Boosting Staff Productivity by Filtering Intrusive Ads and Trackers
This technical reference guide provides actionable strategies for IT managers and network architects to deploy DNS-level filtering on corporate networks. It explores how blocking intrusive ads and trackers mitigates security risks like malvertising while significantly reclaiming bandwidth and boosting staff productivity.
Listen to this guide
View podcast transcript
- Executive Summary
- Technical Deep-Dive
- Architecture and Flow
- Threat Intelligence and Blocklists
- Handling Encrypted DNS (DoH/DoT)
- Implementation Guide
- Phase 1: Network Segmentation and Authentication
- Phase 2: Resolver Deployment
- Phase 3: Monitor-Only Mode
- Phase 4: Allowlist Configuration and Enforcement
- Best Practices
- Troubleshooting & Risk Mitigation
- False Positives
- Encrypted DNS Bypass
- Guest Network Interference
- ROI & Business Impact
- Bandwidth Reclamation
- Productivity Gains
- Compliance and Risk Reduction
- Listen to the Briefing
Executive Summary
Unfiltered corporate networks expose organisations to significant security vulnerabilities and hidden productivity drains. When staff devices connect to the internet, up to 40% of DNS queries can originate from advertising networks, third-party trackers, and telemetry endpoints. This background traffic not only consumes valuable bandwidth but also introduces malvertising vectors directly into the enterprise environment.
For IT managers and network architects operating in Hospitality , Retail , Healthcare , and Transport , deploying network-level ad and tracker filtering is a high-ROI intervention. By intercepting requests at the DNS layer, organisations can prevent malicious payloads from executing, ensure compliance with data privacy regulations like GDPR, and reclaim lost productivity. This guide details the technical architecture of DNS filtering, vendor-neutral deployment strategies, and measurable business impacts for modern enterprise networks.
Technical Deep-Dive
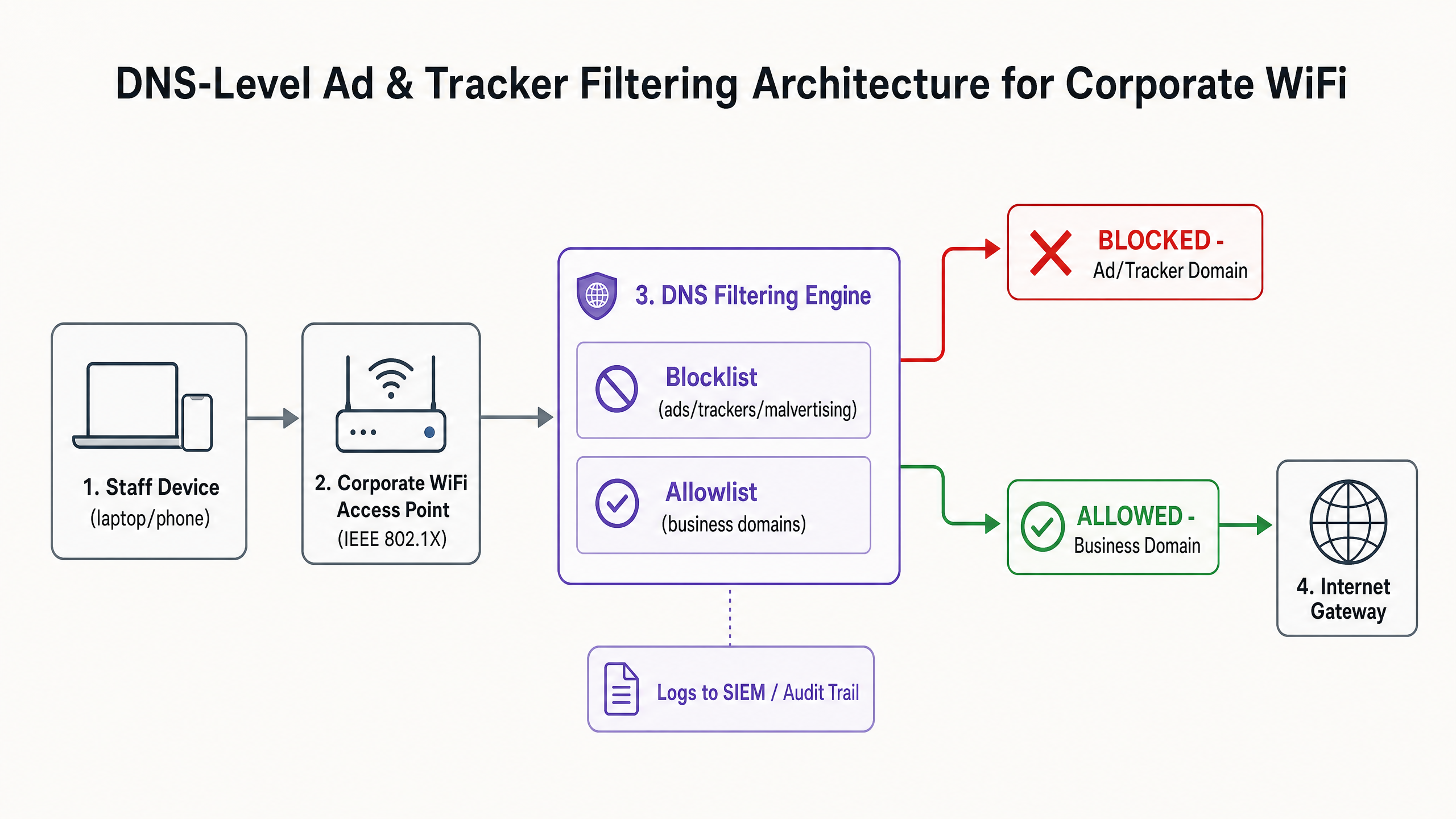
The foundation of effective ad and tracker mitigation is DNS-level filtering. Unlike browser-based extensions that operate at the application layer and require individual endpoint management, DNS filtering provides infrastructure-wide enforcement. When a device—whether corporate-managed or Bring Your Own Device (BYOD)—attempts to resolve a domain, the DNS resolver checks the query against curated threat intelligence blocklists.
Architecture and Flow
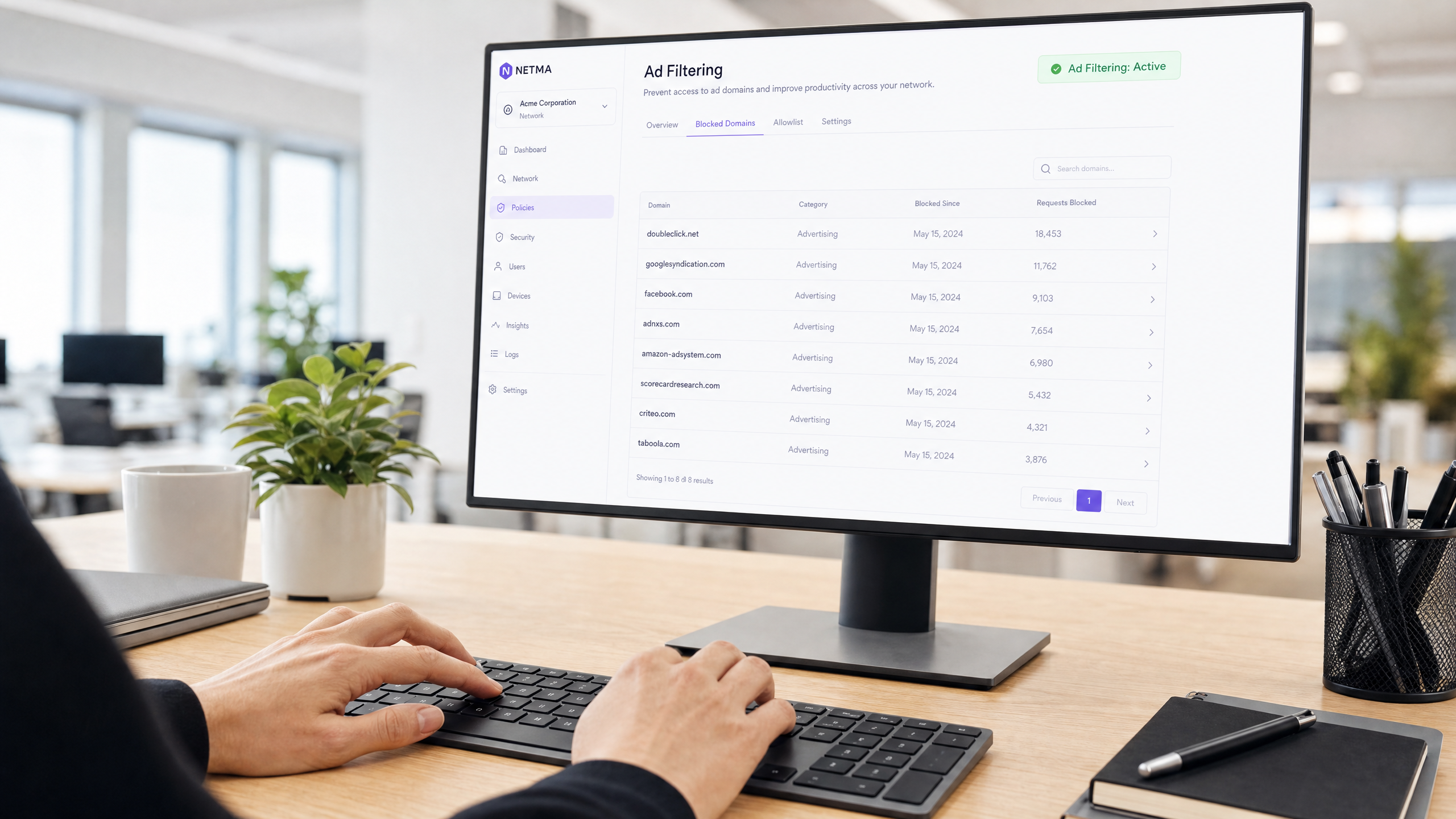
The filtering engine sits between the access point and the internet gateway. If a requested domain matches a known advertising network (e.g., doubleclick.net) or tracker, the resolver returns a null response (0.0.0.0) or an NXDOMAIN error. The malicious or distracting content never reaches the endpoint.
Threat Intelligence and Blocklists
A robust filtering architecture relies on dynamic threat intelligence. Static blocklists are insufficient against rapidly rotating malvertising domains. Enterprise deployments typically aggregate multiple sources, including open-source lists (like EasyList and EasyPrivacy) and commercial threat feeds. These lists must categorise domains accurately to prevent false positives that could disrupt business-critical applications.
Handling Encrypted DNS (DoH/DoT)
Modern operating systems and browsers increasingly default to DNS over HTTPS (DoH) or DNS over TLS (DoT), encrypting queries to external resolvers like Cloudflare (1.1.1.1) or Google (8.8.8.8). This bypasses local DNS filtering. To maintain control, network architects must configure edge firewalls to block outbound TCP/UDP port 853 (DoT) and intercept or block known DoH provider IP addresses, forcing clients to fall back to the provided local resolver.
Implementation Guide
Deploying DNS filtering requires a phased approach to avoid disrupting operations. A sudden, aggressive blocklist implementation will inevitably break legitimate SaaS applications and generate helpdesk tickets.
Phase 1: Network Segmentation and Authentication
Before altering DNS resolution, ensure the staff network is logically separated from the Guest WiFi and IoT environments using VLANs. Implement WPA3-Enterprise with IEEE 802.1X authentication. This ensures that only authenticated users access the corporate SSID and allows for per-user policy enforcement. If you are still relying on pre-shared keys (PSKs), upgrading your authentication model is the prerequisite step. For further insights on modernising your infrastructure, review our guide on Office Wi Fi: Optimize Your Modern Office Wi-Fi Network .
Phase 2: Resolver Deployment
Select a DNS filtering architecture that aligns with your operational capabilities:
- On-Premises Appliance: Offers the lowest latency and ensures all query logs remain within your infrastructure, crucial for strict data sovereignty requirements.
- Cloud-Based Service: Offloads threat intelligence maintenance to the vendor, ideal for distributed retail or hospitality environments.
- Hybrid Model: Uses a local forwarder for internal DNS resolution while routing external queries to a filtered cloud service.
Phase 3: Monitor-Only Mode
Deploy the filtering engine in monitor-only mode for 14 to 28 days. Do not block any traffic. Instead, ingest the query logs into your SIEM to establish a baseline. Analyze the top blocked domains against your business applications.
Phase 4: Allowlist Configuration and Enforcement
Based on the monitoring phase, construct an explicit allowlist for necessary third-party domains used by your CRM, ERP, or payment gateways. Once the allowlist is verified, switch the engine to enforcement mode. Ensure you maintain a clear audit trail of all configuration changes and blocked events.
Best Practices
To ensure a successful deployment and maintain network integrity, adhere to the following vendor-neutral best practices:
- Communicate Before Enforcing: Notify staff before activating the filtering. Frame it as a security and performance upgrade rather than an HR surveillance measure. Provide a clear, SLA-backed process for users to request domain unblocking.
- Enforce DHCP DNS Assignment: Prevent users from manually configuring alternative DNS servers by enforcing the use of the DHCP-provided resolver.
- Regularly Review the Allowlist: Business applications evolve. Conduct quarterly reviews of your allowlist to remove deprecated domains and assess new requirements.
- Integrate with Endpoint Protection: DNS filtering is a perimeter defence. It must be paired with robust Endpoint Detection and Response (EDR) solutions to protect against threats introduced via USB or email attachments.
Troubleshooting & Risk Mitigation
The most significant risk during deployment is over-blocking, which directly impacts business operations.
False Positives
When a legitimate service fails to load, it often relies on a background tracking domain for authentication or analytics.
- Mitigation: Empower the helpdesk with temporary bypass capabilities or a streamlined allowlisting workflow. Use the query logs to identify the specific blocked domain causing the failure.
Encrypted DNS Bypass
Technically proficient users or sophisticated malware may attempt to bypass the local resolver using DoH/DoT.
- Mitigation: Implement strict firewall rules blocking outbound traffic to known DoH resolvers. Monitor firewall logs for repeated connection attempts to port 853.
Guest Network Interference
Applying aggressive staff filtering policies to the guest network can degrade the visitor experience.
- Mitigation: Maintain strict VLAN isolation. Apply a lighter, security-focused filtering profile (blocking malware and adult content) to the guest network, managed through a dedicated WiFi Analytics platform.
ROI & Business Impact
The business impact of network-level filtering extends beyond security; it is a measurable productivity driver.
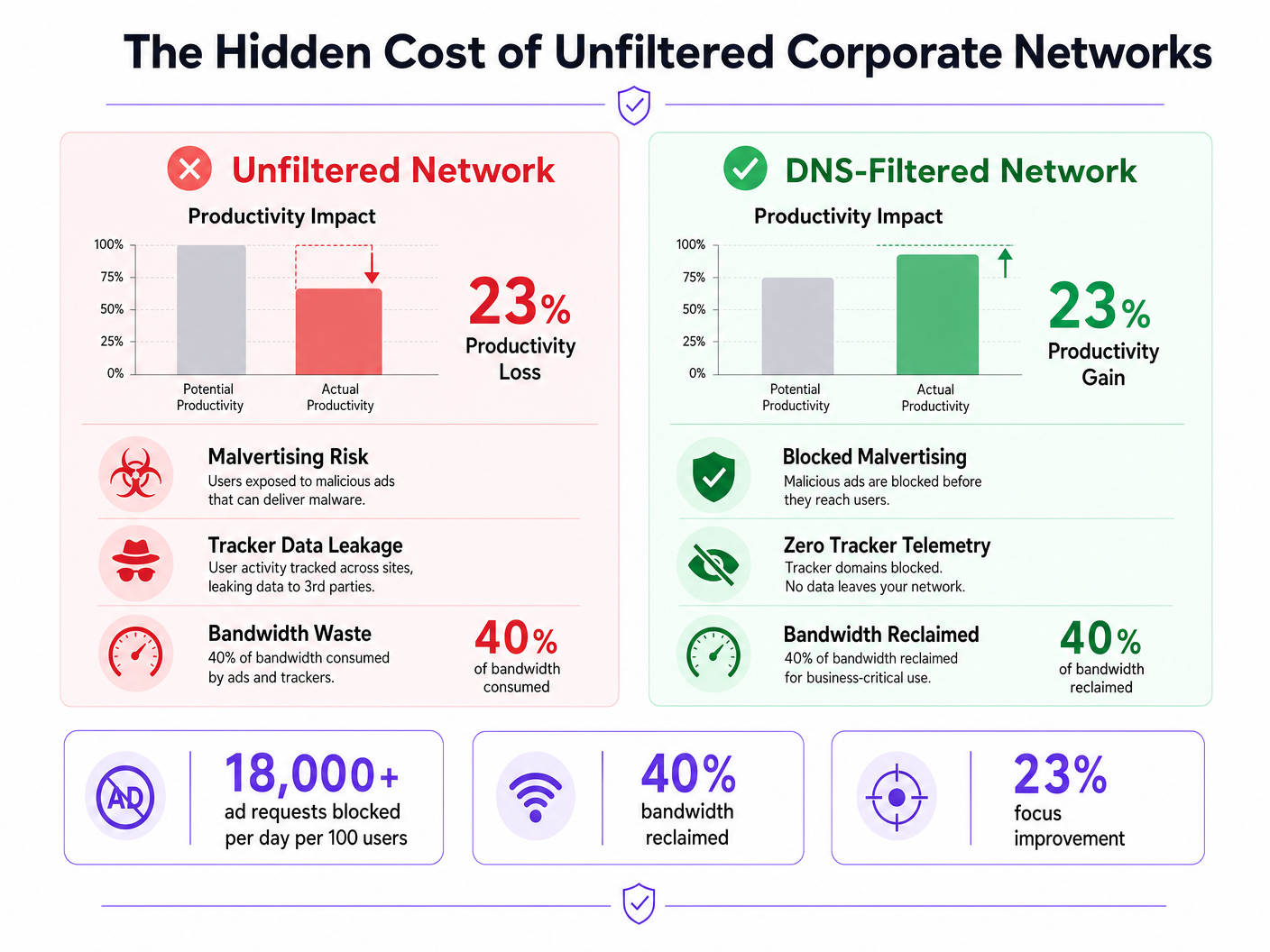
Bandwidth Reclamation
By eliminating up to 40% of unnecessary background requests, organisations reclaim significant bandwidth. This reduces the need for costly WAN circuit upgrades and improves the performance of critical cloud applications.
Productivity Gains
Reducing exposure to intrusive ads and malvertising minimises cognitive interruptions. While exact figures vary, mitigating these distractions recovers hundreds of hours of focused work time annually across the enterprise. For similar strategies applied to educational environments, see our guide on Minimising Student Distractions with Network-Level Ad Blocking and the Spanish version Minimizar las distracciones de los estudiantes con el bloqueo de anuncios a nivel de red .
Compliance and Risk Reduction
Filtering trackers at the network level demonstrates proactive compliance with data protection frameworks like GDPR and PCI DSS. By preventing data exfiltration and blocking malvertising payloads before they reach the endpoint, organisations significantly reduce their risk exposure and potential incident response costs.
Listen to the Briefing
For a deeper dive into the deployment strategies, listen to our audio briefing:
Key Definitions
DNS-Level Filtering
The process of blocking access to specific domains by intercepting DNS queries and returning a null response or redirect, preventing the device from connecting to the target server.
Used by IT teams to enforce security and productivity policies across an entire network without requiring endpoint software.
Malvertising
The use of online advertising to distribute malware. Malicious code is injected into legitimate advertising networks and displayed on trusted websites.
A primary vector for ransomware and spyware, making ad blocking a critical cybersecurity control, not just a productivity tool.
DNS over HTTPS (DoH)
A protocol for performing remote Domain Name System resolution via the HTTPS protocol, encrypting the data between the DoH client and the DoH-based DNS resolver.
While improving user privacy, DoH can bypass corporate DNS filtering policies if not actively managed and blocked at the firewall.
IEEE 802.1X
An IEEE Standard for port-based Network Access Control (PNAC), providing an authentication mechanism to devices wishing to attach to a LAN or WLAN.
Essential for enterprise WiFi security, replacing shared passwords (PSKs) with individual user credentials or certificates.
Telemetry
The automatic recording and transmission of data from remote or inaccessible sources to an IT system in a different location for monitoring and analysis.
Often generated by software and devices tracking user behaviour; blocking unnecessary telemetry reclaims bandwidth and protects privacy.
False Positive
An error in data reporting in which a test result improperly indicates presence of a condition, such as when a legitimate business domain is incorrectly categorised as malware or advertising.
The main cause of operational disruption during DNS filtering rollouts, mitigated by proper allowlisting.
SIEM (Security Information and Event Management)
A solution that provides real-time analysis of security alerts generated by applications and network hardware.
DNS query logs should be exported to the SIEM to identify compromised devices attempting to contact command-and-control servers.
Allowlist
A mechanism that explicitly allows access to specific entities (domains, IP addresses) while denying access to all others by default, or overriding a broader blocklist.
Critical for ensuring third-party integrations (like payment gateways or CRMs) function correctly behind a strict DNS filter.
Worked Examples
A 200-room hotel needs to secure its staff network (used by reception, housekeeping, and management) against malvertising, while ensuring the property management system (PMS) remains fully operational. The current network uses a single WPA2-PSK SSID for all staff.
- Upgrade the staff network to WPA3-Enterprise using IEEE 802.1X authentication to ensure individual accountability and encryption.
- Segment the staff network onto a dedicated VLAN, isolated from the guest WiFi.
- Deploy a cloud-based DNS filtering service with a local forwarder.
- Run the filter in monitor-only mode for 14 days.
- Analyze logs to identify all domains accessed by the PMS (e.g., third-party booking engine APIs, payment gateways) and add them to the allowlist.
- Enforce blocking for 'Advertising', 'Trackers', and 'Malware' categories.
- Block outbound TCP/UDP port 853 at the firewall to prevent DoT bypass.
A retail chain is experiencing high latency on its point-of-sale (POS) terminals during peak hours. Packet analysis reveals 35% of DNS traffic consists of tracking and telemetry requests from staff BYOD devices connected to the corporate network.
- Implement DNS-level filtering targeting 'Trackers' and 'Advertising' categories.
- Ensure POS terminals are on a strictly isolated VLAN with restricted outbound internet access (PCI DSS Requirement 1.3).
- Route the BYOD staff VLAN through the DNS filtering engine.
- Communicate the change to staff, emphasising the performance benefits for the POS systems.
- Monitor bandwidth utilisation post-enforcement to quantify the reclaimed capacity.
Practice Questions
Q1. Your organisation is implementing DNS filtering. During the monitor-only phase, you notice that a high volume of requests to 'api.segment.io' are being flagged under the 'Trackers' category. This domain is used by your marketing team's analytics dashboard. How should you proceed?
Hint: Consider the impact of blocking versus the business requirement for the tool.
View model answer
Add 'api.segment.io' to the explicit allowlist before moving to enforcement mode. While it is technically a tracker, it is a sanctioned business application. Failing to allowlist it will break the marketing dashboard and generate support tickets.
Q2. After deploying DNS filtering, you observe that devices using the latest version of a popular web browser are still loading ads and resolving domains that should be blocked. Older devices are filtered correctly. What is the most likely cause?
Hint: Modern browsers often try to encrypt their DNS queries.
View model answer
The modern browser has likely enabled DNS over HTTPS (DoH) by default, bypassing the local DNS resolver and communicating directly with an external provider (like Cloudflare). You must configure the firewall to block or intercept known DoH IP addresses to force the browser to fall back to the local filtered DNS.
Q3. A venue operations director asks if they can use the same aggressive ad-blocking DNS policy on the public Guest WiFi as they do on the corporate Staff WiFi to save bandwidth. What is the architectural recommendation?
Hint: Consider the user experience and the different risk profiles of staff versus guests.
View model answer
No. The Staff and Guest networks must remain on isolated VLANs with separate DNS policies. Applying aggressive corporate filtering to the Guest WiFi will likely break captive portals, cause false positives on diverse guest devices, and lead to a poor user experience. Guest networks should use a lighter filtering profile focused strictly on malware and legal compliance.