L'impatto degli annunci video sul throughput della rete ospite
Questa guida esplora come gli annunci video a riproduzione automatica consumano silenziosamente il throughput della rete ospite in ambienti ad alta densità. Fornisce strategie attuabili e neutrali rispetto al fornitore per i responsabili IT e gli architetti di rete per recuperare la larghezza di banda utilizzando il filtro DNS perimetrale.
Ascolta questa guida
Visualizza trascrizione del podcast
- Riepilogo Esecutivo
- Approfondimento Tecnico: La Fisica della Saturazione della Rete Guidata dagli Annunci
- L'Anatomia di una Richiesta Web
- La Penalità di Larghezza di Banda degli Annunci Video
- Consumo di Airtime e Inefficienza Spettrale
- Cascate di Latenza della Risoluzione DNS
- Guida all'Implementazione: Architettura di Filtro DNS Perimetrale
- Strategia di Implementazione Passo-Passo
- Best Practice e Conformità
- Privacy by Design (GDPR Articolo 25)
- Segmentazione della Rete (PCI DSS)
- Esperienza Utente Trasparente
- Risoluzione dei Problemi e Mitigazione del Rischio
- ROI e Impatto Commerciale

Riepilogo Esecutivo
Per i CTO e gli architetti di rete che gestiscono sedi ad alta densità—come stadi, centri Retail , ambienti Hospitality e hub di Transport —le prestazioni del WiFi ospite sono una metrica operativa fondamentale. Tuttavia, la pianificazione standard della capacità di rete spesso trascura un consumo silenzioso e strutturale della larghezza di banda: gli annunci video a riproduzione automatica.
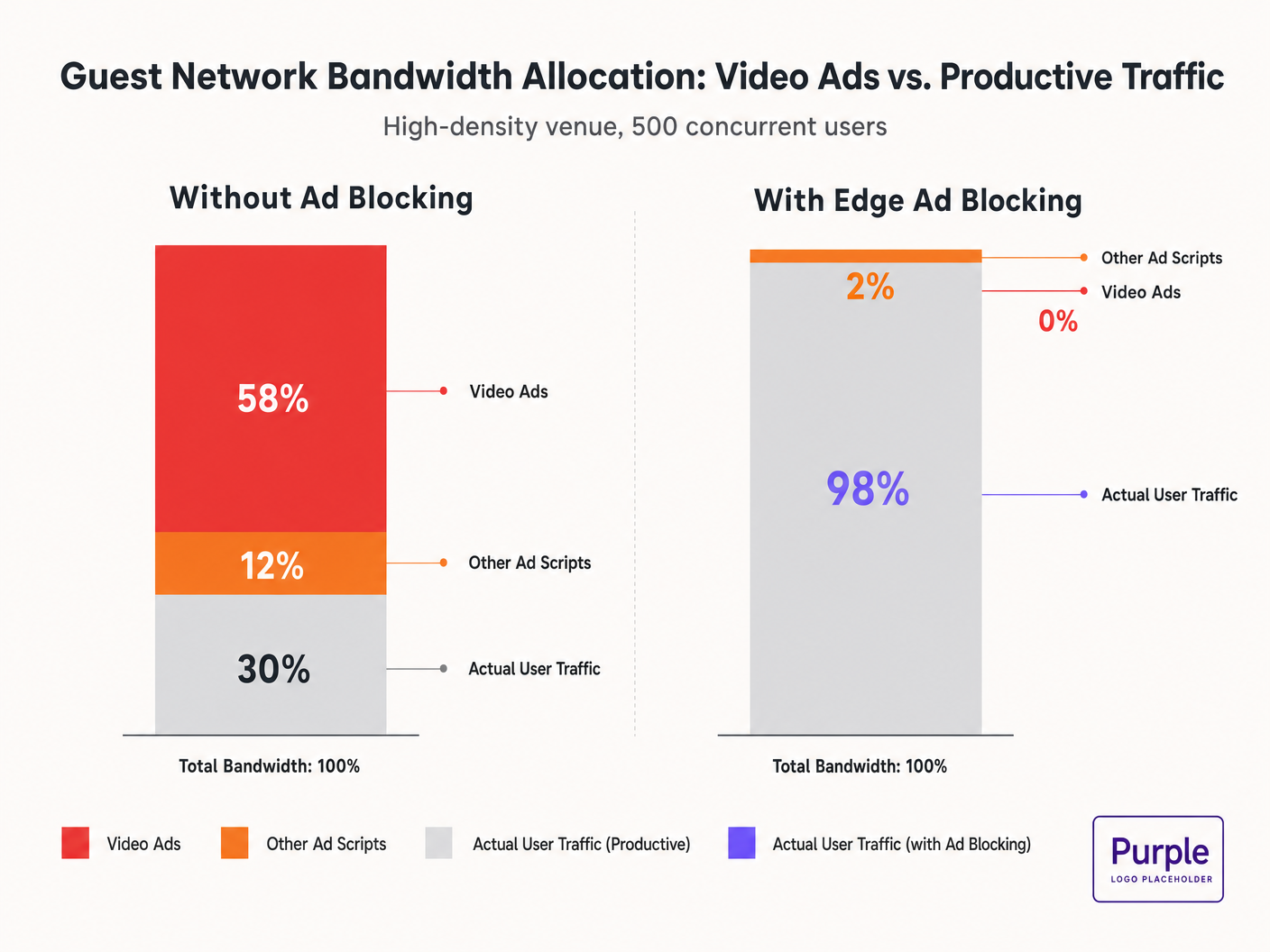
Quando gli ospiti si connettono alla rete e navigano su proprietà web standard, i loro dispositivi avviano decine di connessioni in background a reti di distribuzione di annunci. Questi stream video a bitrate adattivo possono consumare il 50-70% del throughput disponibile, degradando l'esperienza per tutti gli utenti e saturando i collegamenti di backhaul. Questa guida descrive i meccanismi tecnici di questo consumo di larghezza di banda e fornisce un modello neutrale rispetto al fornitore per mitigarla al perimetro utilizzando il filtro DNS. Implementando queste strategie, le sedi possono migliorare drasticamente le prestazioni del Guest WiFi , ridurre i costi dell'infrastruttura e migliorare la conformità senza attendere un ciclo di aggiornamento hardware.
Ascolta il nostro briefing su questo argomento:
Approfondimento Tecnico: La Fisica della Saturazione della Rete Guidata dagli Annunci
L'Anatomia di una Richiesta Web
Quando un utente su una rete ospite accede a un sito web supportato da annunci, il comportamento del browser è estremamente aggressivo. Un singolo caricamento di pagina tipicamente attiva connessioni a 8-40 domini di terze parti separati, inclusi scambi di annunci, Demand-Side Platforms (DSPs) e Content Delivery Networks (CDNs).
La Penalità di Larghezza di Banda degli Annunci Video
Gli annunci video, in particolare i formati pre-roll e mid-roll serviti dai principali scambi, vengono distribuiti come stream a bitrate adattivo. Il CDN sonda la larghezza di banda disponibile e serve lo stream di massima qualità possibile. In un ambiente ad alta densità con 500 utenti concorrenti, se il 20% degli utenti attiva uno stream di annunci 1080p a 4-8 Mbps, la domanda aggregata aumenta istantaneamente di 400-800 Mbps. Questo traffico non richiesto bypassa la modellazione standard del Quality of Service (QoS) perché proviene da connessioni HTTPS legittime.
Consumo di Airtime e Inefficienza Spettrale
Oltre alla saturazione del backhaul, gli annunci video consumano prezioso airtime radio. In un mezzo wireless condiviso, ogni dispositivo che riceve attivamente uno stream ad alto bitrate riduce le opportunità di trasmissione per altri dispositivi. Sebbene lo standard IEEE 802.11ax (Wi-Fi 6) abbia introdotto OFDMA e BSS Colouring per migliorare l'efficienza spettrale, questi meccanismi non possono compensare l'enorme volume di dati richiesto dalle reti pubblicitarie. Lo strato radio si congestiona, portando a un aumento della latenza e della perdita di pacchetti per il traffico produttivo.
Cascate di Latenza della Risoluzione DNS
La distribuzione degli annunci si basa su complesse catene di reindirizzamento. Una singola impressione di annuncio può richiedere 6-12 lookup DNS prima che lo stream video si avvii. In una distribuzione densa, questo aumenta esponenzialmente il carico sul resolver DNS locale. Quando il resolver diventa un collo di bottiglia, la latenza si propaga a cascata, causando un degrado percepibile del caricamento della pagina per ogni utente sulla rete.
Guida all'Implementazione: Architettura di Filtro DNS Perimetrale
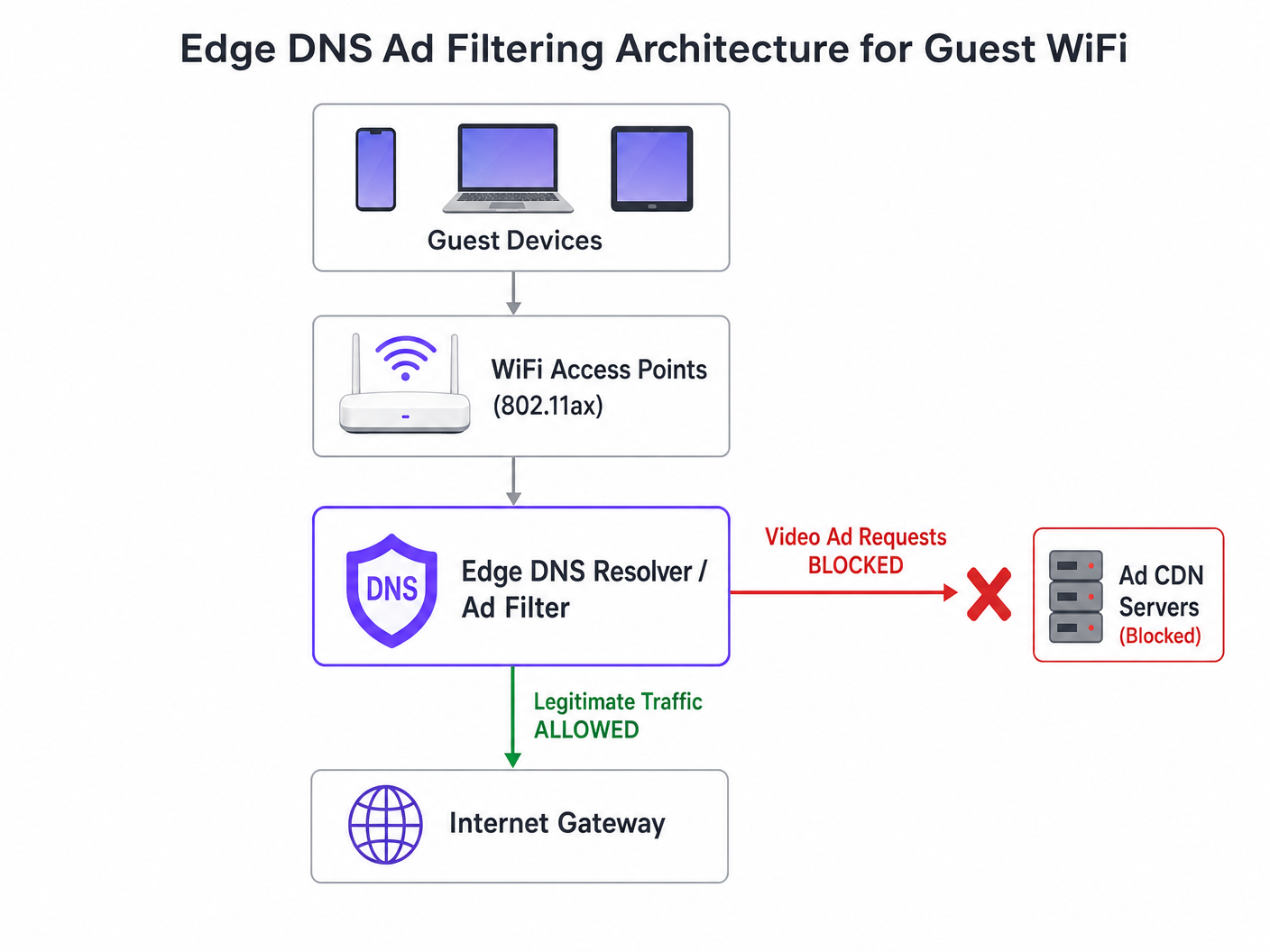
L'intervento architettonico più efficace è il filtro DNS perimetrale. Bloccando i domini delle reti pubblicitarie a livello di resolver, la rete impedisce che la connessione TCP venga mai stabilita. Questo approccio è stateless, scala linearmente e aggiunge una latenza trascurabile.
Strategia di Implementazione Passo-Passo
- Strumentazione Passiva: Implementare il logging DNS passivo sulla rete ospite per 48-72 ore per stabilire un profilo di traffico di base. Identificare i domini più interrogati e il loro volume. Utilizzare piattaforme come WiFi Analytics per visualizzare questi dati.
- Applicazione Conservativa della Blocklist: Non implementare blocklist di comunità massicce (ad es. la lista di Steven Black) il primo giorno. Iniziare con i primi 500 domini noti di distribuzione di annunci video. Verificare che la distribuzione di contenuti legittimi non sia compromessa.
- Configurazione DNS Split-Horizon: Garantire una stretta separazione tra l'infrastruttura DNS aziendale e quella ospite. La politica di filtraggio deve essere limitata esclusivamente alla VLAN ospite per prevenire interruzioni operative.
- Manutenzione Automatica della Blocklist: Le reti pubblicitarie ruotano dinamicamente i domini e utilizzano algoritmi di generazione di domini (DGAs). Configurare il resolver per recuperare intelligence sulle minacce e feed di blocklist aggiornati almeno ogni 4 ore.
- Gestione di DNS over HTTPS (DoH): I browser moderni potrebbero tentare di bypassare i resolver locali utilizzando DoH. Mitigare questo bloccando la porta TCP/UDP 443 in uscita verso intervalli IP noti di provider DoH, forzando il fallback al resolver fornito dalla rete.
Per un approfondimento sulle specifiche di configurazione, fare riferimento alla nostra guida su Migliorare le Velocità WiFi Bloccando le Reti Pubblicitarie al Perimetro .
Best Practice e Conformità
Privacy by Design (GDPR Articolo 25)
L'implementazione del filtro DNS perimetrale si allinea ai principi di privacy by design del GDPR. Prevenendo le connessioni a domini di tracciamento di terze parti, la rete protegge intrinsecamente i dati degli ospiti dalla raccolta non autorizzata. Questo approccio proattivo riduce l'onere di conformità della sede.
Segmentazione della Rete (PCI DSS)
Per il commercio al dettaglio e gli ospedaliLe sedi che elaborano pagamenti, il PCI DSS richiede una rigorosa segmentazione della rete. Il filtro DNS rafforza questo confine garantendo che i dispositivi degli ospiti non possano agire inavvertitamente come condotti per payload dannosi distribuiti tramite reti pubblicitarie compromesse (malvertising).
Esperienza Utente Trasparente
A differenza degli interstitial del captive portal o dell'ispezione approfondita dei pacchetti, il filtro DNS è trasparente. L'utente sperimenta caricamenti di pagina più rapidi e un consumo ridotto della batteria. Se uno slot pubblicitario non si carica, di solito si comprime o visualizza uno spazio vuoto, il che è raramente percepito come un errore di rete dall'utente.
Risoluzione dei Problemi e Mitigazione del Rischio
| Modalità di Guasto | Causa Radice | Strategia di Mitigazione |
|---|---|---|
| Blocco eccessivo di contenuti legittimi | Blocco a livello di root di CDN condivise (es. Akamai, Fastly). | Implementare il filtro a livello di sottodominio. Mantenere una robusta allowlist per i servizi critici della sede. |
| Filtro bypassato da DoH | Browser che utilizzano resolver DoH hardcoded. | Null-route IP di provider DoH noti. Implementare politiche di split-tunneling se si utilizza la gestione dei dispositivi mobili (MDM). |
| Esaurimento CPU del resolver | Infrastruttura DNS sottodimensionata che gestisce risposte NXDOMAIN eccessive. | Fornire resolver con CPU/RAM adeguate. Utilizzare il caching in modo aggressivo. Considerare resolver ricorsivi ospitati nel cloud per l'elasticità. |
ROI e Impatto Commerciale
L'impatto commerciale del filtro DNS edge è immediato e misurabile:
- Recupero della Larghezza di Banda: Le sedi recuperano tipicamente il 30-50% della larghezza di banda della loro rete ospite, ritardando costosi aggiornamenti del backhaul.
- Miglioramento della Soddisfazione degli Ospiti: Caricamenti di pagina più rapidi e connettività affidabile correlano direttamente con punteggi Net Promoter Score (NPS) più elevati e recensioni positive della sede.
- Efficienza Operativa: La riduzione dei ticket dell'helpdesk relativi a "WiFi lento" consente ai team IT di concentrarsi su iniziative strategiche, come l'implementazione di Modalità Mappe Offline o l'espansione delle integrazioni smart city, come sostenuto dalla nostra leadership (vedi Purple nomina Iain Fox come VP Growth ).
- Miglioramento della Postura di Sicurezza: Il blocco proattivo di malvertising e domini di tracciamento semplifica gli audit di sicurezza e la reportistica di conformità. Scopri di più sul mantenimento di una postura di sicurezza nel nostro articolo: Spiega cos'è l'audit trail per la sicurezza IT nel 2026 .
Definizioni chiave
Edge DNS Filtering
The practice of blocking access to specific domains at the local DNS resolver level, preventing devices from resolving the IP addresses of known ad networks.
Used by IT teams to silently drop unwanted traffic before a TCP connection is even attempted, saving bandwidth and improving performance.
Adaptive Bitrate Streaming (ABR)
A technology that dynamically adjusts the quality of a video stream based on the user's available bandwidth.
Ad networks use ABR to serve the highest possible quality video, which aggressively consumes available guest WiFi throughput.
Split-Horizon DNS
A configuration where different DNS responses are provided depending on the source IP address of the query (e.g., guest vs. corporate).
Essential for applying restrictive filtering policies to guest networks without impacting back-office operations.
DNS over HTTPS (DoH)
A protocol for performing remote DNS resolution via the HTTPS protocol, encrypting the queries.
DoH can bypass local edge filtering; network architects must actively block known DoH providers to enforce local DNS policies.
BSS Colouring
A Wi-Fi 6 (802.11ax) feature that adds a 'colour' identifier to transmissions, allowing access points to ignore traffic from overlapping networks.
Improves radio efficiency in dense venues, but does not solve the backhaul saturation caused by video ads.
NXDOMAIN
A DNS response code indicating that the requested domain name does not exist.
The standard response returned by a filtering resolver when a device attempts to query a blocked ad network domain.
Domain Generation Algorithm (DGA)
Techniques used by malware and some aggressive ad networks to periodically generate new domain names to evade static blocklists.
Requires IT teams to use dynamic, frequently updated threat intelligence feeds rather than static hosts files.
Malvertising
The use of online advertising to distribute malware or redirect users to malicious websites.
Blocking ad networks at the edge inherently protects guest devices from these threats, improving the venue's security posture.
Esempi pratici
A 400-room hotel is experiencing severe guest WiFi degradation every evening between 19:00 and 22:00. The 1 Gbps backhaul is saturated, but the property management system (PMS) shows only 600 connected devices. How should the network architect address this without upgrading the circuit?
- Implement passive DNS logging on the guest VLAN to analyze the traffic profile during the peak window. 2. Identify the top bandwidth-consuming domains, which are likely video ad CDNs. 3. Deploy a recursive DNS resolver with a curated blocklist targeting these specific ad networks. 4. Configure the guest DHCP scope to assign the new resolver. 5. Monitor bandwidth utilization; expect a 30-40% reduction in peak load.
A stadium IT director wants to implement DNS ad blocking but is concerned about breaking the venue's own mobile app, which uses a third-party analytics SDK.
- Audit the mobile app's network dependencies using a proxy tool. 2. Identify the specific API endpoints required for the app's functionality. 3. Add these specific FQDNs (Fully Qualified Domain Names) to the DNS resolver's allowlist, superseding any blocklist policies. 4. Roll out the filtering policy to a subset of access points (e.g., one concourse) for beta testing before a venue-wide deployment.
Domande di esercitazione
Q1. A retail chain wants to deploy DNS filtering across 500 stores. They currently use a cloud-managed firewall solution. Should they deploy local DNS resolvers at each store or route all DNS queries to a centralized cloud resolver?
Suggerimento: Consider the latency impact of DNS queries on page load times.
Visualizza risposta modello
They should route queries to a centralized cloud resolver with geographically distributed points of presence (PoPs), provided the latency to the nearest PoP is under 20ms. Deploying and maintaining 500 local resolvers introduces significant operational overhead. Cloud resolvers offer centralized policy management and automated blocklist updates, which is ideal for a distributed retail environment.
Q2. After implementing a DNS blocklist, the marketing team reports that the venue's captive portal splash page is failing to load for some users. What is the most likely cause?
Suggerimento: Captive portals often rely on external resources for tracking or authentication.
Visualizza risposta modello
The blocklist has likely inadvertently blocked a CDN or tracking pixel domain (e.g., Google Analytics or a social login API) that the captive portal depends on. The architect must review the DNS logs for the captive portal's walled garden IP range, identify the blocked dependency, and add it to the allowlist.
Q3. A conference centre is hosting a digital marketing summit. The IT director is concerned that blocking ad networks will disrupt the attendees' ability to work and demonstrate their products. How should this be handled?
Suggerimento: Network policies can be segmented by SSID or VLAN.
Visualizza risposta modello
The IT director should provision a dedicated SSID/VLAN for the summit attendees with a bypass policy that uses unfiltered DNS resolvers (e.g., 8.8.8.8). The standard guest WiFi network can remain filtered. This provides the necessary access for the specific event without compromising the performance of the general public network.