Resolver o Erro 'Ligado, Sem Internet' no WiFi de Convidados
Este guia de referência técnica e autoritário explica como os timeouts de DNS causados por redes congestionadas desencadeiam o erro 'Ligado, Sem Internet' no WiFi de convidados. Fornece a arquitetos de rede e gestores de TI passos de implementação acionáveis para implementar filtros DNS empresariais para resolver estes estrangulamentos e melhorar o onboarding de convidados.
Ouça este guia
Ver transcrição do podcast
- Resumo Executivo
- Análise Técnica Detalhada
- O Mecanismo de Deteção de Captive Portal
- Porque o Congestionamento Desencadeia Timeouts de DNS
- O Papel do Filtro DNS Empresarial
- Guia de Implementação
- 1. Posicionamento do Resolvedor e Otimização da Latência
- 2. Whitelisting de Captive Portal (Passthrough)
- 3. Ajuste de TTL e Gestão de Cache
- 4. Integração com a Infraestrutura Existente
- Melhores Práticas
- Resolução de Problemas e Mitigação de Riscos
- ROI e Impacto no Negócio
Resumo Executivo
Para CTOs e arquitetos de rede que supervisionam locais de alta densidade — como os de Retalho , Hotelaria , Saúde e Transportes — o erro "Ligado, Sem Internet" nas redes Guest WiFi é uma dor de cabeça operacional persistente. Embora muitas vezes seja diagnosticado erroneamente como uma falha de hardware de AP ou largura de banda upstream insuficiente, a causa raiz em ambientes empresariais é tipicamente um timeout de DNS causado por congestionamento de rede.
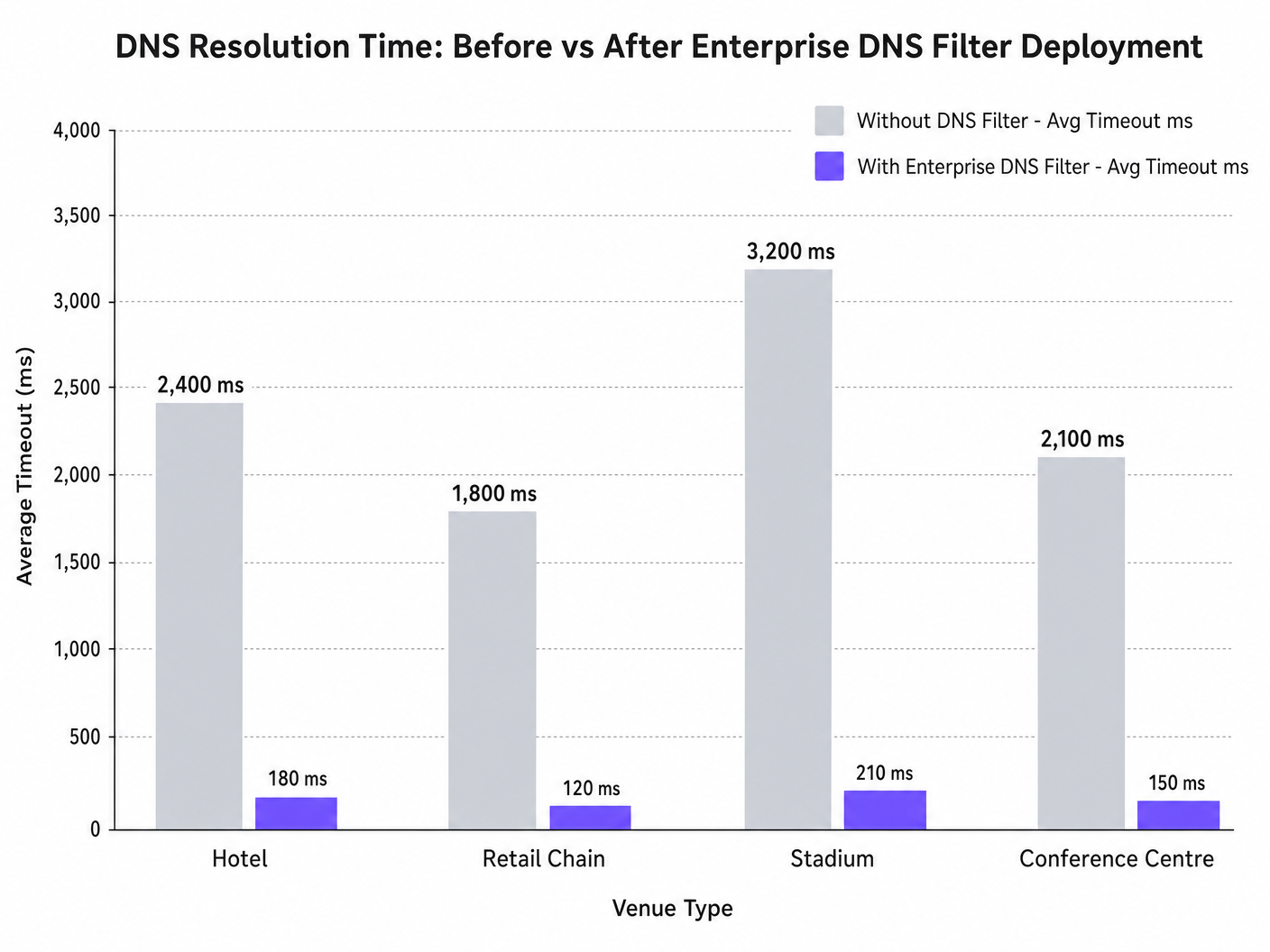
Quando centenas de dispositivos sondam simultaneamente a deteção de Captive Portal (por exemplo, captive.apple.com), as consultas da porta UDP 53 predefinidas podem sobrecarregar os resolvedores upstream padrão. Se a resposta DNS exceder a janela de timeout ao nível do SO (tipicamente 1-5 segundos), o dispositivo assume que não existe conectividade à internet, falhando em acionar o Captive Portal. Este guia detalha a arquitetura técnica deste modo de falha e demonstra como a implementação de um filtro DNS empresarial resolve o estrangulamento, reduzindo a latência da consulta de milhares de milissegundos para menos de 200ms, garantindo a conformidade com padrões como IEEE 802.1X e GDPR, e melhorando drasticamente a experiência de onboarding de convidados.
Análise Técnica Detalhada
O Mecanismo de Deteção de Captive Portal
Quando um dispositivo cliente se associa a um ponto de acesso e recebe um lease DHCP, deve verificar a acessibilidade à internet antes de fazer a transição completa para um estado conectado. Isto é conseguido através de sondas de deteção de Captive Portal:
- iOS/macOS: HTTP GET para
captive.apple.com - Android: HTTP GET para
connectivitycheck.gstatic.com - Windows: HTTP GET para
msftconnecttest.com
Antes que o HTTP GET possa ser emitido, o dispositivo deve resolver o hostname via DNS. Esta consulta DNS inicial é o ponto de falha crítico em ambientes de alta densidade.
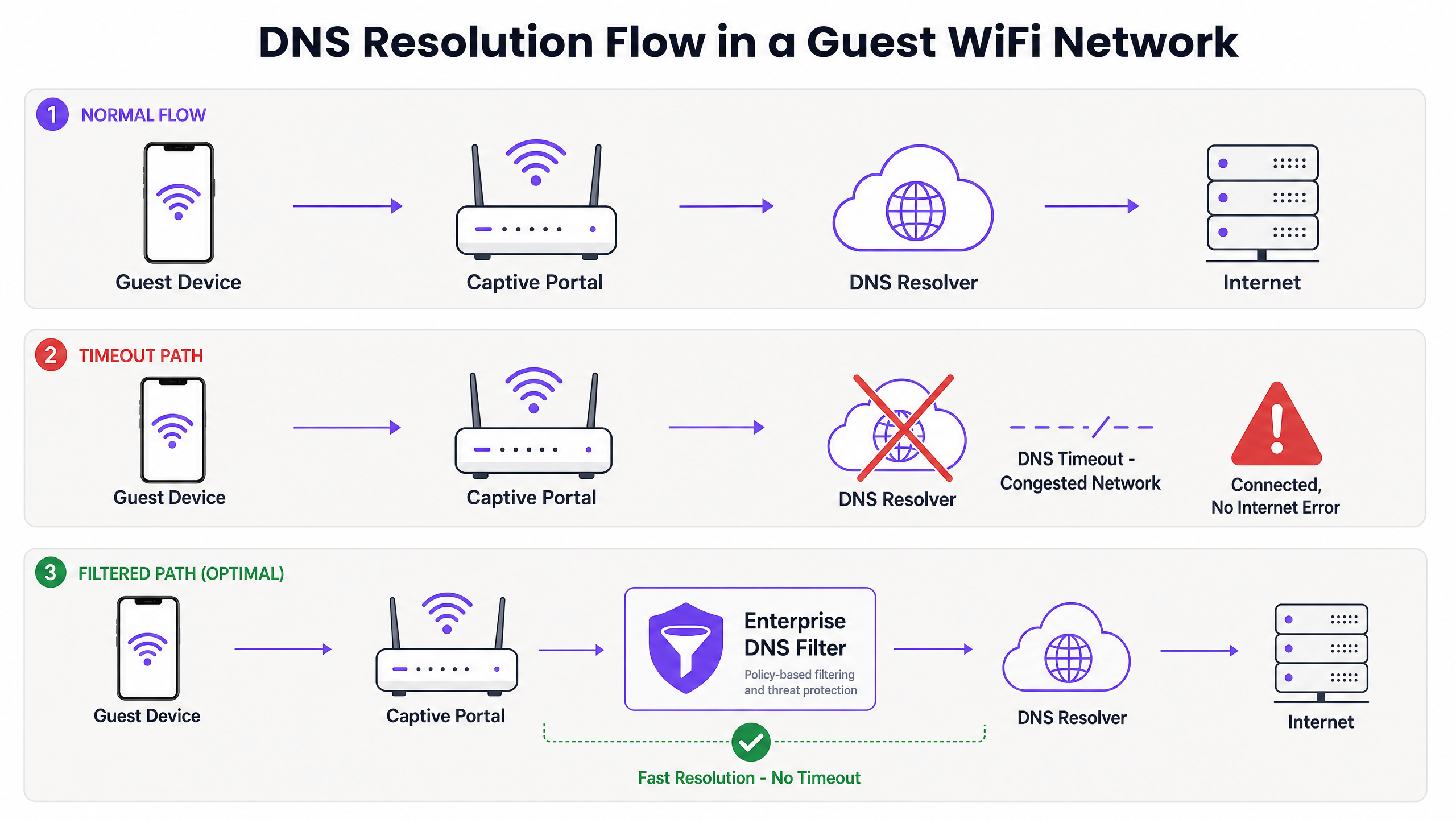
Porque o Congestionamento Desencadeia Timeouts de DNS
As consultas DNS tipicamente usam UDP, um protocolo sem conexão e sem retransmissão na camada de transporte. Numa rede congestionada — como um estádio durante o intervalo ou um hotel durante as horas de pico da manhã — os pacotes UDP são facilmente perdidos ou atrasados.
Se o local depende de um resolvedor ISP padrão ou de um serviço DNS público (como 8.8.8.8), o tempo de ida e volta (RTT) mais o tempo de processamento no resolvedor pode exceder o limite de timeout codificado no SO. Quando o timeout expira, o dispositivo sinaliza a conexão como "Ligado, Sem Internet" e interrompe o processo de redirecionamento do Captive Portal.
Além disso, valores curtos de Time-To-Live (TTL) nestes domínios de sonda exacerbam o problema. À medida que os dispositivos se associam e desassociam constantemente, as entradas em cache expiram rapidamente, desencadeando um fluxo de consultas DNS simultâneas precisamente quando a rede está sob carga máxima.
O Papel do Filtro DNS Empresarial
Um filtro DNS empresarial, como o integrado na plataforma WiFi Analytics da Purple, atua como um resolvedor de alto desempenho, local ou próximo da edge. Ao intercetar as consultas DNS antes que estas atravessem o link WAN congestionado, o filtro:
- Armazena Domínios de Alta Frequência em Cache: Serve domínios de sonda localmente, reduzindo o RTT para níveis de sub-milissegundos.
- Aplicação de Políticas: Descarta imediatamente consultas para domínios maliciosos ou bloqueados, conservando a largura de banda WAN.
- Registo de Auditoria: Fornece um registo de auditoria para Segurança de TI , auxiliando na conformidade com o GDPR e na resposta a incidentes.
Guia de Implementação
A implementação de um filtro DNS empresarial requer um planeamento arquitetónico cuidadoso para evitar a introdução de novos pontos de falha.
1. Posicionamento do Resolvedor e Otimização da Latência
Implemente o filtro DNS o mais próximo possível da edge da rede. Para cadeias de retalho distribuídas, um nó de edge entregue na cloud é apropriado; para grandes locais de site único, como estádios, um appliance localizado ou máquina virtual no switch central é preferível. O objetivo é minimizar o número de saltos de encaminhamento entre a VLAN de convidados e o resolvedor.
2. Whitelisting de Captive Portal (Passthrough)
O passo de configuração mais crítico é garantir que o seu domínio de Captive Portal está explicitamente na whitelist. Se o filtro DNS atrasar ou bloquear a resolução do próprio portal de autenticação, irá induzir o erro exato que está a tentar resolver.
3. Ajuste de TTL e Gestão de Cache
Configure o resolvedor local para armazenar agressivamente em cache os domínios de sonda do Captive Portal. Embora respeitar os TTLs upstream seja uma prática padrão, anular os TTLs para captive.apple.com e domínios semelhantes para um mínimo de 60 segundos localmente pode reduzir drasticamente o volume de consultas upstream durante eventos de associação de pico.
4. Integração com a Infraestrutura Existente
Garanta que a implementação do filtro DNS se alinha com a sua segmentação de rede existente. O tráfego DNS de convidados deve permanecer isolado da infraestrutura DNS corporativa para manter a conformidade com PCI DSS. Este isolamento é crucial, quer esteja a otimizar o WiFi de hotel para viajantes de negócios ou a proteger uma implementação no setor público.
Ouça o nosso podcast de briefing técnico para mais contexto sobre estes passos de implementação:
Melhores Práticas
- Evite Resolvedores Públicos para Redes de Convidados: Confiar em 8.8.8.8 ou 1.1.1.1 como o DO DNS atribuído pelo HCP para redes de convidados de alta densidade introduz variabilidade de latência inaceitável.
- Implementar DNS sobre HTTPS (DoH) com Cuidado: Embora o DoH melhore a privacidade, ele ignora a filtragem tradicional da porta 53. Certifique-se de que a sua solução DNS empresarial pode inspecionar ou gerir o tráfego DoH, se exigido pela política do local.
- Monitorizar Quedas da Porta UDP 53: Configure a sua firewall ou switch central para alertar sobre quedas excessivas de pacotes UDP na porta 53, o que é um indicador principal de timeouts de DNS iminentes.
- Rever Regularmente as Listas de Bloqueio: A filtragem excessivamente agressiva pode quebrar aplicações legítimas. Reveja os registos de consulta DNS semanalmente para identificar falsos positivos.
Para implementações no setor público, garantir uma conectividade robusta faz parte de iniciativas mais amplas de inclusão digital, como recentemente destacado quando Purple nomeia Iain Fox como VP de Crescimento – Setor Público .
Resolução de Problemas e Mitigação de Riscos
Quando ocorre o erro "Conectado, Sem Internet", as equipas de TI devem seguir um caminho de diagnóstico estruturado em vez de assumir imediatamente o esgotamento da largura de banda.
- Captura de Pacotes (PCAP): Execute uma captura de pacotes na VLAN de convidados, filtrando por
udp port 53. Procure por consultas sem respostas correspondentes dentro de uma janela de 2 segundos. - Simular a Sondagem: Use
curlouwgeta partir de um dispositivo de teste na VLAN de convidados para aceder manualmente ahttp://captive.apple.com/hotspot-detect.html. Meça o tempo de resolução DNS versus o tempo de resposta HTTP. - Verificar Regras da Firewall: Verifique se nenhuma política de limitação de taxa ou QoS está a estrangular inadvertidamente o tráfego UDP da porta 53 da sub-rede de convidados.
- Verificar Capacidades Offline: Em ambientes com conectividade WAN intermitente, considere funcionalidades como o Modo de Mapas Offline da Purple para manter algum nível de envolvimento do utilizador mesmo quando a internet a montante está degradada.
ROI e Impacto no Negócio
Resolver timeouts de DNS impacta diretamente os resultados financeiros dos operadores de locais.
- Redução de Custos de Suporte: O erro "Conectado, Sem Internet" é um dos principais impulsionadores de tickets de suporte de Nível 1 na hotelaria e retalho. Eliminá-lo reduz os gastos operacionais de TI.
- Aumento da Captura de Dados: Um carregamento falhado do Captive Portal significa uma oportunidade perdida para a captura de dados e autenticação de utilizadores. Ao garantir uma renderização rápida do portal, os locais maximizam o ROI das suas plataformas de WiFi Analytics .
- Satisfação Aprimorada do Convidado: A conectividade sem falhas é uma expectativa básica. Minimizar o atrito no onboarding correlaciona-se diretamente com a melhoria dos Net Promoter Scores (NPS) e avaliações positivas do local.
Ao mudar a perspetiva de "precisamos de mais largura de banda" para "precisamos de resolução DNS otimizada", os arquitetos de rede podem fornecer WiFi de convidados de nível empresarial que escala graciosamente sob pressão.
Definições Principais
Captive Portal Detection Probe
An automated HTTP request sent by a mobile OS (e.g., to captive.apple.com) immediately upon network association to determine if a login page is required.
If this probe fails due to DNS timeout, the OS assumes there is no internet access and shows the error.
DNS Timeout
The event where a client device abandons a DNS query because the resolver took too long to respond (typically >2-5 seconds).
The primary technical cause of 'Connected, No Internet' errors in high-density environments.
Enterprise DNS Filter
A dedicated DNS resolver that caches queries locally and applies policy-based blocking to prevent access to malicious or unwanted domains.
Used to offload query volume from congested upstream resolvers and reduce latency.
UDP Port 53
The standard connectionless transport protocol and port used for DNS queries.
Because UDP has no guaranteed delivery, DNS packets are easily dropped during network congestion.
Time-To-Live (TTL)
A value in a DNS record that dictates how long a resolver or client should cache the IP address before querying again.
Short TTLs on probe domains cause frequent re-querying, exacerbating congestion.
IEEE 802.1X
A standard for port-based Network Access Control (PNAC) providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
While secure, 802.1X environments still rely on robust DNS infrastructure for post-authentication routing.
Local Internet Breakout
Routing internet-bound traffic directly from a branch location to the internet, rather than backhauling it to a central data center.
Crucial for reducing DNS latency in distributed retail or hospitality networks.
WPA3
The latest Wi-Fi security standard that provides enhanced encryption for open and password-protected networks.
WPA3 improves security but does not alter the fundamental DNS resolution path or mitigate timeout issues.
Exemplos Práticos
A 400-room hotel experiences a surge of 'Connected, No Internet' complaints every morning between 7:30 AM and 8:30 AM when guests wake up and connect to the WiFi. The 1Gbps WAN link shows only 40% utilization during this time.
- Run a packet capture on the guest VLAN filtering for UDP port 53 during the morning peak.
- Identify that DNS queries to captive portal probe domains (e.g., captive.apple.com) are taking >3000ms to resolve via the ISP's default DNS.
- Deploy a local enterprise DNS filter on the guest subnet.
- Configure the DHCP server to assign the local DNS filter IP to guest devices.
- Whitelist the hotel's captive portal domain in the filter.
- Monitor resolution times, which should drop to <50ms.
A large retail chain rolls out a new guest WiFi network across 50 stores, but users in high-footfall flagship stores cannot load the captive portal, while users in smaller stores have no issues.
- Analyze the architecture: all 50 stores are tunneling guest traffic back to a central data center firewall, which then forwards DNS queries to a public resolver.
- In high-footfall stores, the sheer volume of concurrent association events exhausts the NAT/PAT state tables on the central firewall, causing UDP port 53 packets to be dropped.
- Implement a cloud-delivered enterprise DNS filter.
- Reconfigure the local branch routers to forward guest DNS queries directly to the cloud filter via local internet breakout, rather than backhauling them to the data center.
Perguntas de Prática
Q1. A stadium IT director notices that during half-time, thousands of users connect to the WiFi but fail to reach the captive portal. The core switch shows heavy UDP packet drops. Should they increase the WAN bandwidth from 2Gbps to 5Gbps?
Dica: Consider what protocol is being dropped and whether it's related to payload bandwidth or connection state limits.
Ver resposta modelo
No. Increasing WAN bandwidth will not solve the issue. The UDP packet drops indicate that the firewall or resolver cannot handle the sheer volume of concurrent DNS queries (state table exhaustion or CPU limits). The correct approach is to deploy a high-performance local DNS filter at the edge to cache and respond to these queries locally, bypassing the WAN bottleneck entirely.
Q2. You have just deployed an enterprise DNS filter on a hotel guest network. Guests can now resolve public websites quickly, but when they first connect, they are not redirected to the hotel's login page. What is the most likely configuration error?
Dica: Think about the domain name of the login page itself.
Ver resposta modelo
The most likely error is that the captive portal's own domain has not been explicitly whitelisted (passthrough) in the DNS filter. The filter is either blocking or delaying the resolution of the portal URL, preventing the redirection from completing.
Q3. A public sector organization requires all guest WiFi traffic to be logged for 90 days to comply with security policies. How does deploying an enterprise DNS filter assist with this requirement?
Dica: Consider what data a DNS filter processes versus a standard firewall.
Ver resposta modelo
An enterprise DNS filter natively logs all DNS queries made by client devices. This provides a clear, searchable audit trail of which domains were requested and when, satisfying the 90-day logging requirement without needing to perform deep packet inspection on all encrypted HTTPS payload traffic.