the burden on the front desk.
Deploy a WPA3-enabled network with a captive portal integrated directly into the hotel's Property Management System (PMS) via API. Configure the Walled Garden to allow access to the PMS authentication endpoint. When a guest connects, they enter their room number and surname. The portal queries the PMS; upon validation, the device's MAC address is whitelisted for the duration of the stay. Simultaneously, the portal presents a GDPR-compliant opt-in for marketing communications, syncing consented profiles directly to the hotel's CRM.
A national retail chain requires visibility into store conversion rates (footfall vs. transactions) and wants to trigger personalised offers to returning customers based on their previous visits.
Implement access points with dedicated scanning radios to capture passive probe requests for baseline footfall metrics. Deploy a centralised captive portal with social login (OAuth) to capture authenticated identities. Configure cross-venue identity resolution in the central analytics platform. Set up webhooks to trigger an event in the marketing automation platform whenever a known device connects, allowing for real-time, personalised email or SMS offers based on the customer's purchase history.
Scenario Analysis
Q1. A hospital IT director wants to provide free WiFi to patients and visitors but is concerned about HIPAA/GDPR compliance and the security of clinical systems. What is the most critical architectural requirement?
💡 Hint:Consider how network traffic is isolated at Layer 2 and Layer 3.
Show Recommended Approach
The most critical requirement is strict network segmentation. Guest traffic must be placed on a dedicated VLAN that is completely isolated from clinical networks. Inter-VLAN routing must be blocked by stateful firewall policies, ensuring that a compromised guest device cannot access patient records or medical equipment.
Q2. A retail marketing team complains that their WiFi analytics dashboard shows a high number of 'visitors' but very few actionable customer profiles. What technical limitation is likely causing this, and how should the IT team resolve it?
💡 Hint:Think about how modern smartphones handle their hardware identifiers when scanning for networks.
Show Recommended Approach
The dashboard is likely relying on passive probe requests, which are subject to MAC address randomisation by modern mobile operating systems (iOS/Android). This inflates visitor counts with temporary MACs and prevents profile building. The IT team must implement a captive portal to force authentication, capturing a persistent identity (like an email address) rather than relying on hardware MAC addresses.
Q3. During a major sporting event, the stadium's guest WiFi network becomes unresponsive. The access points are online, but users cannot reach the captive portal to log in. What is the most likely configuration issue?
💡 Hint:Consider the dependencies required for a device to resolve and load an external web page before authentication.
Show Recommended Approach
The most likely issue is an incorrectly configured Walled Garden or DNS interception failure. If the Walled Garden does not permit access to the DNS servers, the captive portal hosting domain, or the required external Identity Providers (e.g., Google/Facebook for social login), the device cannot load the portal page, resulting in a denial of service for new connections.



