802.1X Authentication: Securing Network Access on Modern Devices
This guide provides a comprehensive, actionable overview of IEEE 802.1X authentication for senior IT professionals and network architects. It details the critical steps for securing network access across diverse enterprise environments, focusing on practical, vendor-neutral deployment guidance to mitigate risk, ensure compliance, and deliver a seamless, secure user experience.
Listen to this guide
View podcast transcript

Executive Summary
This guide provides a comprehensive, actionable overview of IEEE 802.1X authentication for senior IT professionals and network architects. It details the critical steps for securing network access across diverse enterprise environments—from hospitality and retail to large-scale public venues. We move beyond academic theory to offer practical, vendor-neutral deployment guidance focused on mitigating risk, ensuring compliance with standards like PCI DSS and GDPR, and delivering a seamless, secure user experience on modern devices, including iOS and Android. By leveraging 802.1X, organisations can replace vulnerable pre-shared keys with robust, identity-based access control, ensuring that only authorised and trusted devices can connect to corporate network resources. This document serves as a strategic reference for planning and executing a successful 802.1X implementation, covering architecture, EAP method selection, certificate management, and ROI analysis to help you make informed decisions that enhance your security posture and support business objectives.
Technical Deep-Dive
The IEEE 802.1X standard defines a port-based network access control (PNAC) mechanism to provide authenticated network access for Ethernet and 802.11 wireless networks. It represents a fundamental shift from legacy security protocols, which often relied on a single, shared password (Pre-Shared Key or PSK) for all users. An 802.1X framework authenticates the user or device before they are assigned an IP address and granted access to the network, creating a powerful security boundary at the point of entry.
The architecture is composed of three primary components:
- Supplicant: The client device seeking to connect to the network (e.g., a laptop, smartphone, or IoT device). The supplicant is the software on the client device that provides credentials to the authenticator.
- Authenticator: The network device that controls access to the network, typically a wireless access point (AP) or a switch. The authenticator acts as an intermediary, passing authentication messages between the supplicant and the authentication server.
- Authentication Server (AS): The centralised server that validates the supplicant's credentials and makes the final decision on whether to grant or deny access. In nearly all enterprise deployments, this role is fulfilled by a RADIUS (Remote Authentication Dial-In User Service) server.
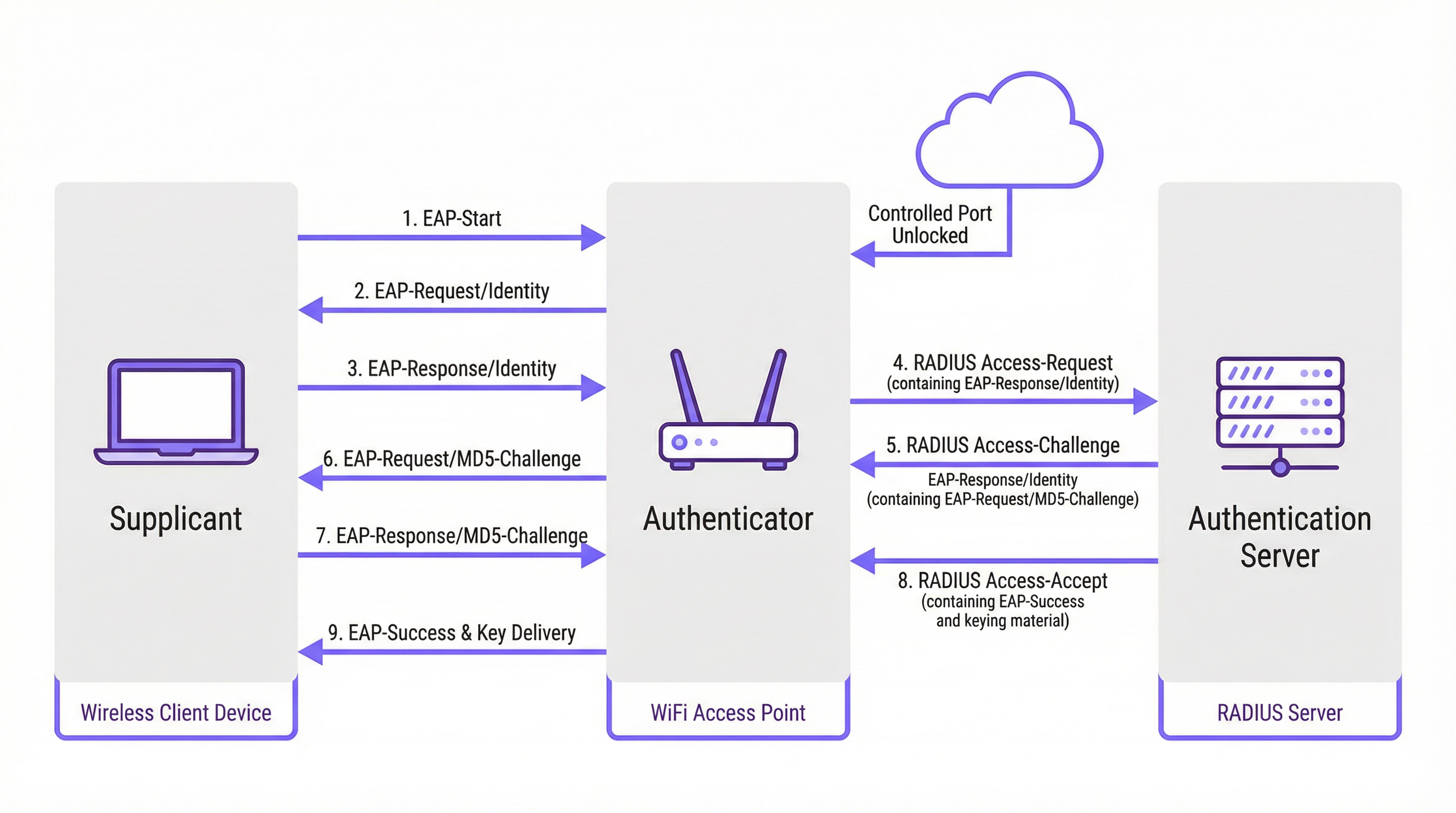
The authentication process follows a structured message exchange orchestrated by the Extensible Authentication Protocol (EAP). EAP is a flexible framework that supports various authentication methods (EAP types), allowing organisations to choose the one that best fits their security requirements and existing infrastructure.
EAP Methods Compared
Choosing the right EAP method is a critical deployment decision. The primary methods used in modern enterprise networks are EAP-TLS, PEAP, and EAP-TTLS.
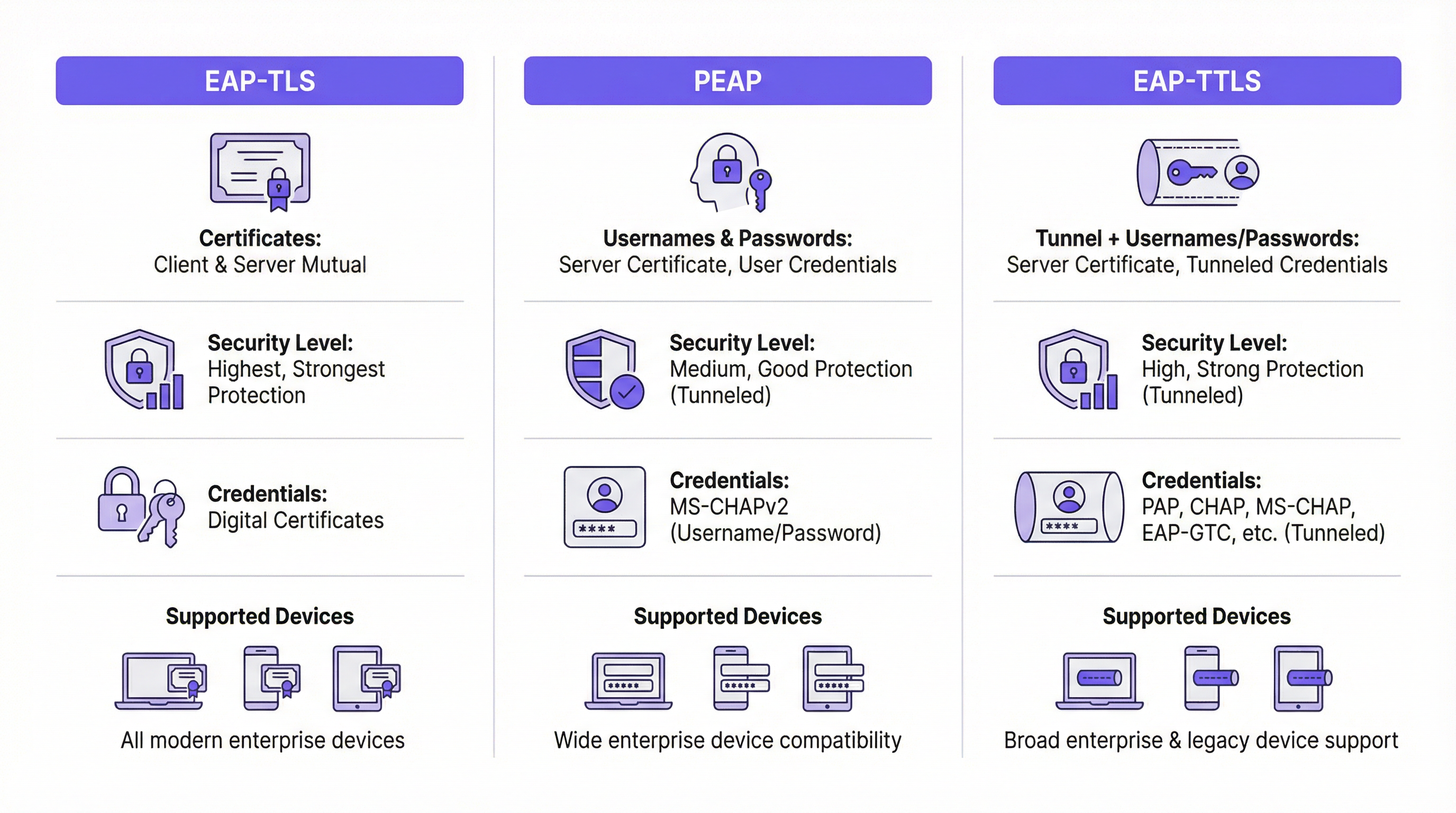
| Feature | EAP-TLS (Transport Layer Security) | PEAP (Protected EAP) | EAP-TTLS (Tunnelled TLS) |
|---|---|---|---|
| Security Level | Highest. Provides mutual certificate-based authentication. | High. Encrypts credential exchange within a TLS tunnel. | High. Similar to PEAP, encrypts credential exchange. |
| Credentials | Client & Server Digital Certificates | Server Certificate, User Credentials (e.g., Username/Password) | Server Certificate, User Credentials (more flexible options) |
| Complexity | High. Requires a Public Key Infrastructure (PKI) to manage certificates for all devices. | Medium. Leverages existing directory credentials (e.g., Active Directory). | Medium. Similar to PEAP but offers greater flexibility for authentication protocols. |
| Use Case | Corporate-owned devices where certificate deployment can be automated via MDM. High-security environments. | BYOD and corporate environments where username/password authentication is preferred. | Diverse environments with a mix of client operating systems (e.g., macOS, Linux). |
EAP-TLS is widely regarded as the gold standard for 802.1X security. It requires both the client and the server to have a digital certificate, enabling mutual authentication. This eliminates the risk of password-based attacks, but introduces the overhead of deploying and managing a certificate on every single client device.
PEAP is the most common EAP type in enterprise environments. It simplifies deployment by only requiring a certificate on the authentication server. The client verifies the server's identity and then creates an encrypted TLS tunnel. Inside this tunnel, the client authenticates using less complex methods, typically MS-CHAPv2 (username and password). While secure, it is still vulnerable to phishing attacks if users are tricked into connecting to a rogue AP with a valid-looking server certificate.
EAP-TTLS is functionally similar to PEAP but offers more flexibility. It also creates a TLS tunnel but allows for a wider range of inner authentication protocols, such as PAP, CHAP, or EAP-MD5, making it a versatile choice for environments with legacy systems or diverse client types.
Implementation Guide
A successful 802.1X deployment requires careful planning and phased execution. The following steps provide a vendor-neutral roadmap.
Phase 1: Infrastructure & Planning
- Select Your RADIUS Server: Choose a RADIUS server that aligns with your existing infrastructure. Microsoft's Network Policy Server (NPS) is a common choice for Windows-centric environments, while open-source options like FreeRADIUS are highly flexible. Cloud-based RADIUS services are also becoming increasingly popular for their scalability and reduced management overhead.
- Choose Your EAP Method: Based on the comparison above, select the EAP method that best balances your security requirements, user base, and administrative capabilities. For most corporate environments, PEAP offers a strong balance. For high-security deployments, EAP-TLS is the recommended path.
- Plan Your Certificate Strategy: This is the most critical step. For PEAP or EAP-TTLS, you will need a server certificate for your RADIUS server. This certificate MUST be issued by a trusted public Certificate Authority (CA). Using a self-signed certificate will result in security warnings on all client devices, undermining user trust and security.
Phase 2: Configuration
- Configure the RADIUS Server: Install and configure your chosen RADIUS server. This involves:
- Installing the server certificate.
- Defining RADIUS clients (your access points and switches).
- Creating Connection Request Policies to process incoming requests.
- Creating Network Policies that define the conditions, constraints, and settings for authentication. For example, a policy might state that only members of a specific Active Directory group are allowed to connect.
- Configure the Authenticator (Wireless APs/Switches):
- Configure your wireless LAN controller or individual access points with the IP address of your RADIUS server and the shared secret.
- Create a new WLAN/SSID dedicated to 802.1X. Do not attempt to run 802.1X on an existing PSK or open network.
- Ensure the SSID is configured for WPA2-Enterprise or WPA3-Enterprise.
Phase 3: Client Onboarding & Deployment
- Corporate Devices: Use a Mobile Device Management (MDM) or Group Policy (GPO) solution to automatically configure corporate-owned devices. The MDM/GPO can push the wireless network profile, including the SSID, EAP type, and any necessary CA certificates, to the device. This provides a zero-touch experience for the end-user.
- BYOD (Bring Your Own Device): Onboarding personal devices is more complex. The best practice is to use a dedicated onboarding solution. These solutions provide a temporary, open "onboarding" SSID. When a user connects, they are redirected to a captive portal where they can authenticate and download a configuration utility or profile that automatically sets up their device for the secure 802.1X network.
Best Practices
- Segment Your Network: Use dynamic VLAN assignment based on RADIUS attributes. This allows you to place different user groups (e.g., employees, contractors, guests) into different VLANs with distinct access policies, even when they connect to the same SSID.
- Always Use a Publicly Trusted Certificate: The importance of using a public certificate on your RADIUS server cannot be overstated. It is the cornerstone of client trust and prevents man-in-the-middle attacks.
- Monitor and Log: Actively monitor RADIUS authentication logs. This is invaluable for troubleshooting connection issues and for security auditing. Failed authentication attempts can be an early indicator of a potential attack.
- Prefer WPA3-Enterprise: Where supported by your hardware and clients, WPA3-Enterprise offers significant security enhancements over WPA2-Enterprise, including Protected Management Frames (PMF) to prevent de-authentication attacks.
Troubleshooting & Risk Mitigation
| Common Issue | Cause | Mitigation Strategy |
|---|---|---|
| Connection Fails | Mismatch in EAP types between client and server. Incorrect RADIUS shared secret. Firewall blocking RADIUS ports (UDP 1812/1813). | Verify EAP settings on both client and server. Double-check shared secret on AP and RADIUS server. Ensure firewalls allow RADIUS traffic. |
| Certificate Warnings | RADIUS server is using a self-signed or untrusted certificate. | Replace the self-signed certificate with one from a trusted public CA (e.g., DigiCert, Sectigo). |
| Slow Connections | RADIUS server is under-provisioned or has high latency to the directory service. | Monitor RADIUS server performance. Ensure low-latency connectivity between the RADIUS server and domain controllers. |
| Phishing/Rogue APs | Users are tricked into connecting to a malicious AP broadcasting the same SSID. | Use EAP-TLS to eliminate passwords. For PEAP/EAP-TTLS, ensure clients are configured to validate the server certificate and name. |
ROI & Business Impact
While implementing 802.1X requires an initial investment in time and resources, the return on investment (ROI) is significant, particularly for large-scale venues.
- Enhanced Security Posture: By moving from a single shared password to unique, per-user or per-device credentials, you dramatically reduce the risk of unauthorised access. This is a critical step in mitigating data breaches.
- Compliance: For organisations subject to PCI DSS, GDPR, or HIPAA, 802.1X is a key control for demonstrating that you have implemented strong access control measures. The cost of a failed audit or a compliance penalty far outweighs the cost of deployment.
- Operational Efficiency: Automating onboarding and using dynamic VLANs reduces the administrative burden on IT teams. New employees can be granted access automatically based on their directory group, and access is instantly revoked when they are removed.
- Improved User Experience: When deployed correctly with automated onboarding, 802.1X provides a seamless and secure connection experience. Users simply turn on their device, and it connects without requiring them to re-enter a password. This is a significant improvement over captive portals or complex PSKs.
Key Definitions
RADIUS
Remote Authentication Dial-In User Service. A networking protocol that provides centralised Authentication, Authorization, and Accounting (AAA) management for users and devices that attempt to access a network service.
In an 802.1X context, the RADIUS server is the 'brain' of the operation. It's the server that checks the user's or device's credentials and tells the access point whether to grant or deny access. IT teams will spend most of their time configuring policies on the RADIUS server.
EAP
Extensible Authentication Protocol. An authentication framework, not a specific authentication mechanism. It provides a standardised way for clients and servers to negotiate an authentication method.
EAP is the language spoken between the client device, the access point, and the RADIUS server. Understanding that EAP is a framework helps explain why there are so many different 'types' of 802.1X (EAP-TLS, PEAP, etc.). The choice of EAP type is the most important decision in an 802.1X deployment.
Supplicant
The software on a client device (like a laptop or smartphone) that is responsible for responding to the authenticator's requests for credentials.
The supplicant is built into modern operating systems like Windows, macOS, iOS, and Android. IT teams rarely interact with the supplicant directly, but they configure it via network profiles, telling it which EAP type to use and which server to trust.
Authenticator
The network device that acts as a gatekeeper, blocking or allowing traffic from the supplicant. In a wireless network, this is the access point (AP).
The authenticator doesn't make the authentication decision itself. It's a middleman that simply passes EAP messages between the supplicant and the authentication server. Its primary job is to enforce the decision made by the RADIUS server.
PKI
Public Key Infrastructure. A set of roles, policies, hardware, software, and procedures needed to create, manage, distribute, use, store, and revoke digital certificates.
A PKI is essential for deploying EAP-TLS, the most secure form of 802.1X. While the term sounds intimidating, a basic PKI can be set up using Microsoft Active Directory Certificate Services or a cloud-based service. It's the foundation for a certificate-based security model.
MDM
Mobile Device Management. Software that allows IT administrators to control, secure, and enforce policies on smartphones, tablets, and other endpoints.
MDM is the key to a scalable and seamless 802.1X deployment for corporate-owned devices. IT teams use the MDM to automatically push the WiFi profile and client certificate to devices, meaning users can connect securely with zero manual configuration.
Dynamic VLAN Assignment
A feature that allows the RADIUS server to assign a user or device to a specific VLAN based on their identity or group membership.
This is a powerful tool for network segmentation. Instead of having multiple SSIDs for different user groups, you can have one secure SSID. The RADIUS server then places employees in the corporate VLAN, guests in the guest VLAN, and IoT devices in their own isolated VLAN, all based on the credentials they present.
WPA3-Enterprise
The latest generation of Wi-Fi security for enterprise networks, building on WPA2-Enterprise by adding stronger encryption and protection against de-authentication attacks.
When procuring new network hardware, IT managers should ensure it supports WPA3-Enterprise. It provides a significant security uplift over its predecessor and is a key component of a modern, secure wireless infrastructure. It's the 'Enterprise' version that integrates with 802.1X.
Worked Examples
A 500-room luxury hotel needs to provide secure WiFi for staff (on corporate-issued tablets) and a separate, seamless experience for guests. The hotel must comply with PCI DSS due to its payment systems.
Staff Network: Implement an 802.1X EAP-TLS network. Deploy a RADIUS server and an internal Certificate Authority (or use a cloud PKI service). Use an MDM to automatically provision the corporate tablets with client certificates and the WPA2/WPA3-Enterprise network profile. This provides the highest level of security for devices handling sensitive operational data. Guest Network: Implement a separate SSID using a captive portal with a straightforward, time-limited voucher or social login. This network should be completely isolated from the staff and PCI networks using VLANs and firewall rules. This approach balances high security for corporate assets with ease of use for transient guests.
A large retail chain with 200 stores needs to secure its in-store network, which is used by Point-of-Sale (POS) terminals, employee-used handheld inventory scanners, and a guest WiFi network.
POS & Inventory Scanners: Deploy a single, hidden SSID using 802.1X EAP-TLS. Since these are corporate-controlled devices, certificates can be pre-loaded before deployment. Use MAC Authentication Bypass (MAB) as a fallback for legacy devices that may not support 802.1X, but this should be an exception. Assign this network to a secure, firewalled VLAN that only allows traffic to the payment processor and inventory management servers. Guest WiFi: Deploy a separate, public-facing SSID with a branded captive portal that requires acceptance of terms and conditions. This network must be completely isolated from the secure store network.
Practice Questions
Q1. Your CFO is concerned about the cost of a commercial certificate for the RADIUS server and suggests using a self-signed certificate from your internal Windows CA. How do you respond?
Hint: Consider the user experience and the security implications of a client not being able to automatically trust the server.
View model answer
A self-signed certificate will cause a security warning on every single device that connects to the network for the first time. This trains users to ignore security warnings, which is a significant security risk. A publicly trusted certificate is automatically recognised by all modern devices, providing a seamless connection experience and ensuring that clients can verify they are connecting to the legitimate server, which is crucial for preventing man-in-the-middle attacks. The annual cost of a public certificate is a small price to pay for the enhanced security and improved user experience.
Q2. A conference centre wants to use 802.1X for event attendees. They have thousands of new users each week. Is EAP-TLS a viable option? Why or why not?
Hint: Think about the lifecycle of a guest user and the administrative overhead of certificate management.
View model answer
EAP-TLS is likely not a viable option for this scenario. The primary challenge is the administrative overhead of provisioning a unique digital certificate for thousands of transient users each week. The process of generating, distributing, and then revoking these certificates would be operationally complex and costly. A better approach would be to use a simpler authentication method for guests, such as a captive portal with voucher codes or social login, while reserving 802.1X for staff and permanent infrastructure.
Q3. You are deploying a PEAP-MS-CHAPv2 network. A user reports that they can connect from their Windows laptop but not from their personal Android phone. What is the most likely cause of this issue?
Hint: Consider how different operating systems handle certificate validation and network profiles.
View model answer
The most likely cause is that the Android phone has not been configured to properly trust the RADIUS server's certificate. While a Windows laptop joined to a domain might automatically trust the certificate (if the root CA is pushed via Group Policy), a personal Android device needs to be manually configured. The user likely needs to install the root CA certificate on their phone and/or explicitly configure the network profile to validate the server certificate and specify the correct domain name. This highlights the importance of a clear and simple onboarding process for BYOD users.
Continue reading in this series
Per-Device PSK by Vendor: iPSK, DPSK, MPSK and PPSK Compared (and WPA3 Support)
A comprehensive comparison of per-device PSK implementations across Cisco Meraki, HPE Aruba, Ruckus, Juniper Mist, Extreme, Fortinet, and Ubiquiti UniFi. Learn how WPA3-SAE impacts per-device key strategies and when to deploy transition modes versus moving to 802.1X.
Per-Device PSK by Vendor: iPSK, DPSK, MPSK and PPSK Compared (and WPA3 Support)
A comprehensive comparison of per-device PSK implementations across Cisco Meraki, HPE Aruba, Ruckus, Juniper Mist, Extreme, Fortinet, and Ubiquiti UniFi. Learn how WPA3-SAE impacts per-device key strategies and when to deploy transition modes versus moving to 802.1X.
Captive Portal Authentication Methods Compared
This authoritative technical reference guide evaluates the architectural, operational, and compliance trade-offs of five core captive portal authentication methods. It provides network architects, IT directors, and marketing managers with the quantitative data and decision frameworks required to balance guest onboarding friction with data-collection requirements across enterprise venues.