Casos de Uso de Guest WiFi: Como Diferentes Indústrias Estão a Usar o WiFi Gratuito
Uma referência técnica abrangente para líderes de TI sobre a implementação de Guest WiFi como uma plataforma estratégica de aquisição de dados e análise. Este guia abrange arquitetura, casos de uso específicos da indústria e melhores práticas para transformar a conectividade em valor de negócio mensurável.
🎧 Ouça este Guia
Ver Transcrição
- Resumo Executivo
- Análise Técnica Aprofundada
- Arquitetura de Rede e Padrões de Segurança
- A Camada de Identidade e Análise
- Guia de Implementação: Casos de Uso por Indústria
- Retalho: Análise de Fluxo de Visitantes e Tempo de Permanência
- Hotelaria: Conectividade Contínua e Engajamento Contextual
- Recintos e Eventos: Alta Densidade Análise de Multidões
- Saúde: Segmentação de Grau de Conformidade
- Transportes: Experiência do Passageiro e Mapeamento de Viagens
- Boas Práticas
- Resolução de Problemas e Mitigação de Riscos
- ROI e Impacto no Negócio

Resumo Executivo
Para as empresas modernas, fornecer Guest WiFi gratuito deixou de ser um centro de custos — é um canal crítico de aquisição de dados. Este guia examina como gestores de TI, arquitetos de rede e CTOs nos setores de retalho, hotelaria, saúde, recintos e transportes estão a transformar a conectividade padrão em inteligência de negócio acionável. Ao implementar mecanismos avançados de autenticação, segmentação de rede robusta e plataformas de análise integradas, as organizações podem capturar dados primários consentidos, medir o fluxo de visitantes físico e impulsionar as receitas através de um re-engajamento direcionado.
Este documento de referência oferece uma análise técnica aprofundada da arquitetura necessária para suportar estes casos de uso, desde os padrões 802.1X e WPA3 até ao design de captive portal e conformidade com o GDPR. Descreve estratégias de implementação neutras em relação a fornecedores e destaca como plataformas como o Guest WiFi e WiFi Analytics da Purple se alinham diretamente com resultados comerciais. Quer esteja a gerir uma implementação de estádio de alta densidade ou uma rede de retalho distribuída, este guia fornece a orientação prática e arquitetónica necessária para otimizar a sua infraestrutura sem fios.
Análise Técnica Aprofundada
A diferença entre uma implementação básica de WiFi gratuito e uma plataforma de inteligência de visitantes totalmente instrumentada é significativa. Uma arquitetura robusta requer uma orquestração cuidadosa em três camadas primárias: a camada de rede, a camada de identidade e a camada de análise.
Arquitetura de Rede e Padrões de Segurança
Na base, a camada de rede deve fornecer um débito fiável, mantendo um isolamento rigoroso. As redes de visitantes empresariais devem aproveitar o WPA3-SAE (Simultaneous Authentication of Equals) para uma maior força criptográfica contra ataques de dicionário offline. Para ambientes que exigem a aplicação de políticas por utilizador, o IEEE 802.1X com autenticação baseada em RADIUS é o padrão. No entanto, para implementações voltadas para o consumidor, onde o provisionamento de dispositivos é impraticável, o captive portal permanece o mecanismo principal para a captura de identidade e aceitação de políticas.
A segmentação rigorosa da rede é inegociável. O tráfego de visitantes deve ser isolado em VLANs dedicadas, com políticas de encaminhamento inter-VLAN aplicadas por firewalls com estado para evitar movimentos laterais para ambientes corporativos ou de ponto de venda (POS). Isto é particularmente crítico no retalho e na saúde, onde a conformidade com PCI DSS e HIPAA/GDPR exige a proteção de dados de titulares de cartões e pacientes.
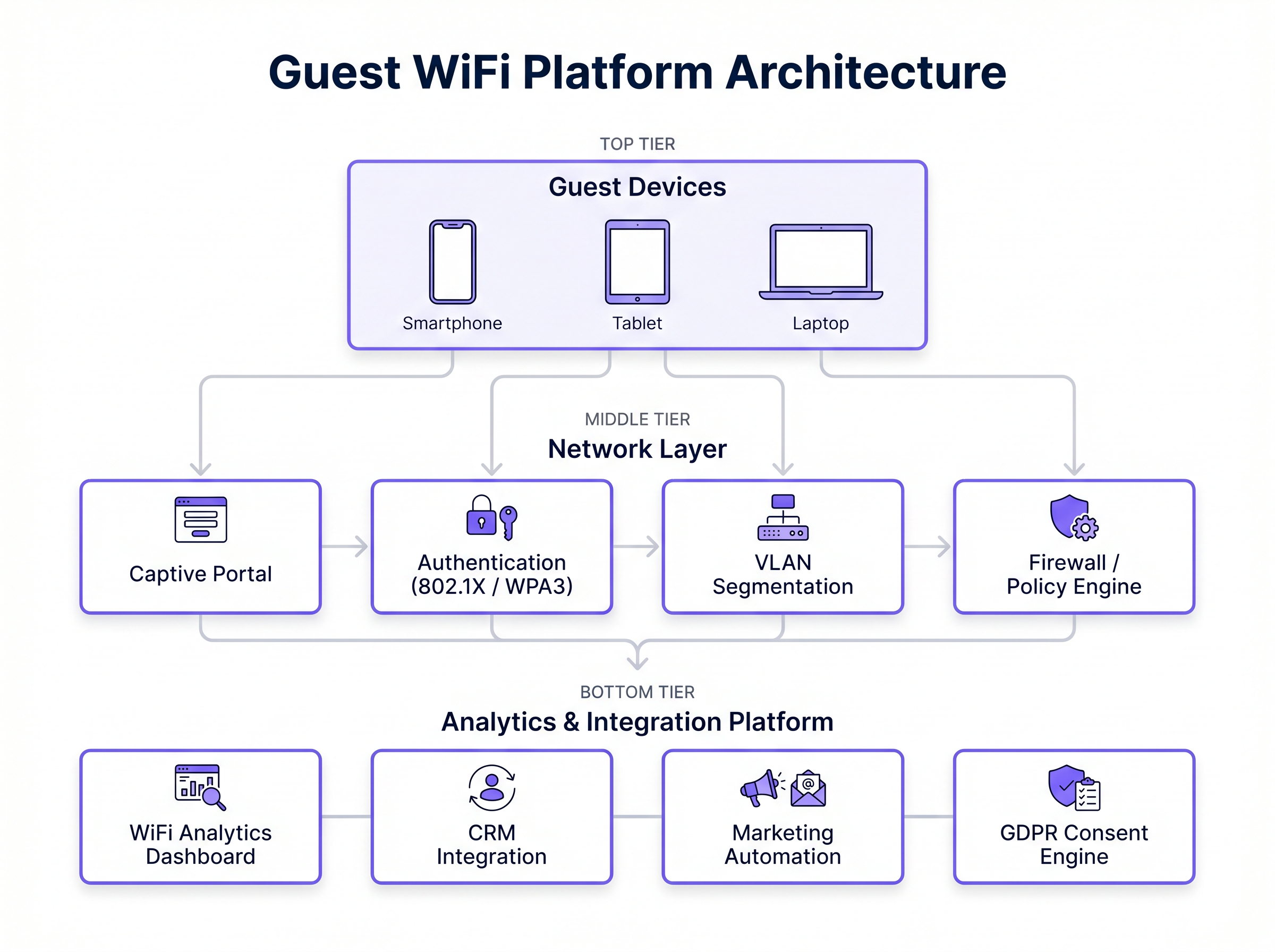
A Camada de Identidade e Análise
O valor comercial de uma rede Guest WiFi é capturado na camada de identidade. Um captive portal bem desenhado atua como um motor de aquisição de dados, capturando identidades autenticadas (via email, SMS ou OAuth social) e registando o consentimento explícito para comunicações de marketing. Estes dados devem então fluir de forma contínua para a camada de análise.
Plataformas como o WiFi Analytics da Purple agregam eventos de conexão, dados de sonda RSSI (Received Signal Strength Indicator) e perfis autenticados. Isto permite a resolução de identidade entre locais — permitindo que um retalhista reconheça um cliente que regressa em diferentes lojas — e fornece a base de dados para integrações CRM automatizadas e campanhas de marketing direcionadas. Além disso, a Purple atua como um fornecedor de identidade gratuito para serviços como o OpenRoaming sob a licença Connect, simplificando o processo de autenticação para utilizadores que regressam.
Guia de Implementação: Casos de Uso por Indústria
Diferentes setores verticais têm requisitos e restrições arquitetónicas distintas ao implementar Guest WiFi. Abaixo, encontra-se uma análise de como indústrias específicas estão a aproveitar a infraestrutura sem fios para impulsionar o valor de negócio.
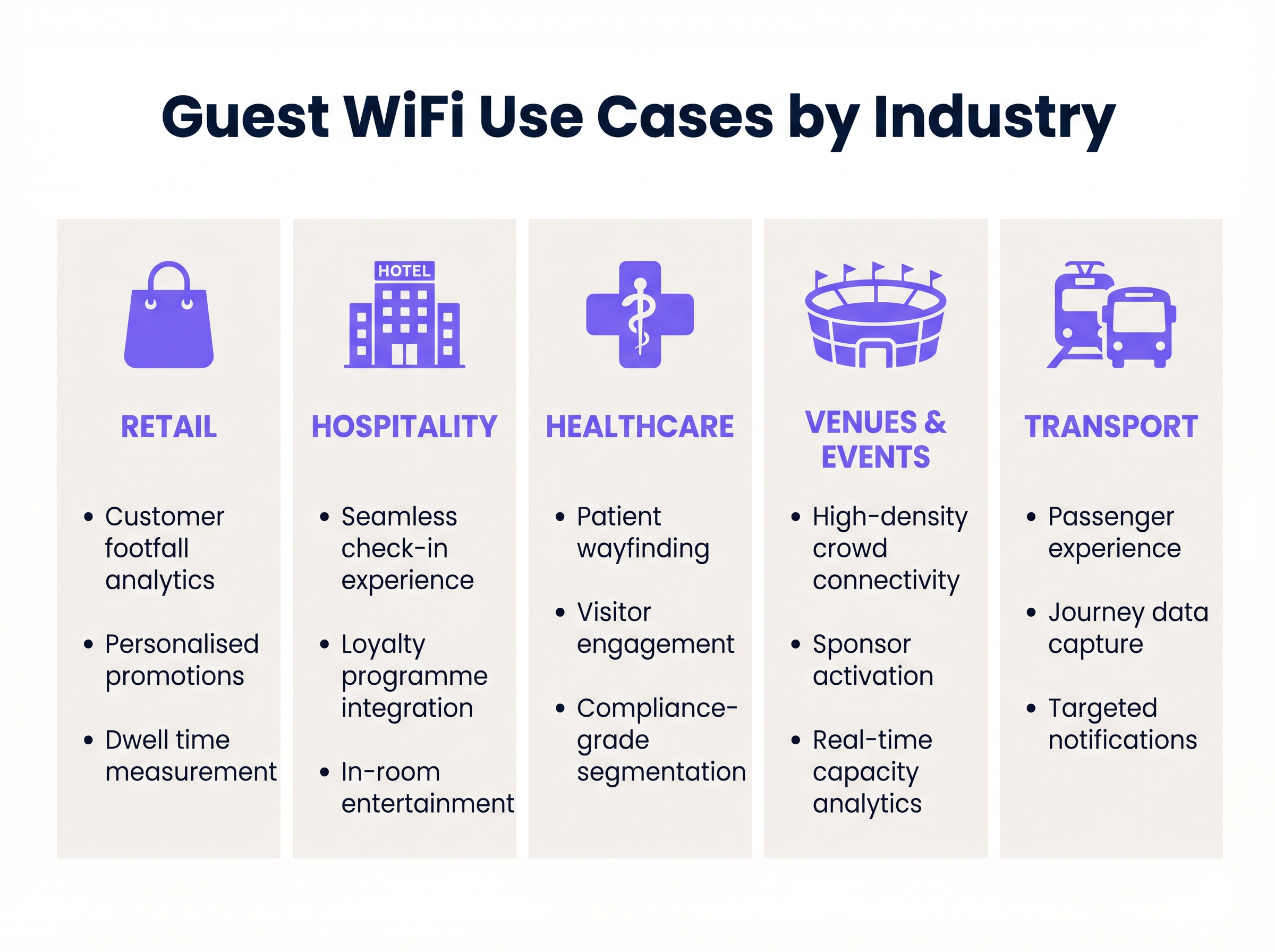
Retalho: Análise de Fluxo de Visitantes e Tempo de Permanência
No setor de Retalho , o objetivo principal é compreender o comportamento físico do cliente. Ao capturar pedidos de sonda não autenticados e dados de sessão autenticados, os retalhistas podem medir o fluxo de visitantes, monitorizar o tempo de permanência em zonas específicas da loja e analisar as taxas de conversão.
Estratégia de Implementação: Implementar pontos de acesso com rádios de digitalização dedicados para capturar pedidos de sonda passivos. Integrar o captive portal com o CRM central para permitir o perfil progressivo. Quando um cliente se autentica, o sistema deve acionar um webhook para a plataforma de automação de marketing, permitindo campanhas de re-engajamento personalizadas com base no seu comportamento na loja.
Hotelaria: Conectividade Contínua e Engajamento Contextual
Para ambientes de Hotelaria , a conectividade fiável é o ponto de partida. O caso de uso avançado envolve a integração do fluxo de autenticação WiFi com o Sistema de Gestão de Propriedades (PMS).
Estratégia de Implementação: Configurar o captive portal para consultar o PMS via API. Quando um hóspede insere o número do quarto e o apelido, o sistema valida as credenciais e provisiona o acesso pela duração da sua estadia. Num ambiente de resort WiFi, a análise baseada na localização pode acionar ofertas contextuais — por exemplo, enviar uma promoção de spa a um hóspede que tenha permanecido perto da área da piscina por um período prolongado.
Recintos e Eventos: Alta Densidade Análise de Multidões
Estádios e centros de conferências enfrentam o desafio da densidade extrema de clientes. Uma implementação de WiFi em jardins zoológicos ou parques temáticos partilha características semelhantes, exigindo um planeamento de RF cuidadoso para gerir um grande número de ligações simultâneas.
Estratégia de Implementação: Utilize antenas direcionais e balanceamento de carga agressivo para gerir a distribuição de clientes pelos pontos de acesso. Implemente captive portals com branding de patrocinadores para gerar receita publicitária imediata. Após o evento, os dados primários capturados (endereços de e-mail e dados demográficos) tornam-se um ativo crítico para futuras vendas de bilhetes e promoções de merchandising.
Saúde: Segmentação de Grau de Conformidade
No setor da Saúde , o foco está na eficiência operacional e na estrita conformidade regulamentar. As redes de convidados devem ser completamente segregadas dos sistemas clínicos.
Estratégia de Implementação: Implemente isolamento rigoroso de VLAN e filtragem de conteúdo web. O captive portal deve apresentar fluxos de consentimento GDPR robustos, separando claramente a aceitação dos termos de serviço das opções de marketing, conforme exigido pelo Data Security and Protection Toolkit. Os casos de uso incluem orientação de pacientes através de mapeamento interno e fornecimento de acesso a recursos de saúde digitais.
Transportes: Experiência do Passageiro e Mapeamento de Viagens
Para o setor dos Transportes , o guest WiFi melhora a experiência do passageiro enquanto gera dados valiosos sobre a viagem.
Estratégia de Implementação: Implemente pontos de acesso móveis com backhaul celular (por exemplo, routers SD-WAN) em comboios ou autocarros. Para compreender a arquitetura de rede necessária para ambientes distribuídos, consulte Os Principais Benefícios do SD WAN para Empresas Modernas . A plataforma de análise pode correlacionar dados de ligação com sistemas de bilhética para mapear fluxos de passageiros e otimizar o planeamento de rotas.
Boas Práticas
Ao projetar e implementar uma solução de guest WiFi, as equipas de TI devem aderir aos seguintes princípios:
- Priorize a Experiência do Utilizador (UX) no Portal: O captive portal é a porta de entrada digital. Garanta que é responsivo, carrega rapidamente e funciona sem problemas em dispositivos iOS, Android e Windows. Para orientação sobre o design do portal, consulte Como criar uma página de login WiFi para convidados .
- Projete para Escalabilidade: Projete a rede para capacidade máxima (o percentil 95), não para carga média. Isso requer levantamentos de RF abrangentes e planeamento de capacidade, particularmente em ambientes de alta densidade.
- Implemente uma Governança de Dados Robusta: Trate os dados dos convidados como um ativo altamente sensível. Implemente políticas automatizadas de retenção de dados, garanta mecanismos de consentimento claros e integre uma Plataforma de Gestão de Consentimento (CMP) para lidar com pedidos de acesso de titulares de dados (DSARs).
- Automatize Integrações: Não deixe os dados isolados no controlador WiFi. Use APIs e webhooks para transmitir eventos de autenticação e dados de localização diretamente para as suas plataformas de CRM e marketing em tempo real.
Resolução de Problemas e Mitigação de Riscos
A implementação de guest WiFi empresarial envolve riscos inerentes. Os modos de falha mais comuns e as suas mitigações incluem:
- Não Aparecimento do Captive Portal: Isso ocorre frequentemente devido a interceção agressiva de DNS ou políticas rigorosas de inspeção HTTPS. Mitigação: Garanta que a configuração do Walled Garden permite o acesso aos fornecedores de identidade necessários (por exemplo, Google, Facebook) e ao domínio de alojamento do portal antes que a autenticação esteja completa.
- Fuga de VLAN: Portas de switch mal configuradas podem permitir que o tráfego de convidados atravesse redes corporativas. Mitigação: Realize testes de penetração regulares e auditorias de configuração automatizadas para verificar o isolamento de VLAN.
- Aleatorização de MAC: Os sistemas operativos móveis modernos empregam a aleatorização de endereços MAC para proteger a privacidade do utilizador, complicando o rastreamento entre visitas. Mitigação: Mude a dependência de identificadores de nível de dispositivo (endereços MAC) para identidades de utilizador autenticadas capturadas através do captive portal.
ROI e Impacto no Negócio
O retorno do investimento (ROI) para uma implementação de guest WiFi deve ser medido em dois eixos: poupanças operacionais e geração de receita.
Operacionalmente, a autenticação automatizada (por exemplo, integração PMS em hotéis) reduz os pedidos de suporte relacionados com o acesso WiFi. Comercialemente, a plataforma atua como uma ferramenta de geração de leads de alto volume. Ao calcular o Custo Por Aquisição (CPA) de um endereço de e-mail através de canais de marketing digital tradicionais versus o custo de o capturar através do portal guest WiFi, as organizações demonstram tipicamente um ROI positivo dentro de 6 a 12 meses. Além disso, os insights derivados da análise de fluxo de pessoas permitem decisões baseadas em dados relativamente aos níveis de pessoal, layouts de lojas e negociações de arrendamento, ampliando o impacto geral no negócio.
Termos-Chave e Definições
Captive Portal
A web page that a user of a public access network is obliged to view and interact with before access is granted. It is the primary mechanism for authentication and terms acceptance.
Critical for capturing first-party data and ensuring users agree to terms of service before consuming bandwidth.
WPA3-SAE
Wi-Fi Protected Access 3 with Simultaneous Authentication of Equals. A security standard that provides robust protection against offline dictionary attacks.
The recommended security standard for modern enterprise guest networks to ensure cryptographic integrity.
MAC Randomisation
A privacy feature in modern mobile operating systems that generates a temporary MAC address for each network connection.
Complicates tracking users based solely on device hardware identifiers, making authenticated captive portal logins essential for persistent tracking.
RSSI (Received Signal Strength Indicator)
A measurement of the power present in a received radio signal.
Used in WiFi analytics to estimate the distance of a device from an access point, enabling location-based services and dwell time calculations.
Walled Garden
A limited environment that controls the user's access to web content and services before they have fully authenticated.
Must be carefully configured to allow access to necessary identity providers (like Google or Facebook for social login) before the user is granted full internet access.
VLAN Segmentation
The practice of dividing a physical network into multiple logical networks to isolate traffic.
Essential for security and compliance, ensuring guest traffic cannot route to corporate or POS systems.
Cross-Venue Identity Resolution
The ability to recognise a returning user across different physical locations within the same brand or estate.
Enables retailers and hospitality groups to build a unified customer profile and trigger consistent marketing campaigns regardless of which location the guest visits.
Progressive Profiling
A method of gradually gathering information about a user across multiple interactions rather than asking for all data upfront.
Used in captive portals to improve conversion rates; a user might provide just an email on their first visit, and a phone number on their second.
Estudos de Caso
A 200-room hotel needs to implement a guest WiFi solution that provides seamless connectivity while capturing first-party data for the marketing team, without increasing the burden on the front desk.
Deploy a WPA3-enabled network with a captive portal integrated directly into the hotel's Property Management System (PMS) via API. Configure the Walled Garden to allow access to the PMS authentication endpoint. When a guest connects, they enter their room number and surname. The portal queries the PMS; upon validation, the device's MAC address is whitelisted for the duration of the stay. Simultaneously, the portal presents a GDPR-compliant opt-in for marketing communications, syncing consented profiles directly to the hotel's CRM.
A national retail chain requires visibility into store conversion rates (footfall vs. transactions) and wants to trigger personalised offers to returning customers based on their previous visits.
Implement access points with dedicated scanning radios to capture passive probe requests for baseline footfall metrics. Deploy a centralised captive portal with social login (OAuth) to capture authenticated identities. Configure cross-venue identity resolution in the central analytics platform. Set up webhooks to trigger an event in the marketing automation platform whenever a known device connects, allowing for real-time, personalised email or SMS offers based on the customer's purchase history.
Análise de Cenários
Q1. A hospital IT director wants to provide free WiFi to patients and visitors but is concerned about HIPAA/GDPR compliance and the security of clinical systems. What is the most critical architectural requirement?
💡 Dica:Consider how network traffic is isolated at Layer 2 and Layer 3.
Mostrar Abordagem Recomendada
The most critical requirement is strict network segmentation. Guest traffic must be placed on a dedicated VLAN that is completely isolated from clinical networks. Inter-VLAN routing must be blocked by stateful firewall policies, ensuring that a compromised guest device cannot access patient records or medical equipment.
Q2. A retail marketing team complains that their WiFi analytics dashboard shows a high number of 'visitors' but very few actionable customer profiles. What technical limitation is likely causing this, and how should the IT team resolve it?
💡 Dica:Think about how modern smartphones handle their hardware identifiers when scanning for networks.
Mostrar Abordagem Recomendada
The dashboard is likely relying on passive probe requests, which are subject to MAC address randomisation by modern mobile operating systems (iOS/Android). This inflates visitor counts with temporary MACs and prevents profile building. The IT team must implement a captive portal to force authentication, capturing a persistent identity (like an email address) rather than relying on hardware MAC addresses.
Q3. During a major sporting event, the stadium's guest WiFi network becomes unresponsive. The access points are online, but users cannot reach the captive portal to log in. What is the most likely configuration issue?
💡 Dica:Consider the dependencies required for a device to resolve and load an external web page before authentication.
Mostrar Abordagem Recomendada
The most likely issue is an incorrectly configured Walled Garden or DNS interception failure. If the Walled Garden does not permit access to the DNS servers, the captive portal hosting domain, or the required external Identity Providers (e.g., Google/Facebook for social login), the device cannot load the portal page, resulting in a denial of service for new connections.



